This document summarizes Yury Chemerkin's presentation at the Balkan Computer Congress on the inefficiency of security features on mobile devices regarding security and compliance. It discusses the relative security of different mobile operating systems like iOS, Android, BlackBerry and Windows Phone. It analyzes vulnerabilities, known issues, security capabilities and examines specific applications to analyze what sensitive data they may expose. It also covers topics like mobile device management, application security testing tools and the concurrency of native features and additional security controls.
![[ YURY CHEMERKIN ]
www.linkedin.com/in/yurychemerkin
http://sto-strategy.com
EXPERIENCED IN :
REVERSE ENGINEERING & AV
SOFTWARE PROGRAMMING & DOCUMENTATION
MOBILE SECURITY AND MDM
CYBER SECURITY & CLOUD SECURITY
COMPLIANCE & TRANSPARENCY
FORENSICS AND SECURITY WRITING
HAKIN9 / PENTEST / EFORENSICS MAGAZINE, GROTECK BUSINESS MEDIA
PARTICIPATION AT CONFERENCES
INFOSECURITYRUSSIA, NULLCON, ATHCON, CONFIDENCE, PHDAYS,
DEFCONMOSCOW, HACTIVITY, HACKFEST
CYBERCRIME FORUM, CYBER INTELLIGENCE EUROPE/INTELLIGENCE-SEC, DEEPINTEL
ICITST, CTICON (CYBERTIMES), ITA, I-SOCIETY
yury.s@chemerkin.com](https://image.slidesharecdn.com/28pdf-29-20yury-chemerkin-balccon-2013-140202131830-phpapp02/85/Pdf-yury-chemerkin-balccon_2013-2-320.jpg)
![[ OPINIONS ]
BLACKBERRY IS SAFER THAN WINDOWS THAT IS SAFER THAN iOS THAT IS SAFER THAN ANDROID IN TURN
APPLE’S CENTRALIZED POINT OF DISTRIBUTION
IS PROVIDING WITH CONFIDENCE THROUGH THE
VALIDATION BY APPLE, EXCEPT
THE SUBMISSION OF SUSPICIOUS APP BY
Ch. MILLER THAT HAD BEEN SUCCESSFULLY
APPROVED BY APPLE
INSTALLING CYDIA &THE REST APPS AFTER
THAT
MICROSOFT (WINDOWS PHONE) HAS A
CENTRALIZED MARKET WITH DEEPER TESTING
AND VALIDATION LIKE APPLE
GOOGLE PROVIDES A CENTRALIZED MARKET
TOO, HOWEVER PROVIDES ABILITY TO INSTALL
APPS FROM 3RD-PARTY SOURCES SUCH AS
AMAZON.
ANY OTHER ARE ORIGINATE FROM
MALWARE HOTSPOTS
ANY ALTERNATIVE MARKETS FOR SOCALLED “CRACKED” DISTRIBUTE FOR FREE
REPACKAGES
BLACKBERRY IS THE SAFEST OS BECAUSE IT IS
THE MOST MANAGEABLE AND SECURE MAINLY
AS IT IS ON AN ENTERPRISE WAY](https://image.slidesharecdn.com/28pdf-29-20yury-chemerkin-balccon-2013-140202131830-phpapp02/85/Pdf-yury-chemerkin-balccon_2013-3-320.jpg)
![2004
2005
2007
2007
2007
2008
2008
2008
2008
2008
2009
2009
2009
2009
2009
2009
2009
2009
2009
2010
2010
2010
2010
2010
2010
2010
2010
2011
2011
2011
2011
2011
2011
2011
2012
2012
2012
2012
2012
2012
2012
2012
2012
2012
2012
2012
2012
2013
2013
2013
2013
[ Vulnerabilities of OS and apps ]
10
9
8
7
6
5
4
3
2
1
0
Score - iOS
Score - Android
Score - BB](https://image.slidesharecdn.com/28pdf-29-20yury-chemerkin-balccon-2013-140202131830-phpapp02/85/Pdf-yury-chemerkin-balccon_2013-4-320.jpg)
![[ Vulnerabilities of OS and apps ]
MIN & AVERAGE SCORE
Android Average; 8,2
iOS Average; 6,3
BB-Average; 6,3
BB Min; 2,1
Android Min; 1,9
iOS Min; 1,2
Min & Average Score](https://image.slidesharecdn.com/28pdf-29-20yury-chemerkin-balccon-2013-140202131830-phpapp02/85/Pdf-yury-chemerkin-balccon_2013-5-320.jpg)
![[ SOURCE & BINARY ANALYSIS TOOLS ]
HEYDUDE, WHYIS IT VULNERABLEAGAIN?
HOW MANY THE TOOLS ARE (approx):
iOS – 10
ANDROID – 50
WINDOWS PHONE – 40
BLACKBERRY - 10
QUANTITY OF BUGS / SECURITY FLAWS
AVERAGE – 50
MIN – 20
MAX – INFINITY
WARINING :: ADS
VERACODE THE MOST USEFUL
SORRY,BIGBOSS,I’D JUST BEENCOMMITEDA WRONGBRANCH
BUGS TYPE (OBVIOUS | LIKELY)
MISSED CONSTRUCTIONS LIKE
DOUBLE/TRIPLE FREE ()
DEBUG PATHS, KEY, AND ETC.
