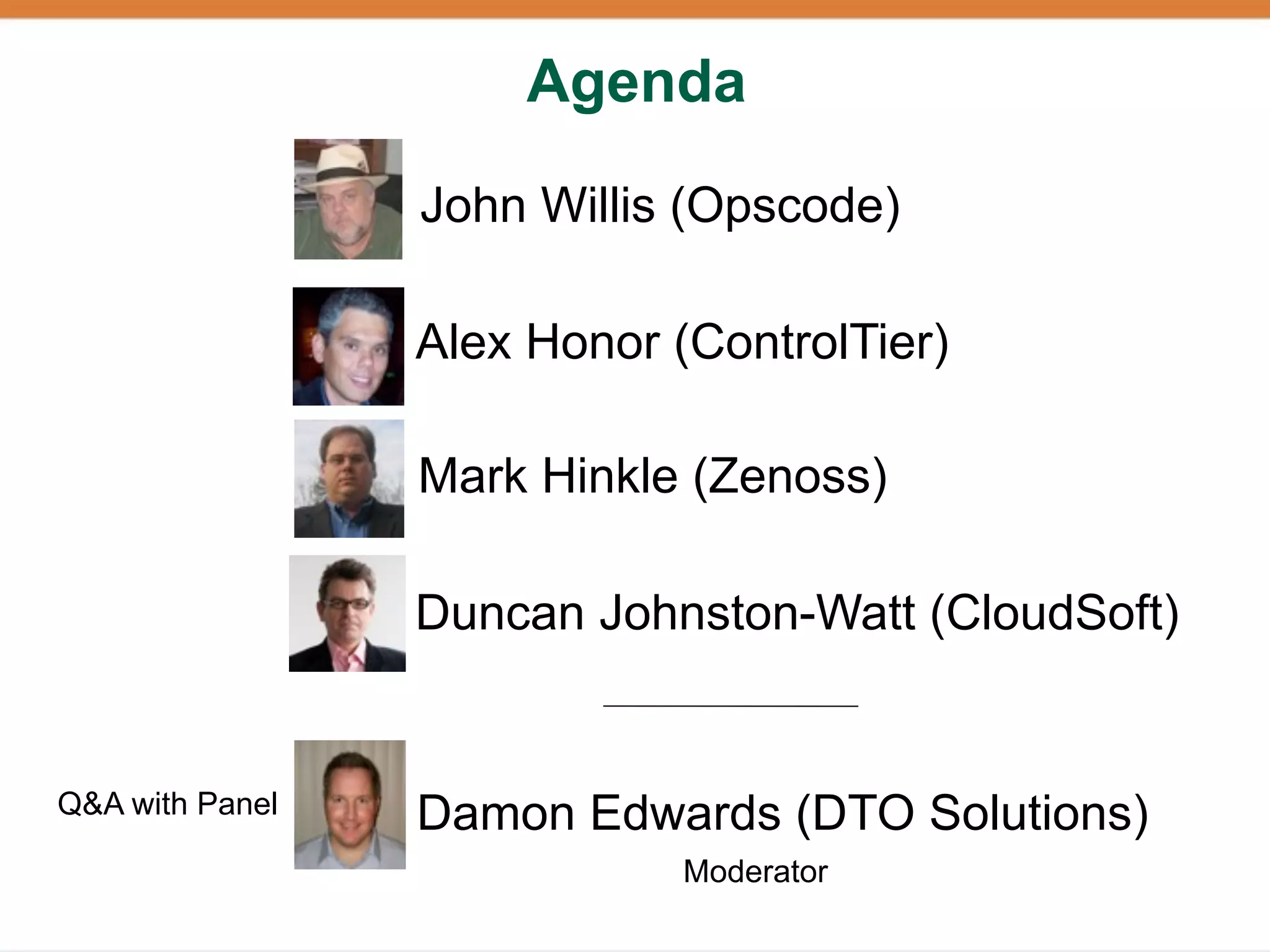
