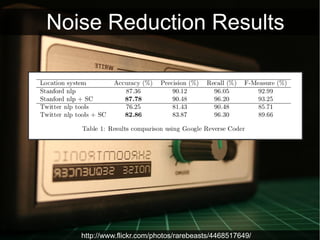
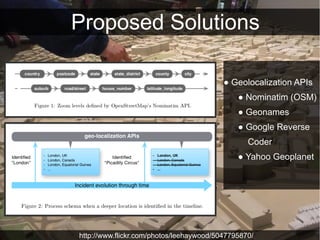
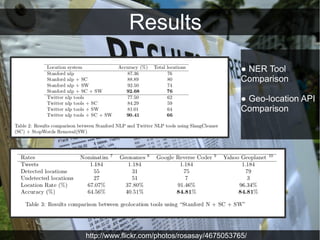
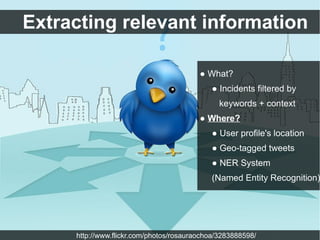
The document discusses utilizing Twitter for enhancing situational awareness in emergency response teams (ERTs) by extracting relevant information from tweets. It outlines the challenges of noise and ambiguity in tweets, and proposes solutions such as geolocation APIs and noise reduction techniques. The authors highlight the importance of improving data accuracy for better incident management in collaboration with social networks.
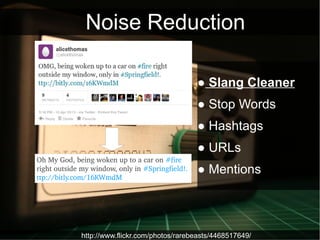
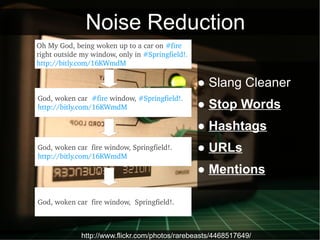
![Noise Reduction
God, woken car fire window, Springfield!.
● Slang Cleaner
● Stop Words
NER Analyser
● Hashtags
● URLs
● Mentions
Springfield [LOCATION].
http://www.flickr.com/photos/rarebeasts/4468517649/](https://image.slidesharecdn.com/presentacion-130417090403-phpapp01/85/Enable-tweet-geolocation-and-don-t-drive-ERTs-crazy-10-320.jpg)