PLAINTEXT & HARD-CODE PASSWORDS,
TOKENS, MASTER-KEYS, ETC.
NON-SECURE FLAWS, CONSTRUCTIONS,
ETC.
CHECK IT OUT
THE SQL-INJECTION IS POSSIBLE
THERE IS NO HTTPS HERE](https://image.slidesharecdn.com/28pdf-29-20yury-chemerkin-balccon-2013-140202131830-phpapp02/85/Pdf-yury-chemerkin-balccon_2013-6-320.jpg)
![[ MOBILE SECURITY CAPABILITIES ]
THE SAME CAPABILITIES AMONG MOBILE OPERATION SYSTEMS
SECURE BOOTLOADER
SYSTEM SOFTWARE SECURITY (UPDATES)
APPLICATION CODE SIGNING
RUNTIME PROCESS SECURITY
SANDBOX
APIs
HARDWARE SECURITY FEATURES
FILE DATA PROTECTION
SSL, TLS, VPN
PASSCODE PROTECTION
SETTINGS
PERMISSIONS/ RESTRICTIONS
CONFIGURATIONS
REMOTE MAGAGEMENT
MDM
REMOTE WIPE](https://image.slidesharecdn.com/28pdf-29-20yury-chemerkin-balccon-2013-140202131830-phpapp02/85/Pdf-yury-chemerkin-balccon_2013-7-320.jpg)
![[ SECURITY ENVIRONMENT ]
EACH OS EVALUATESEVERY REQUEST THAT AN APPLICATION MAKES TO ACCESSTO…
MDM SERVICES HELPS MANAGE AND PROTECT BLACKBERRY, IOS, WINDOWS, AND ANDROID DEVICES.
MDM SERVICES PROVIDE UNIFIED COMMUNICATION AND COLLABORATION SOFTWARE AND SERVICE (SaaS)
EACH OS IS DESIGNED TO PROTECT DATA IN TRANSIT, IN MEMORY AND STORAGE … AT ALL POINTS …
MDM SERVICES ENHANCED BY MANAGING THE BEHAVIOR OF THE DEVICE
OS PROVIDES A CAPABILITY TO PROTECT ANY APPLICATION DATA USING SANDBOXING
OS PROVIDES A CAPABILITY TO MANAGE PERMISSIONS TO ACCESS ITS CAPABILITIES
OS EVALUATES ALL REQUEST MADE BY APP ... BUT LEADS AWAY FROM ANY DETAILS AND APIs](https://image.slidesharecdn.com/28pdf-29-20yury-chemerkin-balccon-2013-140202131830-phpapp02/85/Pdf-yury-chemerkin-balccon_2013-8-320.jpg)
![[ KNOWN ISSUES ]
THREATSBOUNDSBECOME UNCLEAR…
ALL CONTROLLED OBJECTS ARE LIMITED BY
SANDBOX
PERMISSIONS
SECURITY FEATURES ON DEVICEs & MDMs
ADDITIONAL FEATURES AREN’T ACCESSIBLE ON
DEVICE
USER-MODE MALWARE
SPYWARE, ROOTKITS
EXPLOTS & ATTACKS
REVERSING NETWORK LAYER
RECOVERING DATA VS. SANBOX&MEMORY
EXPLOITING TO GET SUPER PRIVILIGIES
MDM& COMPLIANCE BRINGS COMMON
RECOMMENDATIONS
MDM vs. COMPLIANCE
COMMON RECOMMENDATIONS
SET IS LESSER THAN SET OF MDM FEATURES
QUITE BETTER TO MANAGE MDM SOLUTIONS
THAN DEVICE AT ALL
TOO FAR FROM DETAILS
YOUNG STANDARDS
FIRST REVISIONS, DRAFT REVISIONS
MOBILE SECURITY SOFWARE
READ-ONLY MODE / INFORMATION ONLY
APPLICATION FIREWALL (CALLS, MESSAGES…)
NETWORK FIREWALL REQUIRES ROOT
NO REAL SECURITY IF YOU BREAK A SANDBOX](https://image.slidesharecdn.com/28pdf-29-20yury-chemerkin-balccon-2013-140202131830-phpapp02/85/Pdf-yury-chemerkin-balccon_2013-9-320.jpg)
![[ KNOWN ISSUES. Examples ]
BYPASS MDM SOLUTIONS
iOS, ANDROID
EXPLOITS, DUMP /MEM TO GET EMAILS
BLACKHAT EU’13 http://goo.gl/HN829p
BLACKBERRY PLAYBOOK
EXPLOITS, MITM, DUMP ‘.ALL’ FILES
SECTO’11R, INFILTRATE’12, SOURCE
BOSTON’13 http://goo.gl/KaTtFG
GAIN ROOT ACCESS
ANDROID
APP SIGNATURE EXPLOITATION
APP MODIFICATION
BLACKHAT USA’13 http://goo.gl/p5FhWG
TIME-FRAME TO FIX
7+ MONTH or WAIT FOR A NEXT UPDATE
WAIT FOR A VENDOR’S INTEREST TO YOU
ANALYSIS OF APP’S DATA IN THE REST
BLACKBERRY, iOS
DATA LEAKAGE
REVEAL PASSWORDS, MASTERKEYS, ETC.
