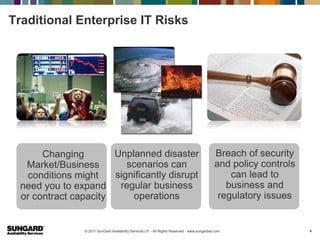
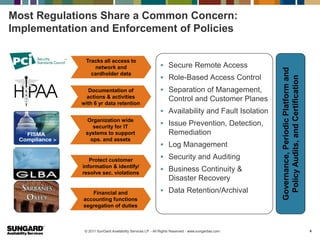
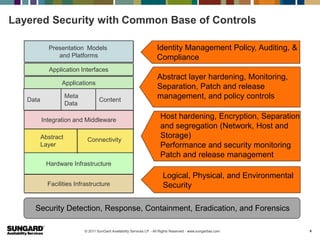
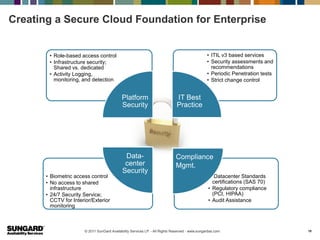
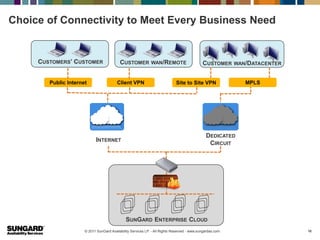
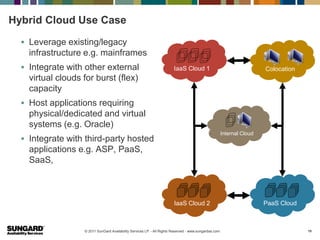
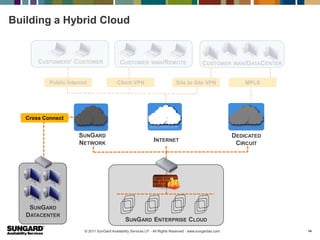
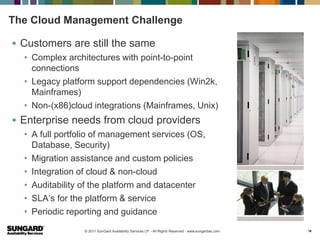
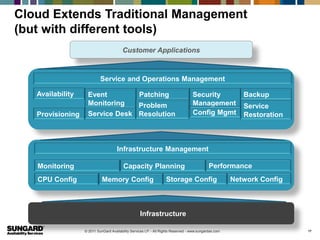
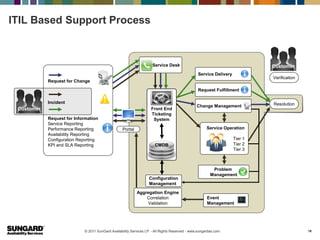
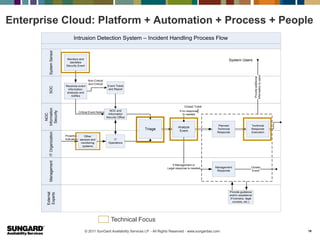
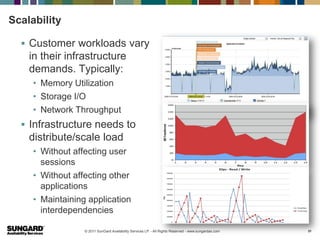
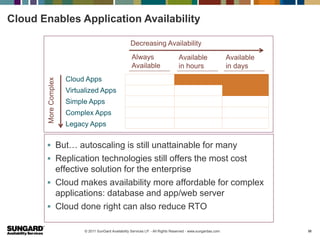
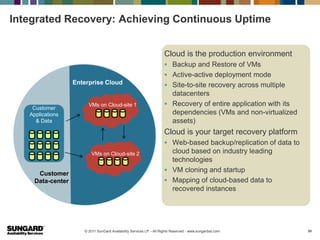
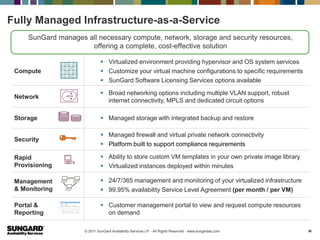
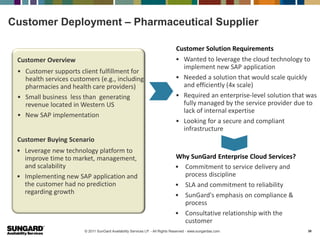
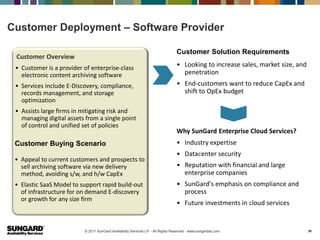
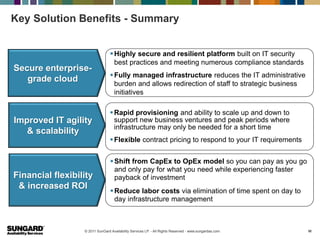
The document discusses the secure enterprise cloud and addresses some key risks of cloud computing. It outlines how security, compliance, connectivity and availability challenges in the cloud are similar to traditional enterprise IT risks. It then describes how a secure cloud foundation can be created for enterprises by implementing security best practices like role-based access control, activity logging and infrastructure security. Finally, it discusses how hybrid cloud models can be used to leverage existing infrastructure and integrate internal, external and third-party cloud applications and services.