Paul Howland - DSTL - SPF EM risk framework presentation v2
•
1 like•624 views
Presentations from the SPF Spectrum Resilience workshop on 03 May 2018 More information about the UK Spectrum Policy Forum is available here. http://www.techuk.org/about/uk-spectrum-policy-forum
Report
Share
Report
Share
Recommended
Exeter university ig manager presentation [1]![Exeter university ig manager presentation [1]](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![Exeter university ig manager presentation [1]](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
What are the information security challenges affecting universities and how would I address them.
The Security Value Chain

By aligning your security and compliance activities in the context of Michael Porter's value chain, you can seek out new metrics to determine your success in mitigating and managing risks.
RPG Analytics Overview 2015

A brief introduction to ReefPoint Group, a data-hungry management consulting firm providing industry-leading analytic power to healthcare, government and business. (A Service Disabled Veteran Owned Small Business - SDVOSB)
Recommended
Exeter university ig manager presentation [1]![Exeter university ig manager presentation [1]](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![Exeter university ig manager presentation [1]](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
What are the information security challenges affecting universities and how would I address them.
The Security Value Chain

By aligning your security and compliance activities in the context of Michael Porter's value chain, you can seek out new metrics to determine your success in mitigating and managing risks.
RPG Analytics Overview 2015

A brief introduction to ReefPoint Group, a data-hungry management consulting firm providing industry-leading analytic power to healthcare, government and business. (A Service Disabled Veteran Owned Small Business - SDVOSB)
Internal financial control - how ready are you - Webinar

Internal financial control - how ready are you
Operational Excellence in Oil and Gas Loss Prevention

Mike Marshall, PE (mtmarshall.llc@gmail.com) is an Oil & Gas industry consultant who has recently developed an EAM loss prevention and asset optimization software product derived from various spreadsheet-based tools (consisting of business methods, practices, KPIs, scorecards, reports, data maps/views, etc.) which were central to the actual asset performance optimization/management and process safety improvement metrics and methodologies he implemented while working for both Marathon (23 years) and Chevron (10 years).
NEBOSH HSE PSM Element 1 v1.pdf

Process Safety Management
NEBOSH
1st pillar in process safet managementb
IT Business Continuity Planning 2004

Strategy, Governance, IT management, Disaster Recovery and Incident Response
Key concepts of Technology Management

Key concepts of Technology ManagementAce Institute of Management (Nepal), Institute of Management Studies (Nepal)
It includes concepts of Technology Management along with key concepts associated with Technology Management like technology forecasting, technology strategy, technology acquisition, technology audit, technology diffusion, technovation etc.How To Build An Incident Response Function

Is your organization ready to respond to an incident? More specifically, do you have the people, process, and technology in place that is required to cope with today's threats?
This webinar will provide practical steps on how to assess your organization's risks, threats, and current capabilities through a methodical and proven approach. From there, it will detail the people, process, and technology considerations when standing up or revitalizing an incident response (IR) program.
Specifically it will cover the four pillars of a modern IR function:
- Identify what must be protected
- Scope potential breach impact to the organization
- Define IR management capabilities
- Determine likely threats and their potential impact
Our featured speakers for this webinar will be:
- Ted Julian, Chief Marketing Officer, Co3 Systems
- Richard White, Solutions Principal, HP
5 Steps to Improve Your Incident Response Plan

Do you have an incident response plan to cover disasters, cyber-attacks, and other threats to your organization? How confident are you that it will work in a real-world situation? While simply having a plan will help you check the box on the audit, it doesn't guarantee effectiveness in a real situation. Assessing your incident response plans through fire drills, desk top exercises, functional scenarios, and full scale exercises will help your organization truly validate the effectiveness of the plan.
IR assessments are meant to:
- Evaluate plans, policies, and procedures
- Find weaknesses in the plan and gaps in resources
- Improve coordination and communication internally and externally
- Define and validate roles and responsibilities
- Train personnel in their roles and responsibilities
This webinar will provide practical steps for assessing your organization's plans and demonstrate ways to improve them through a methodical and proven approach. After all, whether they're big or small, internal or external, in most any organization incidents occur. Complete plans that have been tested, backed by trained resources and thorough communication, are the proven recipe to minimize the impact of incidents when they occur.
Our featured speakers for this webinar will be:
- Ted Julian, Chief Marketing Officer, Co3 Systems
- Richard White, Security Intelligence and Operations Principal, HP Enterprise Security Products
3 focus areas for any organisation's IT & Security department 

This presentation is focus on 3 areas - Improving the overall security posture of the company, Effective management of outsource service providers and work prioritization. Hope some of these ideas will help someone...
Cyber Recovery - Legal Toolkit

Presented by Dr Sam De Silva, partner at Nabarro to over 100 CEOs and Executives in London.
Explains what leaders should do immediately after becoming aware of a cyber attack, from a legal perspective.
The Importance of Security within the Computer Environment

Operating a Computer Environment in a Secured and Standard Approach
Business Continuity, Disaster Recovery Planning & Leadership, 16 - 19 Februar...