BLACKHAT EU’12 http://goo.gl/STpSll
ANDROID
DATA LEAKAGE
WEAKNESS OF CRYPTO ENGINGE
PHDAY III ‘13 http://goo.gl/x1PPGK](https://image.slidesharecdn.com/28pdf-29-20yury-chemerkin-balccon-2013-140202131830-phpapp02/85/Pdf-yury-chemerkin-balccon_2013-10-320.jpg)
![[ KNOWN ISSUES. Examples ]
PLAYBOOK ARTIFACTS (see the previous slide)
BROWSERS HISTORY
NETWORKING IDs, FLAGS, MACs
VIDEO CALLS DETAILS
ACCESS TO INTERNAL NETWORK
KERNEL
BLACKBERRY Z10
DUMP MICROKERNEL
EVEN DEVELOPERS’ CREDENTIALS
(FACEBOOK, MOBILE, EMAILS) BLACKHAT
DEFCON MOSCOW http://goo.gl/R74leX
GUI FAILS
BLACKBERRY OS
DATA LEAKAGE
REVEAL PASSWORDS, … ANYTHING
NO PERMISSIONS REQUESTED
BORROW PERMISSIONS OF ANOTHER APP
NullCon’13, CONFIDENCE’13
http://goo.gl/phMey2](https://image.slidesharecdn.com/28pdf-29-20yury-chemerkin-balccon-2013-140202131830-phpapp02/85/Pdf-yury-chemerkin-balccon_2013-11-320.jpg)
![[ APPLICATION EXAMINATION ]
ONLY THOSE I HAVE TO USE EVERY DAY
Account
country code, phone number
Device Hardware Key
login / tokens of Twitter & Facebook
Calls history
Name + internal ID
Duration + date and time
Address book
Quantity of contacts / viber-contacts
Full name / Email / phone numbers
Messages
FORENSICS EXAMINATION
Conversations
Quantity of messages & participants
per conversations
Additional participant info (full name,
phone)
Messages
Date & Time
content of message
ID](https://image.slidesharecdn.com/28pdf-29-20yury-chemerkin-balccon-2013-140202131830-phpapp02/85/Pdf-yury-chemerkin-balccon_2013-12-320.jpg)
![[ APPLICATION EXAMINATION ]
ONLY THOSE I HAVE TO USE EVERY DAY
Account
country code, phone number
login / tokens Facebook wasn’t revealed
‘Buy me for….$$$’
Avatars :: phone+@s.whatsapp.net.j (jfif)
Address book
No records of address book were revealed…
Check log-file and find these records (!)
Messages
Messages
Date & Time
FORENSICS EXAMINATION
content of message
ID :: phone@s.whatsapp.net](https://image.slidesharecdn.com/28pdf-29-20yury-chemerkin-balccon-2013-140202131830-phpapp02/85/Pdf-yury-chemerkin-balccon_2013-13-320.jpg)
![[ APPLICATION EXAMINATION ]
ONLY THOSE I HAVE TO USE EVERY DAY
Account
Phone number
Password, secret code weren’t revealed
Trace app, find the methods use it
Repack app and have a fun
No masking of data typed
Information
Amount
Full info in history section (incl. info about
who receive money)
FORENSICS EXAMINATION
Connected cards
Encryption?
No
Bank cards
Masked card number only
Qiwi Bank cards
Full & masked number
Cvv/cvc
All other card info ](https://image.slidesharecdn.com/28pdf-29-20yury-chemerkin-balccon-2013-140202131830-phpapp02/85/Pdf-yury-chemerkin-balccon_2013-14-320.jpg)
![[ APPLICATION EXAMINATION ]
ONLY THOSE I HAVE TO USE EVERY DAY
Account
ID , email, password
Information
Loyalty (bonus) of your membership
all you ever type
Date of birth
Passport details
Book/order history
Routes,
Date and time,
Bonus earning
Full info per each order
FORENSICS EXAMINATION
Connected cards
Encryption?
