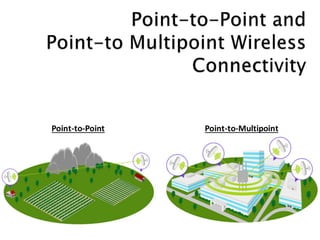
Point to-point and point-to multipoint wireless connectivity
•Download as PPTX, PDF•
1 like•586 views
Get Wireless Communication like Point-to-Point, and Point-to-Multipoint from Dtech Computers. Network architecture for outdoor wireless networks to connect multiple locations to one single central location or one location to another.
Report
Share
Report
Share
Recommended
TCP and UDP 

TCP and UDP are transport layer protocols used for data transfer in the OSI model. TCP is connection-oriented, requiring a three-way handshake to establish a connection that maintains data integrity. It guarantees data will reach its destination without duplication but is slower than UDP. UDP is connectionless and used for applications requiring fast transmission like video calls, but does not ensure packet delivery and order. Both protocols add headers to packets with TCP focused on reliability and UDP on speed.
Mobile Computing UNIT-6

This document discusses synchronization in mobile computing systems. It describes how data is replicated and distributed across mobile devices, personal computers, and remote servers. It then discusses various synchronization techniques used to maintain consistency between distributed copies of data, including one-way synchronization initiated by the server or client, two-way synchronization, and refresh synchronization. The document also covers domain-specific rules that govern how data is synchronized across different platforms and data formats.
Circuit and packet_switching

Packet switching and circuit switching are two different technologies for sending messages over networks. Packet switching breaks messages into packets that can take different routes to the destination, while circuit switching establishes a dedicated connection for the duration of the call. Each approach has advantages - packet switching uses bandwidth efficiently but can experience delays, while circuit switching guarantees quality but is inefficient. Modern networks are shifting more towards packet switching as it allows for easier scaling.
Topic: ISDN (Integrated Services Digital Network)

These slides cover a topic on ISDN (Integrated Services Digital Network) in Data Communication. All the slides are explained in a very simple manner. It is useful for engineering students & also for the candidates who want to master data communication & computer networking.
Wireless Sensor Networks ppt

This document summarizes a seminar presentation on wireless sensor networks (WSNs). It begins with introductions to WSNs, describing them as networks of spatially distributed sensors that monitor conditions like temperature, sound or pollution. It then covers the architecture of WSNs, including special addressing requirements, the architecture of sensor nodes, and differences between WSNs and mobile ad hoc networks. The document discusses applications, design challenges, advantages and disadvantages of WSNs. It concludes by discussing the future potential of WSNs in applications like smart homes and offices.
Guided and unguided media

Guided media uses physical cabling to guide transmission signals along a specific path and includes twisted pair cable, coaxial cable, and optical fiber. Twisted pair cable consists of two insulated copper wires twisted together, and can be unshielded or shielded. Coaxial cable contains two conductors separated by insulation. Fiber optic cable transmits information using pulses of light through glass cores. Unguided media uses electromagnetic waves to transmit without cabling through radio waves, microwaves, or infrared signals broadcast through free space. Radio waves can travel long distances, microwaves require line-of-sight and focused antennas, while infrared works for short-range indoor use.
Introduction & history of mobile computing

The document provides a history and overview of mobile computing. It discusses how mobile computing allows transmission of data, voice and video without a fixed physical link. It defines mobility and different types of mobile devices. The document then covers wireless communication technologies and contrasts wired vs wireless networks. It discusses advantages and disadvantages of wireless networks. The document traces the evolution of wireless technology from early radio experiments to the development of cellular networks and standards.
Basics of computer networks

What is Computer Network? What is Networking? Application of Networks. Network criteria. Types of Network. LAN, MAN, WAN, Workstation, Workgroup, Domain.
Recommended
TCP and UDP 

TCP and UDP are transport layer protocols used for data transfer in the OSI model. TCP is connection-oriented, requiring a three-way handshake to establish a connection that maintains data integrity. It guarantees data will reach its destination without duplication but is slower than UDP. UDP is connectionless and used for applications requiring fast transmission like video calls, but does not ensure packet delivery and order. Both protocols add headers to packets with TCP focused on reliability and UDP on speed.
Mobile Computing UNIT-6

This document discusses synchronization in mobile computing systems. It describes how data is replicated and distributed across mobile devices, personal computers, and remote servers. It then discusses various synchronization techniques used to maintain consistency between distributed copies of data, including one-way synchronization initiated by the server or client, two-way synchronization, and refresh synchronization. The document also covers domain-specific rules that govern how data is synchronized across different platforms and data formats.
Circuit and packet_switching

