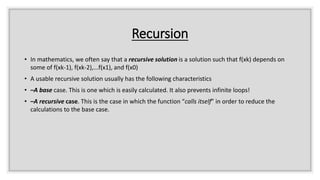
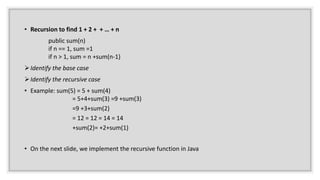
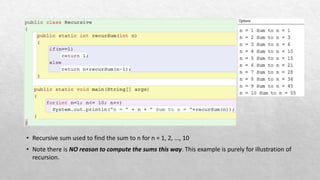
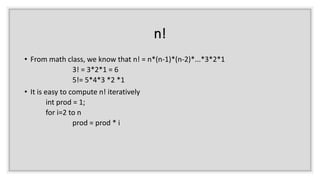
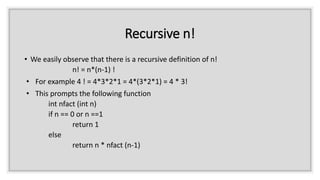
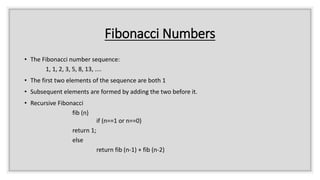
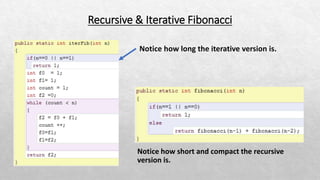
The document explains the concept of recursion in mathematics, highlighting its essential characteristics such as a base case and recursive case. It provides examples of recursive solutions for summing numbers, calculating factorials, and generating Fibonacci numbers, along with comparisons to iterative solutions. Additionally, it discusses the simplicity and coding efficiency of recursive solutions, noting that while they can be easier to implement, iterative solutions may perform better in terms of speed.


![Recursive search
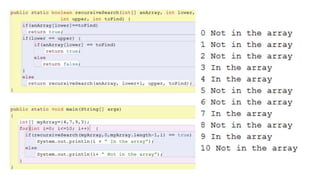
• It is very simple to write an iterative search to determine if a given value (toFind) is in an array
for i = 0 to the array length -1
if array[i] = to_find
return true
End i loop
Return false
• When we do it recursively
• If the array has length 1, we return true if the single element and toFind are the same
• If not
• we check the first element and return true if it and toFind are equal
• Otherwise, we repeat the search on the remainder of the array](https://image.slidesharecdn.com/recursion-191114173524/85/Recursion-11-320.jpg)