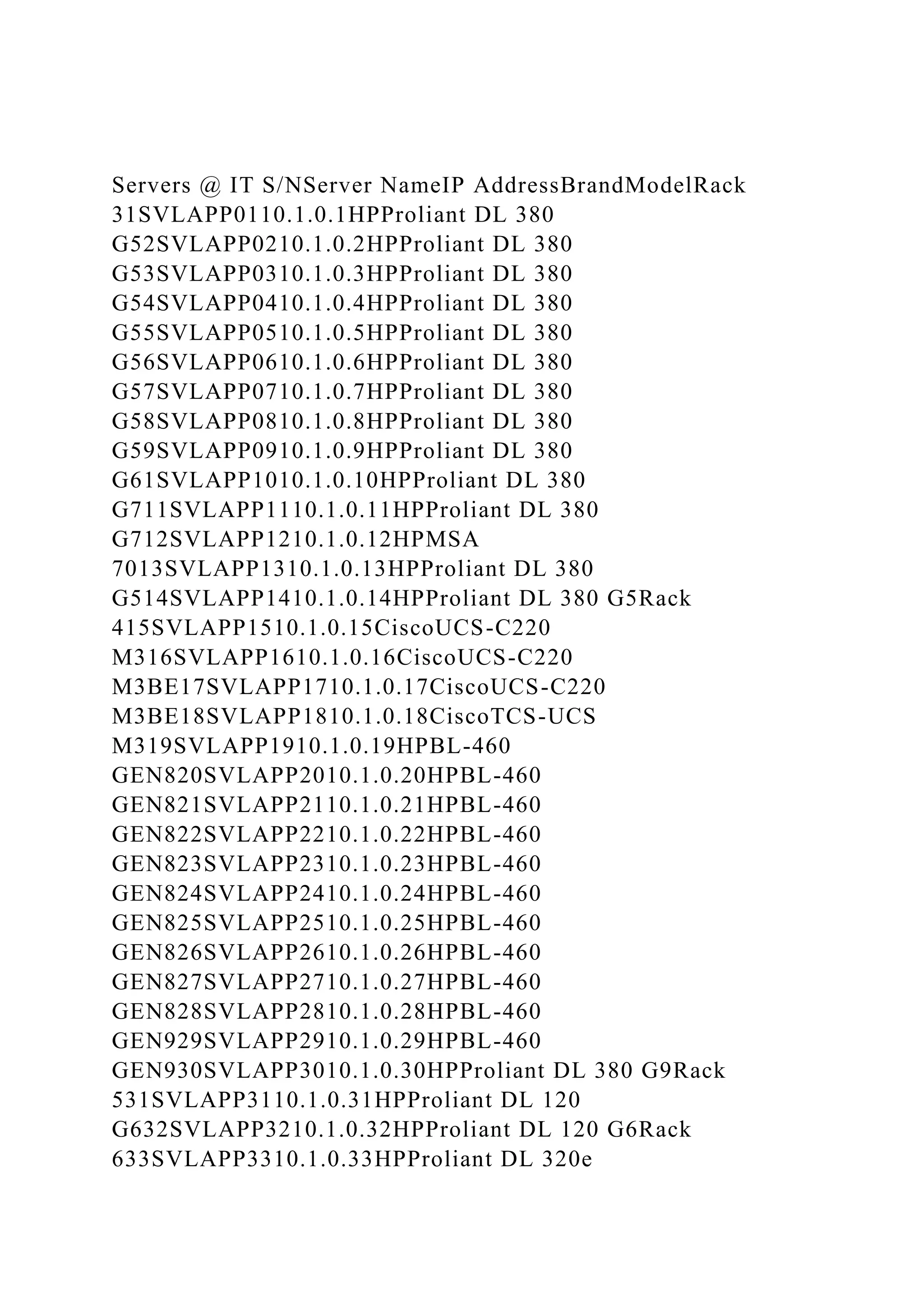
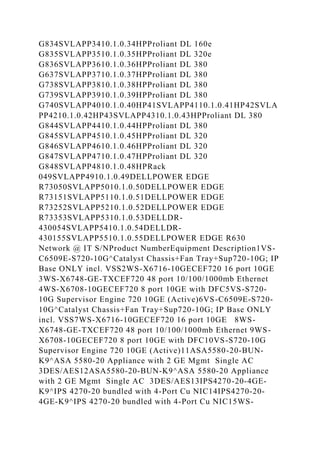
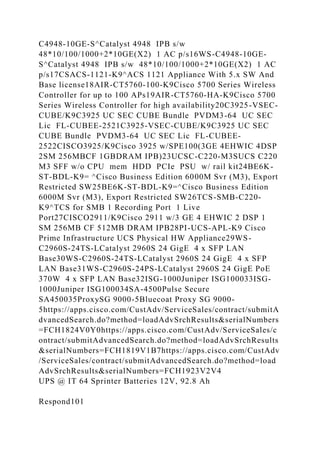
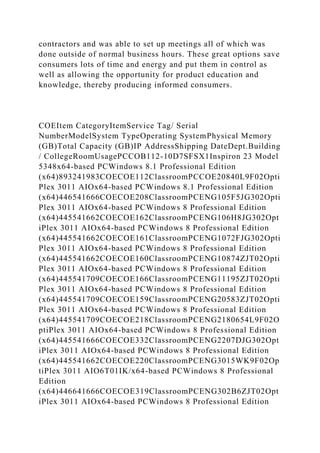
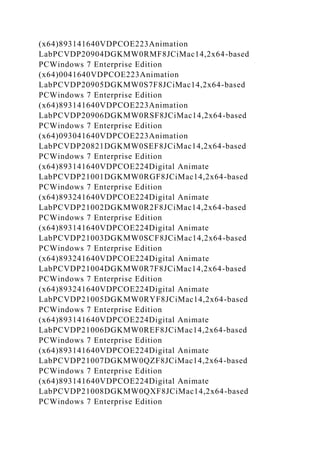
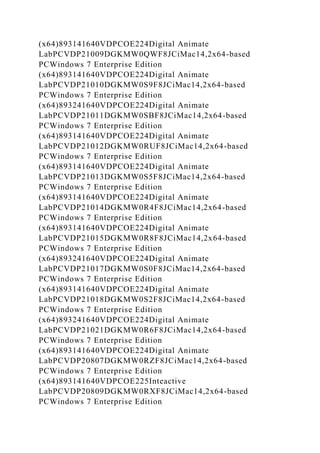
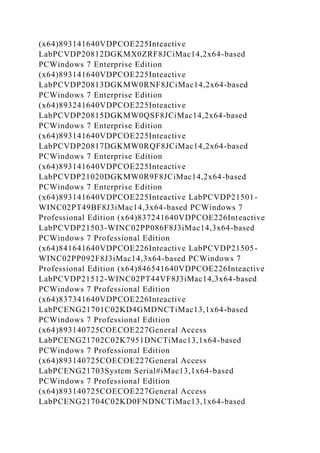
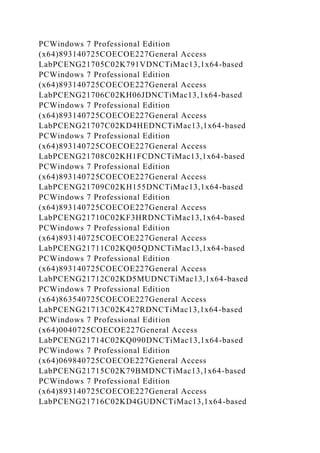
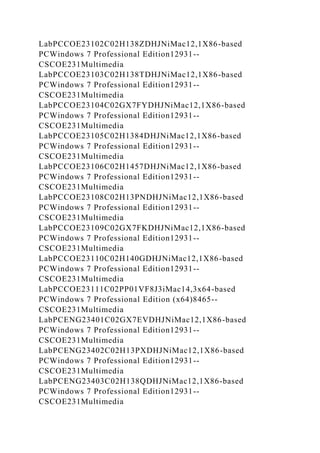
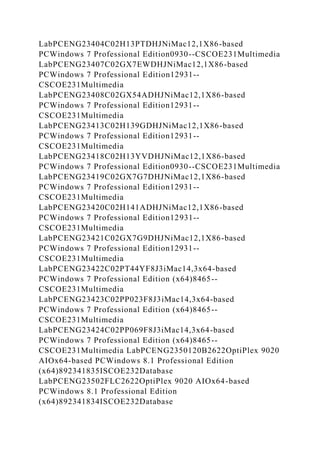
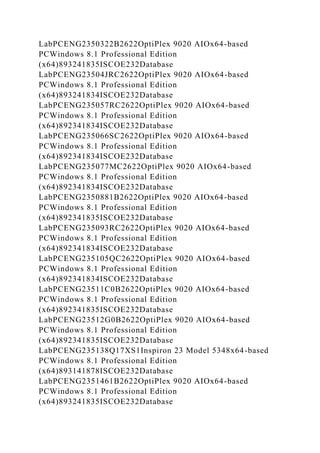
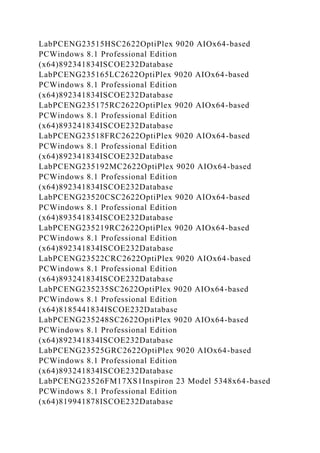
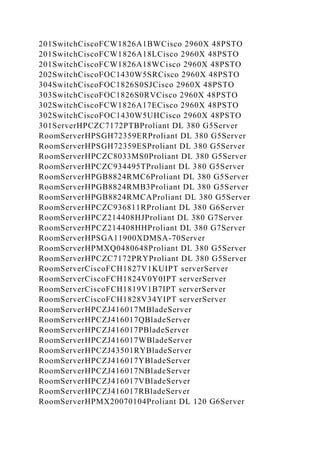
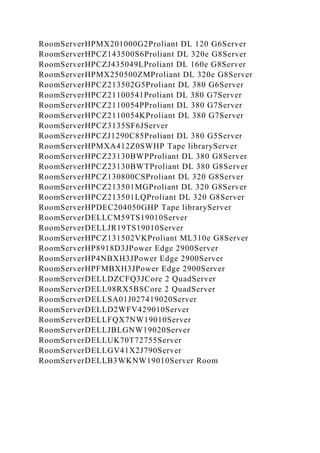
The document lists various servers and network equipment along with their specifications, including IP addresses, brands, models, and system types. It highlights the shift from traditional personal selling to modern, technology-driven approaches where consumers utilize online platforms to drive purchasing decisions. Additionally, it provides examples of classroom technology and offers insights into changes in consumer behavior due to digital trends.