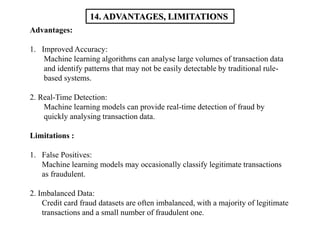
1. The document describes a project that aims to develop a machine learning model for credit card fraud detection. It involves gathering credit card transaction data, preprocessing the data, and using algorithms like decision trees, logistic regression, and random forests to classify transactions as fraudulent or legitimate.
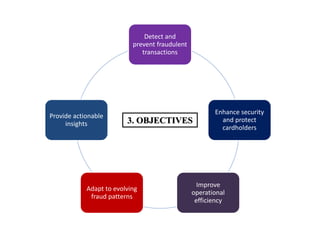
2. The objectives are to accurately identify fraudulent transactions in real-time to prevent financial losses for cardholders and institutions. This would enhance security and protect stakeholders.
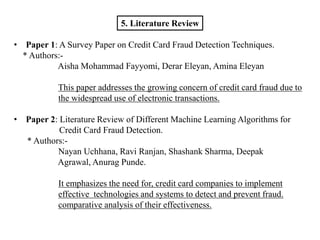
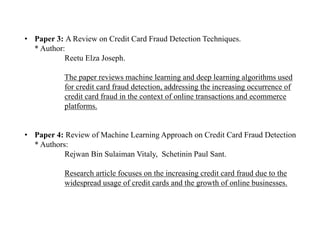
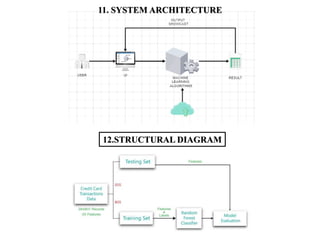
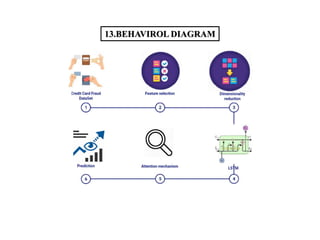
3. A literature review is presented on papers discussing credit card fraud detection techniques using machine learning algorithms. The feasibility, scope, requirements, architecture, algorithms, and diagrams of the proposed system are outlined.
![18. REFERENCES
[1] “Fraud Detection in Credit Cards using Logistic Regression” ,
Hala Z Alenzi1, Nojood O Aljehane,
(IJACSA) International Journal of Advanced Computer Science and Applications,
Vol. 11, No. 12, 2020
[2] “Credit Card Fraud Detection using Machine Learning and Data Science” ,
Aditya Saini, Swarna Deep Sarkar Shadab Ahmed ,
International Journal of Engineering Research & Technology (IJERT) http://www.ijert.org
ISSN: 2278-0181 IJERTV8IS090031 (This work is licensed under a Creative Commons
Attribution 4.0 International License.) Issue 09 September-2019
[3] “Credit Card Fraud Detection using Machine Learning Algorithms’’,
Vaishnavi Nath Dornadulaa , Geetha Sa
- INTERNATIONAL CONFERENCE ON RECENT TRENDS IN
ADVANCED COMPUTING 2019, ICRTAC 2019
[4] “Credit Card Fraud Detection System”
Kartik Madkaikar, Manthan Nagvekar, Preity Parab, Riya Raikar, Supriya Patil,
International Journal of Recent Technology and Engineering (IJRTE) ISSN: 2277-3878
(Online), Volume-10 Issue-2](https://image.slidesharecdn.com/projectpptsem2-240101063750-a6a86c08/85/Project-PPT-sem-2-pptx-19-320.jpg)