smart-net-total-care-data-sheet
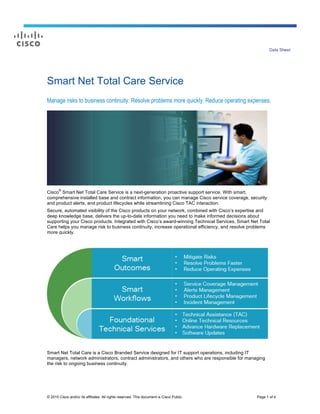
- 1. © 2015 Cisco and/or its affiliates. All rights reserved. This document is Cisco Public. Page 1 of 4 Data Sheet Smart Net Total Care Service Manage risks to business continuity. Resolve problems more quickly. Reduce operating expenses. Cisco ® Smart Net Total Care Service is a next-generation proactive support service. With smart, comprehensive installed base and contract information, you can manage Cisco service coverage, security and product alerts, and product lifecycles while streamlining Cisco TAC interaction. Secure, automated visibility of the Cisco products on your network, combined with Cisco’s expertise and deep knowledge base, delivers the up-to-date information you need to make informed decisions about supporting your Cisco products. Integrated with Cisco’s award-winning Technical Services, Smart Net Total Care helps you manage risk to business continuity, increase operational efficiency, and resolve problems more quickly. Smart Net Total Care is a Cisco Branded Service designed for IT support operations, including IT managers, network administrators, contract administrators, and others who are responsible for managing the risk to ongoing business continuity.
- 2. © 2015 Cisco and/or its affiliates. All rights reserved. This document is Cisco Public. Page 2 of 4 Smart Net Total Care Features and Capabilities A powerful and secure web portal, with customizable dashboard and reports, delivers actionable information and insights into your network. Reports can be configured to deliver the information you want, the way you want it. You can filter and search across any screen to easily find the information you are looking for. Multiple language support provides individual users with the ability to localize their portal interface. Smart Net Total Care delivers: Service Coverage Management Quickly and easily identify items that are covered (or not covered), and ensure that business-critical assets have the necessary support levels to meet business needs and comply with corporate policies. ● See which support contracts and device coverages will expire in the coming year, enabling you to more effectively plan, forecast, and budget. ● Generate a complete list of all devices associated with a support contract, even if not reachable, such as offline spares. ● Consolidate similar support contracts, reducing the resources required to manage and renew. Alerts Management Preempt network disruption by proactively identifying issues – effectively and efficiently manage and track Cisco security, hardware, and software alerts, and Cisco field notices. ● Easily list alerts that apply to your network, and which devices are affected, helping prioritize activity. ● Acknowledge those alerts that have been reviewed or mitigated, providing you with a concise and persistent list of activities and alerts needing attention. ● See which Cisco alerts have been generated, and alerts activities associated with your devices, during a specific time period. Product Lifecycle Management Automatically maintain a comprehensive and up-to-date view of your Cisco installed base, including device and configuration details such as serial number, IOS version, install memory and firmware, IP address and hostname. ● Identify Cisco products that are reaching end-of-life, end-of-sale, or end-of-support. ● Easily see what has moved, been added or changed in your network. ● Ensure your Cisco hardware is running current, supported software versions. ● Mitigate risk and plan for upgrades to equipment that is no longer supported. Incident Management Streamline TAC interaction with readily available device and support contract information. All necessary device information is at your fingertips, even if the device is unreachable. ● Easily create a service request against a device from within the portal. Click on a device to create a service request, which is auto-populated with information such as serial number and contract number. ● Review outstanding service requests or get a complete list of recent requests. ● SmartData Advantage automatically provides diagnostic information – configuration and logging information – to the TAC engineer when the case is started, improving resolution time. ● Device Diagnostics uses self-monitoring Smart Call Home technology on enabled devices to proactively diagnose, alert, and recommended remediation via the online portal. Integrated with Award-winning Foundational Technical Services Smart Net Total Care provides award-winning technical support services that give you direct, anytime access to field engineers and Cisco.com resources to get fast, expert response and accountability needed to resolve critical IT service operation issues. These include: ● Direct 24x7x365 access to specialized engineers in the Cisco Technical Assistance Center (TAC). ● Advance hardware replacement fits your needs – from next business day to as little as two hours. ● Extensive online trouble-shooting tools at cisco.com. ● Anytime access to eligible software and OS updates. ● Options for onsite field engineering to install replacement parts.