Disasters could cripple your organization, suspending mission-critical processes and disrupting service to your customers. These disasters could be man-made or natural in nature.
The Business Continuity Plan addresses an organization’s ability to continue functioning when normal operations are disrupted. A Disaster Recovery Plan is used to define the resources, action, tasks, and data required to manage the business recovery process in the event of a disaster.
In this workshop you learn to identify vulnerabilities and implement appropriate countermeasures to prevent and mitigate threats to your mission-critical processes. You will learn techniques for creating a business continuity plan (BCP) and the methodology for building an infrastructure that supports its effective implementation.
Benefits of Attending:
Using a carefully selected case study, course participants will:
- Create, document and test continuity arrangements for an organization
- Perform a risk assessment and Business Impact Assessment (BIA) to identify vulnerabilities
- Select and deploy an alternate site for continuity of mission-critical activities
- Identify appropriate strategies to recover the infrastructure and processes
- Organize and manage recovery teams
- Test and maintain an effective recovery plan in a rapidly changing technology environment
Exclusive:
- Bring your BCP/DRP for private consultation review
- BCP/DRP Step-by-step Guide
- BCP/DRP templates and worksheets to aid you in applying and putting into practice what you have learned from this workshop
- FREE CD containing course material, case studies, and other related items of the training workshop
Who should attend:
- Vice Presidents, Directors, General Managers
- Chief Information Officers
- Chief Security Officers
- Chief Information Security Officers
- Chief Technology Officers
- Heads of Departments in Information Security Management
Contact Kris at kris@360bsi.com to register.
After the Contracts Are Signed: Busing the Most Common Myths in HR Technology

After the Contracts Are Signed: Busing the Most Common Myths in HR Technology - Presentation slides presented by Steve Boese and Trish McFarlane at the SHRM Annual Conference, June 30, 2015.
Setting up an Effective Security and Compliance Office

First presented at the UC David Security Symposium
June 18, 2013
Information security, governance, compliance, and organizational design.
Abhaya Sumanasena - Real Wireless - Spectrum Options 

Presentations from the SPF Cluster 2 & 3: Release Mechanisms & Flexible Spectrum Access workshop on 21 May 2018
More information about the UK Spectrum Policy Forum is available here.
http://www.techuk.org/about/uk-spectrum-policy-forum
Anil Shukla - QinetiQ - spectrum policy forum-framework_qinetiq_030518_intro_...

Presentations from the SPF Spectrum Resilience workshop on 03 May 2018
More information about the UK Spectrum Policy Forum is available here.
http://www.techuk.org/about/uk-spectrum-policy-forum
More Related Content
Similar to Paul Howland - DSTL - SPF EM risk framework presentation v2
Internal financial control - how ready are you - Webinar

Internal financial control - how ready are you
Operational Excellence in Oil and Gas Loss Prevention

Mike Marshall, PE (mtmarshall.llc@gmail.com) is an Oil & Gas industry consultant who has recently developed an EAM loss prevention and asset optimization software product derived from various spreadsheet-based tools (consisting of business methods, practices, KPIs, scorecards, reports, data maps/views, etc.) which were central to the actual asset performance optimization/management and process safety improvement metrics and methodologies he implemented while working for both Marathon (23 years) and Chevron (10 years).
NEBOSH HSE PSM Element 1 v1.pdf

Process Safety Management
NEBOSH
1st pillar in process safet managementb
IT Business Continuity Planning 2004

Strategy, Governance, IT management, Disaster Recovery and Incident Response
Key concepts of Technology Management

Key concepts of Technology ManagementAce Institute of Management (Nepal), Institute of Management Studies (Nepal)
It includes concepts of Technology Management along with key concepts associated with Technology Management like technology forecasting, technology strategy, technology acquisition, technology audit, technology diffusion, technovation etc.How To Build An Incident Response Function

