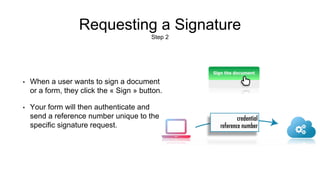
Signder is a web service that allows users to acquire handwritten signatures for forms or applications, saving the signer’s information such as timestamp and IP address. The process involves filling out a form, requesting a signature, and then capturing it using various devices before locking it for security. The service also provides examples and resources for implementing the signing functionality into applications.