Packet switching and circuit switching are two different technologies for sending messages over networks. Packet switching breaks messages into packets that can take different routes to the destination, while circuit switching establishes a dedicated connection for the duration of the call. Each approach has advantages - packet switching uses bandwidth efficiently but can experience delays, while circuit switching guarantees quality but is inefficient. Modern networks are shifting more towards packet switching as it allows for easier scaling.
Topic: ISDN (Integrated Services Digital Network)

These slides cover a topic on ISDN (Integrated Services Digital Network) in Data Communication. All the slides are explained in a very simple manner. It is useful for engineering students & also for the candidates who want to master data communication & computer networking.
Wireless Sensor Networks ppt

This document summarizes a seminar presentation on wireless sensor networks (WSNs). It begins with introductions to WSNs, describing them as networks of spatially distributed sensors that monitor conditions like temperature, sound or pollution. It then covers the architecture of WSNs, including special addressing requirements, the architecture of sensor nodes, and differences between WSNs and mobile ad hoc networks. The document discusses applications, design challenges, advantages and disadvantages of WSNs. It concludes by discussing the future potential of WSNs in applications like smart homes and offices.
Guided and unguided media

Guided media uses physical cabling to guide transmission signals along a specific path and includes twisted pair cable, coaxial cable, and optical fiber. Twisted pair cable consists of two insulated copper wires twisted together, and can be unshielded or shielded. Coaxial cable contains two conductors separated by insulation. Fiber optic cable transmits information using pulses of light through glass cores. Unguided media uses electromagnetic waves to transmit without cabling through radio waves, microwaves, or infrared signals broadcast through free space. Radio waves can travel long distances, microwaves require line-of-sight and focused antennas, while infrared works for short-range indoor use.
Introduction & history of mobile computing

The document provides a history and overview of mobile computing. It discusses how mobile computing allows transmission of data, voice and video without a fixed physical link. It defines mobility and different types of mobile devices. The document then covers wireless communication technologies and contrasts wired vs wireless networks. It discusses advantages and disadvantages of wireless networks. The document traces the evolution of wireless technology from early radio experiments to the development of cellular networks and standards.
Basics of computer networks

What is Computer Network? What is Networking? Application of Networks. Network criteria. Types of Network. LAN, MAN, WAN, Workstation, Workgroup, Domain.
Transmission Medium

Transmission media are located below the physical layer and are used to transmit signals representing data in the form of electromagnetic energy. There are two main types of transmission media: guided and unguided. Guided media like twisted pair cable, coaxial cable, and fiber optic cable provide a conduit for transmission. Factors like transmission rate, cost, environmental resistance, and distance must be considered when choosing a transmission medium. Twisted pair is the most commonly used guided medium and comes in shielded and unshielded varieties. Coaxial cable provides higher bandwidth but is more difficult to install. Fiber optic cable has the highest bandwidth but is also the most expensive. Unguided media like radio waves, infrared, and microwaves transmit
Guided Transmission Media

The Presentation describes about the Transmission media and in detail about coaxial cable,Twisted pair, Fiber optics, Power lines and their comparisons
Tcp/ip model

The document describes the TCP/IP model and its layers:
1. The application layer contains common protocols like FTP, SMTP, HTTP, and DNS.
2. The transport layer contains TCP and UDP which manage end-to-end message transmission and error handling.
3. The network layer is IP which handles routing and congestion of data packets.
4. The lower layers include the data link layer which manages reliable data delivery to physical networks, and the physical layer which defines the physical media.
TCP/IP Network ppt

The document provides an overview of the TCP/IP model, describing each layer from application to network. The application layer allows programs access to networked services and contains high-level protocols like TCP and UDP. The transport layer handles reliable delivery via protocols like TCP and UDP. The internet layer organizes routing with the IP protocol. The network layer consists of device drivers and network interface cards that communicate with the physical transmission media.
Ppt for tranmission media

Transmission media are located below the physical layer and are used to transmit signals representing data. There are two main types of transmission media: guided media (wired), which provide a conduit for transmission, and unguided media (wireless), which transmit via electromagnetic waves without a physical pathway. Common guided media include twisted-pair cable, coaxial cable, and fiber-optic cable. Unguided media include radio waves, microwaves, and infrared. Each type of transmission media has different characteristics that determine its suitable uses.
Structure of Telephone System.pptx