Is your organization ready to respond to an incident? More specifically, do you have the people, process, and technology in place that is required to cope with today's threats?
This webinar will provide practical steps on how to assess your organization's risks, threats, and current capabilities through a methodical and proven approach. From there, it will detail the people, process, and technology considerations when standing up or revitalizing an incident response (IR) program.
Specifically it will cover the four pillars of a modern IR function:
- Identify what must be protected
- Scope potential breach impact to the organization
- Define IR management capabilities
- Determine likely threats and their potential impact
Our featured speakers for this webinar will be:
- Ted Julian, Chief Marketing Officer, Co3 Systems
- Richard White, Solutions Principal, HP
5 Steps to Improve Your Incident Response Plan

Do you have an incident response plan to cover disasters, cyber-attacks, and other threats to your organization? How confident are you that it will work in a real-world situation? While simply having a plan will help you check the box on the audit, it doesn't guarantee effectiveness in a real situation. Assessing your incident response plans through fire drills, desk top exercises, functional scenarios, and full scale exercises will help your organization truly validate the effectiveness of the plan.
IR assessments are meant to:
- Evaluate plans, policies, and procedures
- Find weaknesses in the plan and gaps in resources
- Improve coordination and communication internally and externally
- Define and validate roles and responsibilities
- Train personnel in their roles and responsibilities
This webinar will provide practical steps for assessing your organization's plans and demonstrate ways to improve them through a methodical and proven approach. After all, whether they're big or small, internal or external, in most any organization incidents occur. Complete plans that have been tested, backed by trained resources and thorough communication, are the proven recipe to minimize the impact of incidents when they occur.
Our featured speakers for this webinar will be:
- Ted Julian, Chief Marketing Officer, Co3 Systems
- Richard White, Security Intelligence and Operations Principal, HP Enterprise Security Products
3 focus areas for any organisation's IT & Security department 

This presentation is focus on 3 areas - Improving the overall security posture of the company, Effective management of outsource service providers and work prioritization. Hope some of these ideas will help someone...
Cyber Recovery - Legal Toolkit

Presented by Dr Sam De Silva, partner at Nabarro to over 100 CEOs and Executives in London.
Explains what leaders should do immediately after becoming aware of a cyber attack, from a legal perspective.
The Importance of Security within the Computer Environment

Operating a Computer Environment in a Secured and Standard Approach
Business Continuity, Disaster Recovery Planning & Leadership, 16 - 19 Februar...

Disasters could cripple your organization, suspending mission-critical processes and disrupting service to your customers. These disasters could be man-made or natural in nature.
The Business Continuity Plan addresses an organization’s ability to continue functioning when normal operations are disrupted. A Disaster Recovery Plan is used to define the resources, action, tasks, and data required to manage the business recovery process in the event of a disaster.
In this workshop you learn to identify vulnerabilities and implement appropriate countermeasures to prevent and mitigate threats to your mission-critical processes. You will learn techniques for creating a business continuity plan (BCP) and the methodology for building an infrastructure that supports its effective implementation.
Benefits of Attending:
Using a carefully selected case study, course participants will:
- Create, document and test continuity arrangements for an organization
- Perform a risk assessment and Business Impact Assessment (BIA) to identify vulnerabilities
- Select and deploy an alternate site for continuity of mission-critical activities
- Identify appropriate strategies to recover the infrastructure and processes
- Organize and manage recovery teams
- Test and maintain an effective recovery plan in a rapidly changing technology environment
Exclusive:
- Bring your BCP/DRP for private consultation review
- BCP/DRP Step-by-step Guide
- BCP/DRP templates and worksheets to aid you in applying and putting into practice what you have learned from this workshop
- FREE CD containing course material, case studies, and other related items of the training workshop
Who should attend:
- Vice Presidents, Directors, General Managers
- Chief Information Officers
- Chief Security Officers
- Chief Information Security Officers
- Chief Technology Officers
- Heads of Departments in Information Security Management
Contact Kris at kris@360bsi.com to register.
After the Contracts Are Signed: Busing the Most Common Myths in HR Technology

After the Contracts Are Signed: Busing the Most Common Myths in HR Technology - Presentation slides presented by Steve Boese and Trish McFarlane at the SHRM Annual Conference, June 30, 2015.
Setting up an Effective Security and Compliance Office