- 3. © 2015 Cisco and/or its affiliates. All rights reserved. This document is Cisco Public. Page 3 of 4 Actionable Information and Reports Smart Net Total Care provides you the information you need to support your Cisco network devices. There are dozens of customizable screens and reports that can be configured to show just the information you need, the way you want to see it. Screens and reports can be printed, saved, or exported to other applications for further analysis, or integration into your workflow. Smart Net Total Care uses up-to-date device information from your network, correlates and analyzes it with Cisco’s deep knowledge base, and delivers actionable, smart information for the Cisco contracts, devices, and alerts that apply to your network. Role-Task Reports and Screens Service Coverage Management All Contracts: A list of your company’s Cisco support contracts, with coverage details. Contracts Management: Extensive information and insights into service coverage, including gaps, contracts due for renewal, and Last Date of Support (LDOS). Covered/Not Covered Devices: Which devices do not have support contracts, which devices have support contracts, and the associated service level. Contract Duplicates: Shows which devices are covered by multiple contracts. Expiring Contracts/Devices: Which contracts are expiring in the upcoming 24-month period, and which devices are covered by expiring contracts. Aggregated: A comprehensive service contract view that includes devices in your network plus additional items listed on associated support contracts. Alerts Management Product Security Incident Response Team (PSIRT): Relevant security alerts for each affected device in your network. Hardware and Software: Lists hardware and software alerts for devices and software in your network, with links to detailed information and remediation. Field Notice: Relevant Field Notice information, with links to detailed information and remediation. Active Alerts: Lists those alerts that are active in your network. Alerts Delta: Identifies alerts from a specific period of time. Product Lifecycle Management Last Date of Support (LDOS): Items in your network that are near or past LDOS. Inventory Summary: Comprehensive information of chassis, cards, and other devices in your network. Inventory Collection Delta: Changes to your network, including adds, deletes, and moves (such as IP address changes) between two points in time. Chassis and Cards: Lists Cisco chassis, cards, and configuration and support contract details. All Equipment: Lists additional items associated with inventory devices, such as fans, power supplies, modules and cards. Also, software type and version for each item. Additional reports and screens show lifecycle information such as items that are not field replaceable, and inventory by site. Incident Management Inventory reports provide device details such as serial number, and Product ID, and corresponding configuration and service contract coverage information, including software type and version. Both summarized and detailed product alert information is also included. Bug-Affected Devices: Lists those devices with outstanding defects, with link to bug details. All Support Cases for Past 90 Days: Lists recent support cases, by device.
- 4. © 2015 Cisco and/or its affiliates. All rights reserved. This document is Cisco Public. Page 4 of 4 Why Cisco Cisco is delivering next-generation enterprise capabilities to our customers with software, services, and solutions in four areas: ● First we bring pre-integrated, network-centric, and scalable experience and engagement solutions that provide our customers with the ability to drive customer loyalty and employee productivity with rich interactivity ● We also bring a portfolio of open source, standards-based, and cloud-ready software and services to help our customers automate critical business processes and to integrate customer facing, partner facing, and back-end applications. ● With our data and analytics software and services, we help our customers instantly access distributed data sources and use network-powered analytics to gain actionable insights, drive higher performance, and achieve better business outcomes. ● With our portfolio of infrastructure operations offerings we establish the foundation for business continuity and optimization for our customers. With these offerings we bring software-enabled capabilities, network and device diagnostic data, and Cisco’s deep knowledge base to proactively manage infrastructure operation risks, accelerate problem resolution, and reduce operating expenses. With Cisco IoE Software Platforms and Services we make it possible to integrate solutions by combining services, platforms, and the rich set of Cisco Architectures. As a result our offers are tightly integrated with Cisco Networking, Collaboration, Data Center, and Service Provider architectures to extend the value of Cisco architectural services to industry applications and analytics solutions within our customers’ environment. More Information For more information about Cisco Smart Net Total Care Service, visit www.cisco.com/go/total or contact your local account representative. Get involved with the Smart Net Total Care Community. You can find resources such as videos, training, and case studies. Interact with other users in the discussion forums. www.bit.ly/community-sntc. For more information about other types of Cisco Services to maintain and optimize your network, including technology-specific and remote management services, visit www.cisco.com/go/supportservices. For a complete list of the technical services available for your Cisco products and applications, visit our Service Finder tool at www.cisco-servicefinder.com. Printed in USA 01/15