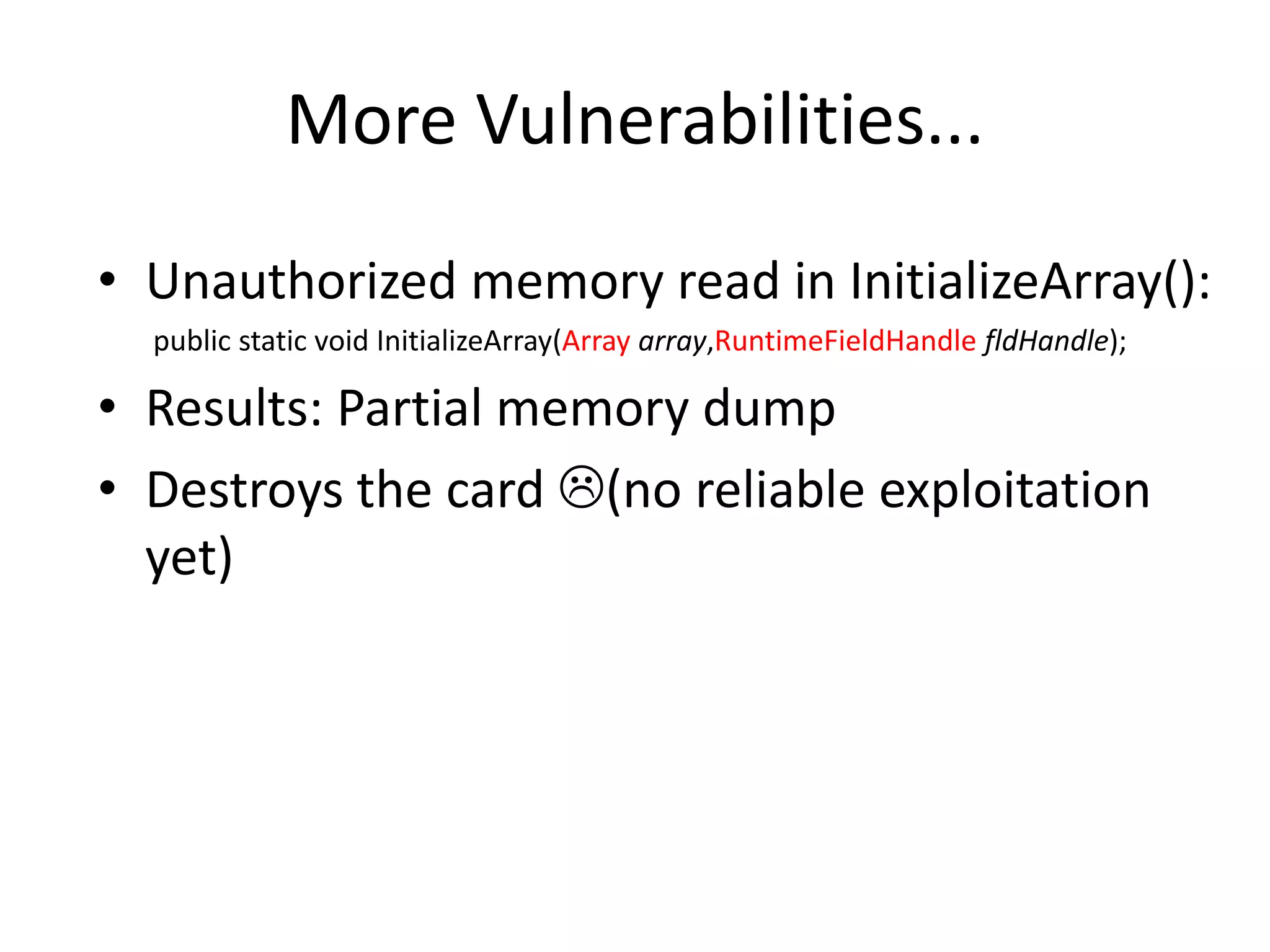
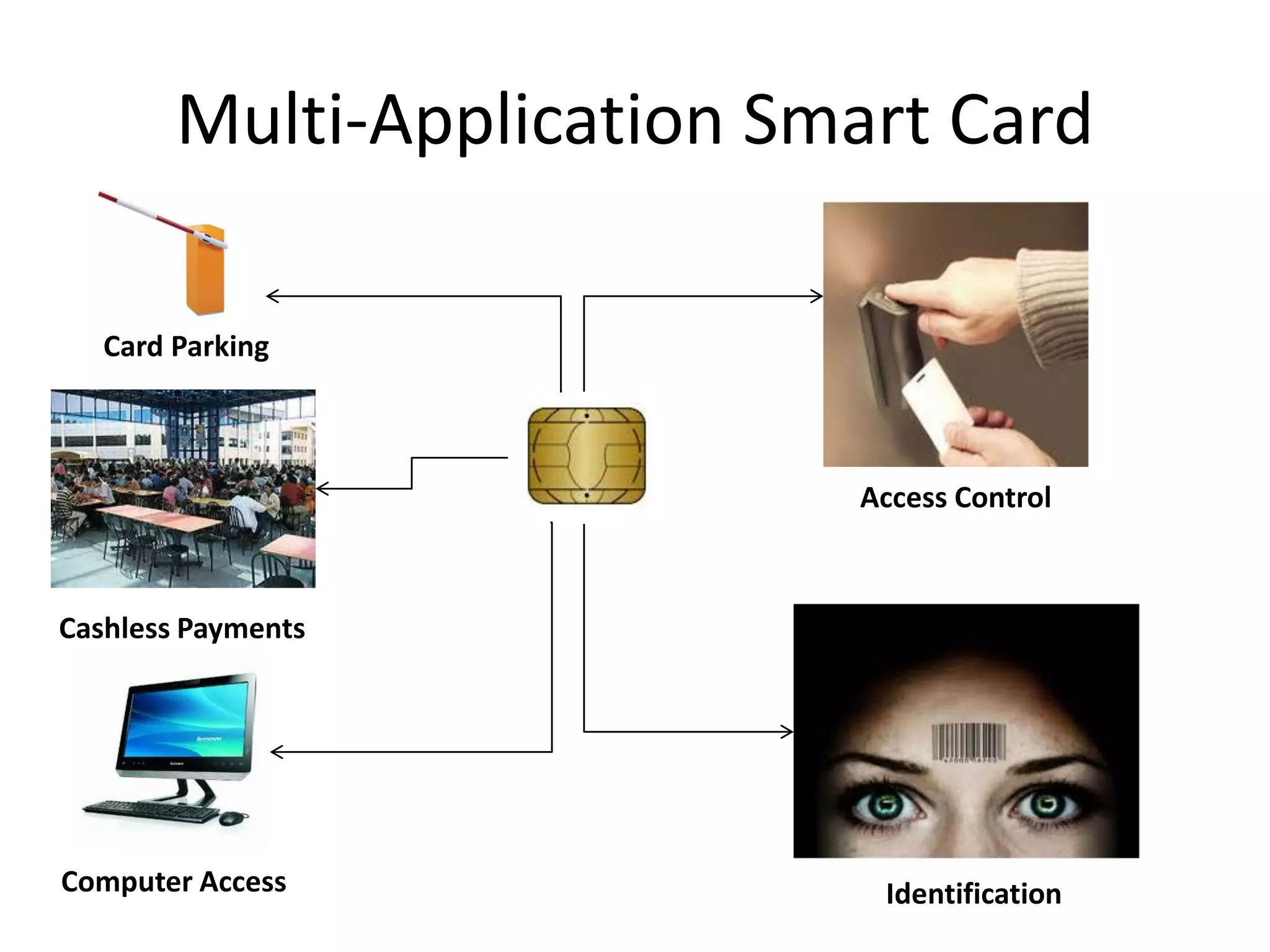
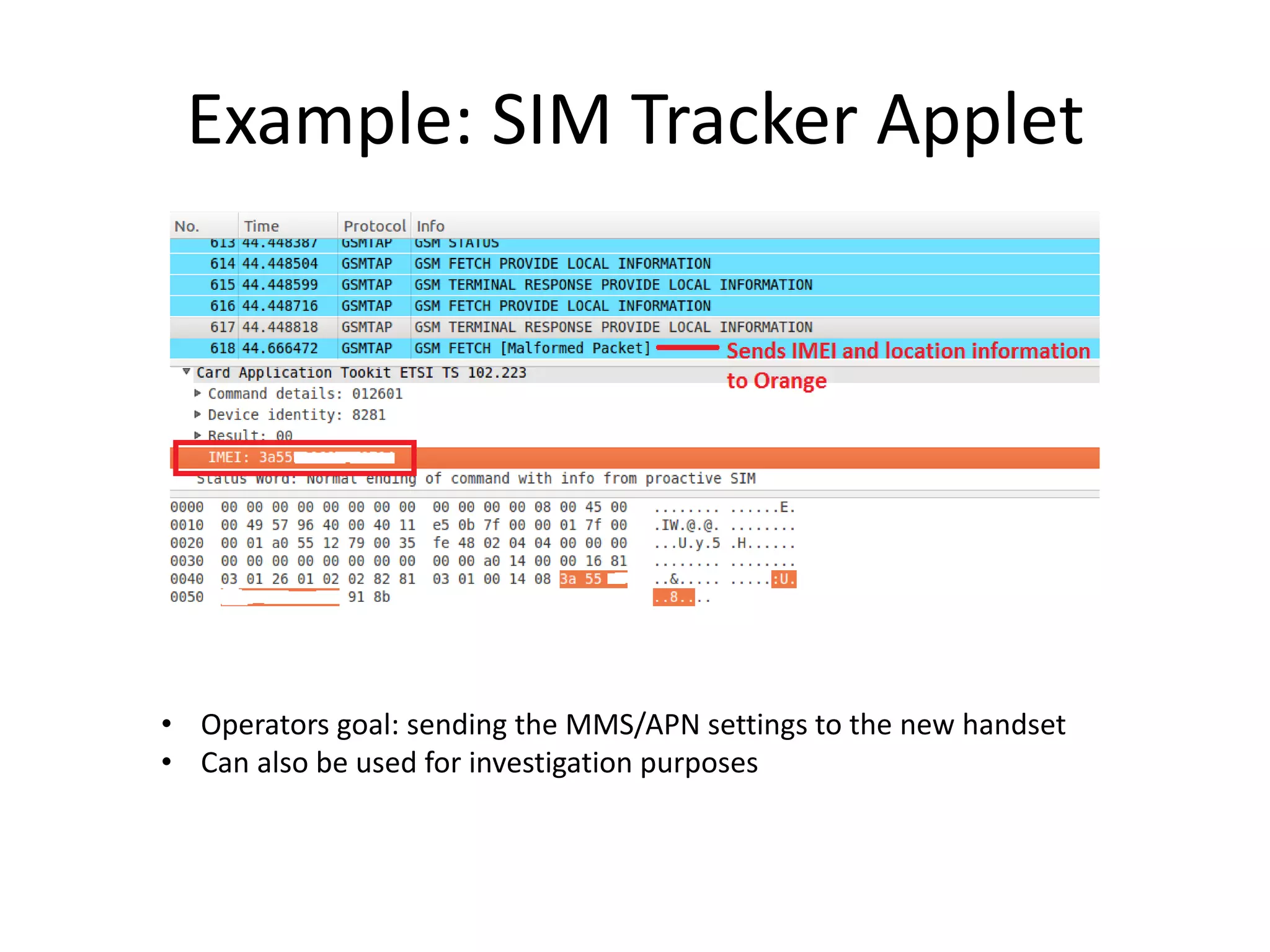
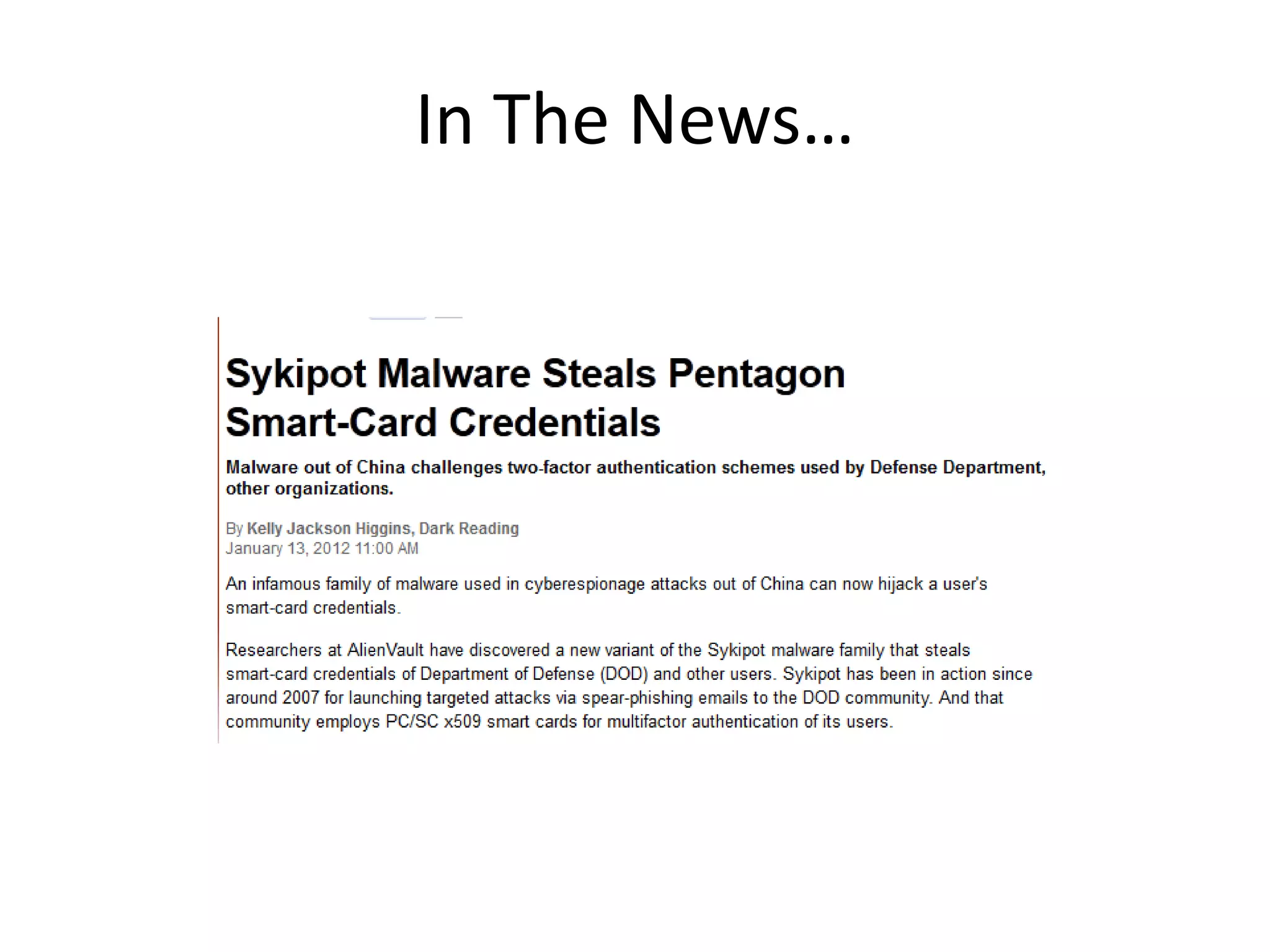
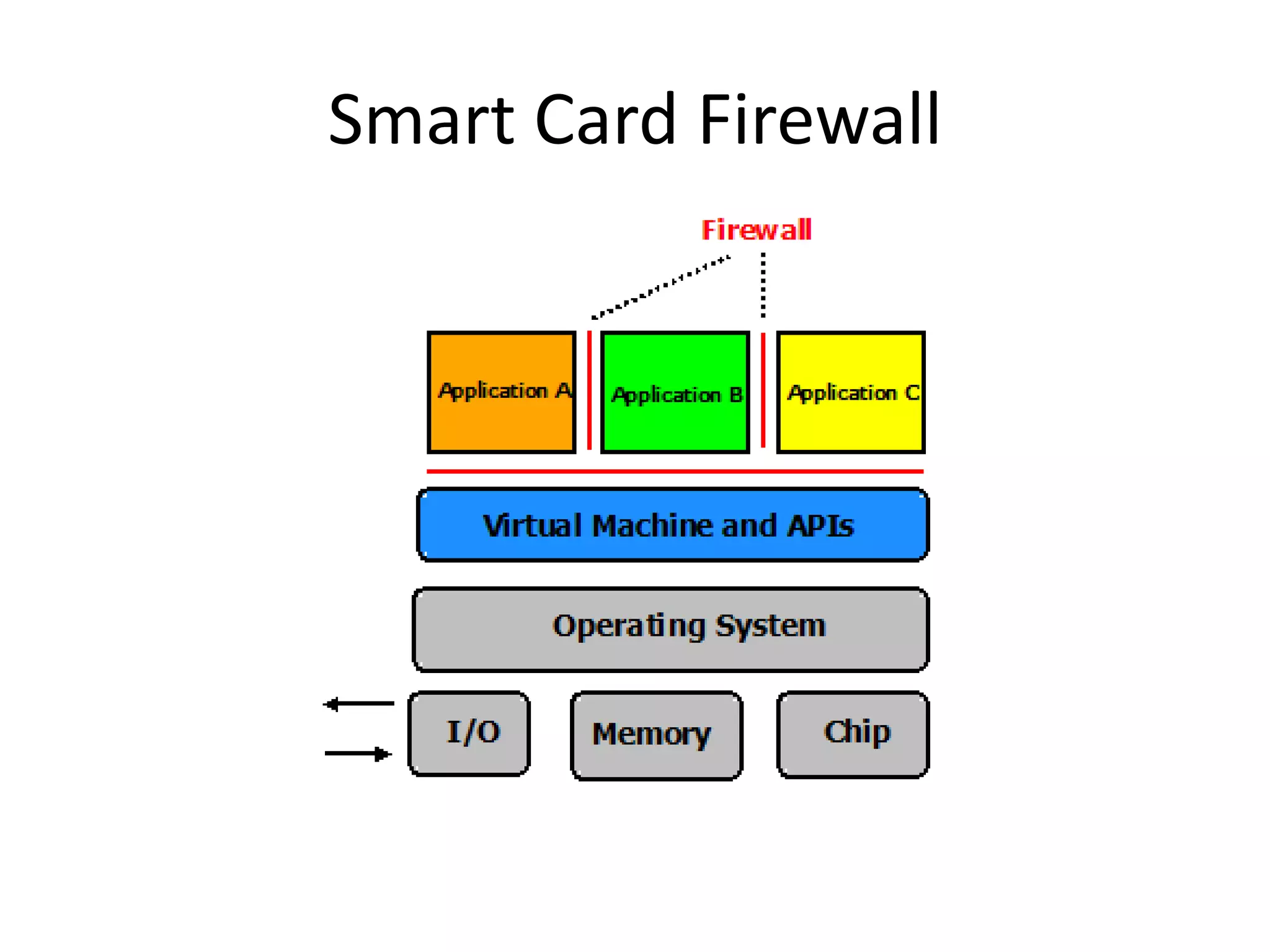