First presented at the UC David Security Symposium
June 18, 2013
Information security, governance, compliance, and organizational design.
Similar to Paul Howland - DSTL - SPF EM risk framework presentation v2 (20)
Internal financial control - how ready are you - Webinar

Internal financial control - how ready are you - Webinar
Operational Excellence in Oil and Gas Loss Prevention

Operational Excellence in Oil and Gas Loss Prevention
Syllabus CIISA ( Certified Internasional Information System Auditor ).pdf

Syllabus CIISA ( Certified Internasional Information System Auditor ).pdf
3 focus areas for any organisation's IT & Security department 

3 focus areas for any organisation's IT & Security department
The Importance of Security within the Computer Environment

The Importance of Security within the Computer Environment
Business Continuity, Disaster Recovery Planning & Leadership, 16 - 19 Februar...

Business Continuity, Disaster Recovery Planning & Leadership, 16 - 19 Februar...
After the Contracts Are Signed: Busing the Most Common Myths in HR Technology

After the Contracts Are Signed: Busing the Most Common Myths in HR Technology
Setting up an Effective Security and Compliance Office

Setting up an Effective Security and Compliance Office
More from techUK
Abhaya Sumanasena - Real Wireless - Spectrum Options 

Presentations from the SPF Cluster 2 & 3: Release Mechanisms & Flexible Spectrum Access workshop on 21 May 2018
More information about the UK Spectrum Policy Forum is available here.
http://www.techuk.org/about/uk-spectrum-policy-forum
Anil Shukla - QinetiQ - spectrum policy forum-framework_qinetiq_030518_intro_...

Presentations from the SPF Spectrum Resilience workshop on 03 May 2018
More information about the UK Spectrum Policy Forum is available here.
http://www.techuk.org/about/uk-spectrum-policy-forum
Peter Curnow-Ford - SPF Cluster 2 - Spectrum Access Evolution

Presentations from the SPF Cluster 2 & 3: Release Mechanisms & Flexible Spectrum Access workshop on 21 May 2018
More information about the UK Spectrum Policy Forum is available here.
http://www.techuk.org/about/uk-spectrum-policy-forum
Stephen Temple - 5GIC - Dynamic Spectrum Expansion for 21 May SPF

Presentations from the SPF Cluster 2 & 3: Release Mechanisms & Flexible Spectrum Access workshop on 21 May 2018
More information about the UK Spectrum Policy Forum is available here.
http://www.techuk.org/about/uk-spectrum-policy-forum
Nigel King - UK WISPA - Flexible Spectrum Access

Presentations from the SPF Cluster 2 & 3: Release Mechanisms & Flexible Spectrum Access workshop on 21 May 2018
More information about the UK Spectrum Policy Forum is available here.
http://www.techuk.org/about/uk-spectrum-policy-forum
Tony lavender - Plum Consulting - Flexible Spectrum Access Methods

Presentations from the SPF Cluster 2 & 3: Release Mechanisms & Flexible Spectrum Access workshop on 21 May 2018
More information about the UK Spectrum Policy Forum is available here.
http://www.techuk.org/about/uk-spectrum-policy-forum
Cliff Mason - Ofcom - Spectrum Awards, Access and Sharing

Presentations from the SPF Cluster 2 & 3: Release Mechanisms & Flexible Spectrum Access workshop on 21 May 2018
More information about the UK Spectrum Policy Forum is available here.
http://www.techuk.org/about/uk-spectrum-policy-forum
Tony lavender - Plum Consulting - incorporating social value into spectrum al...

Incorporating Social Value into Spectrum Allocation Decisions
Presentation to UK Spectrum Policy Forum - Cluster 3: Economic and Social Value of Spectrum
29 March 2018
Tony Lavender
More information on the UK Spectrum Policy Forum can be found here: https://www.techuk.org/about/uk-spectrum-policy-forum
Philip bates - Analysys Mason - spectrum policy forum 29 march 2018

Overview of Analysys Mason 2012 study on the value of spectrum to the UK economy
Presentation to UK Spectrum Policy Forum - Cluster 3: Economic and Social Value of Spectrum
29 March 2018
Philip Bates
More information on the UK Spectrum Policy Forum can be found here: https://www.techuk.org/about/uk-spectrum-policy-forum
Enabling Dynamic Spectrum Management

Presentations from the UK SPF Cluster 2: Public Sector Spectrum Release (PSSR) - Utilities and 5G
Spectrum Requirements for Utilities

