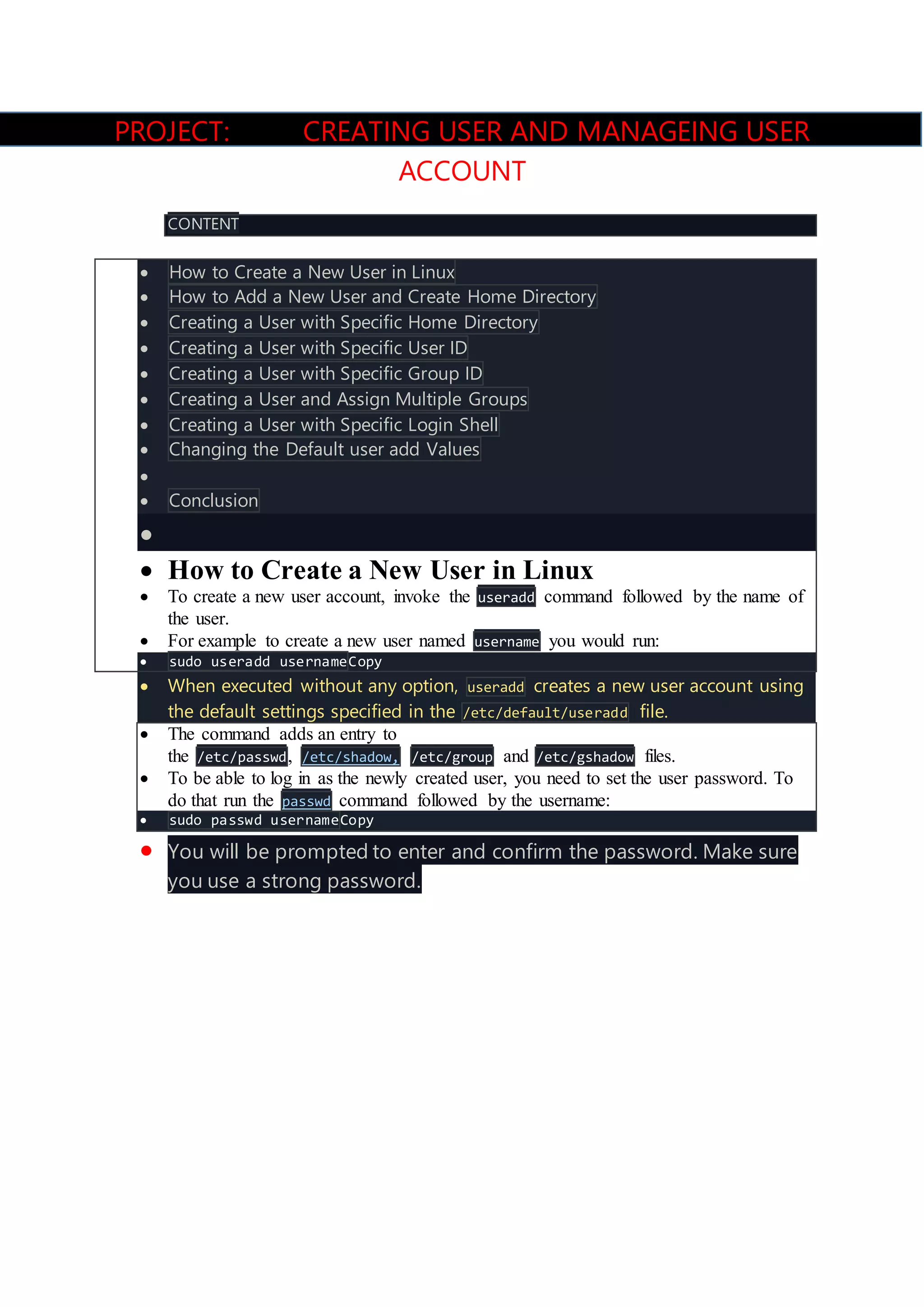
This document discusses how to create and manage user accounts in Linux. It describes how to use the useradd command to create a new user with default settings or custom settings like a specific home directory, user ID, group ID, login shell, or multiple groups. It also covers how to set the password for a new user using the passwd command.