The telephone system consists of three major components: local loops connecting subscribers to end offices, trunks connecting the switching offices, and switching offices that route calls between trunks. Early telephone systems connected each telephone directly to every other telephone, but this model did not scale. The modern system uses a hierarchical structure of switching offices - including end offices, toll offices, primary offices, and regional offices - connected by digital trunks to route calls across long distances. Local loops remain the last analog component, connecting subscribers to end offices by twisted pair.
Computer network ppt

A computer network connects multiple computers and devices to allow communication and sharing of resources. There are different types of networks including local area networks (LANs) within a single building, metropolitan area networks (MANs) within a city, and wide area networks (WANs) across large distances like countries. Common network topologies include bus, ring, star, tree and mesh configurations. Computer networks enable file sharing, printer sharing, collaboration, remote access, data protection, and centralized administration.
switching techniques in data communication and networking

This document discusses different types of network switching: circuit switching, packet switching, and message switching. It describes circuit switching as establishing a dedicated electrical path for communication between two ports. Packet switching breaks communication down into small packets that are routed through the network based on destination addresses. There are two approaches for packet switching - datagram and virtual circuit. Datagram packets can take different paths to the destination while virtual circuit establishes a pre-planned route. Message switching does not establish a dedicated path, and each message is treated independently with the destination address added. The document was submitted by several students to their professor.
Wireless network

Wireless networks allow devices to connect to a network without being physically connected by cables. They work by transmitting radio signals that carry data between wireless devices and access points or base stations. There are different types of wireless networks including WLANs for local areas like campuses, WPANs for personal networks using technologies like Bluetooth, and WMANs for connecting multiple networks over a metropolitan area. Wireless networks offer mobility and flexibility compared to wired networks but have lower bandwidth and speeds. Common applications of wireless networks include mobile access to the internet, extending wired networks wirelessly, and connecting remote areas without wired infrastructure.
Multiplexing

All Necessary information about Multiplexing is provided in this. Full Class of Analog and Digital Multiplexing. And also Include
FDM, WDM, TDM.
Distributed Multimedia Systems(DMMS)

This document discusses distributed multimedia systems (DMMS). It defines DMMS as consisting of multimedia databases, proxy servers, and clients intended to distribute multimedia content over networks. Key requirements of DMMS include supporting continuous media like audio and video, quality of service management to ensure requests are met, and multiparty communications. The document outlines the basic DMMS architecture and discusses factors like server bandwidth that affect the system. It also covers approaches like proxy-based and clustered servers, as well as quality of service management through techniques such as buffering, bandwidth reservation and traffic shaping. Examples of DMMS applications include digital libraries, distance learning, and audio/video streaming.
Circuit Switching

Circuit switching is a method of establishing a dedicated communication path or circuit between two endpoints in a network before transmission begins. It requires reserving bandwidth throughout the network for the duration of the connection. A circuit-switched network establishes a physical path and dedicates resources to a single connection. It operates in three phases: circuit establishment, data transfer, and circuit disconnection. The public telephone network is an example of a circuit-switched network.
Mobile Network Layer

Mobile Network Layer protocols and mechanisms allow nodes to change their point of attachment to different networks while maintaining ongoing communication. Key concepts include:
- Mobile IP adds mobility support to IP, allowing nodes to use the same IP address even when changing networks. It relies on home agents and care-of addresses.
- Registration allows mobile nodes to inform their home agent of their current location when visiting foreign networks. Tunneling and encapsulation techniques are used to forward packets to mobile nodes' current locations.
- Various routing protocols like DSDV have been developed for mobile ad hoc networks which have no fixed infrastructure and dynamic topologies.
Evolution of Mobile Network Technology

What is the difference between mobile networks? In this presentation we tried to show the evolution of mobile network technology up to 5G.
Read our Short Review on Generation of Mobile Network Technology (1G, 2G, 2.5G 3G, 4G, 5G)
Umts system architecture

Universal Mobile Telecommunications System (UMTS) a 3G cellular system for networks based on the GSM standard.
IT6601 MOBILE COMPUTING

Unit - I
Mobile Computing – Mobile Computing Vs wireless Networking – Mobile Computing Applications – Characteristics of Mobile computing – Structure of Mobile Computing Application. MAC Protocols – Wireless MAC Issues – Fixed Assignment Schemes – Random Assignment Schemes – Reservation Based Schemes.
Introduction To Mobile Computing

The document provides an introduction to mobile computing. It discusses how mobile computing allows transmission of data without a fixed physical link. It describes the growth of mobile voice communication and how mobile data communication has become important. It discusses existing cellular network architecture and technologies like GSM. It covers advances in technology that have enabled mobile computing. It describes the different types of device mobility and portability. It provides examples of mobile computing applications in vehicles, emergencies, business, and for information services. It also discusses the history and market for mobile communications and some open research topics in the field.
Transmission Impairment

With any communications system, it must be recognized that the received signal may differ from the transmitted signal due to various transmission impairments.
Circuit Switching, Packet Switching, Virtual Circuit Networks and Datagram Ne...

