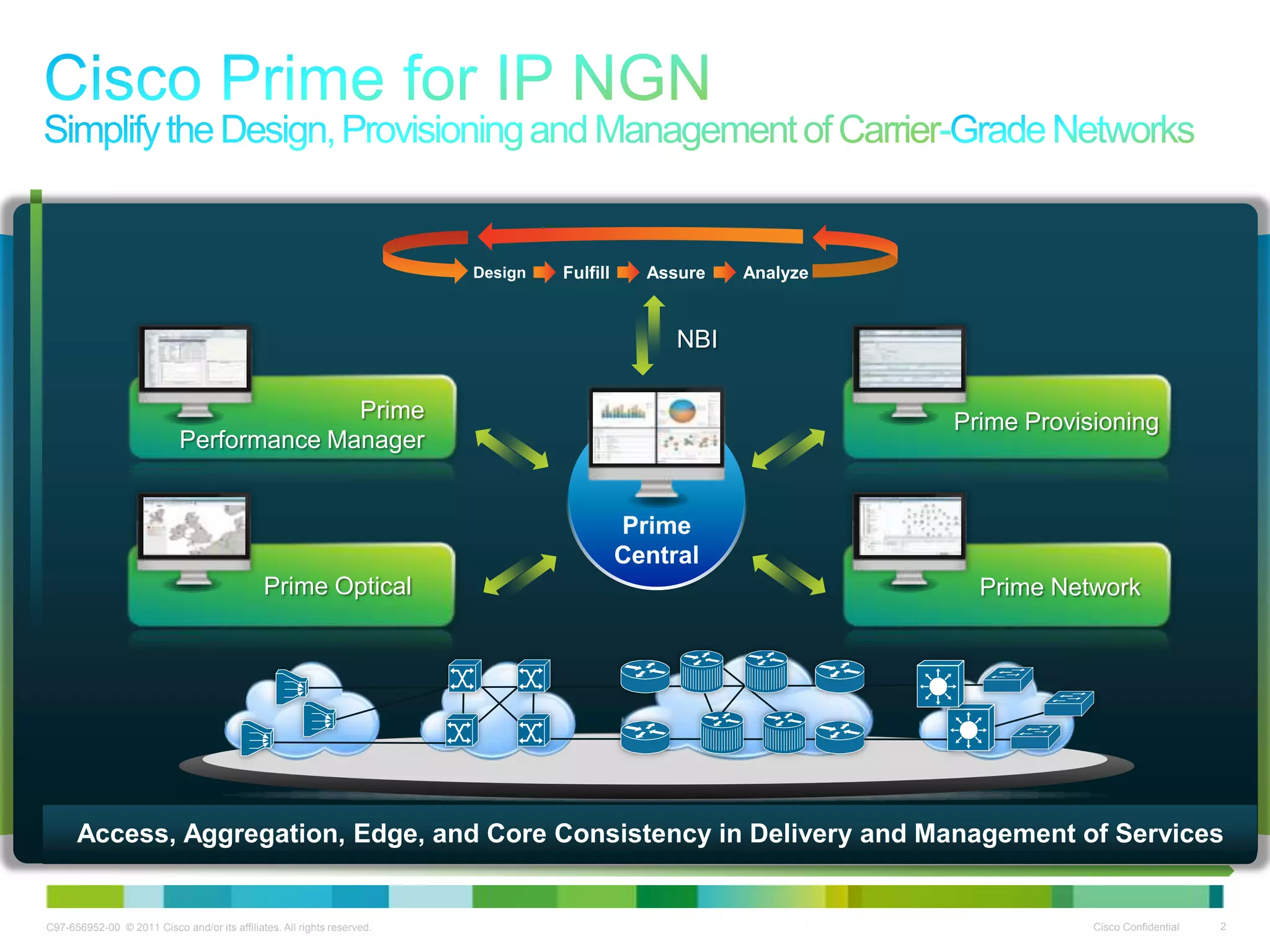
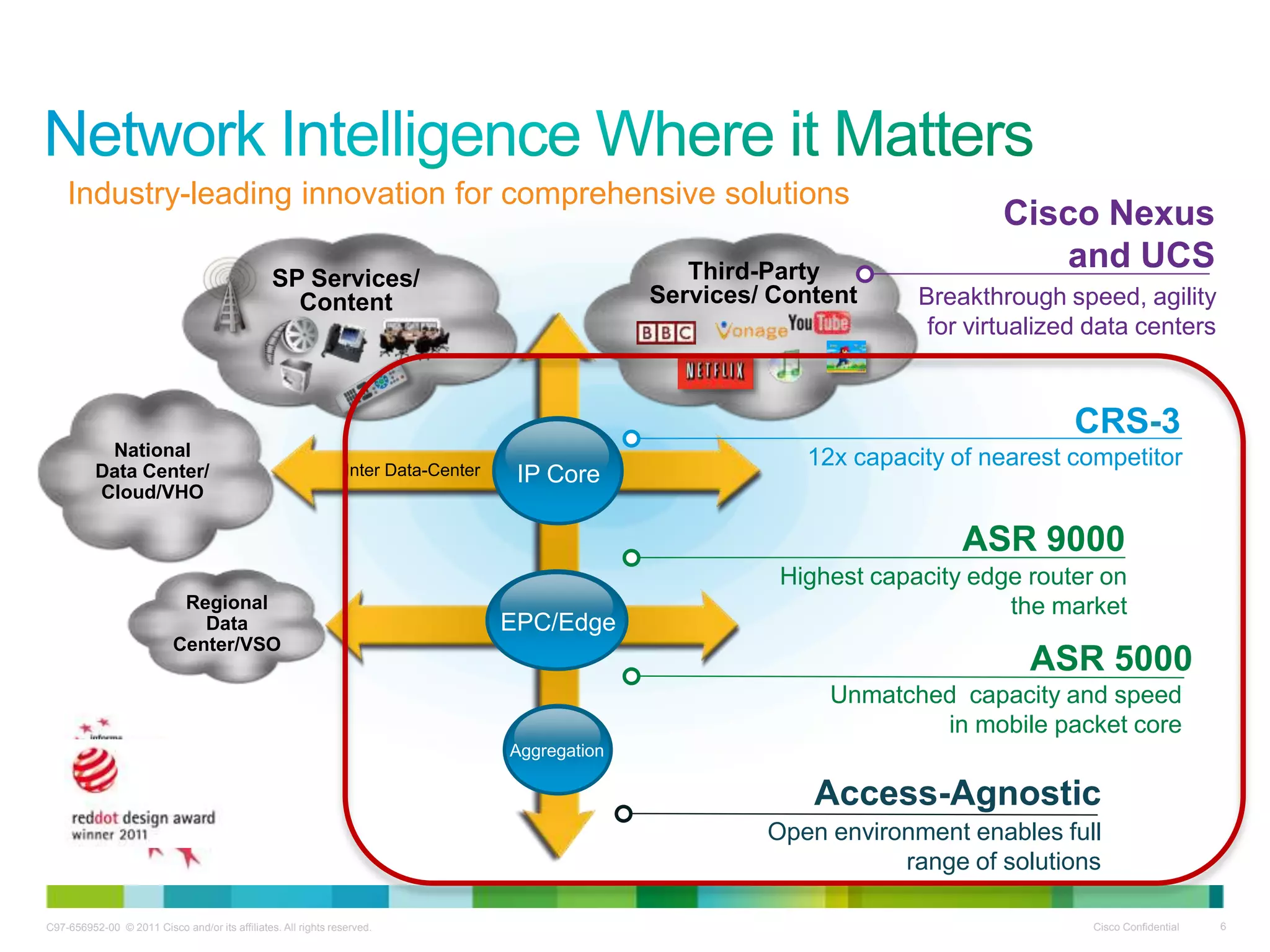
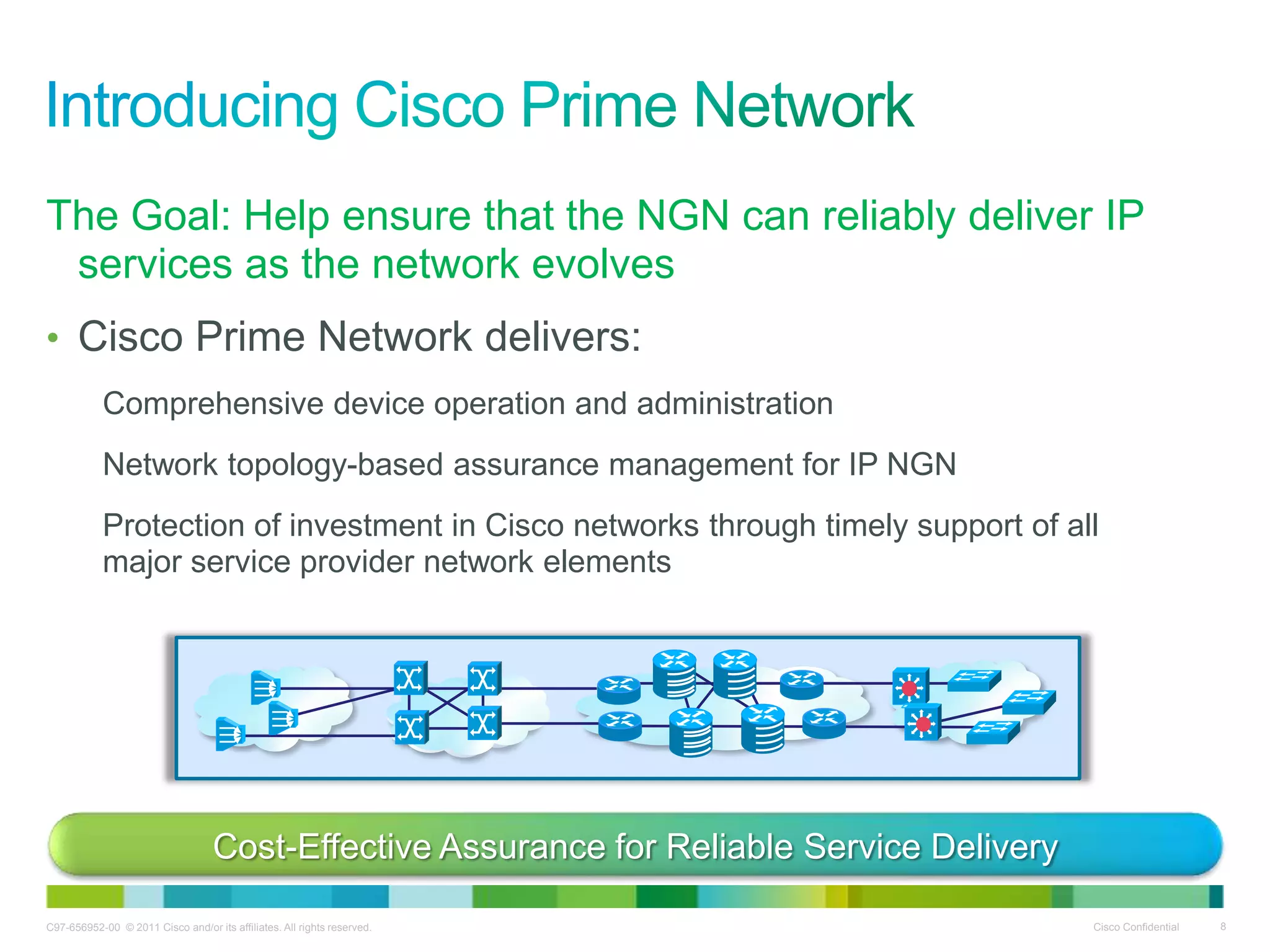
