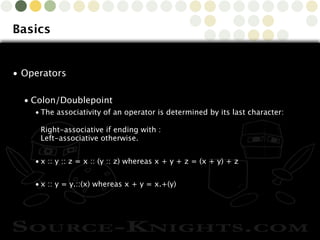
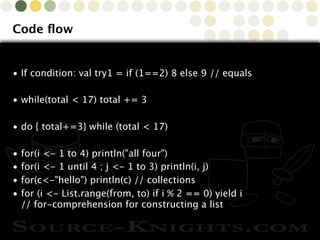
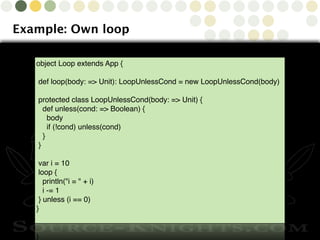
This document provides an overview of the Scala programming language. It covers Scala basics like data types, tuples, exceptions, modifiers, special types, and operators. It also discusses code flow constructs, classes, traits, functions, and matching. The document outlines additional Scala features like collections, generics, implicits, and streams. It concludes by mentioning an upcoming Agile conference in London and providing contact information for questions.




• Special syntax: tuple with x1, ..., xn can be written (x1, ..., xn)
• Example:
• def divmod(x: Int, y: Int) = new Tuple2[Int, Int](x / y, x % y)](https://image.slidesharecdn.com/scala-131002021033-phpapp01/85/Scala-A-brief-tutorial-5-320.jpg)
![Copyright © 2010 Source-Knights.com
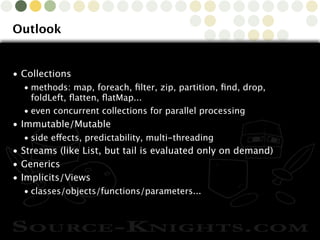
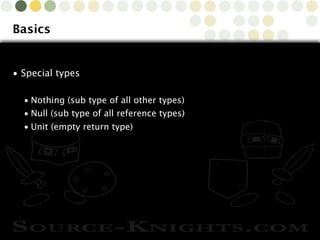
Basics
• Exceptions
• no checked exceptions in Scala
• use throws annotation such that Java code can catch exception
• @throws(classOf[IOException])](https://image.slidesharecdn.com/scala-131002021033-phpapp01/85/Scala-A-brief-tutorial-6-320.jpg)
![Copyright © 2010 Source-Knights.com
Basics
• Modifiers
• Annotations, each on their own line (lower case name), some
java ones might be upper case
• Override modifier (override)
• Access modifier (protected, private)
(also with [packagenames, classnames or this]
• Final modifier (final)](https://image.slidesharecdn.com/scala-131002021033-phpapp01/85/Scala-A-brief-tutorial-7-320.jpg)
![Copyright © 2010 Source-Knights.com
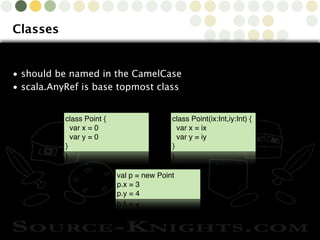
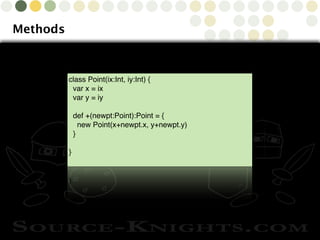
Classes
// precondition, triggering an IllegalArgumentException
require(y > 0, "y must be positive")
// auxiliary constructor
def this(x: Int) = { ... }
// private method
private def test(a: Int): Int = { ... }
// allow access to package/subpackages/classes
protected[packagename] def test2(a: Int): Int = { ... }
// allow access to subclasses but only same instance
protected[this] def test3(a: Int): Int = { ... }
// overridden method
override def toString = { member1 + ", " + member2 }](https://image.slidesharecdn.com/scala-131002021033-phpapp01/85/Scala-A-brief-tutorial-13-320.jpg)
![Copyright © 2010 Source-Knights.com
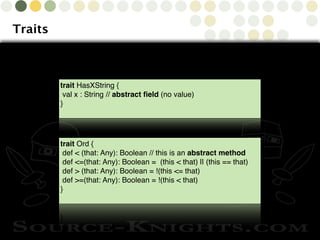
Traits
class Date(y: Int, m: Int, d: Int) extends Ord {
def year = y
def month = m
def day = d
//Implement the abstract trait method
def <(that: Any): Boolean = {
if (!that.isInstanceOf[Date]) error("cannot compare”)
val o = that.asInstanceOf[Date]
// latest expression is return value
(year < o.year) || (year == o.year && (month < o.month ||
(month == o.month && day < o.day)))
}](https://image.slidesharecdn.com/scala-131002021033-phpapp01/85/Scala-A-brief-tutorial-16-320.jpg)
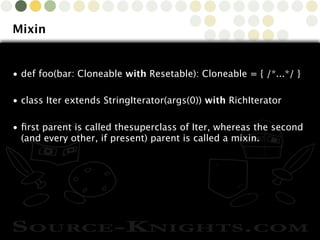
 {...}
// Uses the defaults
val m1 = new HashMap[String,Int]
// initialCapacity 20, default loadFactor
val m2= new HashMap[String,Int](20)
// overriding both
val m3 = new HashMap[String,Int](20,0.8)
// override only the loadFactory via
// named arguments
val m4 = new HashMap[String,Int](loadFactor = 0.8)](https://image.slidesharecdn.com/scala-131002021033-phpapp01/85/Scala-A-brief-tutorial-20-320.jpg)
![Copyright © 2010 Source-Knights.com
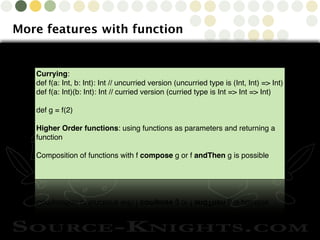
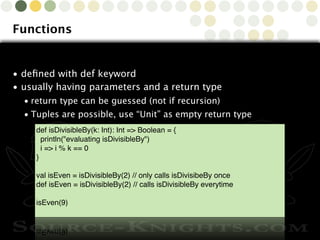
Functions
• Functions are technically an object with an apply method
• val func = (x) => x + 1 // creates a function object
• def func = (x) => x + 1 // creates a function (or method in
class context)
• A Function is a set of traits
• Specifically, a function that takes one argument is an instance
of a Function1 trait.
scala> object addOne extends Function1[Int, Int] {
def apply(m: Int): Int = m + 1 }
defined module addOne
A nice short-hand for extends Function1[Int, Int] is extends (Int => Int)](https://image.slidesharecdn.com/scala-131002021033-phpapp01/85/Scala-A-brief-tutorial-22-320.jpg)
![Copyright © 2010 Source-Knights.com
Functions
//Anonymous functions
(x: Int) => x + 1
val addOne = (x: Int) => x + 1
// Function as parameter
filter(lst, (x:String) => x.length() > 3)
def filter(inLst:List[Int],cond:(Int)=>Boolean):List[Int]={
if(inLst==Nil) Nil
else if(cond(inLst.head)) inLst.head::filter(inLst.tail,cond)
else filter(inLst.tail,cond)
}](https://image.slidesharecdn.com/scala-131002021033-phpapp01/85/Scala-A-brief-tutorial-23-320.jpg)