This Slide includes the description about Circuit Switching, Packet Switching, Virtual Circuit Networks and Datagram Networks
Mobile computing notes and material

Here are the key points about guided and unguided transmission:
- Guided transmission uses physical media like wires and fiber optics to transmit signals along a directed path from transmitter to receiver. It allows for high-quality transmission but limits mobility.
- Unguided or wireless transmission converts signals to electromagnetic waves that can transmit through open space. It allows mobility as devices can communicate anywhere within range of a cell tower or access point. However, wireless signals can be interrupted by interference.
- Mobile communication involves transmission of data to/from handheld devices, with at least one being mobile. It uses wireless networks for mobility as users move around.
Unlock the Future of Search with MongoDB Atlas_ Vector Search Unleashed.pdf

Discover how MongoDB Atlas and vector search technology can revolutionize your application's search capabilities. This comprehensive presentation covers:
* What is Vector Search?
* Importance and benefits of vector search
* Practical use cases across various industries
* Step-by-step implementation guide
* Live demos with code snippets
* Enhancing LLM capabilities with vector search
* Best practices and optimization strategies
Perfect for developers, AI enthusiasts, and tech leaders. Learn how to leverage MongoDB Atlas to deliver highly relevant, context-aware search results, transforming your data retrieval process. Stay ahead in tech innovation and maximize the potential of your applications.
#MongoDB #VectorSearch #AI #SemanticSearch #TechInnovation #DataScience #LLM #MachineLearning #SearchTechnology
June Patch Tuesday

Ivanti’s Patch Tuesday breakdown goes beyond patching your applications and brings you the intelligence and guidance needed to prioritize where to focus your attention first. Catch early analysis on our Ivanti blog, then join industry expert Chris Goettl for the Patch Tuesday Webinar Event. There we’ll do a deep dive into each of the bulletins and give guidance on the risks associated with the newly-identified vulnerabilities.
More Related Content
What's hot
Transmission Medium

Transmission media are located below the physical layer and are used to transmit signals representing data in the form of electromagnetic energy. There are two main types of transmission media: guided and unguided. Guided media like twisted pair cable, coaxial cable, and fiber optic cable provide a conduit for transmission. Factors like transmission rate, cost, environmental resistance, and distance must be considered when choosing a transmission medium. Twisted pair is the most commonly used guided medium and comes in shielded and unshielded varieties. Coaxial cable provides higher bandwidth but is more difficult to install. Fiber optic cable has the highest bandwidth but is also the most expensive. Unguided media like radio waves, infrared, and microwaves transmit
Guided Transmission Media

The Presentation describes about the Transmission media and in detail about coaxial cable,Twisted pair, Fiber optics, Power lines and their comparisons
Tcp/ip model

The document describes the TCP/IP model and its layers:
1. The application layer contains common protocols like FTP, SMTP, HTTP, and DNS.
2. The transport layer contains TCP and UDP which manage end-to-end message transmission and error handling.
3. The network layer is IP which handles routing and congestion of data packets.
4. The lower layers include the data link layer which manages reliable data delivery to physical networks, and the physical layer which defines the physical media.
TCP/IP Network ppt

The document provides an overview of the TCP/IP model, describing each layer from application to network. The application layer allows programs access to networked services and contains high-level protocols like TCP and UDP. The transport layer handles reliable delivery via protocols like TCP and UDP. The internet layer organizes routing with the IP protocol. The network layer consists of device drivers and network interface cards that communicate with the physical transmission media.
Ppt for tranmission media

Transmission media are located below the physical layer and are used to transmit signals representing data. There are two main types of transmission media: guided media (wired), which provide a conduit for transmission, and unguided media (wireless), which transmit via electromagnetic waves without a physical pathway. Common guided media include twisted-pair cable, coaxial cable, and fiber-optic cable. Unguided media include radio waves, microwaves, and infrared. Each type of transmission media has different characteristics that determine its suitable uses.
Structure of Telephone System.pptx

The telephone system consists of three major components: local loops connecting subscribers to end offices, trunks connecting the switching offices, and switching offices that route calls between trunks. Early telephone systems connected each telephone directly to every other telephone, but this model did not scale. The modern system uses a hierarchical structure of switching offices - including end offices, toll offices, primary offices, and regional offices - connected by digital trunks to route calls across long distances. Local loops remain the last analog component, connecting subscribers to end offices by twisted pair.
Computer network ppt