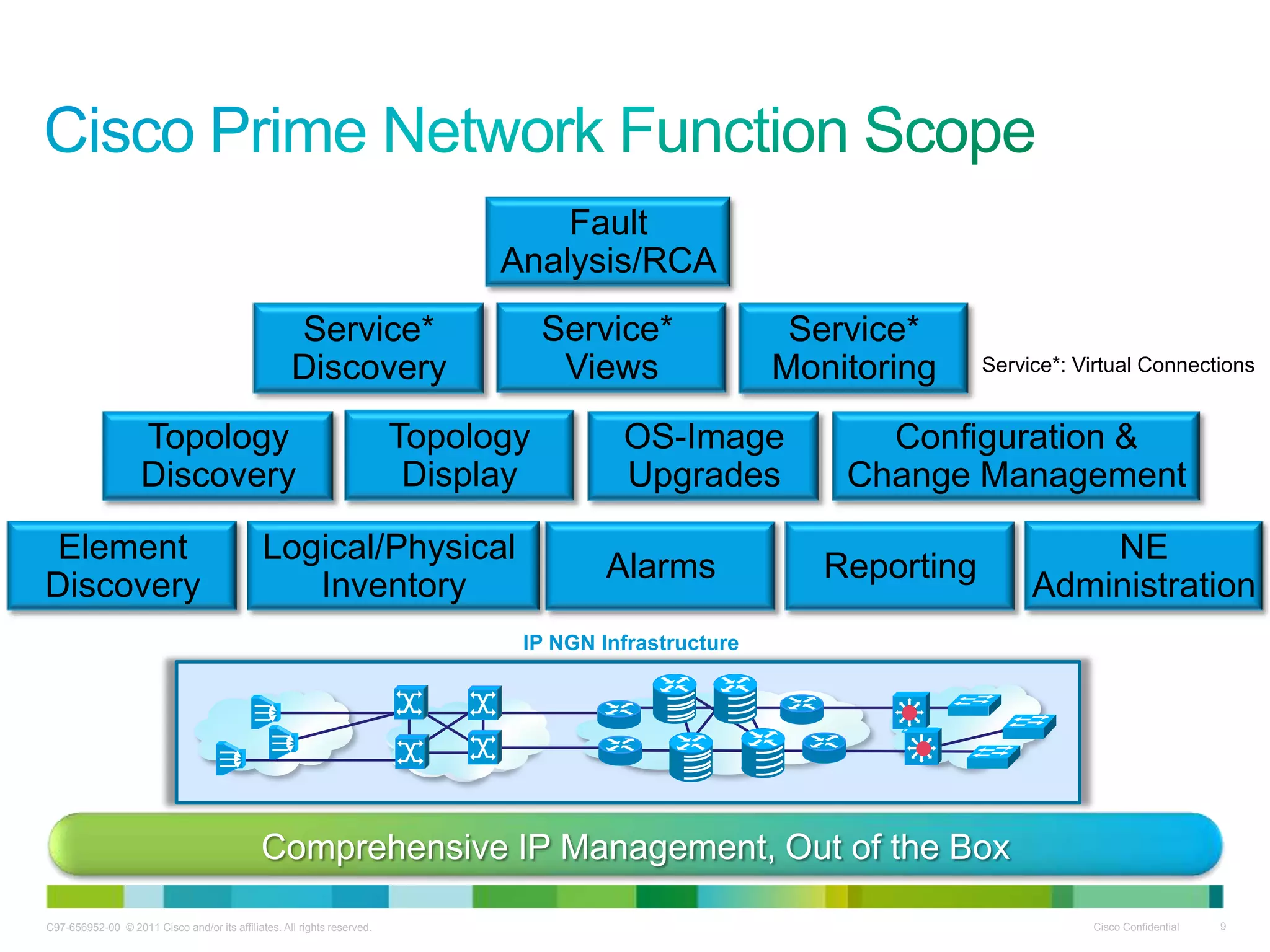
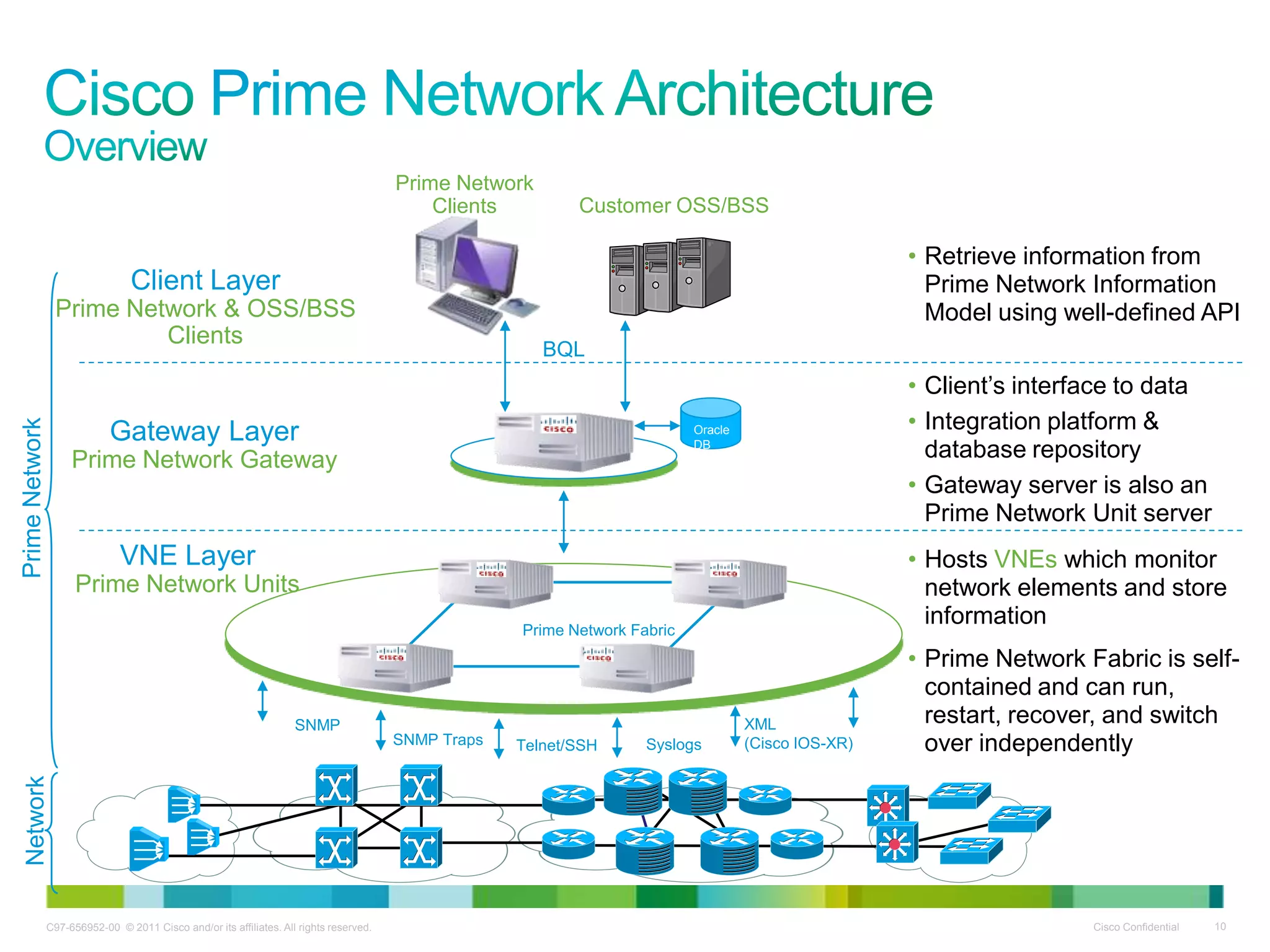
