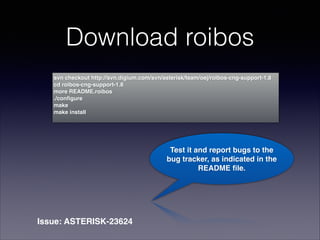
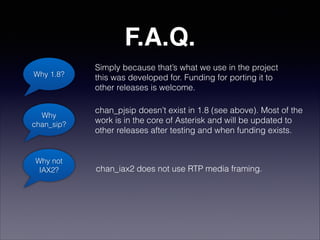
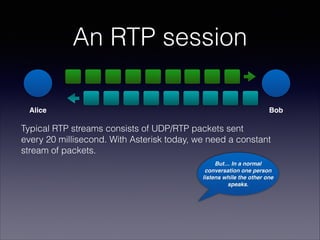
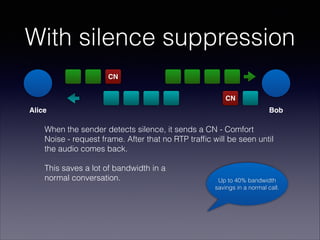
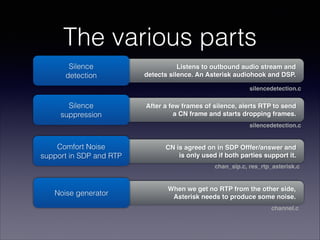
The document discusses the implementation of silence suppression in the Asterisk 1.8 telephony platform, aimed at saving bandwidth by detecting silence in conversations and sending comfort noise packets instead of continuous RTP traffic. Funded by Bressner Technology, the project includes detailed instructions for configuration and testing, with future plans for integration into later versions of Asterisk pending positive feedback. Key technical details are provided, including codec configurations and the necessity of testing for broader applicability in RTP channels.
![Configuration
Add the ”cn” codec to allowed codecs in sip.conf
Add ”silencesuppression=yes”
in the [general] section or device section of sip.conf
Note: If you enable the CN codec but not silence suppression,
we will accept CN but never send a CN frame.
This saves some CPU for silence detection,
but still uses CPU for noice generation.
1.
2.](https://image.slidesharecdn.com/asterisk-silence-suppression-140413014124-phpapp02/85/roibos-asterisk-bandwidth-saving-6-320.jpg)