Presentations from the UK SPF Cluster 2: Public Sector Spectrum Release (PSSR) - Utilities and 5G
406MHz - 430MHz Sharing and Trials 

Presentations from the UK SPF Cluster 2: Public Sector Spectrum Release (PSSR) - Utilities and 5G
CMU Update Review 

Presentations from the UK SPF Cluster 2: Public Sector Spectrum Release (PSSR) - Utilities and 5G
Sharing Defence Managed Spectrum - MOD

Presentations from the UK SPF Cluster 2: Public Sector Spectrum Release (PSSR) - Utilities and 5G
Amberhawk - Law Enforcement Parts of the Data Protection Bill

Presentations on How Will Policing and Justice Be Affected By the Data Protection Bill? event held on 14 November
Thales - LED and DP from a Vendor's Perspective

Presentations on How Will Policing and Justice Be Affected By the Data Protection Bill? event held on 14 November
More from techUK (20)
Abhaya Sumanasena - Real Wireless - Spectrum Options 

Abhaya Sumanasena - Real Wireless - Spectrum Options
Anil Shukla - QinetiQ - spectrum policy forum-framework_qinetiq_030518_intro_...

Anil Shukla - QinetiQ - spectrum policy forum-framework_qinetiq_030518_intro_...
Peter Curnow-Ford - SPF Cluster 2 - Spectrum Access Evolution

Peter Curnow-Ford - SPF Cluster 2 - Spectrum Access Evolution
Stephen Temple - 5GIC - Dynamic Spectrum Expansion for 21 May SPF

Stephen Temple - 5GIC - Dynamic Spectrum Expansion for 21 May SPF
Tony lavender - Plum Consulting - Flexible Spectrum Access Methods

Tony lavender - Plum Consulting - Flexible Spectrum Access Methods
Cliff Mason - Ofcom - Spectrum Awards, Access and Sharing

Cliff Mason - Ofcom - Spectrum Awards, Access and Sharing
Tony lavender - Plum Consulting - incorporating social value into spectrum al...

Tony lavender - Plum Consulting - incorporating social value into spectrum al...
Philip bates - Analysys Mason - spectrum policy forum 29 march 2018

Philip bates - Analysys Mason - spectrum policy forum 29 march 2018
Amberhawk - Law Enforcement Parts of the Data Protection Bill

Amberhawk - Law Enforcement Parts of the Data Protection Bill
Recently uploaded
GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...

Effective Application Security in Software Delivery lifecycle using Deployment Firewall and DBOM
The modern software delivery process (or the CI/CD process) includes many tools, distributed teams, open-source code, and cloud platforms. Constant focus on speed to release software to market, along with the traditional slow and manual security checks has caused gaps in continuous security as an important piece in the software supply chain. Today organizations feel more susceptible to external and internal cyber threats due to the vast attack surface in their applications supply chain and the lack of end-to-end governance and risk management.
The software team must secure its software delivery process to avoid vulnerability and security breaches. This needs to be achieved with existing tool chains and without extensive rework of the delivery processes. This talk will present strategies and techniques for providing visibility into the true risk of the existing vulnerabilities, preventing the introduction of security issues in the software, resolving vulnerabilities in production environments quickly, and capturing the deployment bill of materials (DBOM).
Speakers:
Bob Boule
Robert Boule is a technology enthusiast with PASSION for technology and making things work along with a knack for helping others understand how things work. He comes with around 20 years of solution engineering experience in application security, software continuous delivery, and SaaS platforms. He is known for his dynamic presentations in CI/CD and application security integrated in software delivery lifecycle.
Gopinath Rebala
Gopinath Rebala is the CTO of OpsMx, where he has overall responsibility for the machine learning and data processing architectures for Secure Software Delivery. Gopi also has a strong connection with our customers, leading design and architecture for strategic implementations. Gopi is a frequent speaker and well-known leader in continuous delivery and integrating security into software delivery.
Connector Corner: Automate dynamic content and events by pushing a button

Here is something new! In our next Connector Corner webinar, we will demonstrate how you can use a single workflow to:
Create a campaign using Mailchimp with merge tags/fields
Send an interactive Slack channel message (using buttons)
Have the message received by managers and peers along with a test email for review
But there’s more:
In a second workflow supporting the same use case, you’ll see:
Your campaign sent to target colleagues for approval
If the “Approve” button is clicked, a Jira/Zendesk ticket is created for the marketing design team
But—if the “Reject” button is pushed, colleagues will be alerted via Slack message
Join us to learn more about this new, human-in-the-loop capability, brought to you by Integration Service connectors.
And...
Speakers:
Akshay Agnihotri, Product Manager
Charlie Greenberg, Host
State of ICS and IoT Cyber Threat Landscape Report 2024 preview