AES
256 bit
On password
anywayanydayanywayanyday
Store in plaintext
Sizeof(anywayanydayanywayanyday) =
192 bit](https://image.slidesharecdn.com/28pdf-29-20yury-chemerkin-balccon-2013-140202131830-phpapp02/85/Pdf-yury-chemerkin-balccon_2013-15-320.jpg)
![[ APPLICATION EXAMINATION ]
ONLY THOSE I HAVE TO USE EVERY DAY
Account
ID ,bonus card number, password not revealed
Other id & tokens
Information
Date of birth
Passport details
History (airlines, city, flight number only)
Flights tickets, logins credentials
Repack app and grab it
FORENSICS EXAMINATION](https://image.slidesharecdn.com/28pdf-29-20yury-chemerkin-balccon-2013-140202131830-phpapp02/85/Pdf-yury-chemerkin-balccon_2013-16-320.jpg)
![[ APPLICATION EXAMINATION ]
ONLY THOSE I HAVE TO USE EVERY DAY
Account
ID , password
Loyalty (bonus) card number
Information
Not revealed (tickets, history or else)
Repack app
FORENSICS EXAMINATION](https://image.slidesharecdn.com/28pdf-29-20yury-chemerkin-balccon-2013-140202131830-phpapp02/85/Pdf-yury-chemerkin-balccon_2013-17-320.jpg)
![[ APPLICATION EXAMINATION ]
ONLY THOSE I HAVE TO USE EVERY DAY
FORENSICS EXAMINATION
Account
ID , email, password
Other id & tokens
Information
Loyalty (bonus) of your membership
all you ever type
Date of birth
Passport details
All PASSPORT INFO (not only travel data)
Your work data (address, job, etc.) you have never typed!
Flights tickets
Repack app and grab it](https://image.slidesharecdn.com/28pdf-29-20yury-chemerkin-balccon-2013-140202131830-phpapp02/85/Pdf-yury-chemerkin-balccon_2013-18-320.jpg)
![[ DEVICE MANAGEMENT ]
APPLICATION LEVEL ATTACK’SVECTOR
GOALS - MOBILE RESOURCES / AIM OF ATTACK
DEVICE RESOURCES
OUTSIDE-OF-DEVICE RESOURCES
ATTACKS – SET OF ACTIOSN UNDER THE THREAT
APIs - RESOURCES WIDELY AVAILABLE TO CODERS
SECURITY FEATURES
KERNEL PROTECTION , NON-APP FEATURES
PERMISSIONS - EXPLICITLY CONFIGURED
3RD PARTY
AV, FIREWALL, VPN, MDM
COMPLIANCE - RULES TO DESIGN A MOBILE SECURITY
IN ALIGNMENT WITH COMPLIANCE TO…
Goals
AV, MDM,
DLP, VPN
Non-app
features
MDM features
Kernel
protection
Permissions
APIs
Attacks
APIs](https://image.slidesharecdn.com/28pdf-29-20yury-chemerkin-balccon-2013-140202131830-phpapp02/85/Pdf-yury-chemerkin-balccon_2013-19-320.jpg)
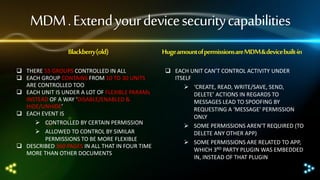
![[ DEVICE MANAGEMENT ]
Concurrencyover native & additional security features
𝚫 = 𝚨 ∪ 𝚩 ∪ 𝚪 ∪ 𝚼 , 𝚨 ⊂ 𝚩, 𝚼 ⊆ 𝚩, 𝚼 ⊂ 𝐀
𝛥 – set of OS permissions, 𝛢 – set of device permissions, 𝛣 – set
of MDM permissions, 𝛤 – set of missed permissions (lack of
controls), 𝜰 – set of rules are explicitly should be applied to gain
a compliance
𝚮 = 𝚬+ 𝚭, 𝚬 ⊃ 𝚨∪ 𝚩
𝛨 – set of APIs , 𝛦 – set of APIs that interact with sensitive data,
𝛧 – set of APIs that do not interact with sensitive data
To get a mobile security designed with full granularity the set 𝛤
should be empty set to get 𝚬 ⊇ 𝚨 ∪ 𝚩 instead of 𝚬 ⊃ 𝚨 ∪ 𝚩, so
the matter how is it closer to empty. On another hand it should
find out whether assumptions 𝚼 ⊆ 𝚩, 𝚼 ⊂ 𝐀 are true and if it is
possible to get ⊆ 𝐀.
The situationis very serious
Set of permissions < Set of activities efficiency is
typical case < 100%,
ability to control each API = 100%
More than 1 permission per APIs >100%
lack of knowledge about possible attacks
improper granularity
AV, MDM, DLP,
VPN
Non-app features
MDM features
Kernel protection
Permissions](https://image.slidesharecdn.com/28pdf-29-20yury-chemerkin-balccon-2013-140202131830-phpapp02/85/Pdf-yury-chemerkin-balccon_2013-20-320.jpg)
![[ BLACKBERRY. PERMISSIONS ]
BB 10 Cascades SDK
Background processing
BlackBerry Messenger
Calendar, Contacts
Camera
Device identifying information
Email and PIN messages
GPS location
Internet
Location
Microphone
Narrow swipe up
Notebooks
Notifications
Player
Phone
Push
Shared files
Text messages
Volume
BB 10 AIR SDK
+
+
+
+
+
+
+
+
+
+
+
+
+
+
+
-
PB (NDK/AIR)
+
via invoke calls
+
+
via invoke calls
+
+
+
+
+
+
+
+](https://image.slidesharecdn.com/28pdf-29-20yury-chemerkin-balccon-2013-140202131830-phpapp02/85/Pdf-yury-chemerkin-balccon_2013-21-320.jpg)
![[ BLACKBERRY. Significant APIs ]
Feature
BlackBerry Messenger
Calendar
Camera
Contacts
Device identifying info
Email & PIN messages
Internet
Microphone
Notebooks
Notifications
Phone
Push
Shared files
Text messages
Account
MediaPlayer
NFC
Radio & SIM
Clipboard
Q. APIs
77
443
47
316
15
347
161
21
123
32
27
25
78
10
66
66
24
68
6
Q. sign. APIs
70
126
41
150
14
211
145
15
86
24
22
22
70
6
21
63
11
51
4
% (sign .APIs)
90,91
28,44
87,23
47,47
93,33
60,81
90,06
71,43
69,92
75,00
81,48
88,00
89,74
60,00
31,82
95,45
45,83
75,00
66,67
Controlled ?