A computer network connects multiple computers and devices to allow communication and sharing of resources. There are different types of networks including local area networks (LANs) within a single building, metropolitan area networks (MANs) within a city, and wide area networks (WANs) across large distances like countries. Common network topologies include bus, ring, star, tree and mesh configurations. Computer networks enable file sharing, printer sharing, collaboration, remote access, data protection, and centralized administration.
switching techniques in data communication and networking

This document discusses different types of network switching: circuit switching, packet switching, and message switching. It describes circuit switching as establishing a dedicated electrical path for communication between two ports. Packet switching breaks communication down into small packets that are routed through the network based on destination addresses. There are two approaches for packet switching - datagram and virtual circuit. Datagram packets can take different paths to the destination while virtual circuit establishes a pre-planned route. Message switching does not establish a dedicated path, and each message is treated independently with the destination address added. The document was submitted by several students to their professor.
Wireless network

Wireless networks allow devices to connect to a network without being physically connected by cables. They work by transmitting radio signals that carry data between wireless devices and access points or base stations. There are different types of wireless networks including WLANs for local areas like campuses, WPANs for personal networks using technologies like Bluetooth, and WMANs for connecting multiple networks over a metropolitan area. Wireless networks offer mobility and flexibility compared to wired networks but have lower bandwidth and speeds. Common applications of wireless networks include mobile access to the internet, extending wired networks wirelessly, and connecting remote areas without wired infrastructure.
Multiplexing

All Necessary information about Multiplexing is provided in this. Full Class of Analog and Digital Multiplexing. And also Include
FDM, WDM, TDM.
Distributed Multimedia Systems(DMMS)

This document discusses distributed multimedia systems (DMMS). It defines DMMS as consisting of multimedia databases, proxy servers, and clients intended to distribute multimedia content over networks. Key requirements of DMMS include supporting continuous media like audio and video, quality of service management to ensure requests are met, and multiparty communications. The document outlines the basic DMMS architecture and discusses factors like server bandwidth that affect the system. It also covers approaches like proxy-based and clustered servers, as well as quality of service management through techniques such as buffering, bandwidth reservation and traffic shaping. Examples of DMMS applications include digital libraries, distance learning, and audio/video streaming.
Circuit Switching

Circuit switching is a method of establishing a dedicated communication path or circuit between two endpoints in a network before transmission begins. It requires reserving bandwidth throughout the network for the duration of the connection. A circuit-switched network establishes a physical path and dedicates resources to a single connection. It operates in three phases: circuit establishment, data transfer, and circuit disconnection. The public telephone network is an example of a circuit-switched network.
Mobile Network Layer

Mobile Network Layer protocols and mechanisms allow nodes to change their point of attachment to different networks while maintaining ongoing communication. Key concepts include:
- Mobile IP adds mobility support to IP, allowing nodes to use the same IP address even when changing networks. It relies on home agents and care-of addresses.
- Registration allows mobile nodes to inform their home agent of their current location when visiting foreign networks. Tunneling and encapsulation techniques are used to forward packets to mobile nodes' current locations.
- Various routing protocols like DSDV have been developed for mobile ad hoc networks which have no fixed infrastructure and dynamic topologies.
Evolution of Mobile Network Technology

What is the difference between mobile networks? In this presentation we tried to show the evolution of mobile network technology up to 5G.
Read our Short Review on Generation of Mobile Network Technology (1G, 2G, 2.5G 3G, 4G, 5G)
Umts system architecture

Universal Mobile Telecommunications System (UMTS) a 3G cellular system for networks based on the GSM standard.
IT6601 MOBILE COMPUTING

Unit - I
Mobile Computing – Mobile Computing Vs wireless Networking – Mobile Computing Applications – Characteristics of Mobile computing – Structure of Mobile Computing Application. MAC Protocols – Wireless MAC Issues – Fixed Assignment Schemes – Random Assignment Schemes – Reservation Based Schemes.
Introduction To Mobile Computing

The document provides an introduction to mobile computing. It discusses how mobile computing allows transmission of data without a fixed physical link. It describes the growth of mobile voice communication and how mobile data communication has become important. It discusses existing cellular network architecture and technologies like GSM. It covers advances in technology that have enabled mobile computing. It describes the different types of device mobility and portability. It provides examples of mobile computing applications in vehicles, emergencies, business, and for information services. It also discusses the history and market for mobile communications and some open research topics in the field.
Transmission Impairment

With any communications system, it must be recognized that the received signal may differ from the transmitted signal due to various transmission impairments.
Circuit Switching, Packet Switching, Virtual Circuit Networks and Datagram Ne...