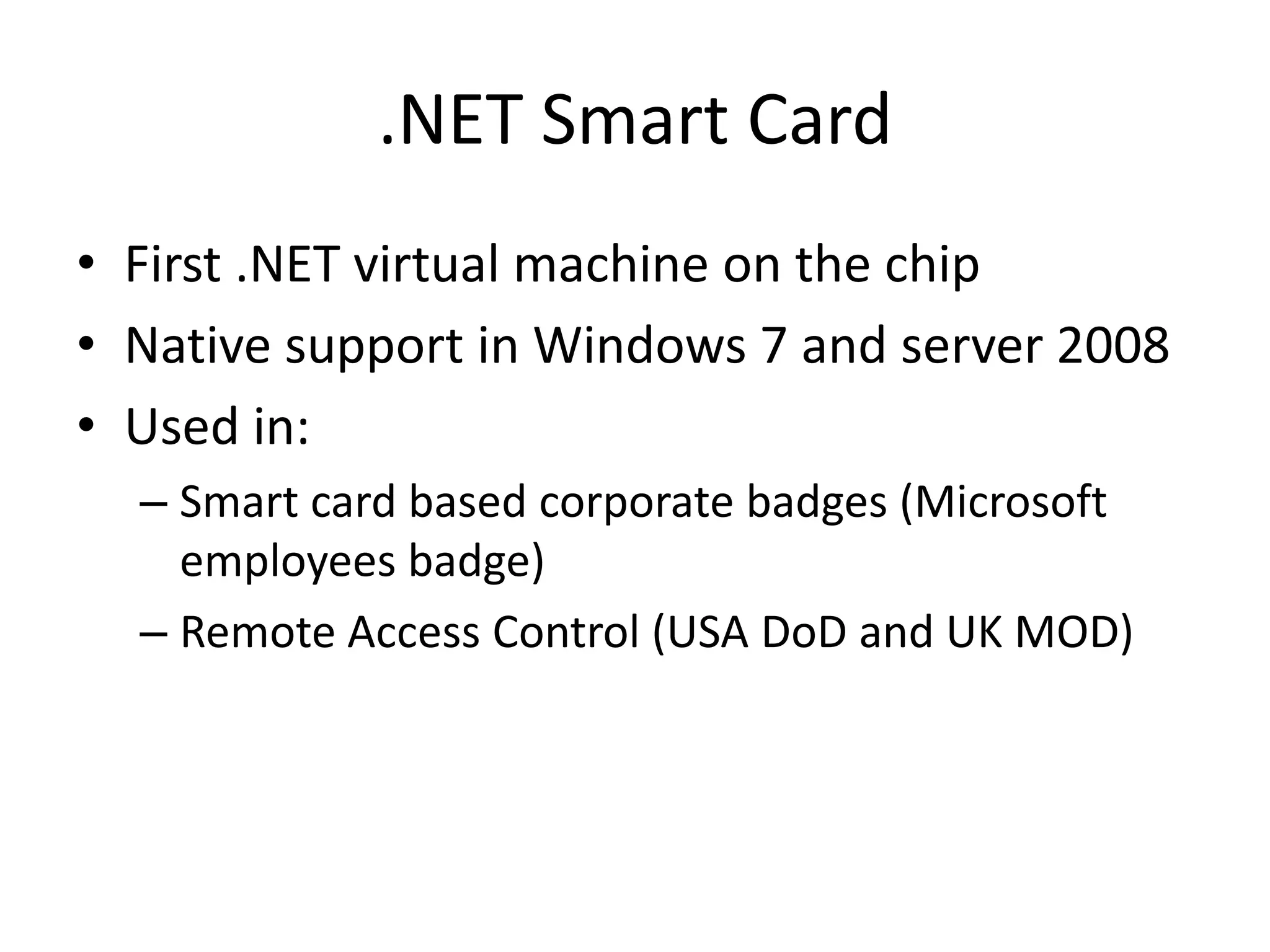
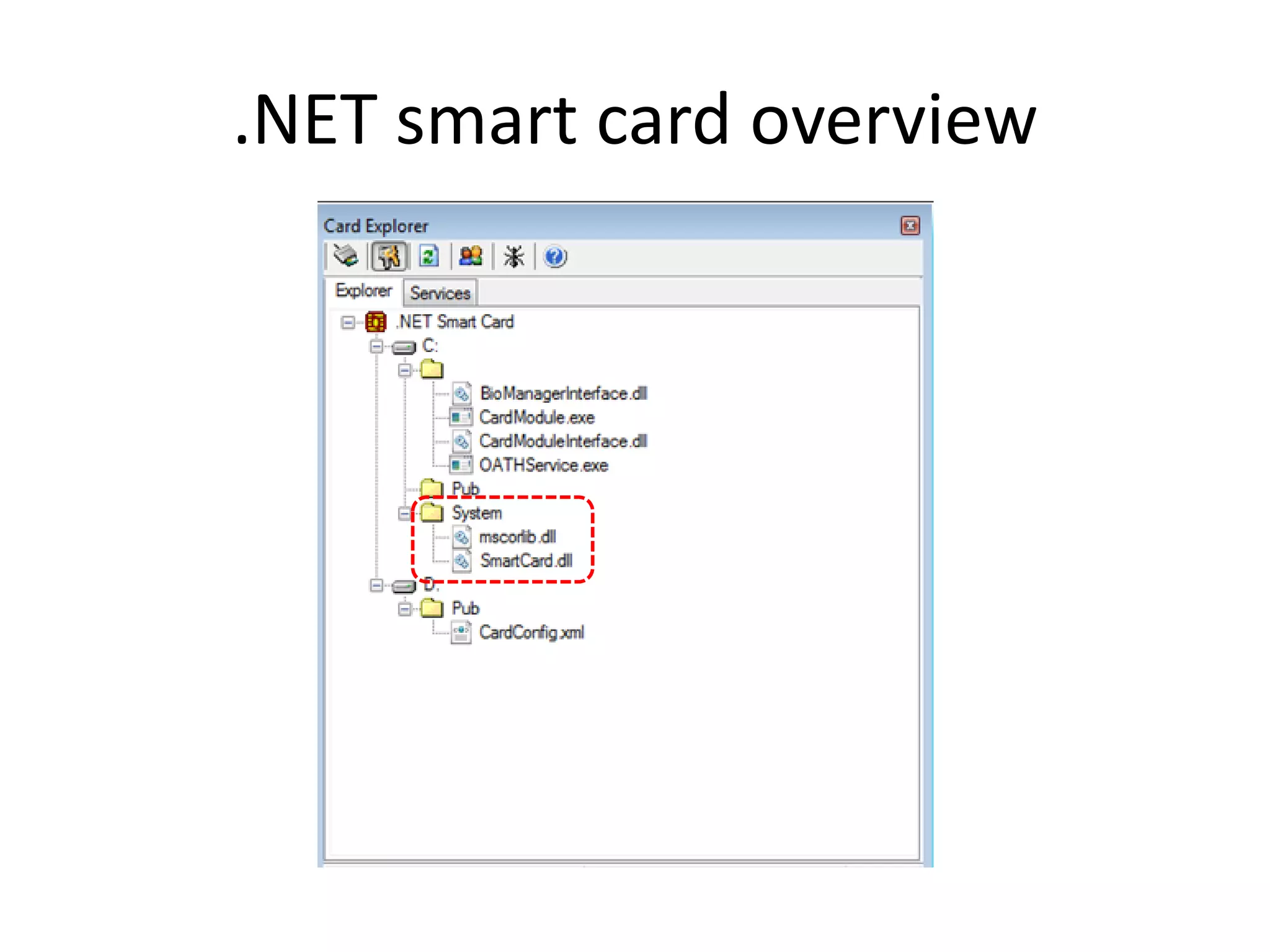
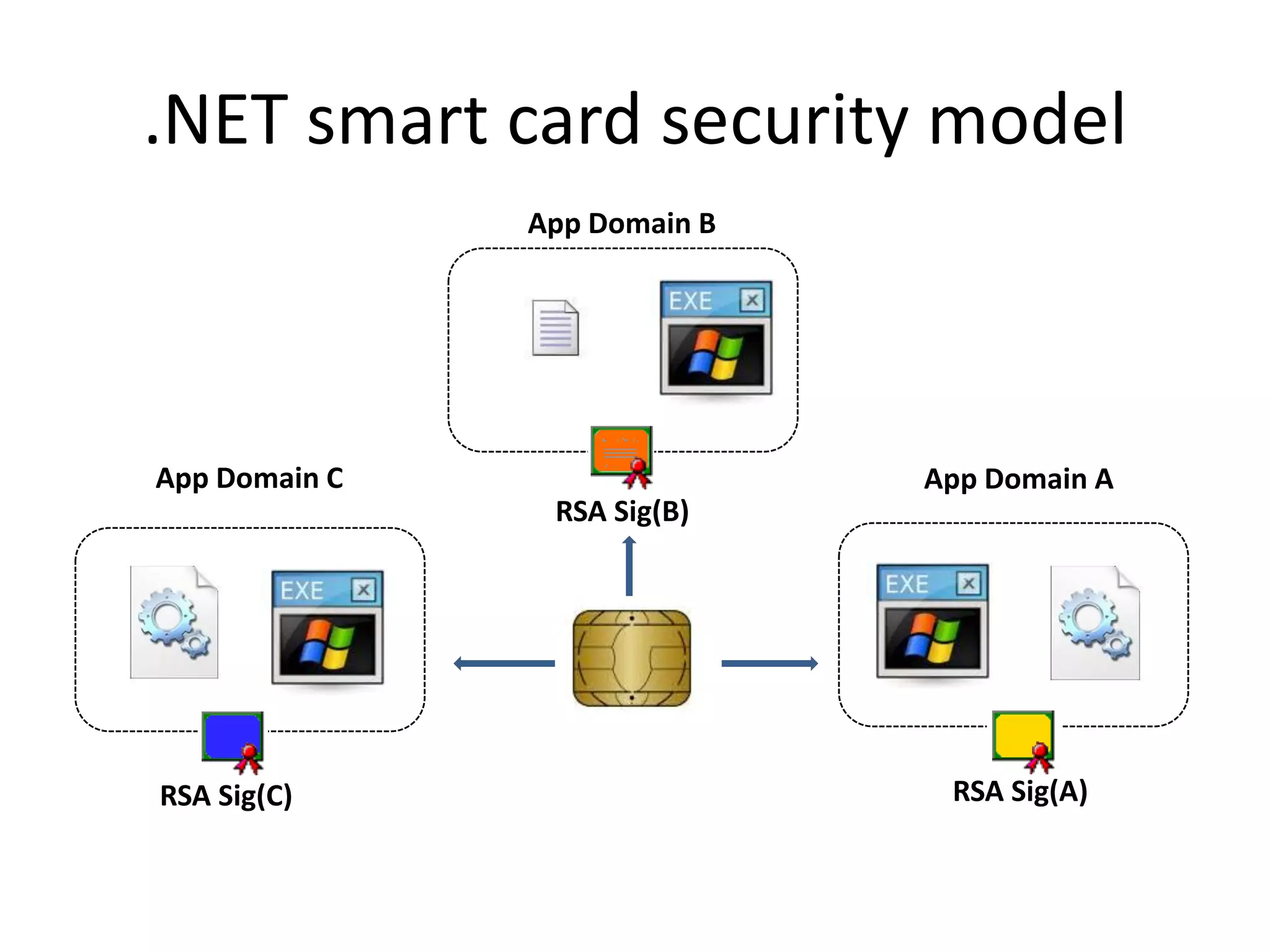
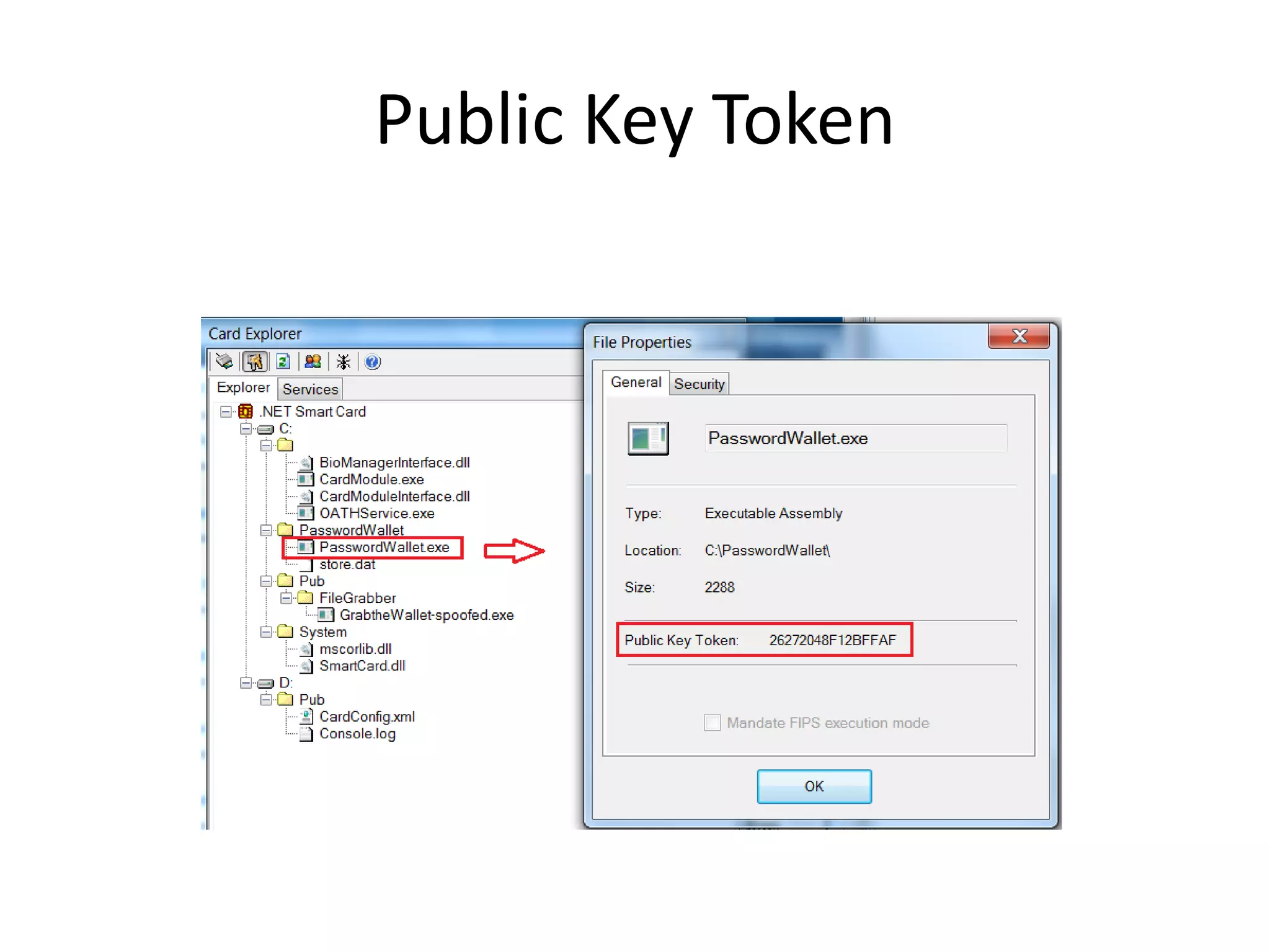