+
+
+
+
+
+
+
+
+
+
+
+
+
+
-](https://image.slidesharecdn.com/28pdf-29-20yury-chemerkin-balccon-2013-140202131830-phpapp02/85/Pdf-yury-chemerkin-balccon_2013-22-320.jpg)
![[ BLACKBERRY. Common activities ]
34
35
30
25
21
18
20
17
14
15
10
6
5
0
7
5
4
1
3
8
6
3
2
1
1
1
Q. of m.+a. activity
4
3
2
2
2
4
2
1
1
4
1
Q. of m.+a. permission
4
1
4
3
1
2
2 5
1](https://image.slidesharecdn.com/28pdf-29-20yury-chemerkin-balccon-2013-140202131830-phpapp02/85/Pdf-yury-chemerkin-balccon_2013-23-320.jpg)
![[ BLACKBERRY. Derived activities ]
116
120
100
89
80
59
60
47
40
20
0
24
1
4
3
3
23
16
7
6
1
3
46
11
3
1
2
Q. of derived activities
2
2
9
3
1
2
Q. of derived perm
27
25
24
19
1
1
8
1
2
2
5
1](https://image.slidesharecdn.com/28pdf-29-20yury-chemerkin-balccon-2013-140202131830-phpapp02/85/Pdf-yury-chemerkin-balccon_2013-24-320.jpg)
![[ BLACKBERRY. Efficiency (%) ]
250,00
250,00
200,00
150,00
3,45
16,67
8,70
5,08
100,00
50,00
12,50
60,00
16,67 19,05
3,37 6,25
66,67
14,29
5,88 14,29 5,56 16,67
66,67
66,67
4,26
9,09
66,67
11,76
25,00
5,26
50,00
4,17
50,00
25,00 25,00
0,00
% m+a activity vs perm
8,00
88,89
2,17
% m+a derived activity vs perm
250,00
33,33
3,70
50,00
7,14](https://image.slidesharecdn.com/28pdf-29-20yury-chemerkin-balccon-2013-140202131830-phpapp02/85/Pdf-yury-chemerkin-balccon_2013-25-320.jpg)
![[ iOS. Info.plist(app capabilities) ]
Key
auto-focus-camera
Description
handle autofocus capabilities in the device’s still camera in case of a macro photography or image processing.
bluetooth-le
camera-flash
front-facing-camera
gamekit
gps
handle the presence of Bluetooth low-energy hardware on the device.
handle a camera flash for taking pictures or shooting video.
handle a forward-facing camera such as capturing video from the device’s camera.
handle a Game Center.
handle a GPS (or AGPS) hardware to track a locations in case of need the higher accuracy more than Cellular/Wi-Fi.
location-services
retrieve the device’s current location using the Core Location framework though Cellular/Wi-Fi
microphone
peer-peer
sms
handle the built-in microphone and its accessories
handle peer-to-peer connectivity over a Bluetooth network.
handle the presence of the Messages application such as opening URLs with the sms scheme.
still-camera
handle the presence of a camera on the device such as capturing images from the device’s still camera.
telephony
handle the presence of the Phone application such as opening URLs with the telephony scheme.
video-camera
handle the presence of a camera with video capabilities on device such as capturing video from the device’s camera.