This Slide includes the description about Circuit Switching, Packet Switching, Virtual Circuit Networks and Datagram Networks
Mobile computing notes and material

Here are the key points about guided and unguided transmission:
- Guided transmission uses physical media like wires and fiber optics to transmit signals along a directed path from transmitter to receiver. It allows for high-quality transmission but limits mobility.
- Unguided or wireless transmission converts signals to electromagnetic waves that can transmit through open space. It allows mobility as devices can communicate anywhere within range of a cell tower or access point. However, wireless signals can be interrupted by interference.
- Mobile communication involves transmission of data to/from handheld devices, with at least one being mobile. It uses wireless networks for mobility as users move around.
What's hot (20)
switching techniques in data communication and networking

switching techniques in data communication and networking
Circuit Switching, Packet Switching, Virtual Circuit Networks and Datagram Ne...

Circuit Switching, Packet Switching, Virtual Circuit Networks and Datagram Ne...
Recently uploaded
Unlock the Future of Search with MongoDB Atlas_ Vector Search Unleashed.pdf

Discover how MongoDB Atlas and vector search technology can revolutionize your application's search capabilities. This comprehensive presentation covers:
* What is Vector Search?
* Importance and benefits of vector search
* Practical use cases across various industries
* Step-by-step implementation guide
* Live demos with code snippets
* Enhancing LLM capabilities with vector search
* Best practices and optimization strategies
Perfect for developers, AI enthusiasts, and tech leaders. Learn how to leverage MongoDB Atlas to deliver highly relevant, context-aware search results, transforming your data retrieval process. Stay ahead in tech innovation and maximize the potential of your applications.
#MongoDB #VectorSearch #AI #SemanticSearch #TechInnovation #DataScience #LLM #MachineLearning #SearchTechnology
June Patch Tuesday

Ivanti’s Patch Tuesday breakdown goes beyond patching your applications and brings you the intelligence and guidance needed to prioritize where to focus your attention first. Catch early analysis on our Ivanti blog, then join industry expert Chris Goettl for the Patch Tuesday Webinar Event. There we’ll do a deep dive into each of the bulletins and give guidance on the risks associated with the newly-identified vulnerabilities.
Salesforce Integration for Bonterra Impact Management (fka Social Solutions A...

Sidekick Solutions uses Bonterra Impact Management (fka Social Solutions Apricot) and automation solutions to integrate data for business workflows.
We believe integration and automation are essential to user experience and the promise of efficient work through technology. Automation is the critical ingredient to realizing that full vision. We develop integration products and services for Bonterra Case Management software to support the deployment of automations for a variety of use cases.
This video focuses on integration of Salesforce with Bonterra Impact Management.
Interested in deploying an integration with Salesforce for Bonterra Impact Management? Contact us at sales@sidekicksolutionsllc.com to discuss next steps.
HCL Notes und Domino Lizenzkostenreduzierung in der Welt von DLAU

Webinar Recording: https://www.panagenda.com/webinars/hcl-notes-und-domino-lizenzkostenreduzierung-in-der-welt-von-dlau/
DLAU und die Lizenzen nach dem CCB- und CCX-Modell sind für viele in der HCL-Community seit letztem Jahr ein heißes Thema. Als Notes- oder Domino-Kunde haben Sie vielleicht mit unerwartet hohen Benutzerzahlen und Lizenzgebühren zu kämpfen. Sie fragen sich vielleicht, wie diese neue Art der Lizenzierung funktioniert und welchen Nutzen sie Ihnen bringt. Vor allem wollen Sie sicherlich Ihr Budget einhalten und Kosten sparen, wo immer möglich. Das verstehen wir und wir möchten Ihnen dabei helfen!
Wir erklären Ihnen, wie Sie häufige Konfigurationsprobleme lösen können, die dazu führen können, dass mehr Benutzer gezählt werden als nötig, und wie Sie überflüssige oder ungenutzte Konten identifizieren und entfernen können, um Geld zu sparen. Es gibt auch einige Ansätze, die zu unnötigen Ausgaben führen können, z. B. wenn ein Personendokument anstelle eines Mail-Ins für geteilte Mailboxen verwendet wird. Wir zeigen Ihnen solche Fälle und deren Lösungen. Und natürlich erklären wir Ihnen das neue Lizenzmodell.
Nehmen Sie an diesem Webinar teil, bei dem HCL-Ambassador Marc Thomas und Gastredner Franz Walder Ihnen diese neue Welt näherbringen. Es vermittelt Ihnen die Tools und das Know-how, um den Überblick zu bewahren. Sie werden in der Lage sein, Ihre Kosten durch eine optimierte Domino-Konfiguration zu reduzieren und auch in Zukunft gering zu halten.
Diese Themen werden behandelt
- Reduzierung der Lizenzkosten durch Auffinden und Beheben von Fehlkonfigurationen und überflüssigen Konten
- Wie funktionieren CCB- und CCX-Lizenzen wirklich?
- Verstehen des DLAU-Tools und wie man es am besten nutzt
- Tipps für häufige Problembereiche, wie z. B. Team-Postfächer, Funktions-/Testbenutzer usw.
- Praxisbeispiele und Best Practices zum sofortigen Umsetzen
Letter and Document Automation for Bonterra Impact Management (fka Social Sol...

