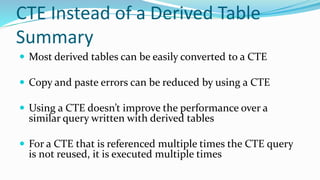
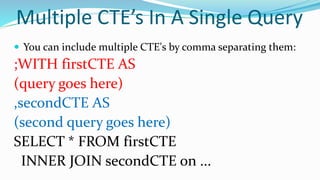
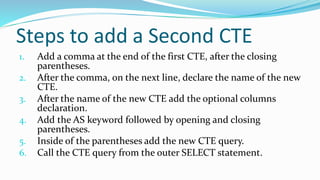
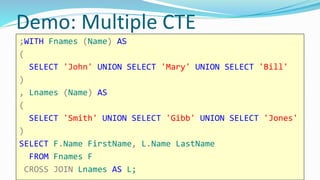
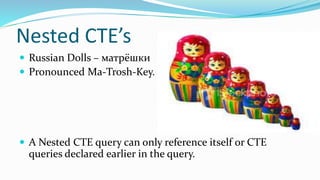
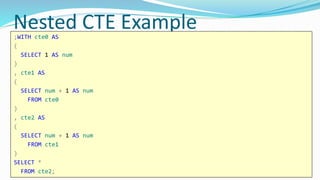
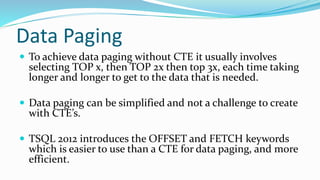
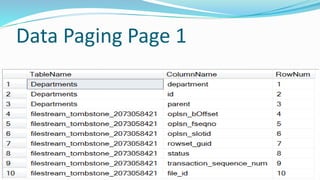
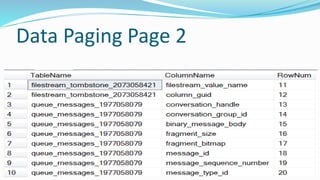
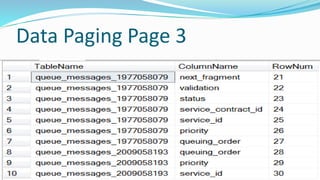
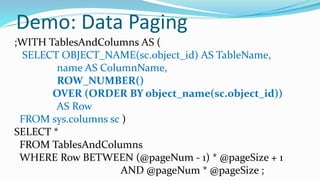
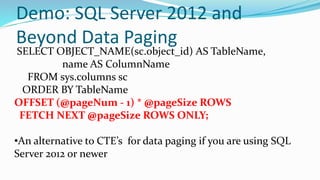
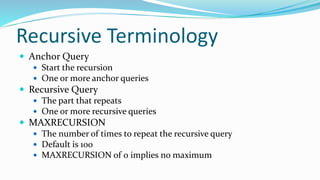
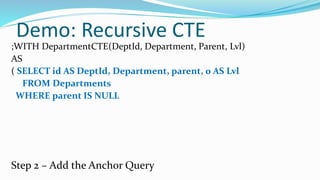
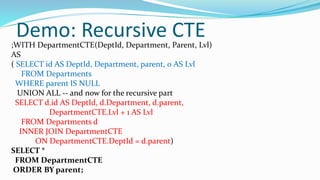
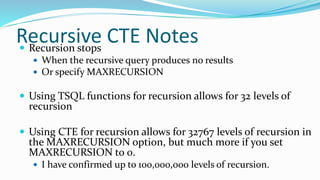
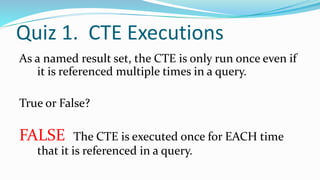
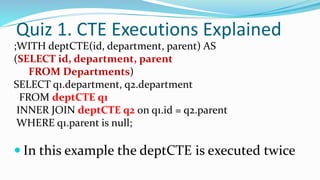
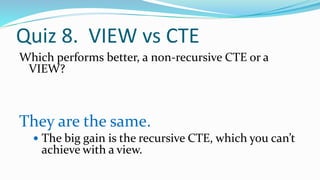
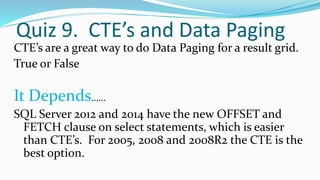
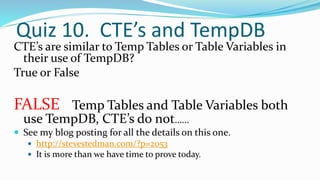
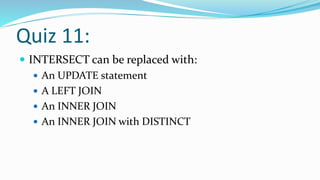
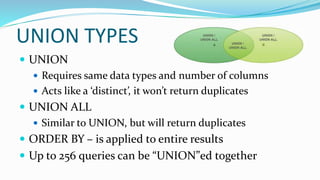
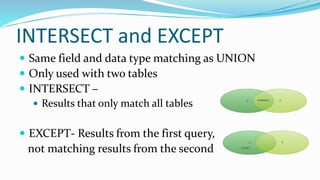
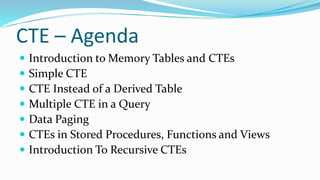
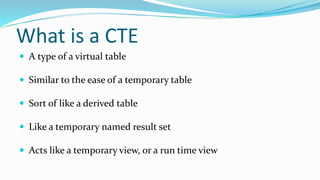
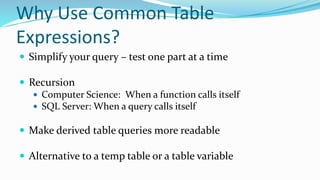
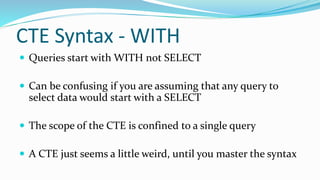
This document is a training presentation by Steve Stedman and Aaron Buma on SQL, covering topics like set operators, derived tables, common table expressions (CTEs), and recursion. It highlights the usage of CTEs, their syntax, and benefits such as simplification of queries and improved readability. The training also discusses data paging, recursion in CTEs, and multiple CTEs in a single query, along with practical examples and demos.