wifi
access to the networking features of the device.](https://image.slidesharecdn.com/28pdf-29-20yury-chemerkin-balccon-2013-140202131830-phpapp02/85/Pdf-yury-chemerkin-balccon_2013-26-320.jpg)
![[ iOS. Settings ]
Component
Unit
Safari
Camera, FaceTime
iTunes Store, iBookstore
Siri
Manage applications*
Manage applications*
Explicit Language (Siri)
Privacy*, Accounts*
Content Type Restrictions*
Restrictions :: Native application
Restrictions :: 3rd application
Unit subcomponents
Privacy :: Location
Privacy :: Private Info
Accounts
Content Type Restrictions
Game Center
Manage applications
Per each 3rd party app
For system services
Contacts, Calendar, Reminders, Photos
Bluetooth Sharing
Twitter, Facebook
Disables changes to Mail, Contacts, Calendars, iCloud, and Twitter accounts
Find My Friends
Volume limit
Ratings per country and region
Music and podcasts
Movies, Books, Apps, TV shows
In-app purchases
Require Passwords (in-app purchases)
Multiplayer Games
Adding Friends (Game Center)
Installing Apps
Removing Apps](https://image.slidesharecdn.com/28pdf-29-20yury-chemerkin-balccon-2013-140202131830-phpapp02/85/Pdf-yury-chemerkin-balccon_2013-27-320.jpg)
![[ iOS. Common activities ]
20
18
16
14
12
10
8
6
4
2
0
17
12
3
2
13
8
5
0
1
1
10
0
0
1
Q. of m.+a. activity
3
0
10
0
6
0
0
3
0
1
2
0
1
0
Q. of m.+a. permission
2
1
1
0
1
2
3
0
10
1
3
0
1
Q. of m.+a. perm plus parental perm
4](https://image.slidesharecdn.com/28pdf-29-20yury-chemerkin-balccon-2013-140202131830-phpapp02/85/Pdf-yury-chemerkin-balccon_2013-28-320.jpg)
![[ iOS. Derived activities ]
4
3
82
80
70
60
50
40
30
20
10
0
1
0
0
1
1
2
1
0
13
9
20 3
0
0
13
Q. of derived activities
0
9
0 18
12
0
0
10
Q. of derived perm
0
2
0
1
1
1
1
10
0
25
0
10
6
1
Q. of derived perm + plus parental perm
2
1](https://image.slidesharecdn.com/28pdf-29-20yury-chemerkin-balccon-2013-140202131830-phpapp02/85/Pdf-yury-chemerkin-balccon_2013-29-320.jpg)
![[ iOS. Efficiency (%) ]
100%
90%
80%
70%
60%
50%
40%
30%
20%
10%
0%
11,11
15,00 7,69
20,00
% m+a activity vs perm
0,00
0,00
0,00
0,00
5,56
0,00
0,00
0,00
% m+a derived activity vs perm
7,69
8,00
40,00
50,00 16,67
0,00
0,00
0,00
0,00 16,67
0,00
0,00
4,88
10,00
16,67
7,69
25,00
10,00 33,33
50,00
5,56
0,00
0,00
0,00
11,76
0,00
0,00
50,00 10,00
0,00
0,00
50,00
16,67
Q. of m.+a. perm plus parental perm
0,00
0,00
0,00
0,00
33,33
3,66
4,00
0,00
0,00
30,00
5,88
Q. of derived perm + plus parental perm](https://image.slidesharecdn.com/28pdf-29-20yury-chemerkin-balccon-2013-140202131830-phpapp02/85/Pdf-yury-chemerkin-balccon_2013-30-320.jpg)
![[ Windows. Permissions ]
Permission
Description
General use capabilities
musicLibrary
provides access to the user's Music library, allowing the app to enumerate and access all files w/o user interaction.
picturesLibrary
videosLibrary
removableStorage
provides access to the user's Pictures library, allowing to enumerate and access all files w/o user interaction.
provides access to the user's Videos library, allowing the app to enumerate and access all w/o user interaction.
provides access to files on removable storage, such as USB keys and external hard drives, filtered to the file type
microphone
provides access to the microphone’s audio feed, which allows to record audio from connected microphones..
webcam
provides access to the webcam’s video feed, which allows to capture snapshots, movies from a connected webcam.
location
provides access to location functionality like a GPS sensor or derived from available network info.
enables multiple devices in close proximity to communicate with one another via possible connection, incl.
Bluetooth, WiFi, and the internet.
proximity
internetClient,
internetClientServer
privateNetworkClientServer
enterpriseAuthentication
sharedUserCertificates
documentsLibrary
provides outbound (inbound is for server only) access to the Internet, public networks via the firewall.
provides inbound and outbound access to home and work networks through the firewall for games or for
applications that share data across local devices.
Special use capabilities
enable a user to log into remote resources using their credentials, and act as if a user provided their user name and
password.
enables an access to software and hardware certificates like smart card.
provides access to the user's Documents library, filtered to the file type associations](https://image.slidesharecdn.com/28pdf-29-20yury-chemerkin-balccon-2013-140202131830-phpapp02/85/Pdf-yury-chemerkin-balccon_2013-31-320.jpg)
![[ Windows. Significant APIs ]
Feature
Q. APIs
Notifications
Music library
Pictures library
Videos library
Removable storage
Microphone
Webcam
Location
Proximity
Internet and public networks
Home and work networks
68
1300
1157
1300
1045
274
409
37
54
488
488
Enterprise authentication
Shared User Certificates
Documents library
8
20
1045
Clipboard
Phone
SMS
Contacts
Device Info
132
18
122
97
221
Q. sign. APIs
General use capabilities
4
138
133
138
109
33
91
5
19
134
134
Special use capabilities
4
5
126
Non-controlled capabilities
20
6
25
31
30
% (sign. APIs)
Controlled?