The IoT and OT threat landscape report has been prepared by the Threat Research Team at Sectrio using data from Sectrio, cyber threat intelligence farming facilities spread across over 85 cities around the world. In addition, Sectrio also runs AI-based advanced threat and payload engagement facilities that serve as sinks to attract and engage sophisticated threat actors, and newer malware including new variants and latent threats that are at an earlier stage of development.
The latest edition of the OT/ICS and IoT security Threat Landscape Report 2024 also covers:
State of global ICS asset and network exposure
Sectoral targets and attacks as well as the cost of ransom
Global APT activity, AI usage, actor and tactic profiles, and implications
Rise in volumes of AI-powered cyberattacks
Major cyber events in 2024
Malware and malicious payload trends
Cyberattack types and targets
Vulnerability exploit attempts on CVEs
Attacks on counties – USA
Expansion of bot farms – how, where, and why
In-depth analysis of the cyber threat landscape across North America, South America, Europe, APAC, and the Middle East
Why are attacks on smart factories rising?
Cyber risk predictions
Axis of attacks – Europe
Systemic attacks in the Middle East
Download the full report from here:
https://sectrio.com/resources/ot-threat-landscape-reports/sectrio-releases-ot-ics-and-iot-security-threat-landscape-report-2024/
De-mystifying Zero to One: Design Informed Techniques for Greenfield Innovati...

De-mystifying Zero to One: Design Informed Techniques for Greenfield Innovation With Your Product by VP of Product Design, Warner Music Group
Dev Dives: Train smarter, not harder – active learning and UiPath LLMs for do...

💥 Speed, accuracy, and scaling – discover the superpowers of GenAI in action with UiPath Document Understanding and Communications Mining™:
See how to accelerate model training and optimize model performance with active learning
Learn about the latest enhancements to out-of-the-box document processing – with little to no training required
Get an exclusive demo of the new family of UiPath LLMs – GenAI models specialized for processing different types of documents and messages
This is a hands-on session specifically designed for automation developers and AI enthusiasts seeking to enhance their knowledge in leveraging the latest intelligent document processing capabilities offered by UiPath.
Speakers:
👨🏫 Andras Palfi, Senior Product Manager, UiPath
👩🏫 Lenka Dulovicova, Product Program Manager, UiPath
Knowledge engineering: from people to machines and back

Keynote at the 21st European Semantic Web Conference
"Impact of front-end architecture on development cost", Viktor Turskyi

I have heard many times that architecture is not important for the front-end. Also, many times I have seen how developers implement features on the front-end just following the standard rules for a framework and think that this is enough to successfully launch the project, and then the project fails. How to prevent this and what approach to choose? I have launched dozens of complex projects and during the talk we will analyze which approaches have worked for me and which have not.
FIDO Alliance Osaka Seminar: The WebAuthn API and Discoverable Credentials.pdf

FIDO Alliance Osaka Seminar
Accelerate your Kubernetes clusters with Varnish Caching

A presentation about the usage and availability of Varnish on Kubernetes. This talk explores the capabilities of Varnish caching and shows how to use the Varnish Helm chart to deploy it to Kubernetes.
This presentation was delivered at K8SUG Singapore. See https://feryn.eu/presentations/accelerate-your-kubernetes-clusters-with-varnish-caching-k8sug-singapore-28-2024 for more details.
Designing Great Products: The Power of Design and Leadership by Chief Designe...

Designing Great Products: The Power of Design and Leadership by Chief Designer, Beats by Dr Dre
Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head...

Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head of Product, Amazon Games
Kubernetes & AI - Beauty and the Beast !?! @KCD Istanbul 2024

As AI technology is pushing into IT I was wondering myself, as an “infrastructure container kubernetes guy”, how get this fancy AI technology get managed from an infrastructure operational view? Is it possible to apply our lovely cloud native principals as well? What benefit’s both technologies could bring to each other?
Let me take this questions and provide you a short journey through existing deployment models and use cases for AI software. On practical examples, we discuss what cloud/on-premise strategy we may need for applying it to our own infrastructure to get it to work from an enterprise perspective. I want to give an overview about infrastructure requirements and technologies, what could be beneficial or limiting your AI use cases in an enterprise environment. An interactive Demo will give you some insides, what approaches I got already working for real.
Mission to Decommission: Importance of Decommissioning Products to Increase E...

