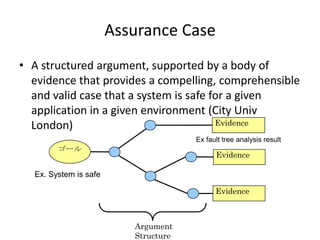
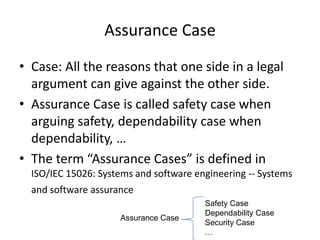
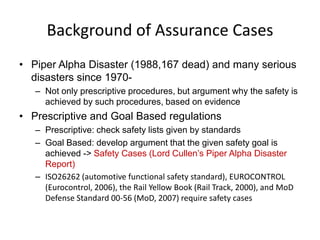
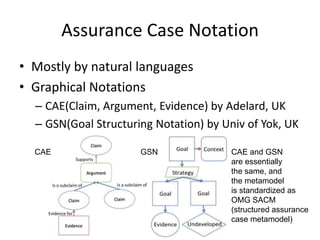
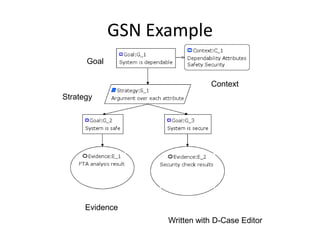
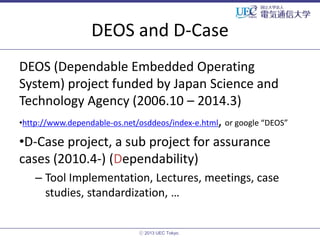
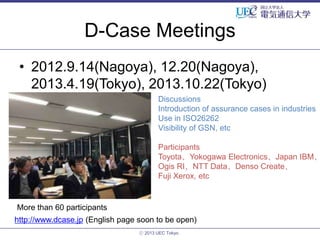
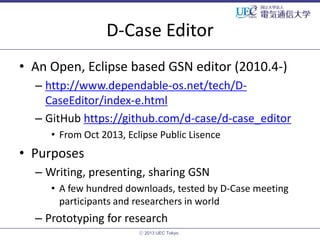
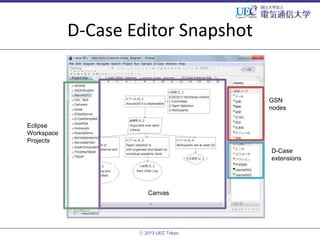
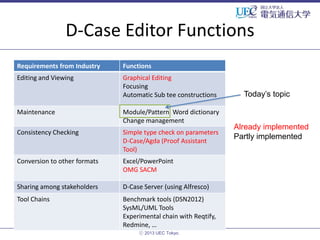
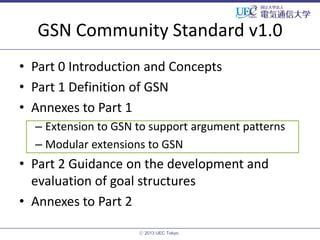
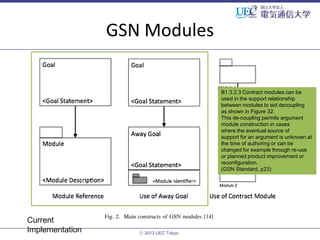
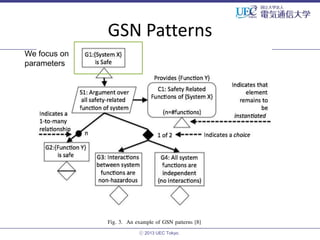
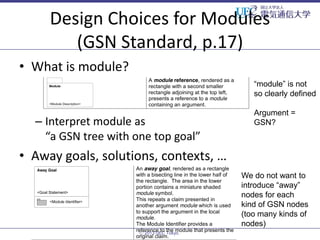
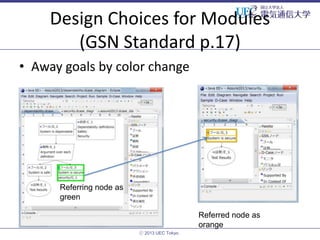
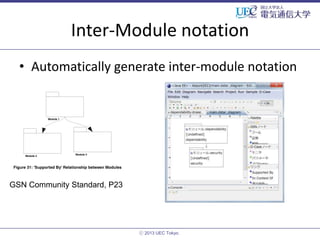
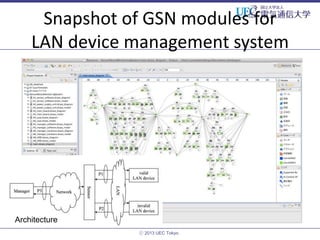
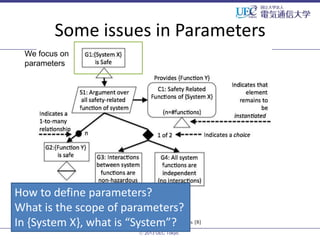
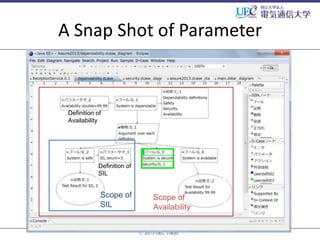
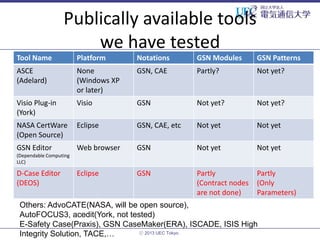
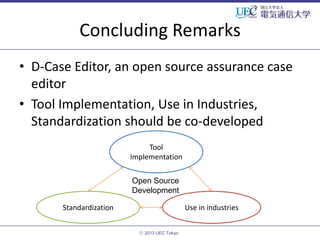
The document discusses the D-Case Editor, an open-source tool for creating assurance cases, emphasizing its role in evidencing system safety in various industries, including automotive and healthcare. It outlines the historical context, compliance with international standards, and the structure of assurance cases, while highlighting the need for effective argumentation and evidence-based practices. Additionally, it covers D-Case's development, functions, and community feedback, stressing the importance of harmonizing tools and standardization in the field.