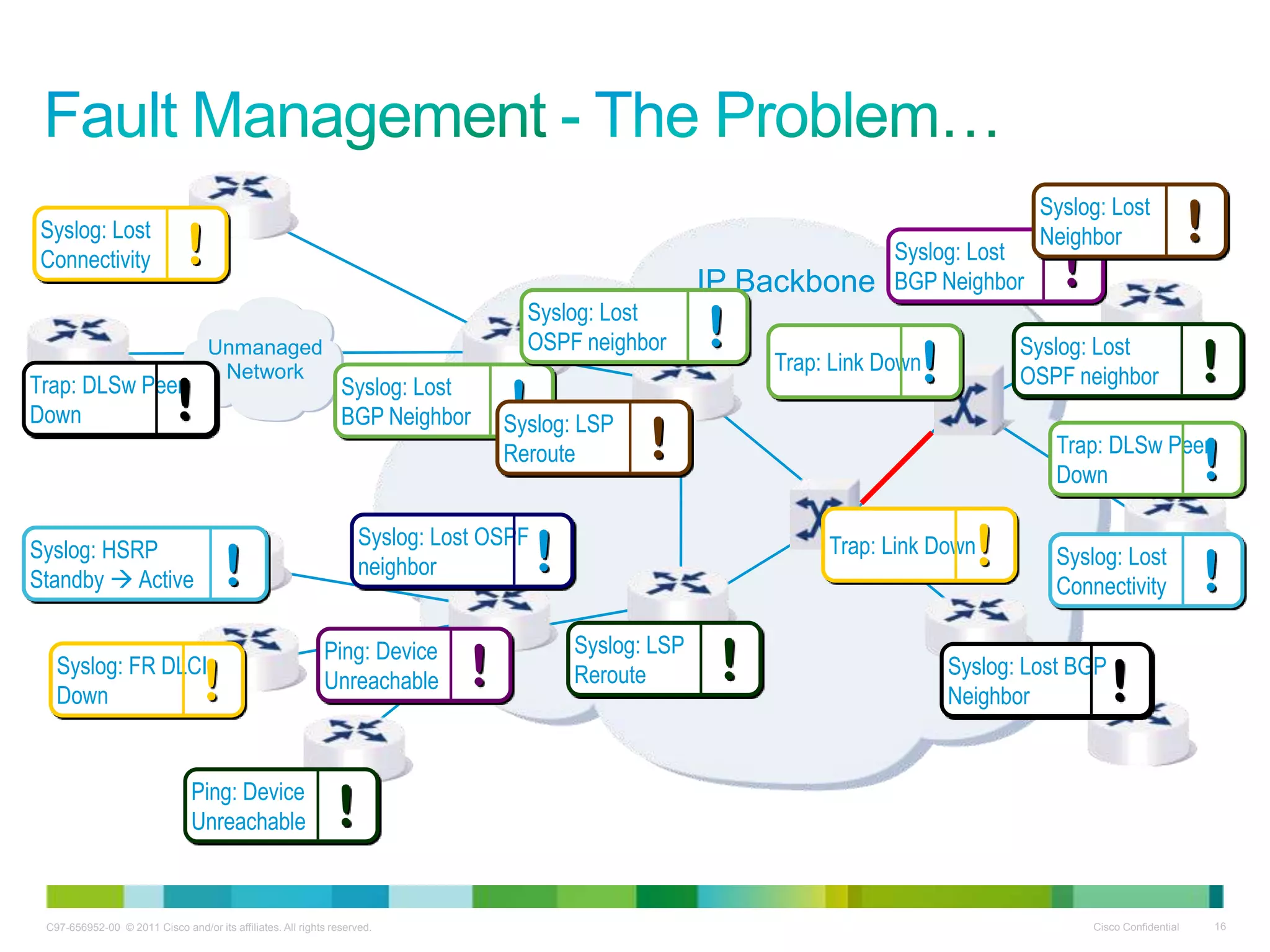
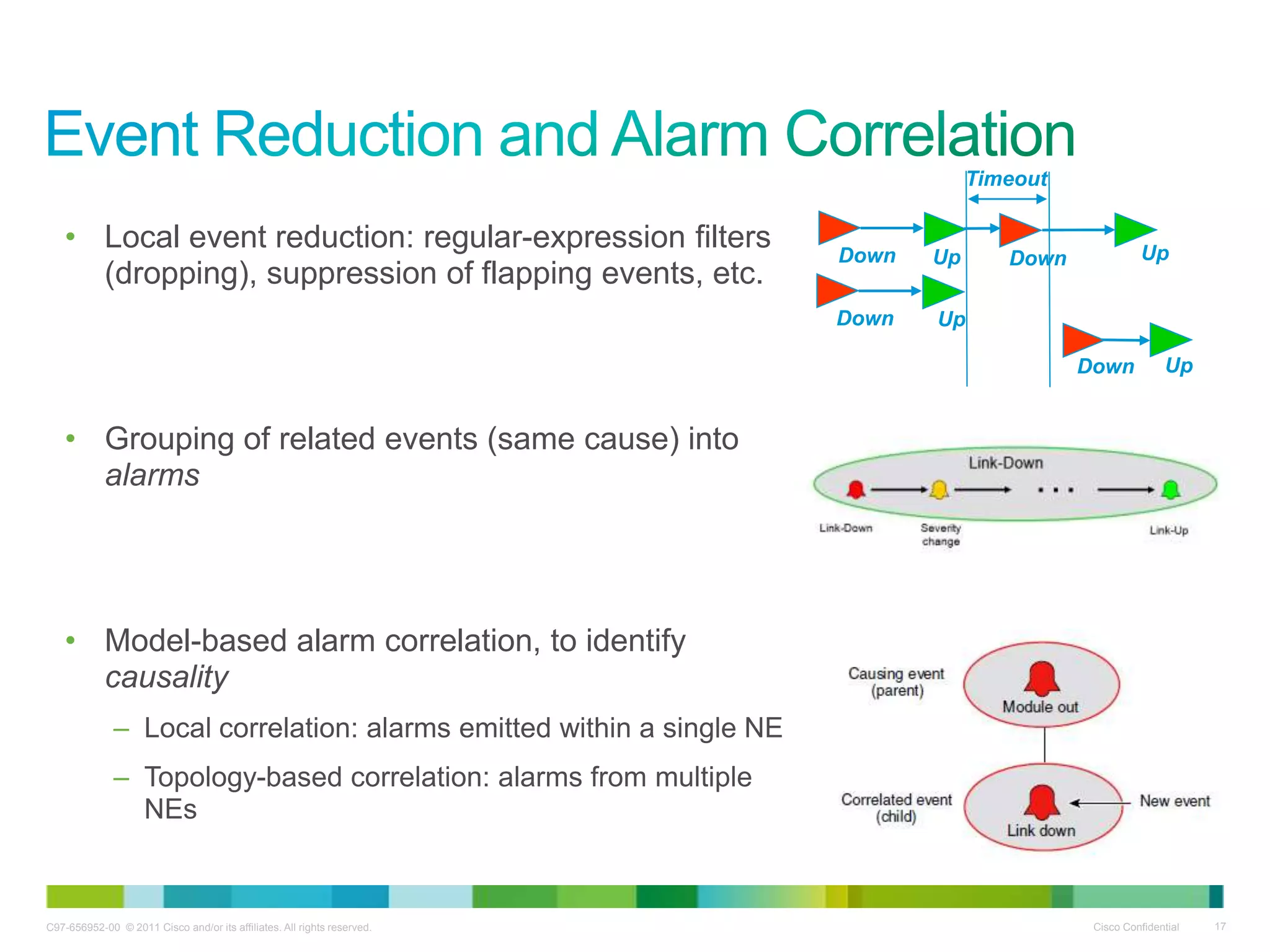
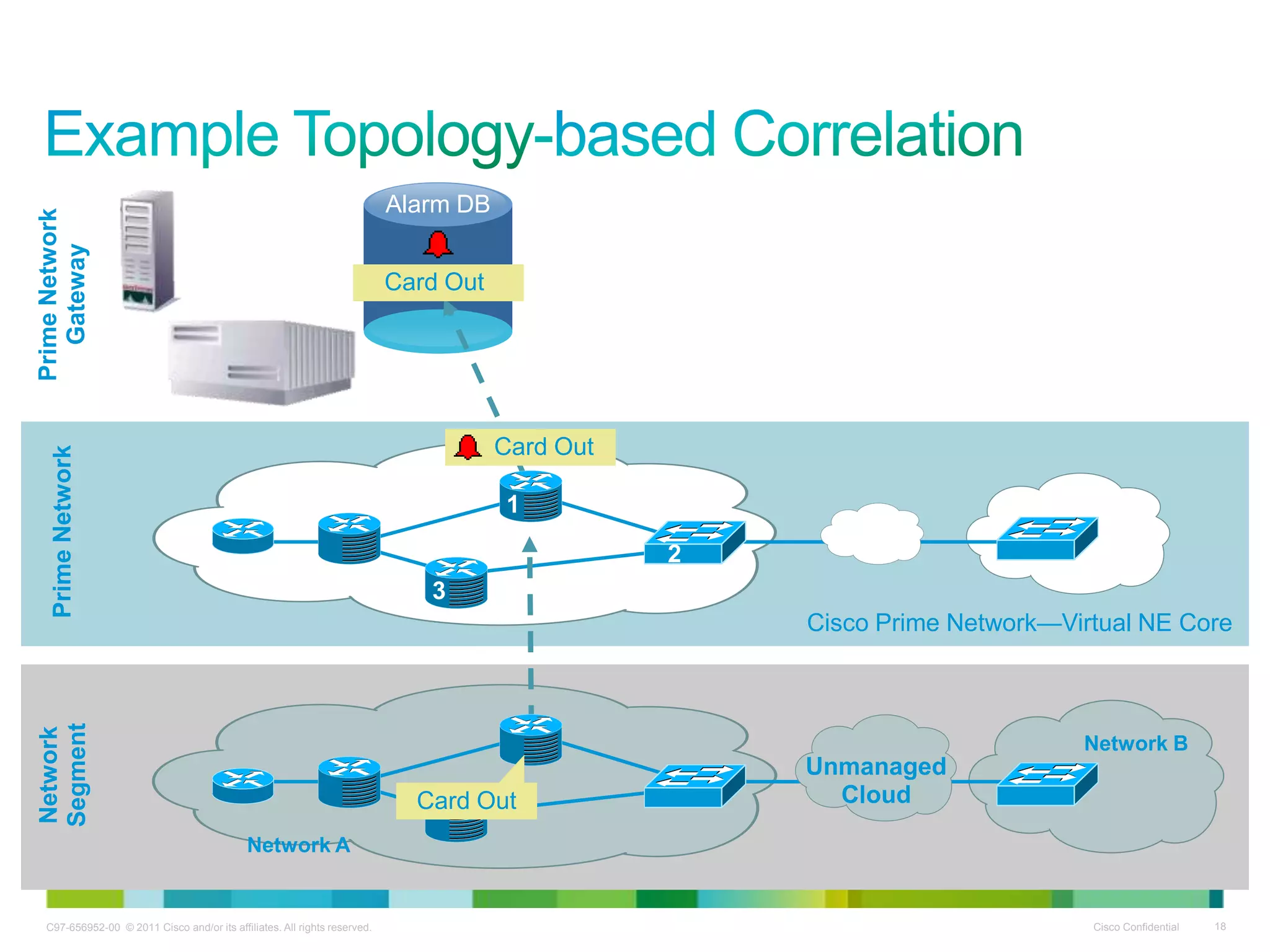
