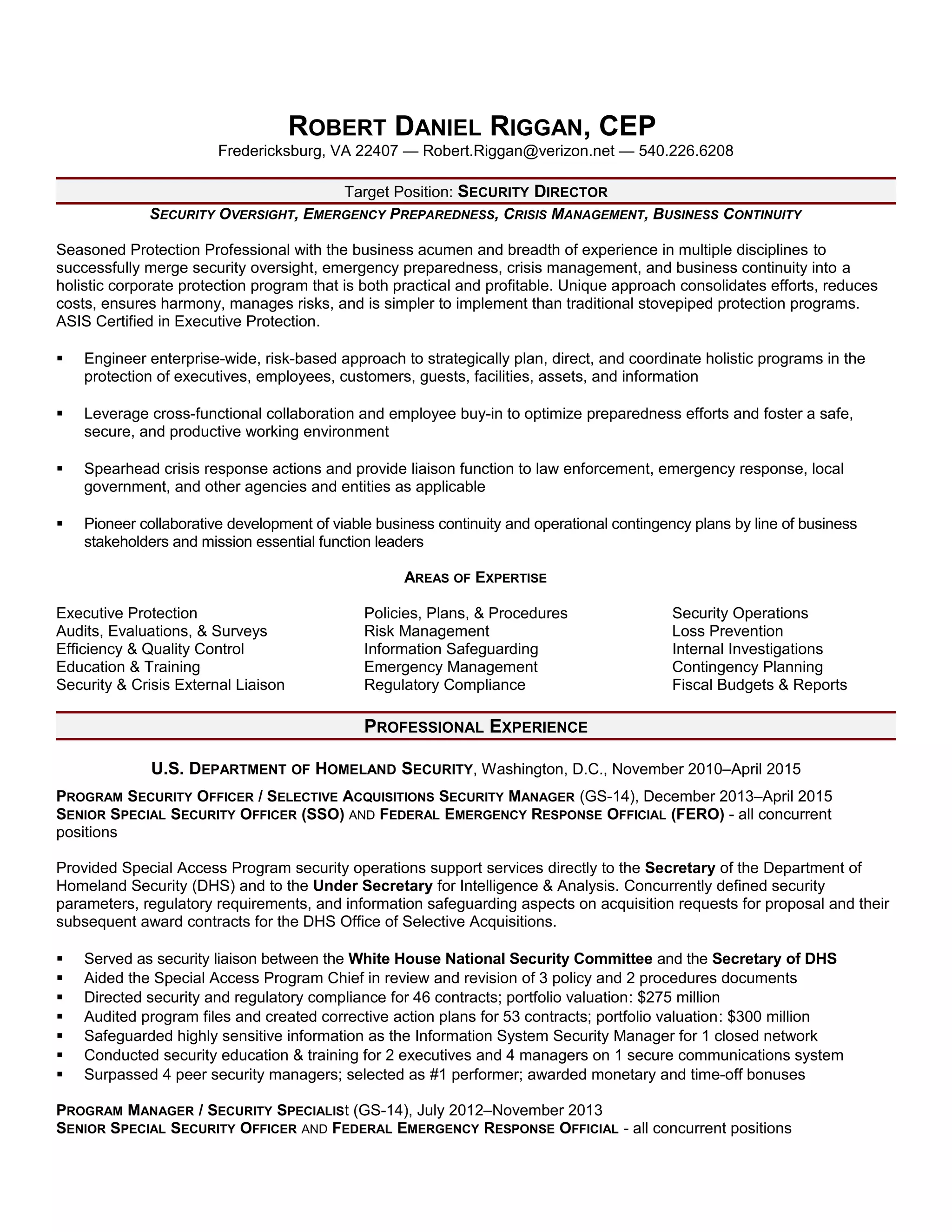
Robert Daniel Riggan is a seasoned protection professional targeting a director position in security, leveraging extensive experience in emergency preparedness, crisis management, and business continuity. He has held significant roles in the U.S. Department of Homeland Security and other organizations, focusing on risk management, compliance, and security operations, while achieving numerous accolades for performance. Riggan’s education includes coursework in security management, complemented by professional development in various security disciplines.