5,88
10,62
11,50
10,62
10,43
12,04
22,25
13,51
35,19
27,46
27,46
+
+
+
+
+
+
+
+
+
+
+
50,00
25,00
12,06
+
+
+
15,15
33,33
20,49
31,96
13,57
-](https://image.slidesharecdn.com/28pdf-29-20yury-chemerkin-balccon-2013-140202131830-phpapp02/85/Pdf-yury-chemerkin-balccon_2013-32-320.jpg)
![[ Windows. Common Activities ]
14
14
12
10
8
8
3
4
2
0
6
5 6
6
1
1
1
1
3
1
1
1
1
1
3
8
4 5
3
1
Q. of m.+a. activity
1
2
4
3
1
Q. of m.+a. permission
2
2
3
2
1
2
0
0
0
0
0](https://image.slidesharecdn.com/28pdf-29-20yury-chemerkin-balccon-2013-140202131830-phpapp02/85/Pdf-yury-chemerkin-balccon_2013-33-320.jpg)
![[ Windows. Derived Activities ]
25
21
20
15
0
1
2
12
8
7
5
1
15
11
10
8
10
5
16
14
2
2
1
3
12
11
8
6
6 3
8
8
5
1
1
Q. of derived activities
2
1
Q. of derived perm
2
2
0
0
0
0
0](https://image.slidesharecdn.com/28pdf-29-20yury-chemerkin-balccon-2013-140202131830-phpapp02/85/Pdf-yury-chemerkin-balccon_2013-34-320.jpg)
![[ Windows. Efficiency (%) ]
120,00
120,00
100,00
100,00 100,00
100,00 100,00
100,00
100,00
80,00
60,00
40,00
20,00
125,00
100,00
27,27 42,86
25,00
25,00 20,00
33,33
20,00
33,33
33,33 14,29
31,25
16,67
14,29 9,52
50,00
33,33
16,67 16,6716,67
0,00
% m+a activity vs perm
% m+a derived activity vs perm
0,00 0,00 0,00 0,00 0,00
0,00 0,00 0,00 0,00 0,00](https://image.slidesharecdn.com/28pdf-29-20yury-chemerkin-balccon-2013-140202131830-phpapp02/85/Pdf-yury-chemerkin-balccon_2013-35-320.jpg)
![[ A droid. Permissions ]
List contains~150 permissions
I have ever seen that on old BlackBerry devices
ACCESS_CHECKIN_PROPERTIES,ACCESS_COARSE_LOCATION,
OSTIC,DISABLE_KEYGUARD,DUMP,EXPAND_STATUS_BAR,FAC
RD_AUDIO,REORDER_TASKS,RESTART_PACKAGES,SEND_SMS
ACCESS_FINE_LOCATION,ACCESS_LOCATION_EXTRA_COMM
TORY_TEST,FLASHLIGHT,FORCE_BACK,GET_ACCOUNTS,GET_
,SET_ACTIVITY_WATCHER,SET_ALARM,SET_ALWAYS_FINISH,
ANDS,ACCESS_MOCK_LOCATION,ACCESS_NETWORK_STATE,
PACKAGE_SIZE,GET_TASKS,GLOBAL_SEARCH,HARDWARE_TE
SET_ANIMATION_SCALE,SET_DEBUG_APP,SET_ORIENTATION
ACCESS_SURFACE_FLINGER,ACCESS_WIFI_STATE,ACCOUNT_
ST,INJECT_EVENTS,INSTALL_LOCATION_PROVIDER,INSTALL_P
,SET_POINTER_SPEED,SET_PREFERRED_APPLICATIONS,SET_P
MANAGER,ADD_VOICEMAIL,AUTHENTICATE_ACCOUNTS,BAT
ACKAGES,INTERNAL_SYSTEM_WINDOW,INTERNET,KILL_BACK
ROCESS_LIMIT,SET_TIME,SET_TIME_ZONE,SET_WALLPAPER,S
TERY_STATS,BIND_ACCESSIBILITY_SERVICE,BIND_APPWIDGET
GROUND_PROCESSES,MANAGE_ACCOUNTS,MANAGE_APP_T
ET_WALLPAPER_HINTS,SIGNAL_PERSISTENT_PROCESSES,STA
,BIND_DEVICE_ADMIN,BIND_INPUT_METHOD,BIND_REMOTE
OKENS,MASTER_CLEAR,MODIFY_AUDIO_SETTINGS,MODIFY_
TUS_BAR,SUBSCRIBED_FEEDS_READ,SUBSCRIBED_FEEDS_WR
VIEWS,BIND_TEXT_SERVICE,BIND_VPN_SERVICE,BIND_WALL
PHONE_STATE,MOUNT_FORMAT_FILESYSTEMS,MOUNT_UN
ITE,SYSTEM_ALERT_WINDOW,UPDATE_DEVICE_STATS,USE_C
PAPER,BLUETOOTH,BLUETOOTH_ADMIN,BRICK,BROADCAST_
MOUNT_FILESYSTEMS,NFC,PERSISTENT_ACTIVITY,PROCESS_
REDENTIALS,USE_SIP,VIBRATE,WAKE_LOCK,WRITE_APN_SET