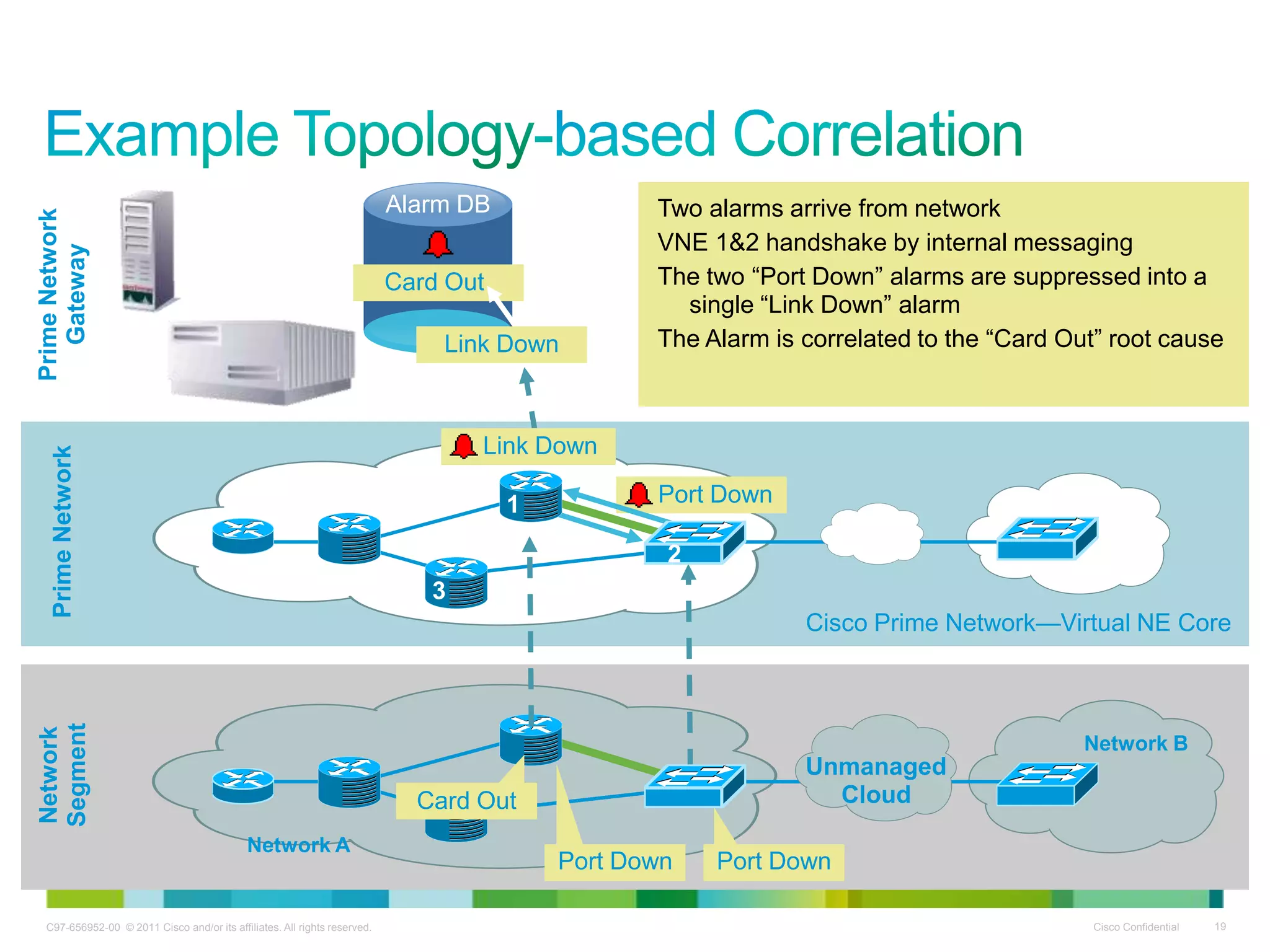
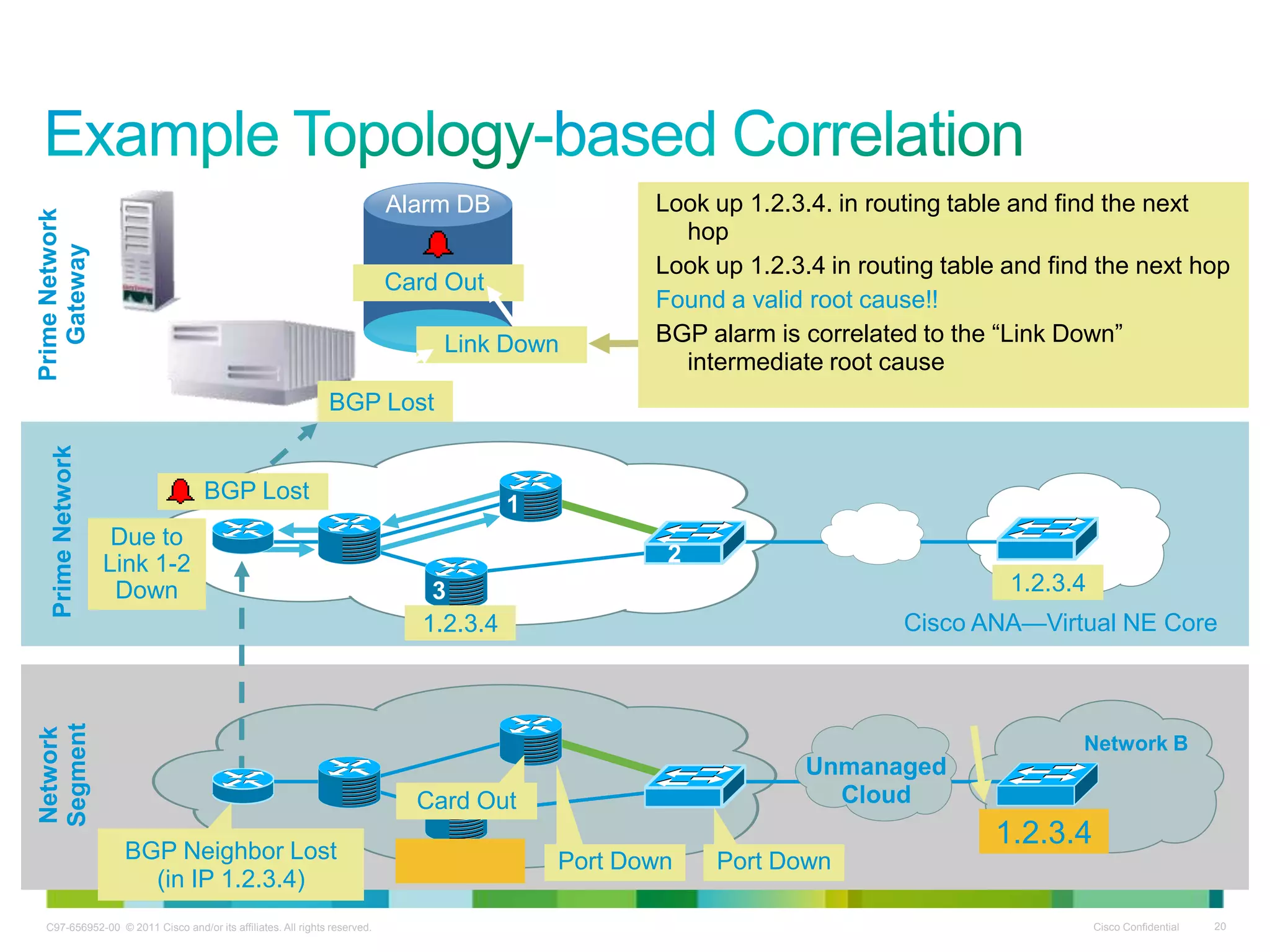
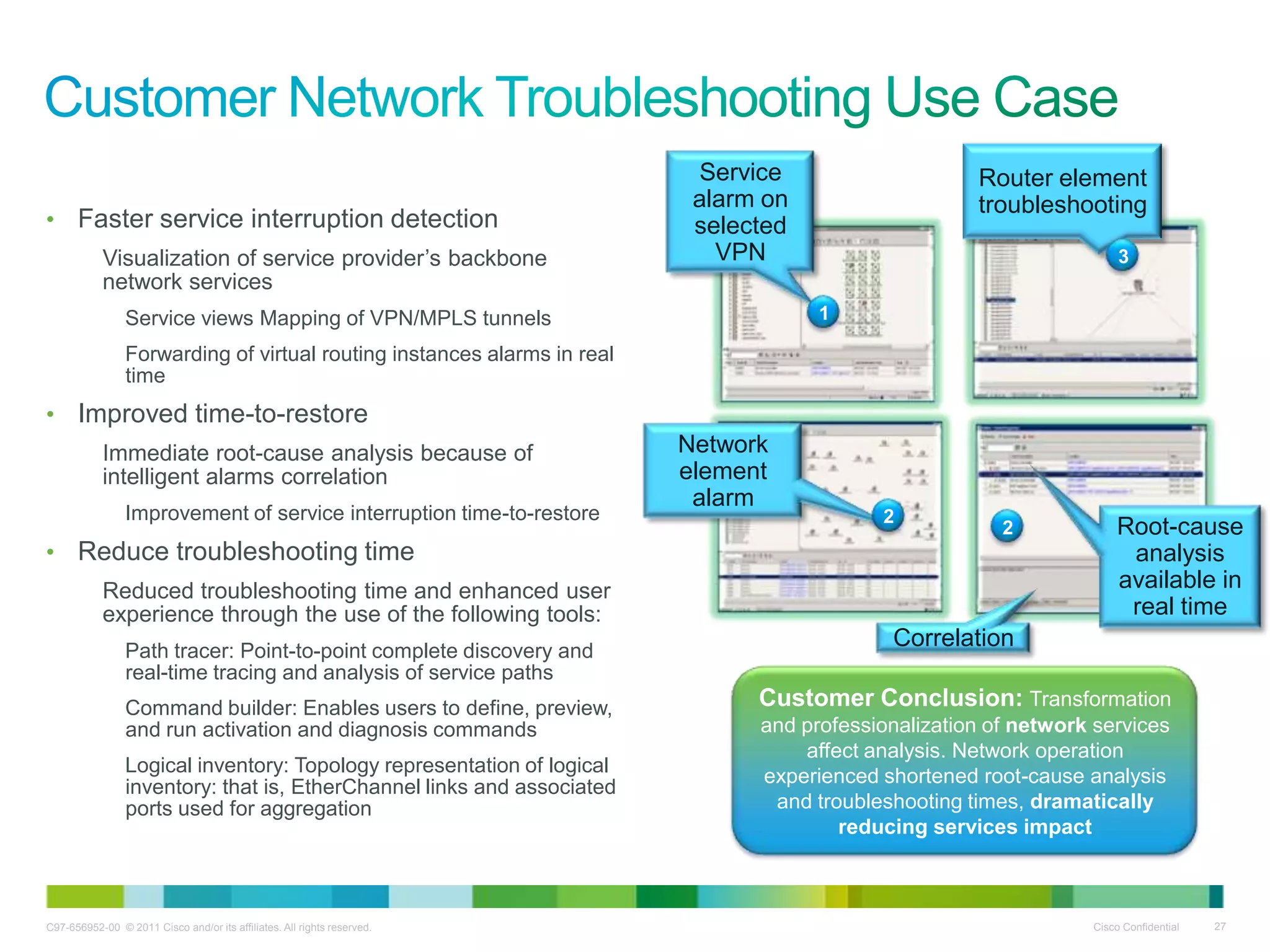
The document presents an overview of Cisco Prime for IP NGN, detailing its architecture and capabilities for managing and assuring network services. It emphasizes the integration of various network elements, efficient inventory management, and robust alarm correlation to enhance operational efficiency. Key benefits include reduced troubleshooting times and improved service delivery in evolving network environments.