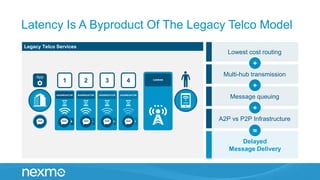
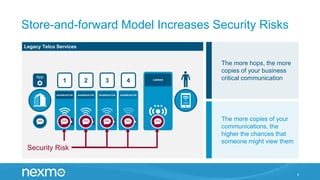
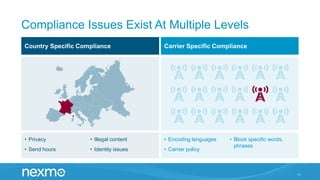
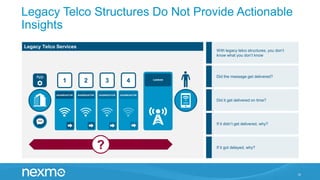
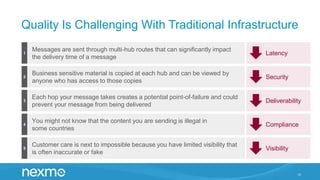
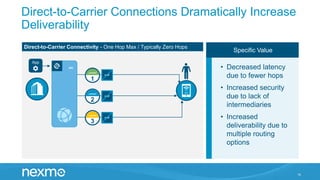
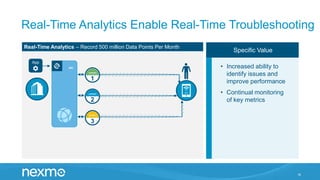
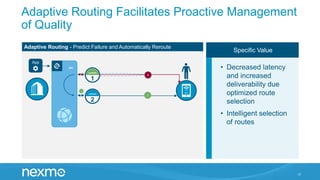
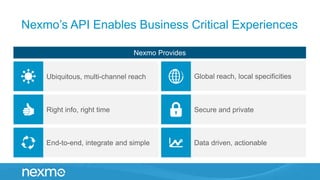
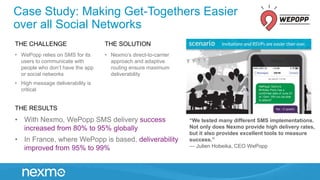
The document highlights the advantages and challenges of using SMS for business communications, noting a high engagement and read rate but potential delays and security risks from the legacy telco infrastructure. It discusses the impact of routing models and emphasizes the benefits of direct-to-carrier connections for improved deliverability and reduced latency. Case studies provided demonstrate successful implementations using Nexmo's solutions, showcasing significant improvements in message deliverability and user experience.