Embed presentation
Downloaded 20 times



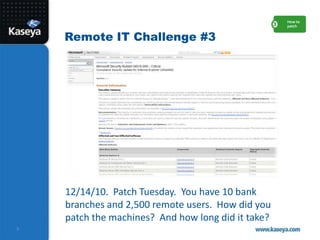
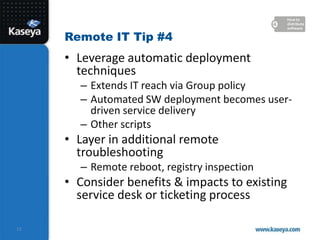
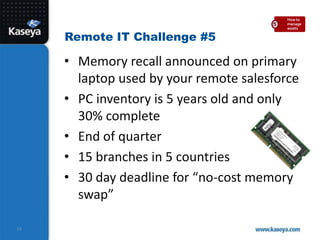
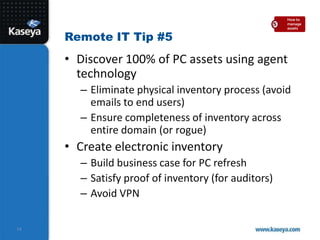
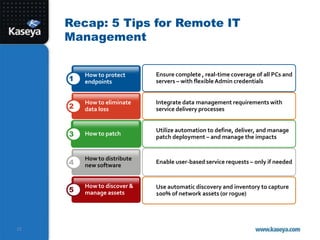




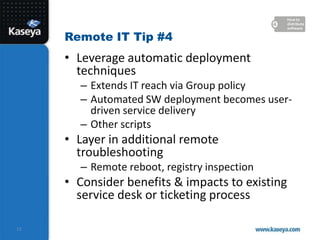
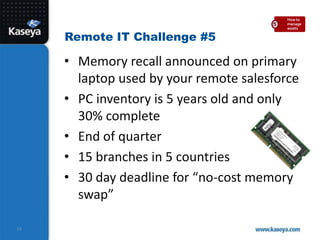
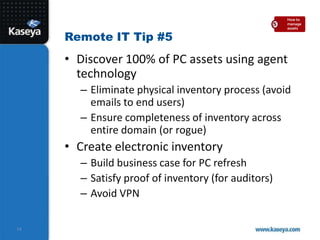
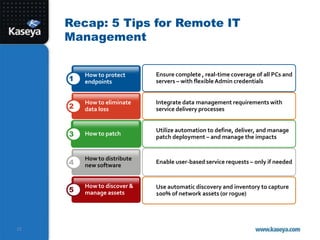
The document outlines five key strategies for managing remote IT systems effectively, focusing on protecting endpoints, eliminating data loss, automating patch delivery, distributing software, and managing IT assets. It emphasizes the increased need for remote IT management due to the rise in mobile workforce and distributed data environments, while providing tips and challenges related to each strategy. Additionally, it highlights Kaseya's solutions for streamlining these processes and improving overall IT management efficiency.