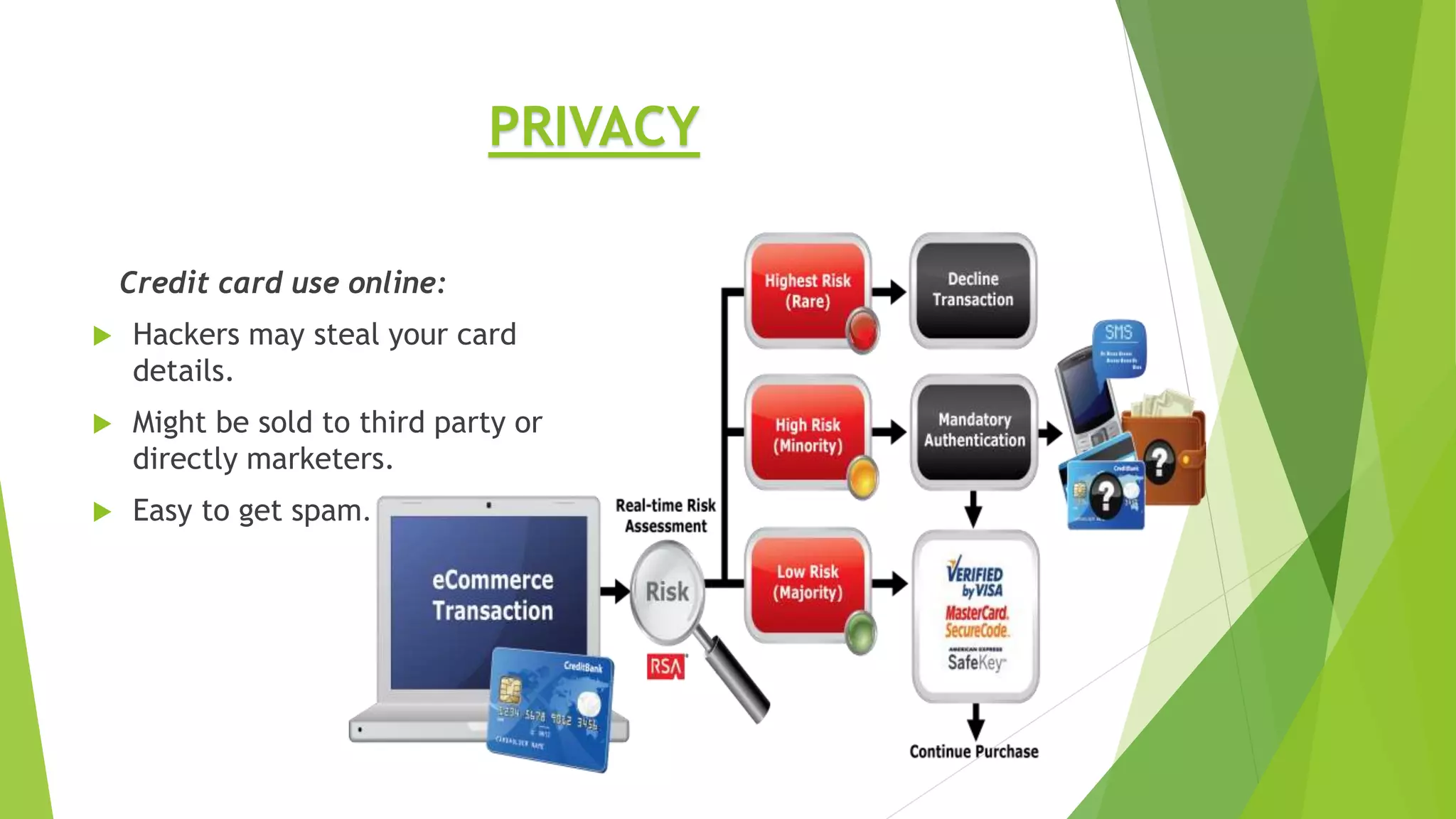
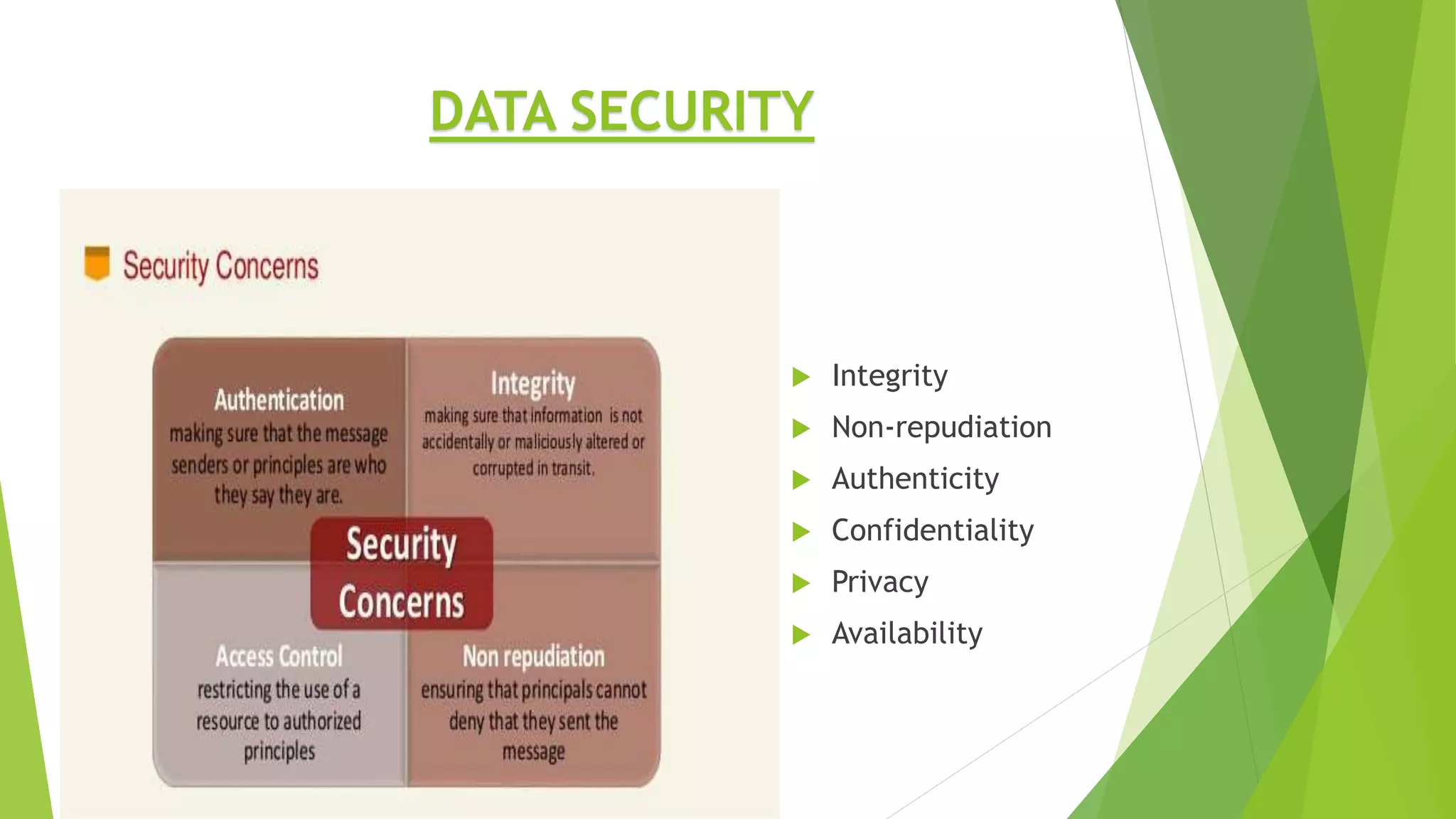
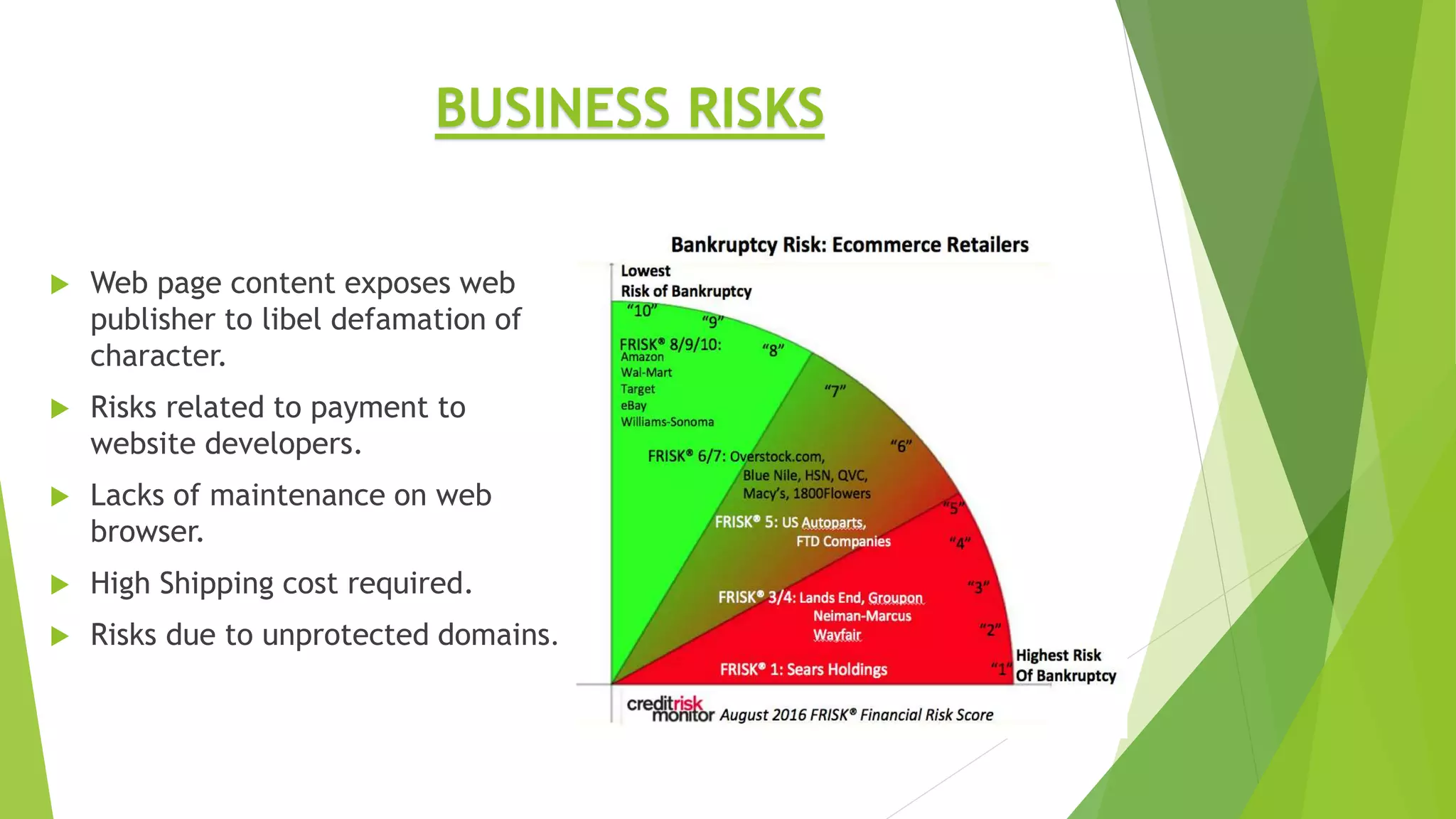