Sidekick Solutions uses Bonterra Impact Management (fka Social Solutions Apricot) and automation solutions to integrate data for business workflows.
We believe integration and automation are essential to user experience and the promise of efficient work through technology. Automation is the critical ingredient to realizing that full vision. We develop integration products and services for Bonterra Case Management software to support the deployment of automations for a variety of use cases.
This video focuses on automated letter generation for Bonterra Impact Management using Google Workspace or Microsoft 365.
Interested in deploying letter generation automations for Bonterra Impact Management? Contact us at sales@sidekicksolutionsllc.com to discuss next steps.
Let's Integrate MuleSoft RPA, COMPOSER, APM with AWS IDP along with Slack

Discover the seamless integration of RPA (Robotic Process Automation), COMPOSER, and APM with AWS IDP enhanced with Slack notifications. Explore how these technologies converge to streamline workflows, optimize performance, and ensure secure access, all while leveraging the power of AWS IDP and real-time communication via Slack notifications.
HCL Notes and Domino License Cost Reduction in the World of DLAU

Webinar Recording: https://www.panagenda.com/webinars/hcl-notes-and-domino-license-cost-reduction-in-the-world-of-dlau/
The introduction of DLAU and the CCB & CCX licensing model caused quite a stir in the HCL community. As a Notes and Domino customer, you may have faced challenges with unexpected user counts and license costs. You probably have questions on how this new licensing approach works and how to benefit from it. Most importantly, you likely have budget constraints and want to save money where possible. Don’t worry, we can help with all of this!
We’ll show you how to fix common misconfigurations that cause higher-than-expected user counts, and how to identify accounts which you can deactivate to save money. There are also frequent patterns that can cause unnecessary cost, like using a person document instead of a mail-in for shared mailboxes. We’ll provide examples and solutions for those as well. And naturally we’ll explain the new licensing model.
Join HCL Ambassador Marc Thomas in this webinar with a special guest appearance from Franz Walder. It will give you the tools and know-how to stay on top of what is going on with Domino licensing. You will be able lower your cost through an optimized configuration and keep it low going forward.
These topics will be covered
- Reducing license cost by finding and fixing misconfigurations and superfluous accounts
- How do CCB and CCX licenses really work?
- Understanding the DLAU tool and how to best utilize it
- Tips for common problem areas, like team mailboxes, functional/test users, etc
- Practical examples and best practices to implement right away
Digital Marketing Trends in 2024 | Guide for Staying Ahead

https://www.wask.co/ebooks/digital-marketing-trends-in-2024
Feeling lost in the digital marketing whirlwind of 2024? Technology is changing, consumer habits are evolving, and staying ahead of the curve feels like a never-ending pursuit. This e-book is your compass. Dive into actionable insights to handle the complexities of modern marketing. From hyper-personalization to the power of user-generated content, learn how to build long-term relationships with your audience and unlock the secrets to success in the ever-shifting digital landscape.
Finale of the Year: Apply for Next One!

