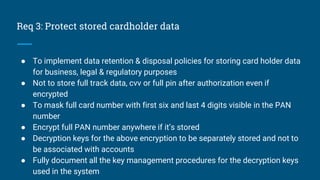
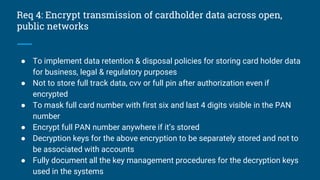
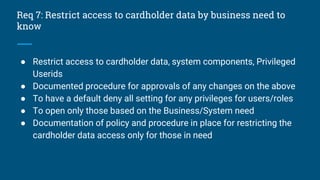
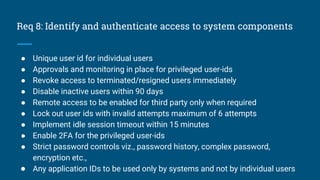
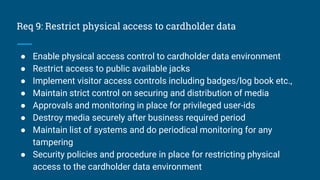
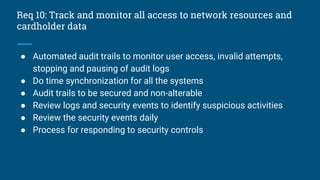
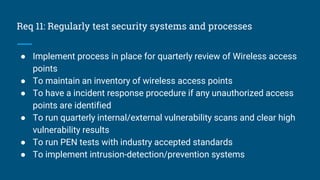
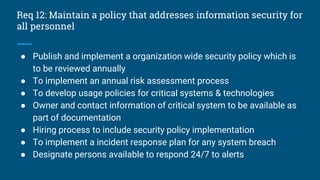
The document outlines the requirements and processes for implementing PCI DSS v3.2 for entities dealing with cardholder data, emphasizing the need for security measures across various systems and applications. It details 12 high-level requirements ranging from firewall maintenance to encryption, access control, and regular audits to ensure compliance and protect sensitive data. Additionally, the document stresses the importance of documentation and establishing policies to safeguard cardholder information and mitigate risks.