PACKAGE_REMOVED,BROADCAST_SMS,BROADCAST_STICKY,
OUTGOING_CALLS,READ_CALENDAR,READ_CALL_LOG,READ_
TINGS,WRITE_CALENDAR,WRITE_CALL_LOG,WRITE_CONTAC
BROADCAST_WAP_PUSH,CALL_PHONE,CALL_PRIVILEGED,CA
CONTACTS,READ_EXTERNAL_STORAGE,READ_FRAME_BUFFE
TS,WRITE_EXTERNAL_STORAGE,WRITE_GSERVICES,WRITE_HI
MERA,CHANGE_COMPONENT_ENABLED_STATE,CHANGE_CO
R,READ_HISTORY_BOOKMARKS,READ_INPUT_STATE,READ_L
STORY_BOOKMARKS,WRITE_PROFILE,WRITE_SECURE_SETTIN
NFIGURATION,CHANGE_NETWORK_STATE,CHANGE_WIFI_M
OGS,READ_PHONE_STATE,READ_PROFILE,READ_SMS,READ_
GS,WRITE_SETTINGS,WRITE_SMS,WRITE_SOCIAL_STREAM,W
ULTICAST_STATE,CHANGE_WIFI_STATE,CLEAR_APP_CACHE,C
SOCIAL_STREAM,READ_SYNC_SETTINGS,READ_SYNC_STATS,
RITE_SYNC_SETTINGS,WRITE_USER_DICTIONARY,
LEAR_APP_USER_DATA,CONTROL_LOCATION_UPDATES,DELE
READ_USER_DICTIONARY,REBOOT,RECEIVE_BOOT_COMPLET
TE_CACHE_FILES,DELETE_PACKAGES,DEVICE_POWER,DIAGN
ED,RECEIVE_MMS,RECEIVE_SMS,RECEIVE_WAP_PUSH,RECO](https://image.slidesharecdn.com/28pdf-29-20yury-chemerkin-balccon-2013-140202131830-phpapp02/85/Pdf-yury-chemerkin-balccon_2013-36-320.jpg)
![[ A droid. Permission Groups ]
But there only 30 permissions groups
ACCOUNTS
AFFECTS_BATTERY
APP_INFO
AUDIO_SETTINGS
BLUETOOTH_NETWORK
BOOKMARKS
CALENDAR
CAMERA
COST_MONEY
DEVELOPMENT_TOOLS
DEVICE_ALARMS
DISPLAY
HARDWARE_CONTROLS
I have ever seen that on old BlackBerry devices too
LOCATION
MESSAGES
MICROPHONE
NETWORK
PERSONAL_INFO
PHONE_CALLS
SCREENLOCK
SOCIAL_INFO
STATUS_BAR
STORAGE
SYNC_SETTINGS
SYSTEM_CLOCK
SYSTEM_TOOLS
USER_DICTIONARY
VOICEMAIL
WALLPAPER
WRITE_USER_DICTIONARY](https://image.slidesharecdn.com/28pdf-29-20yury-chemerkin-balccon-2013-140202131830-phpapp02/85/Pdf-yury-chemerkin-balccon_2013-37-320.jpg)
![[ A droid. Efficiency (%) ]
50,00
45,00
40,00
33,33
35,00
30,00
25,00
20,00
15,00
10,00
28,57
25,00
20,00
20,00
15,38 15,38
20,00
9,52
0,00
0,00
2,91
10,71
5,00
0,00
2,00
7,14
0,00
4,55
8,33
7,14
0,00
% m+a activity vs perm
% m+a derived activity vs perm
10,00
4,00
3,13
5,88
3,13
0,00](https://image.slidesharecdn.com/28pdf-29-20yury-chemerkin-balccon-2013-140202131830-phpapp02/85/Pdf-yury-chemerkin-balccon_2013-38-320.jpg)
![[ Average quantitative indicators ]
100%
102,74
90%
80%
119,31
60,63
8,86
29,26
1,89
42,04
2,32
70%
60%
60,38
435,95
9,06
0,64
7,43
0,69
1,47
1,63
2,01
2,19
Q. of m.+a.
permissions
Q. of derived
permissions
17,07
30,48
5,94
48,06
32,79
16,99
9,21
50%
40%
62,37
3,84
67,48
9,23
9,68
54
20,97
58,06
22,76
30%
20%
394,86
10%
32,48
38,4
27,6
38,4
27,6
0%
Q. APIs
Q. sign APIs
Q. of m.+a.
activities
Q. of derived
activities
Android
Windows
iOS
% m+a activities %m+a derived vs % m+a vs perm
vs perm
perm
enhanced by
MDM
BlackBerry
% derived vs
perm enhanced
by MDM](https://image.slidesharecdn.com/28pdf-29-20yury-chemerkin-balccon-2013-140202131830-phpapp02/85/Pdf-yury-chemerkin-balccon_2013-39-320.jpg)