Mission to Decommission: Importance of Decommissioning Products to Increase Enterprise-Wide Efficiency by VP Data Platform, American Express
ODC, Data Fabric and Architecture User Group

Let's dive deeper into the world of ODC! Ricardo Alves (OutSystems) will join us to tell all about the new Data Fabric. After that, Sezen de Bruijn (OutSystems) will get into the details on how to best design a sturdy architecture within ODC.
Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf

91mobiles recently conducted a Smart TV Buyer Insights Survey in which we asked over 3,000 respondents about the TV they own, aspects they look at on a new TV, and their TV buying preferences.
Key Trends Shaping the Future of Infrastructure.pdf

Keynote at DIGIT West Expo, Glasgow on 29 May 2024.
Cheryl Hung, ochery.com
Sr Director, Infrastructure Ecosystem, Arm.
The key trends across hardware, cloud and open-source; exploring how these areas are likely to mature and develop over the short and long-term, and then considering how organisations can position themselves to adapt and thrive.
PHP Frameworks: I want to break free (IPC Berlin 2024)

In this presentation, we examine the challenges and limitations of relying too heavily on PHP frameworks in web development. We discuss the history of PHP and its frameworks to understand how this dependence has evolved. The focus will be on providing concrete tips and strategies to reduce reliance on these frameworks, based on real-world examples and practical considerations. The goal is to equip developers with the skills and knowledge to create more flexible and future-proof web applications. We'll explore the importance of maintaining autonomy in a rapidly changing tech landscape and how to make informed decisions in PHP development.
This talk is aimed at encouraging a more independent approach to using PHP frameworks, moving towards a more flexible and future-proof approach to PHP development.
GraphRAG is All You need? LLM & Knowledge Graph

Guy Korland, CEO and Co-founder of FalkorDB, will review two articles on the integration of language models with knowledge graphs.
1. Unifying Large Language Models and Knowledge Graphs: A Roadmap.
https://arxiv.org/abs/2306.08302
2. Microsoft Research's GraphRAG paper and a review paper on various uses of knowledge graphs:
https://www.microsoft.com/en-us/research/blog/graphrag-unlocking-llm-discovery-on-narrative-private-data/
Recently uploaded (20)
GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...

GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...
Connector Corner: Automate dynamic content and events by pushing a button

Connector Corner: Automate dynamic content and events by pushing a button
State of ICS and IoT Cyber Threat Landscape Report 2024 preview

State of ICS and IoT Cyber Threat Landscape Report 2024 preview
De-mystifying Zero to One: Design Informed Techniques for Greenfield Innovati...

De-mystifying Zero to One: Design Informed Techniques for Greenfield Innovati...
Dev Dives: Train smarter, not harder – active learning and UiPath LLMs for do...

Dev Dives: Train smarter, not harder – active learning and UiPath LLMs for do...
Knowledge engineering: from people to machines and back

Knowledge engineering: from people to machines and back
"Impact of front-end architecture on development cost", Viktor Turskyi

"Impact of front-end architecture on development cost", Viktor Turskyi
FIDO Alliance Osaka Seminar: The WebAuthn API and Discoverable Credentials.pdf

FIDO Alliance Osaka Seminar: The WebAuthn API and Discoverable Credentials.pdf
Accelerate your Kubernetes clusters with Varnish Caching

Accelerate your Kubernetes clusters with Varnish Caching
Designing Great Products: The Power of Design and Leadership by Chief Designe...

Designing Great Products: The Power of Design and Leadership by Chief Designe...
FIDO Alliance Osaka Seminar: Passkeys at Amazon.pdf

FIDO Alliance Osaka Seminar: Passkeys at Amazon.pdf
Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head...

Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head...
Kubernetes & AI - Beauty and the Beast !?! @KCD Istanbul 2024

Kubernetes & AI - Beauty and the Beast !?! @KCD Istanbul 2024
Mission to Decommission: Importance of Decommissioning Products to Increase E...

