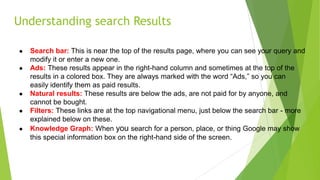
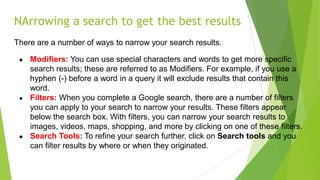
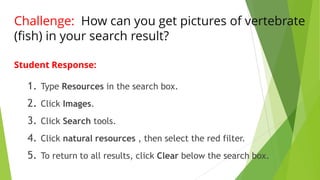
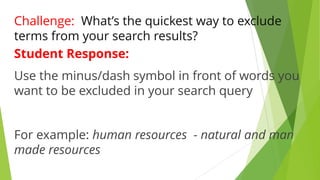
The document emphasizes the importance of 'search smart' skills for students and teachers, highlighting how effective searches can enhance learning and critical thinking. It outlines the basics of smart searching, which include choosing the right search terms, understanding search results, and narrowing searches through various modifiers and filters. Additionally, it provides examples of search techniques and encourages students to evaluate the credibility of websites.