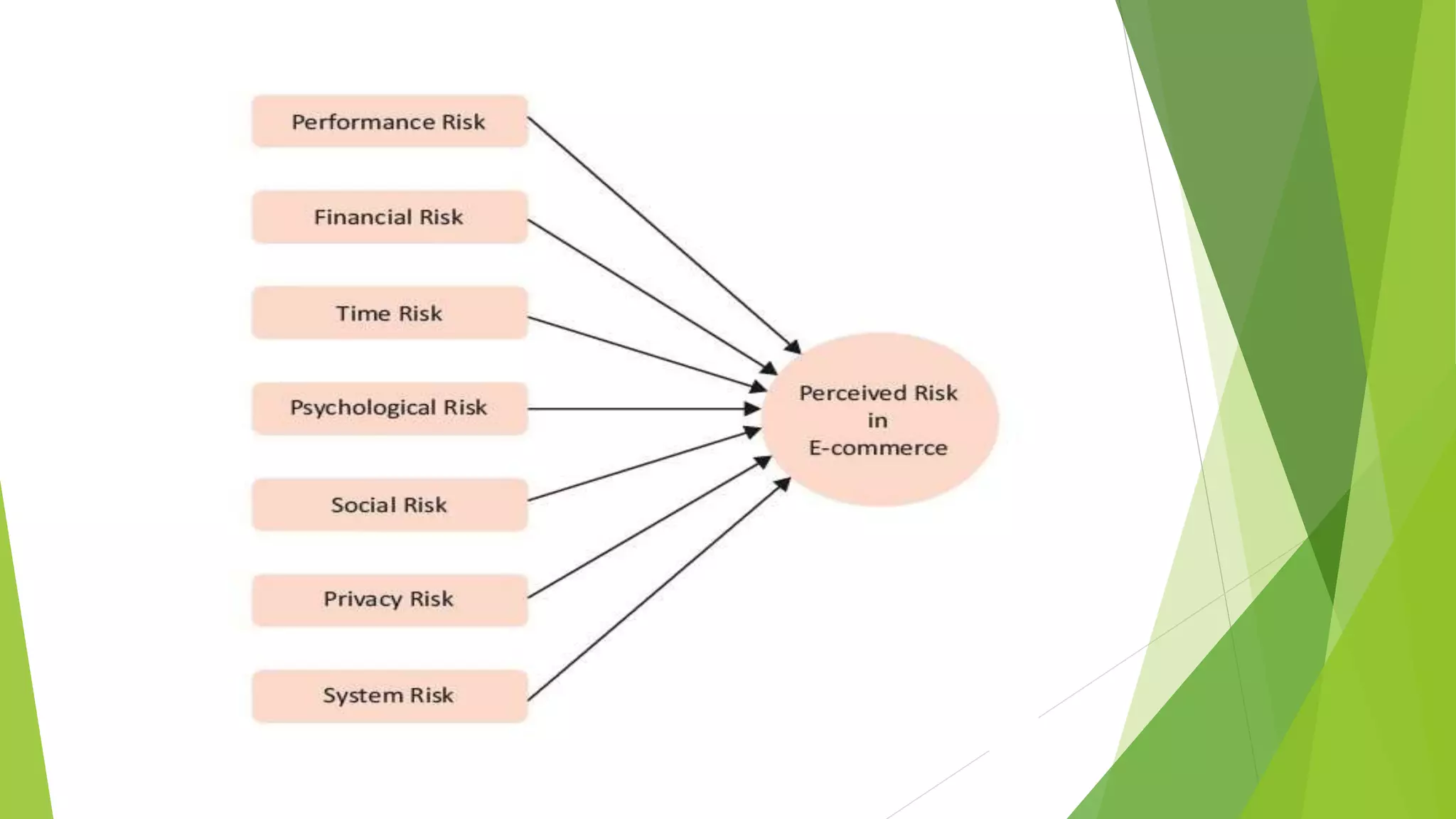
The presentation outlines various risks associated with e-commerce, including privacy concerns, data security issues, and potential business and technology risks. Key points cover threats like hacking, unauthorized access, and marketing failures that can affect online transactions. The document emphasizes the importance of awareness and measures to mitigate these risks in the e-commerce landscape.