Mission to Decommission: Importance of Decommissioning Products to Increase E...
Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf

Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf
Key Trends Shaping the Future of Infrastructure.pdf

Key Trends Shaping the Future of Infrastructure.pdf
PHP Frameworks: I want to break free (IPC Berlin 2024)

PHP Frameworks: I want to break free (IPC Berlin 2024)
FIDO Alliance Osaka Seminar: FIDO Security Aspects.pdf

FIDO Alliance Osaka Seminar: FIDO Security Aspects.pdf
Paul Howland - DSTL - SPF EM risk framework presentation v2
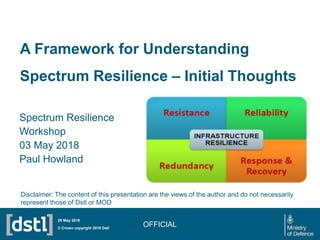
- 1. A Framework for Understanding Spectrum Resilience – Initial Thoughts Spectrum Resilience Workshop 03 May 2018 Paul Howland OFFICIAL© Crown copyright 2018 Dstl 29 May 2018 Disclaimer: The content of this presentation are the views of the author and do not necessarily represent those of Dstl or MOD
- 2. Key Framework Elements • Understand – How does an enterprise use EM Spectrum – What is the enterprise exposure to EM Threats and Risks • Assessment – What are the impacts to the enterprise of threats and risks – What are the probabilities of these threats and risks being realised • Measures – What has/can be done to mitigate threats and risks • Test and Verify – Evaluate and verify efficacy of measures • Regular Validation and Verification – To ensure changing and emerging threats are recognised and managed – Ensure currency of training, process, technology etc. OFFICIAL© Crown copyright 2018 Dstl 29 May 2018
- 3. Understand • Understand the Enterprise Exposure to Threat/Risk – What systems are reliant on EM Spectrum • Directly - Sensors , Data Communications, Product Delivery • Indirectly – Sales, Market Mechanisms, Synchronisation • Corporate/Enterprise Communications • Noting that manufacturing and service control need to be considered as well as office Information Systems – How is this impacted by medium and long term plans – This is potentially complex and often not intuative OFFICIAL© Crown copyright 2018 Dstl 29 May 2018
- 4. Assessment - Consideration Space • Risks (Examples Only) – Service Delivery – Product Management – Manufacturing Output – Product Quality – Growth – Reputation – Share Value • Risk Dimensions – Impact, Probability OFFICIAL • EM “Threat” Classes (Enterprise risks arise from Threats) – Deliberate – Accidental – Environmental – Regulatory – Technical • Threat Evolution (Now, Next Future) © Crown copyright 2018 Dstl 29 May 2018 Scaling and prioritisation of potential impacts is neccesary
- 5. Mitigation Measures • A good starting point for considering threat mitigation measures • Most have civil analogies • Not yet thought through so to seed thinking OFFICIAL • Defence Lines of Development – Describing capability needs • TEPIDOIL – Training – Equipment and technology – Personnel – Information – Doctrine and concepts – Organization, – Infrastructure – Logistics © Crown copyright 2018 Dstl 29 May 2018
- 6. Test and Verify • Once mitigations are in place: – Verify Status of mitigations e.g. • Key Staff identified and posts filled • Redundant Equipment and Infrastructure in place • Response and Recovery processes in place – Test • Analogous to fire alarm testing • To suit Risk and mitigation • Paper exercises – for enterprise wide contingency planning • Extension to penetration testing – Cyber and Physical • Equipment and Infrastructure Component Testing (Lab and Field) • Audit Training Records OFFICIAL© Crown copyright 2018 Dstl 29 May 2018
- 7. Revalidation and regular verification • Revalidate: – Threat – Risk exposure – Mitigations – Test and verification processes • Re-verification – Ensure testing and training regimes are kept up to date – That prioritisation is reviewed – Processes keep pace with technical and infrastructure evolution – That assessments are in line with current medium and long term plans OFFICIAL© Crown copyright 2018 Dstl 29 May 2018 Threat Changes, Risk exposure changes, Staff change, Technology advances
- 8. Finally • Example Metrics – Blue, Green, Amber or Red for each Risk – (Vulnerability?) – Blue – System does not degrade “significantly” in the presence of Threat, – Green - some degradation but minimum impact on critical infrastructure (CI) or customer services – Amber – Significant impact on CI or Customer service (Short outage or significant degradation in service quality attributes, – Red – Prolonged, significant impact or service outage) © Crown copyright 2018 Dstl 29 May 2018
- 9. © Crown copyright 2018 Dstl 29 May 2018
Editor's Notes
- This slide may be shown at the end of the presentation.