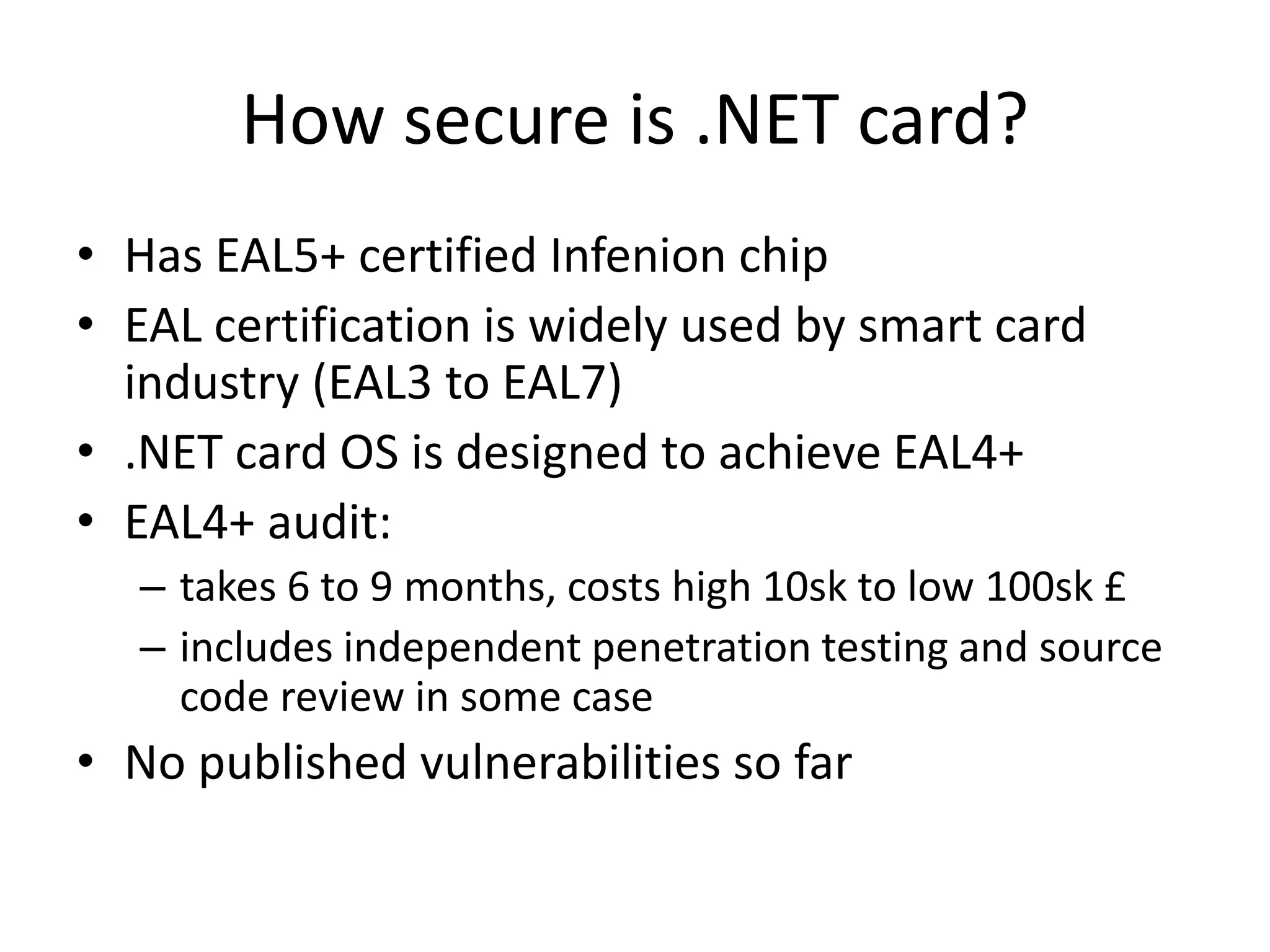
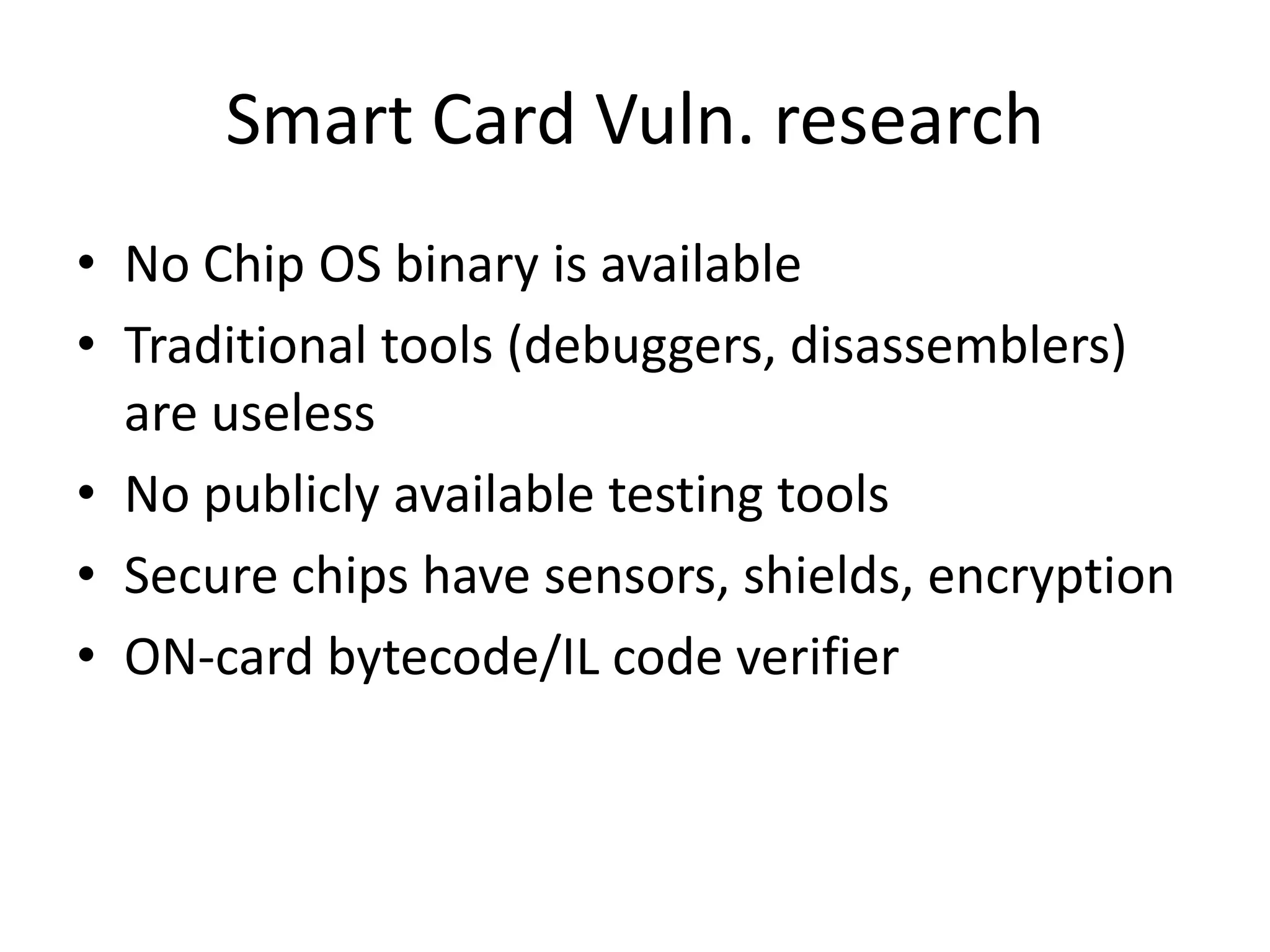
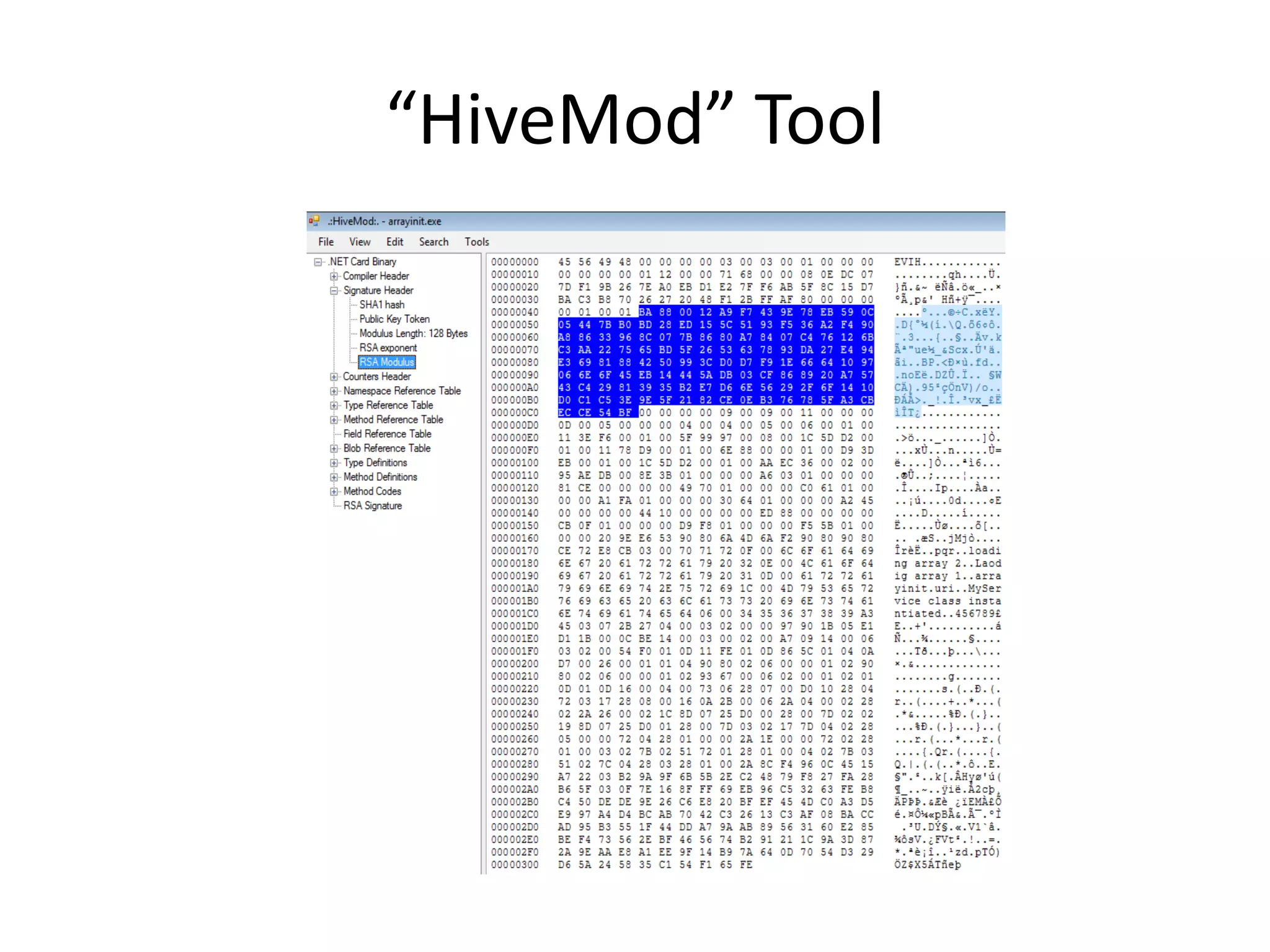
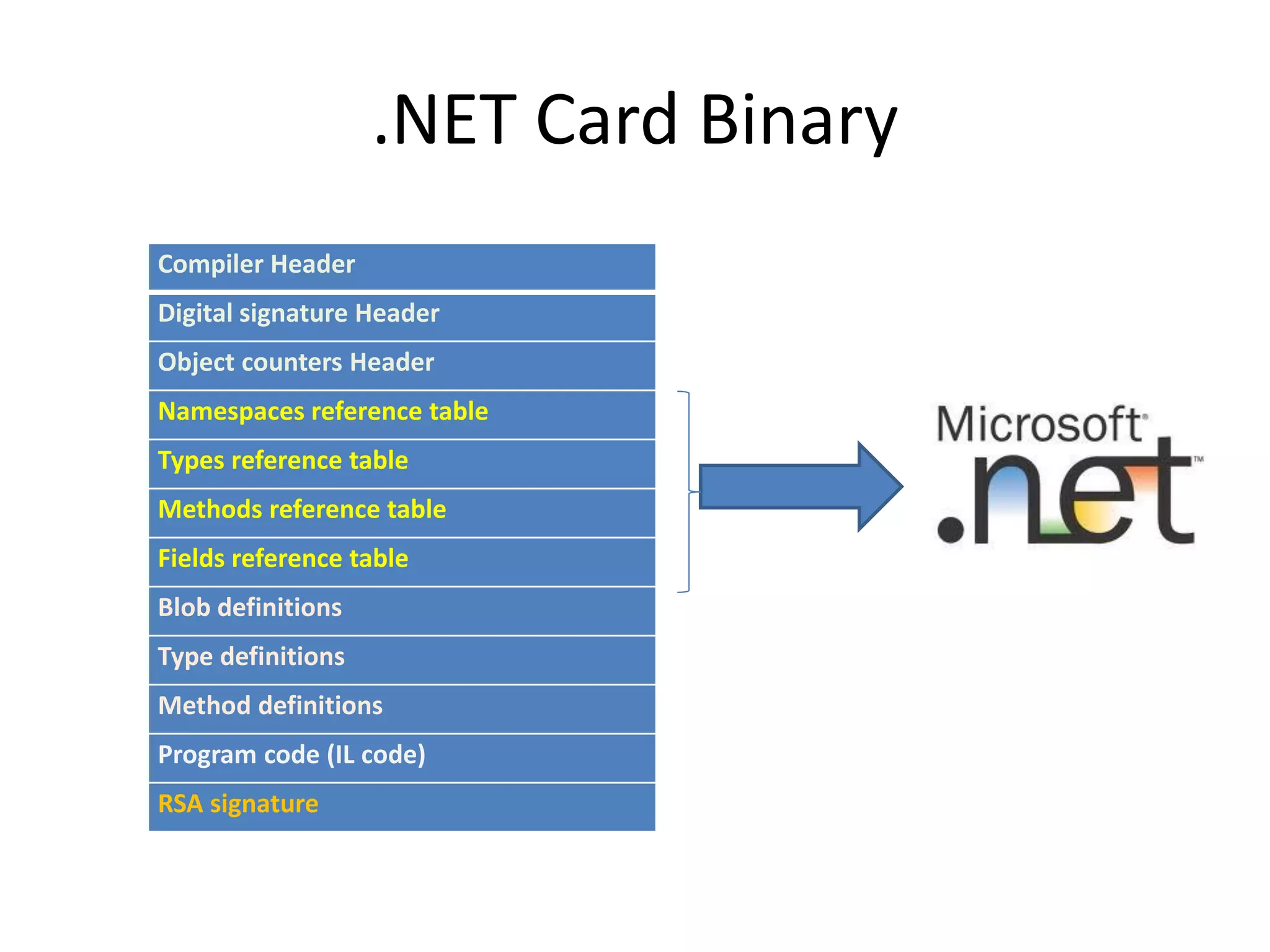
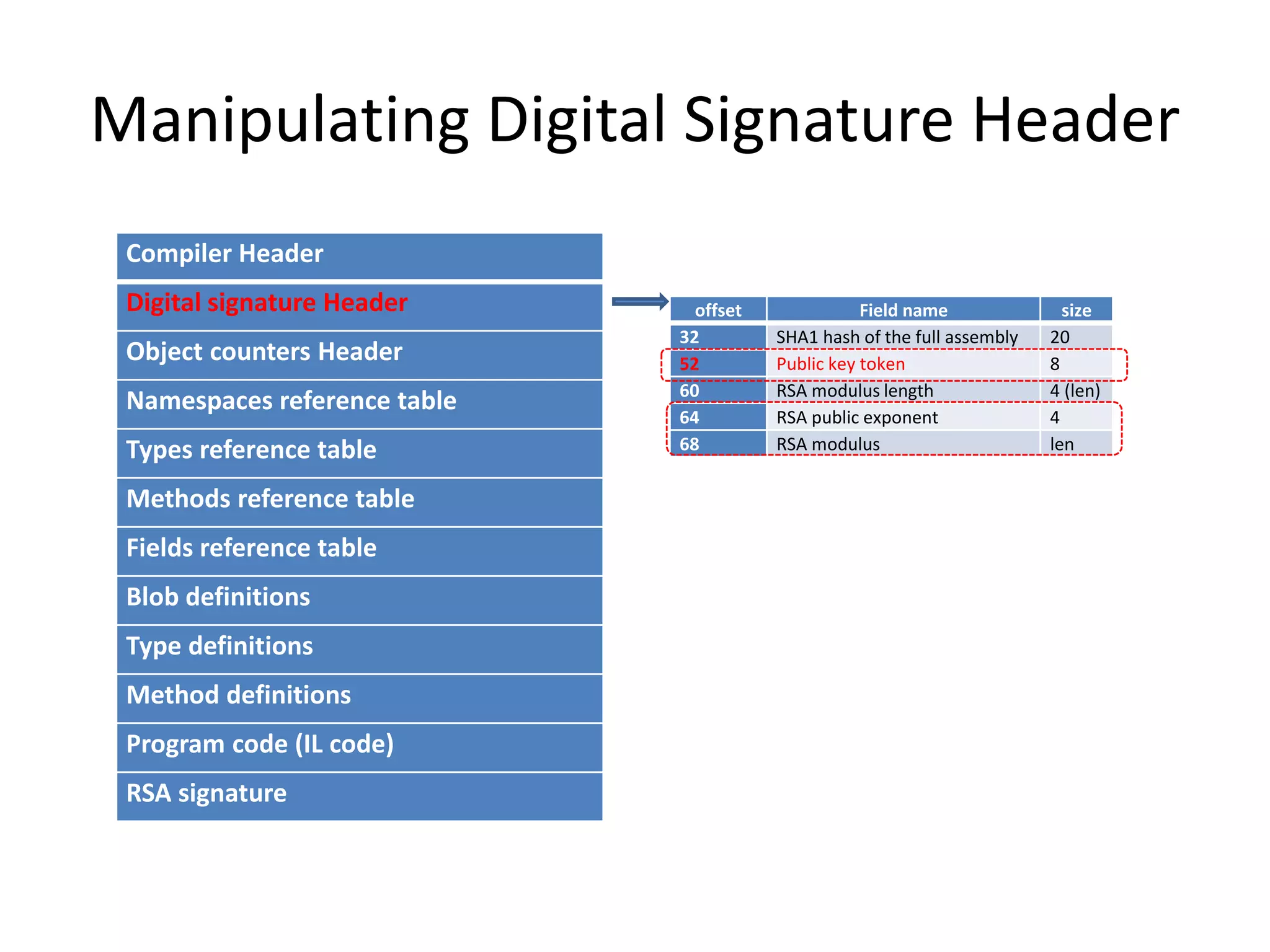
