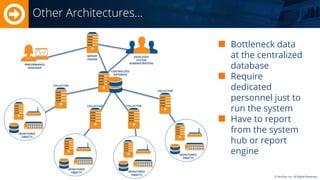
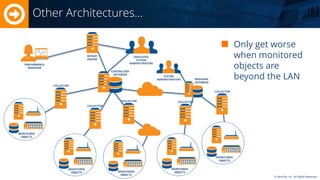
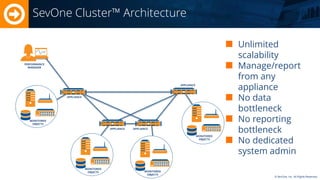
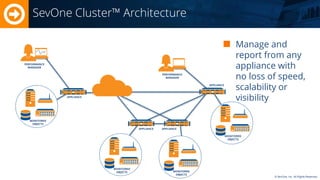
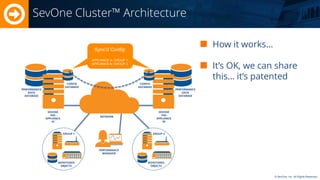
The Sevone Cluster architecture is designed to provide unlimited scalability for data collection and reporting without bottlenecks, eliminating the need for dedicated system administration. It integrates various appliances to manage and report monitored objects efficiently, maintaining speed and visibility. The architecture allows for remote management beyond local area networks (LAN) while ensuring performance data is synchronized across different appliances.