Presentation for the event called "Finale of the Year: Apply for Next One!" organized by GDSC PJATK
TrustArc Webinar - 2024 Global Privacy Survey

How does your privacy program stack up against your peers? What challenges are privacy teams tackling and prioritizing in 2024?
In the fifth annual Global Privacy Benchmarks Survey, we asked over 1,800 global privacy professionals and business executives to share their perspectives on the current state of privacy inside and outside of their organizations. This year’s report focused on emerging areas of importance for privacy and compliance professionals, including considerations and implications of Artificial Intelligence (AI) technologies, building brand trust, and different approaches for achieving higher privacy competence scores.
See how organizational priorities and strategic approaches to data security and privacy are evolving around the globe.
This webinar will review:
- The top 10 privacy insights from the fifth annual Global Privacy Benchmarks Survey
- The top challenges for privacy leaders, practitioners, and organizations in 2024
- Key themes to consider in developing and maintaining your privacy program
dbms calicut university B. sc Cs 4th sem.pdf

Its a seminar ppt on database management system using sql
Choosing The Best AWS Service For Your Website + API.pptx

Have you ever been confused by the myriad of choices offered by AWS for hosting a website or an API?
Lambda, Elastic Beanstalk, Lightsail, Amplify, S3 (and more!) can each host websites + APIs. But which one should we choose?
Which one is cheapest? Which one is fastest? Which one will scale to meet our needs?
Join me in this session as we dive into each AWS hosting service to determine which one is best for your scenario and explain why!
Columbus Data & Analytics Wednesdays - June 2024

Columbus Data & Analytics Wednesdays, June 2024 with Maria Copot 20
Introduction of Cybersecurity with OSS at Code Europe 2024

I develop the Ruby programming language, RubyGems, and Bundler, which are package managers for Ruby. Today, I will introduce how to enhance the security of your application using open-source software (OSS) examples from Ruby and RubyGems.
The first topic is CVE (Common Vulnerabilities and Exposures). I have published CVEs many times. But what exactly is a CVE? I'll provide a basic understanding of CVEs and explain how to detect and handle vulnerabilities in OSS.
Next, let's discuss package managers. Package managers play a critical role in the OSS ecosystem. I'll explain how to manage library dependencies in your application.
I'll share insights into how the Ruby and RubyGems core team works to keep our ecosystem safe. By the end of this talk, you'll have a better understanding of how to safeguard your code.
Recently uploaded (20)
Unlock the Future of Search with MongoDB Atlas_ Vector Search Unleashed.pdf

Unlock the Future of Search with MongoDB Atlas_ Vector Search Unleashed.pdf
Salesforce Integration for Bonterra Impact Management (fka Social Solutions A...

Salesforce Integration for Bonterra Impact Management (fka Social Solutions A...
HCL Notes und Domino Lizenzkostenreduzierung in der Welt von DLAU

HCL Notes und Domino Lizenzkostenreduzierung in der Welt von DLAU
Letter and Document Automation for Bonterra Impact Management (fka Social Sol...

Letter and Document Automation for Bonterra Impact Management (fka Social Sol...
Let's Integrate MuleSoft RPA, COMPOSER, APM with AWS IDP along with Slack

Let's Integrate MuleSoft RPA, COMPOSER, APM with AWS IDP along with Slack
HCL Notes and Domino License Cost Reduction in the World of DLAU

HCL Notes and Domino License Cost Reduction in the World of DLAU
Deep Dive: AI-Powered Marketing to Get More Leads and Customers with HyperGro...

Deep Dive: AI-Powered Marketing to Get More Leads and Customers with HyperGro...
Digital Marketing Trends in 2024 | Guide for Staying Ahead

Digital Marketing Trends in 2024 | Guide for Staying Ahead
Nordic Marketo Engage User Group_June 13_ 2024.pptx

Nordic Marketo Engage User Group_June 13_ 2024.pptx
Deep Dive: Getting Funded with Jason Jason Lemkin Founder & CEO @ SaaStr

Deep Dive: Getting Funded with Jason Jason Lemkin Founder & CEO @ SaaStr
Choosing The Best AWS Service For Your Website + API.pptx

Choosing The Best AWS Service For Your Website + API.pptx
Overcoming the PLG Trap: Lessons from Canva's Head of Sales & Head of EMEA Da...

Overcoming the PLG Trap: Lessons from Canva's Head of Sales & Head of EMEA Da...
Introduction of Cybersecurity with OSS at Code Europe 2024

Introduction of Cybersecurity with OSS at Code Europe 2024
Point to-point and point-to multipoint wireless connectivity
- 2. Point to point communication is the easiest and most effective way to provide a wireless connection from one location or building to another, without the need for wire leasing fees.
- 3. In Wireless communications, Point-to- Multipoint communication (P2MP, PTMP or PMP) is communication which is accomplished via a distinct type of one-to-many connection, providing multiple paths from a single location to multiple locations.
- 4. Building to Building Connectivity Leased Line Replacement Fiber Line Replacement Wireless Failover High Speed Connectivity
- 5. Connecting Multiple Buildings CCTV Solutions Lease Line Replacement Fiber Replacement Outdoor Wi-Fi