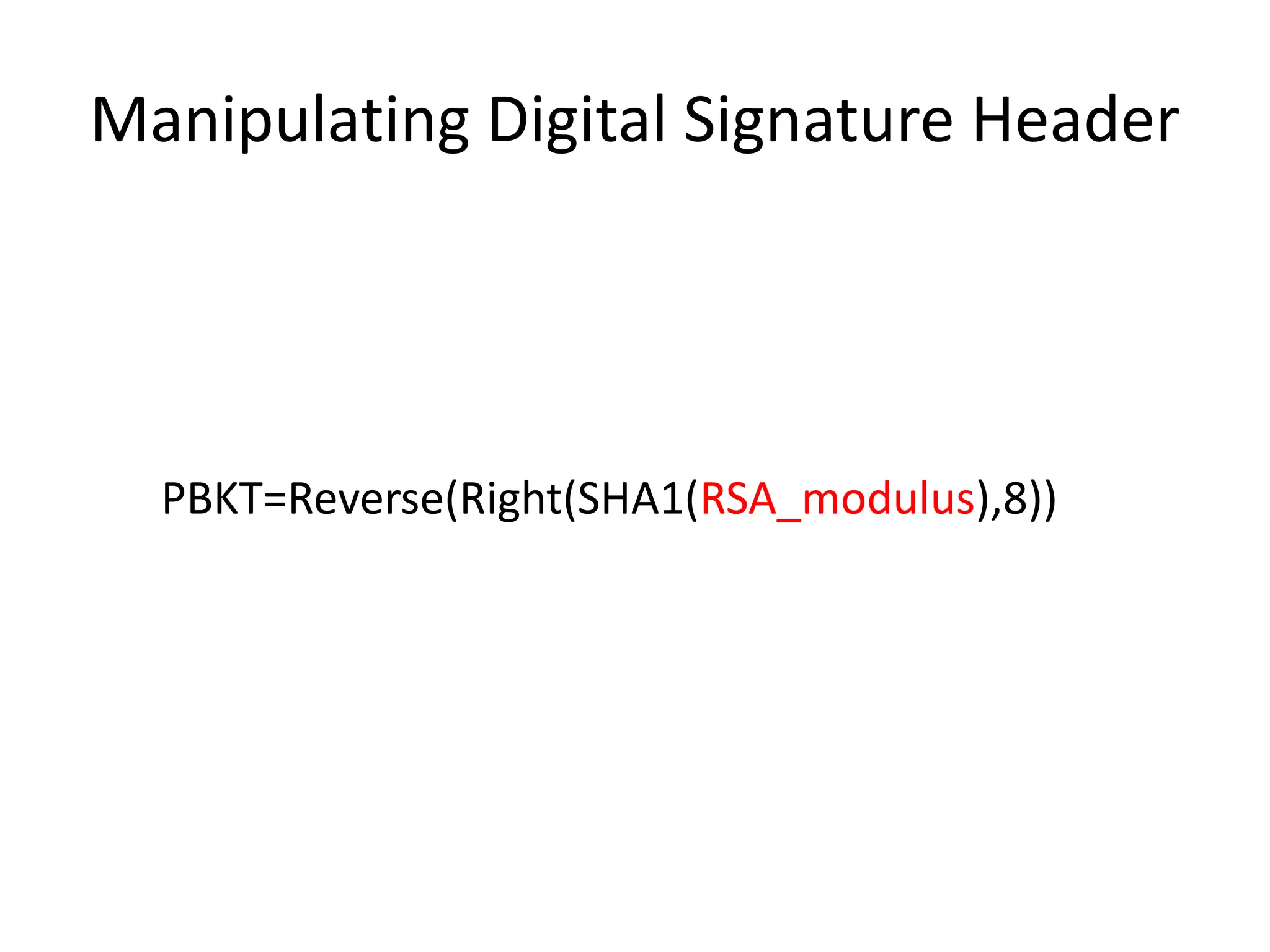
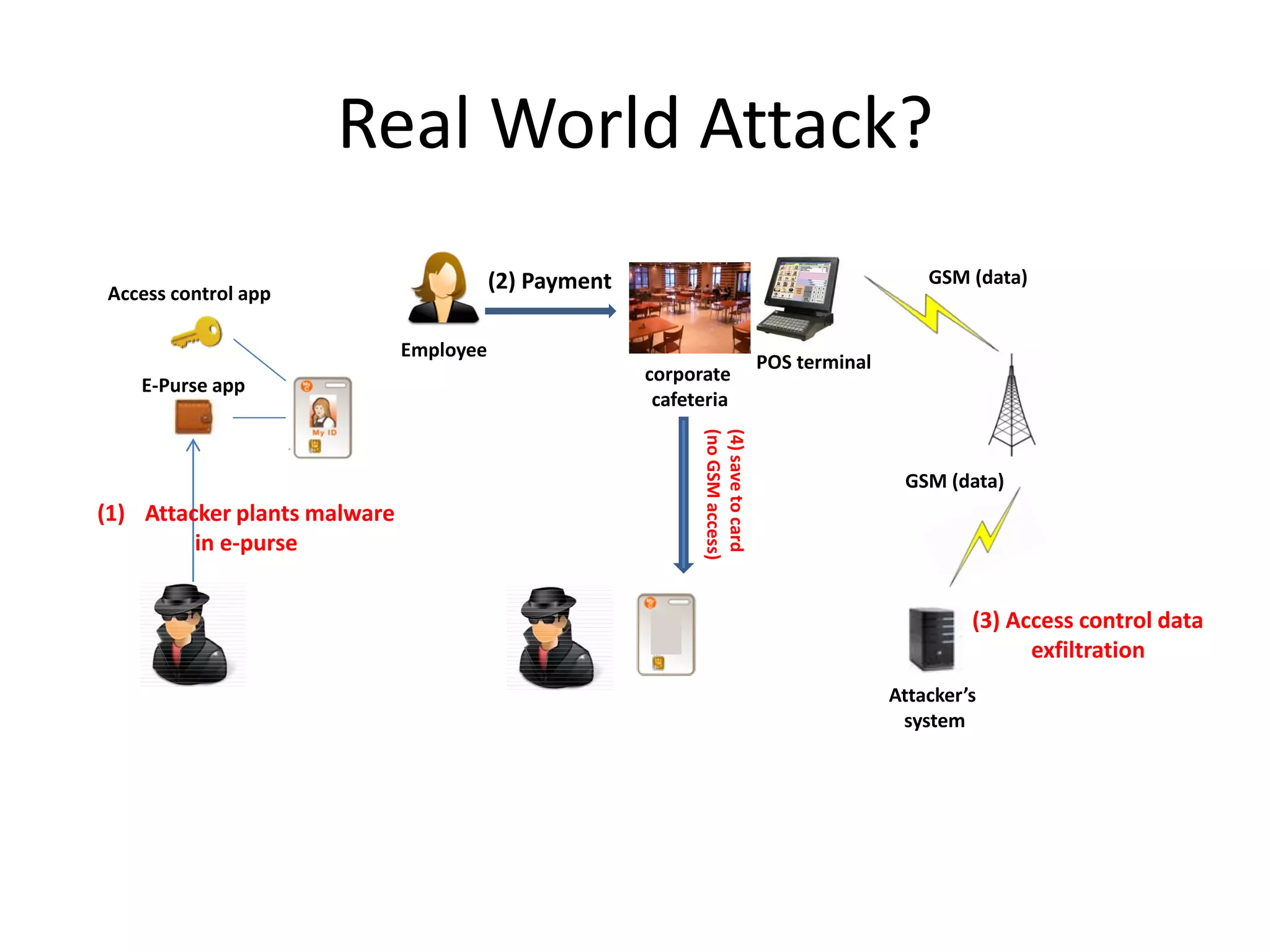
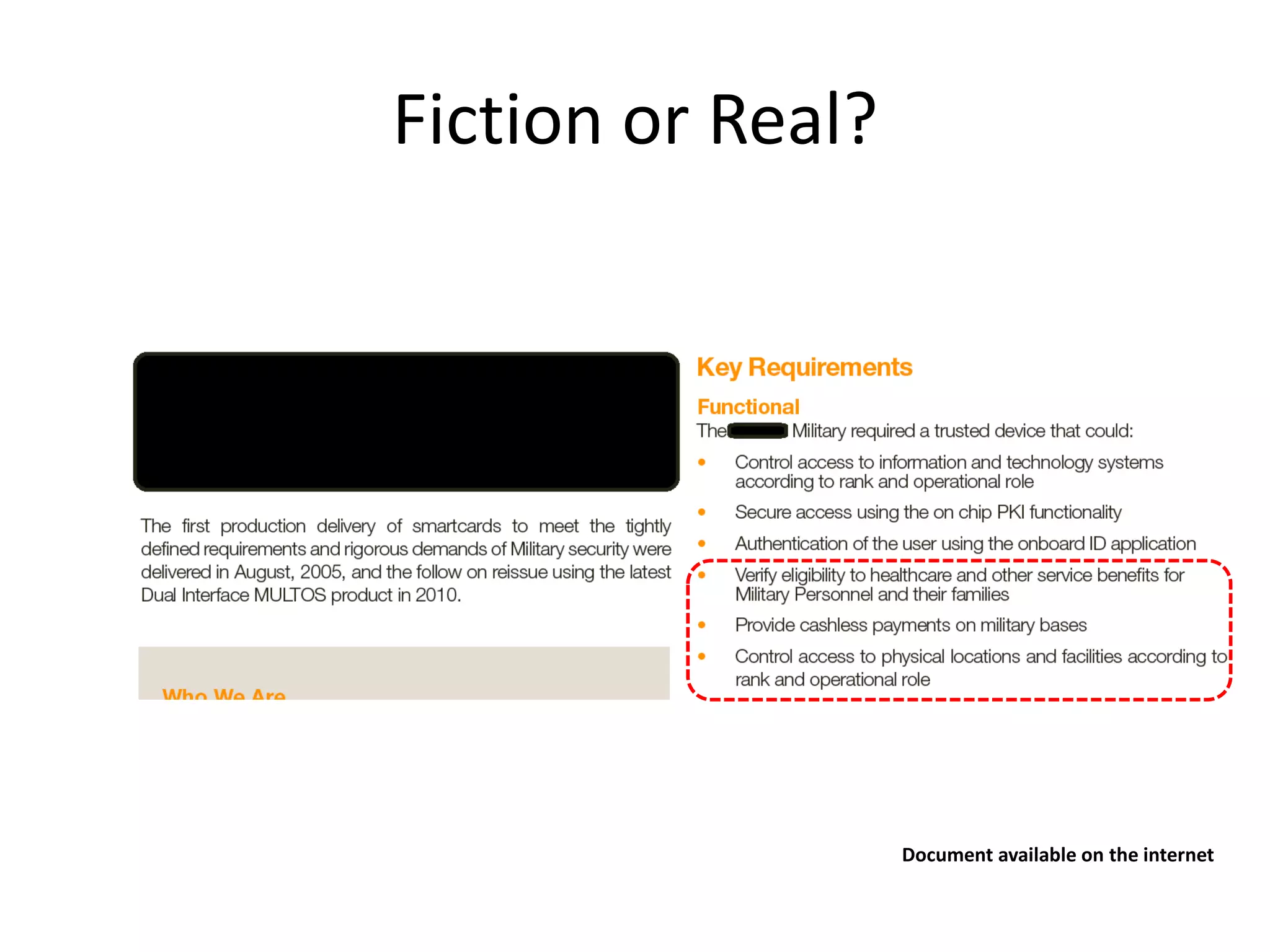
The document discusses the .NET Smart Card Operating System, highlighting its applications in various areas such as identification, access control, and cashless payments. It addresses security concerns and vulnerabilities associated with smart cards, including potential attacks and the need for penetration testing. Additionally, it introduces the hivemod tool for vulnerability research and emphasizes the importance of secure card management systems.



![Vendor’s Response
• “The targeted application must use private
file-system storage for its data to be exposed.
Therefore, internal (Application Domain)
storage is immune to such attack”.
byte[] key={0xaf,0x09,0x45,0x12,....};](https://image.slidesharecdn.com/44connetcard-120910103019-phpapp02-121011150032-phpapp02/75/Inside-NET-Smart-Card-Operating-System-44CON-2012-38-2048.jpg)