![ Virtual Tables
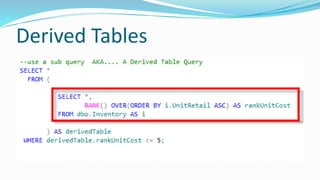
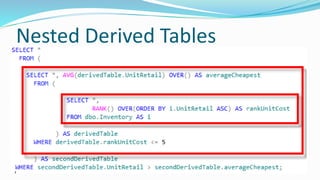
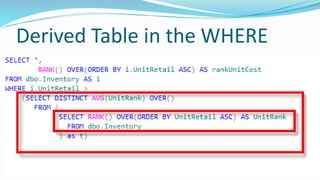
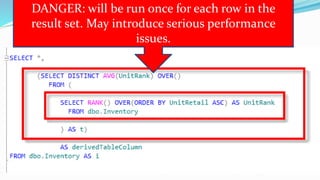
Derived Table
Sub query
Views
Temporary Named Result Set
Temp Tables
Table Variables
Common Table Expressions
Memory Tables SELECT *
FROM (SELECT id,
department,
parent
FROM Departments) as Dept;
CREATE VIEW [dbo].[DeptView]
AS
SELECT id, department, parent
FROM Departments;
GO
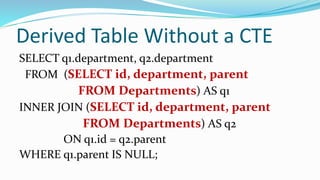
SELECT q1.department,
q2.department AS subDept
FROM DeptView q1
INNER JOIN DeptView q2
ON q1.id = q2.parent
WHERE q1.parent IS NULL;
CREATE TABLE #deptTempTable (
id int,
department VARCHAR (200),
parent int
);
DECLARE @deptTableVariable TABLE(
id int,
department VARCHAR (200),
parent int
);](https://image.slidesharecdn.com/setoperators-derivedtablesandctes-150213113055-conversion-gate01/85/Set-operators-derived-tables-and-CTEs-20-320.jpg)
![Simple CTE Syntax
;WITH expression_name [(column_name[,...n])]
AS
(
CTE_query_definition
)
SELECT <column_list>
FROM expression_name;](https://image.slidesharecdn.com/setoperators-derivedtablesandctes-150213113055-conversion-gate01/85/Set-operators-derived-tables-and-CTEs-25-320.jpg)