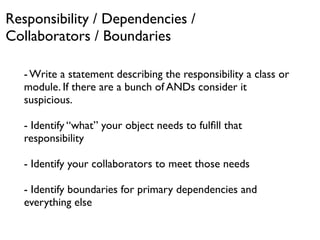
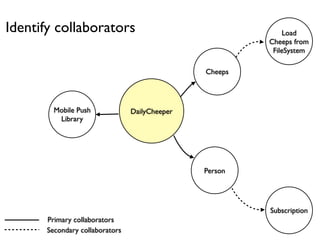
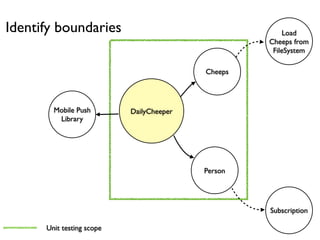
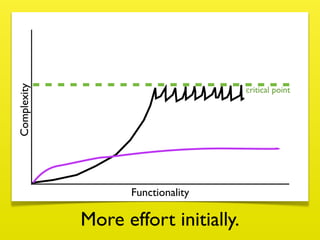
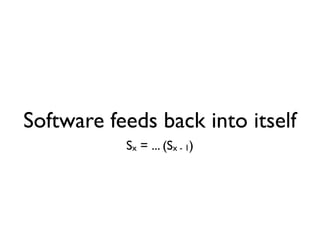
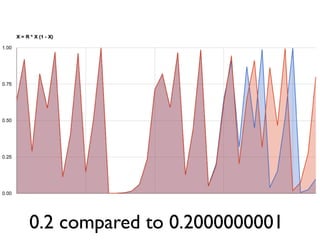
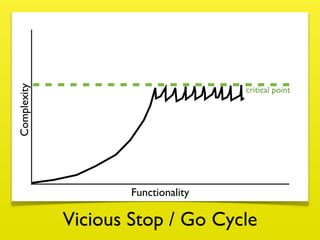
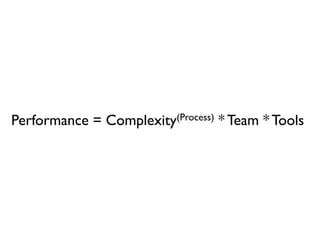
Sand Piles and software systems can both reach a critical point where small perturbations can cause large changes or failures. To prevent reaching this critical point, software needs to be designed and developed in a way that dampens complexity through practices like optimizing decision pathways, balancing responsibilities across components, and keeping dependencies loose. Reflection on processes and values is important for continuously improving software quality and stability over time.

























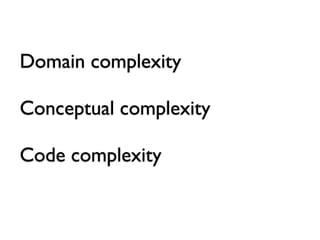

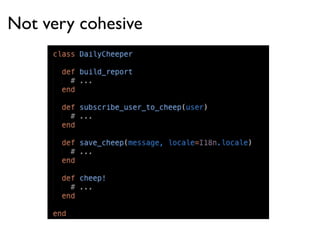
![Cohesion
the focus of an individual software component
given its function or purpose to exist
Array#push Cheeper#delivery_daily Cheeps#load
Array#pop Cheeper#delivery_weekly Cheeps#add
Array#[] Cheeper#deliver_monthly Cheeps#save
Array#count Cheeps#remove
Array#<<](https://image.slidesharecdn.com/sandpiles-and-software-madison-ruby-2012-120825180356-phpapp01/85/Sand-Piles-and-Software-Madison-Ruby-Conference-42-320.jpg)