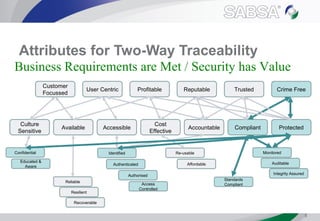
The document outlines the offerings and benefits of SABSA courses as an exclusive training partner in eCrime and information security, particularly in Abu Dhabi. It highlights the global reach of SABSA's certified architects, their methodology, and the various applications of their security architecture framework. The document also announces upcoming training opportunities in Dubai and Abu Dhabi, emphasizing the importance of aligning business requirements with security measures.