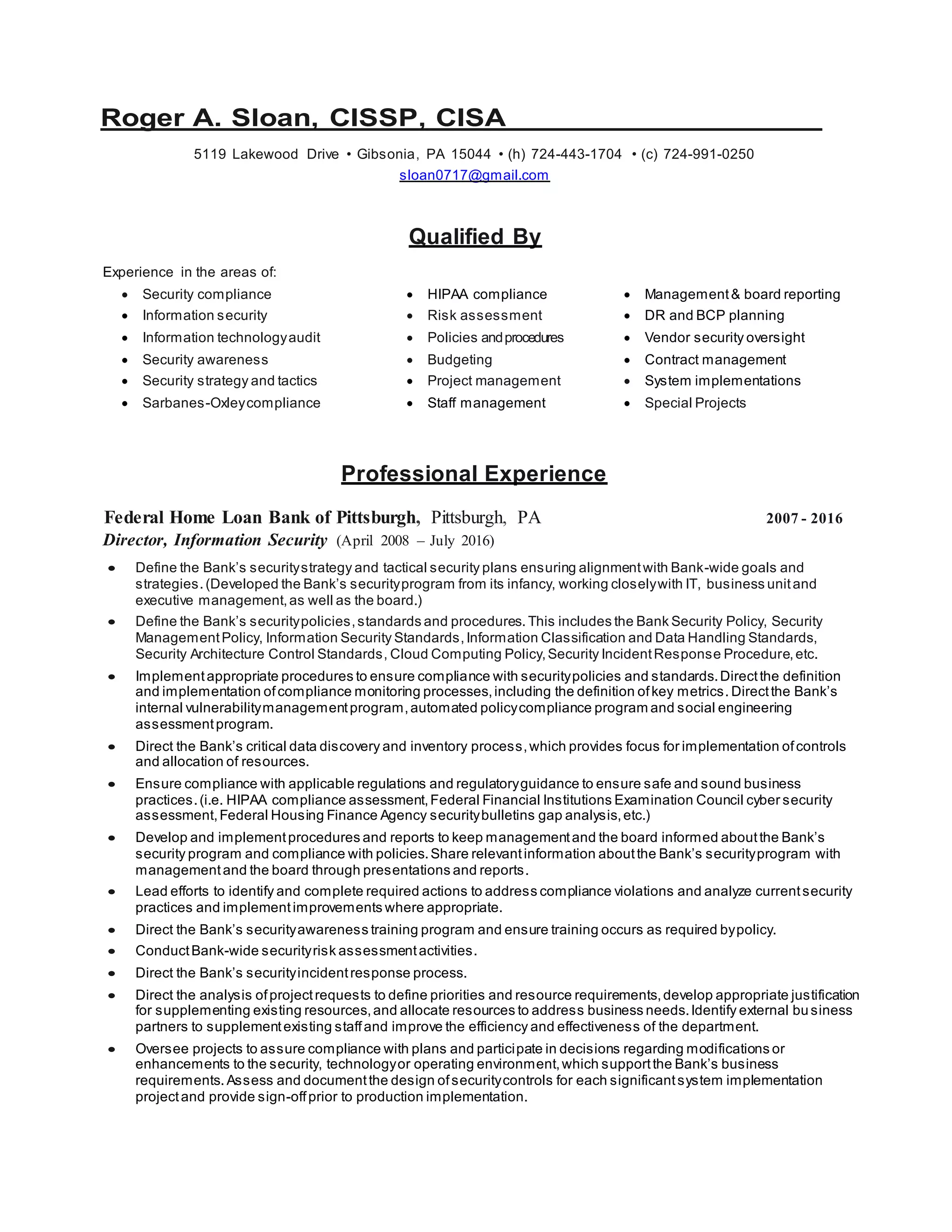
This document is a resume for Roger A. Sloan that outlines his experience and qualifications in information security, compliance, auditing, and risk management. Over 30 years of experience includes positions as Director of Information Security, Audit Manager, Manager of Audit Services, and various security, audit and analyst roles. Sloan holds CISSP and CISA certifications and has extensive experience developing and managing security programs, policies, compliance, risk assessments, audits, awareness training and incident response.