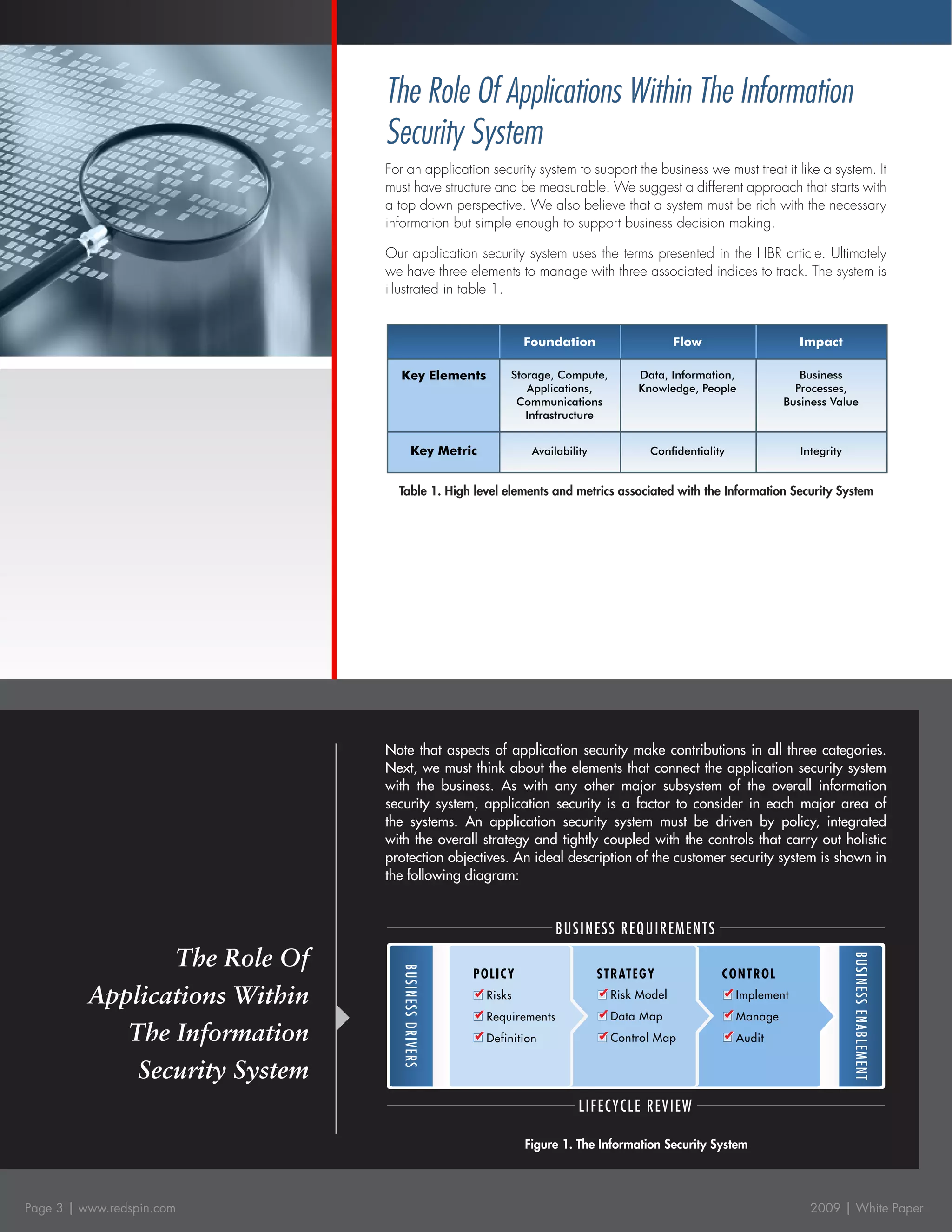
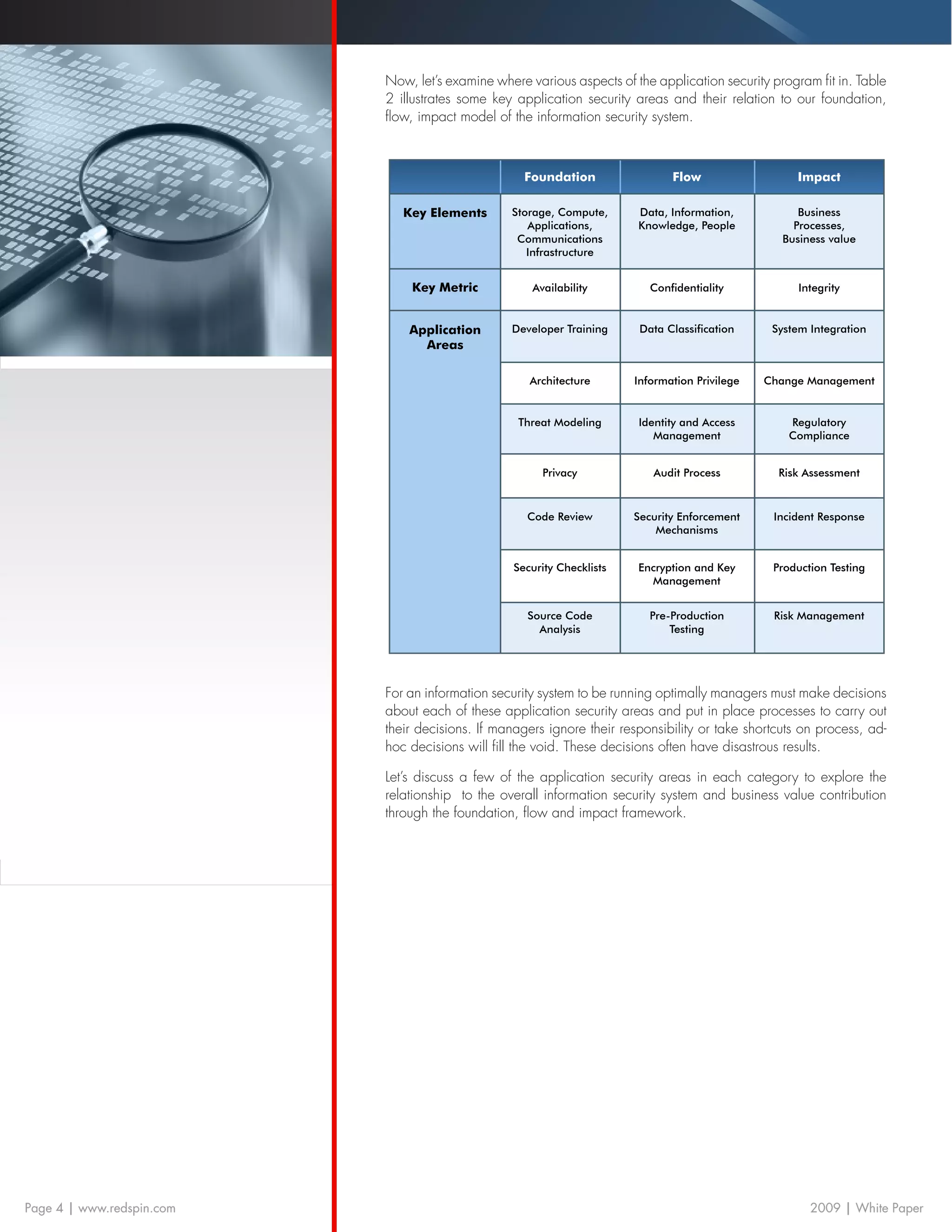
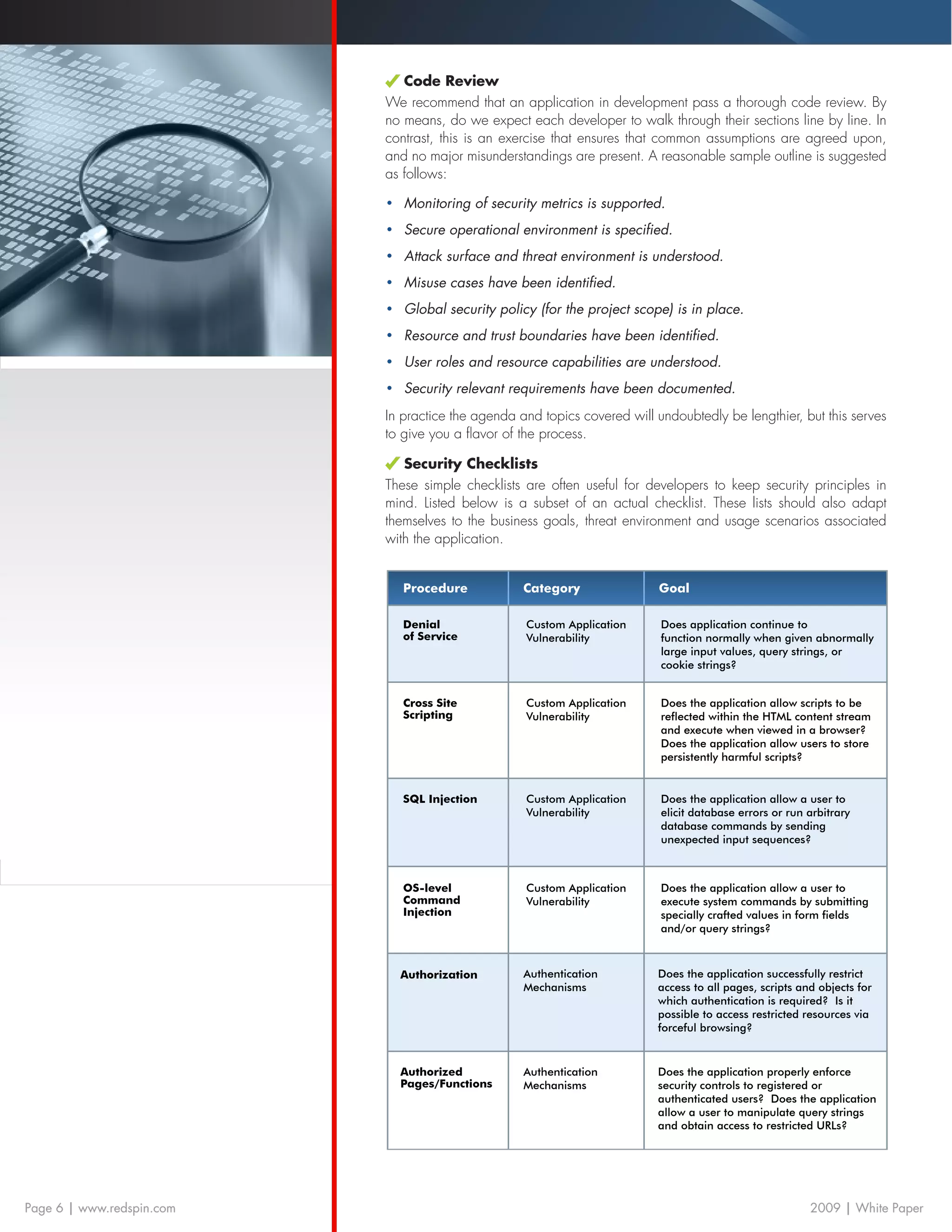
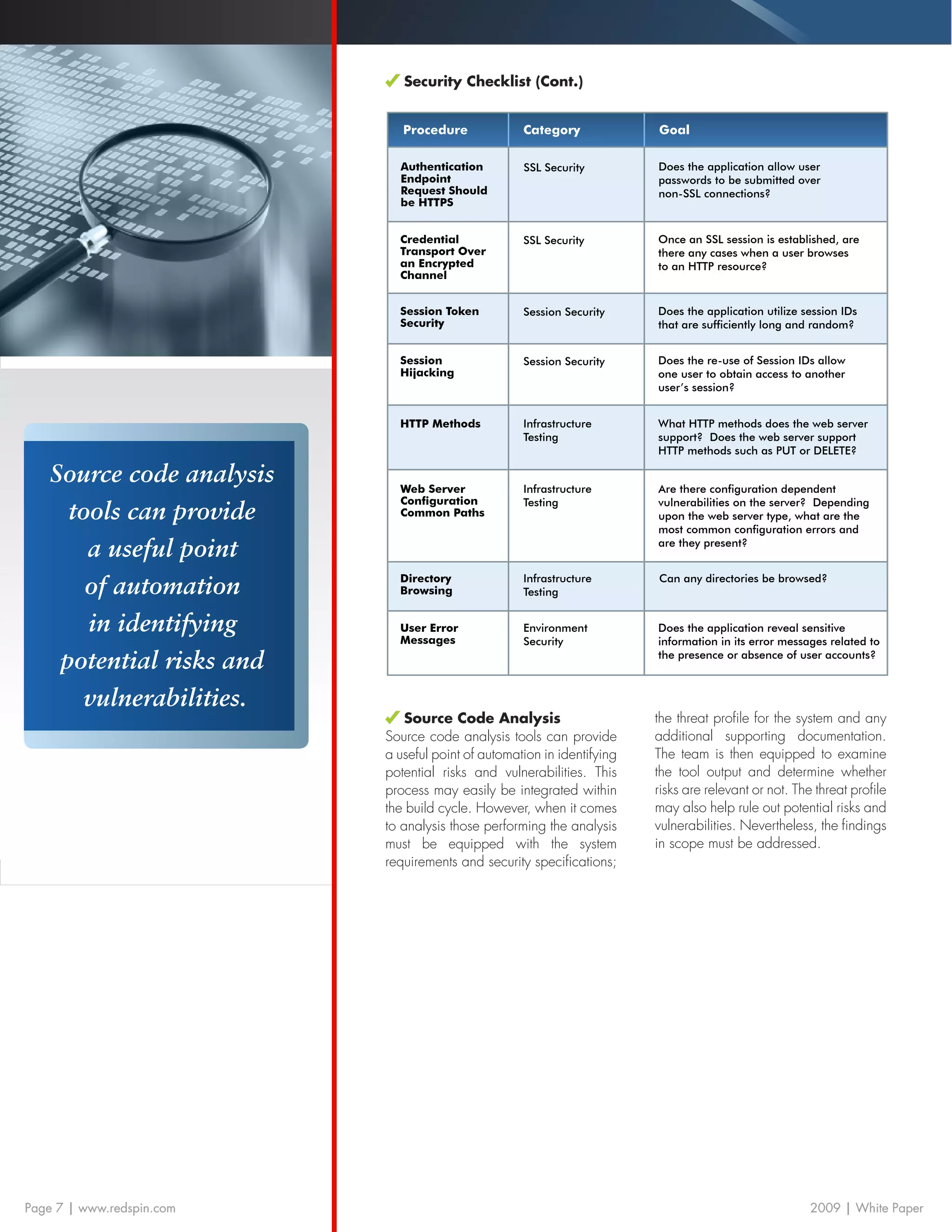
This white paper discusses the vital role of application security in enhancing business value and reducing risk. It presents a framework connecting application security to three indices: foundation, flow, and impact, while proposing methodologies for secure software development and integration within the overall business and information security systems. The document emphasizes that effective application security management is crucial for improving brand loyalty and competitive advantage.