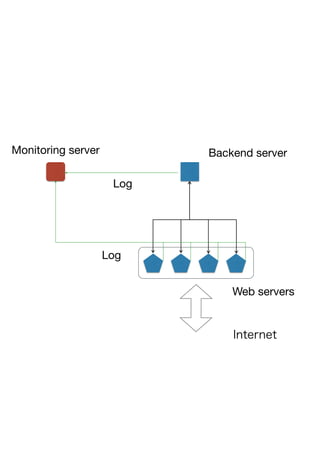
This document summarizes a runtime verification framework that monitors network applications using CSP (Communicating Sequential Processes) notation. It currently implements a monitor for system calls in dtruss output to check if open and close calls are matched. The goals are natural concurrency notations, integration with web servers, databases and syslog. Future work includes completing the file descriptor model, improving error reporting, and interfacing with Fluentd for log parsing.