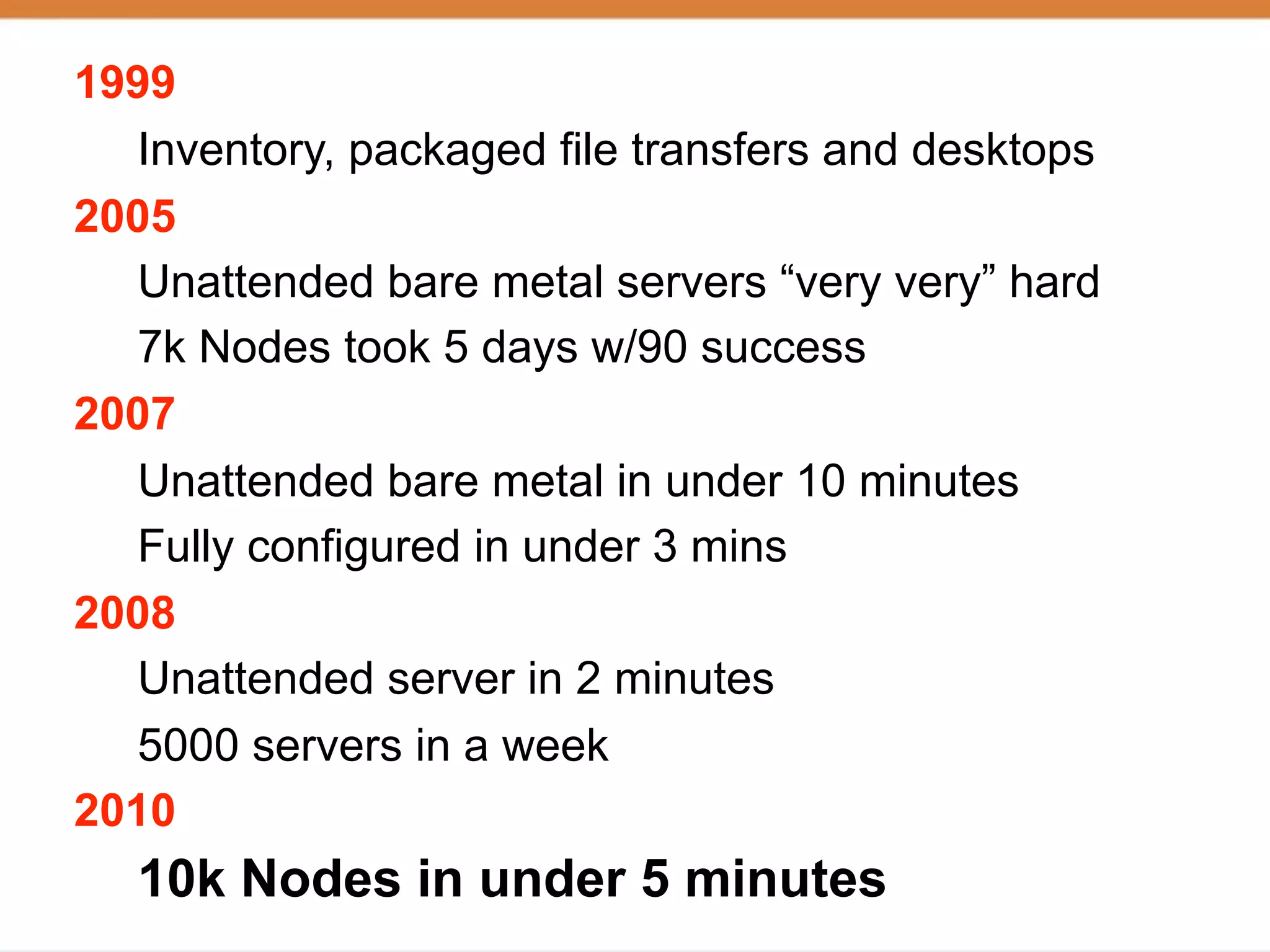
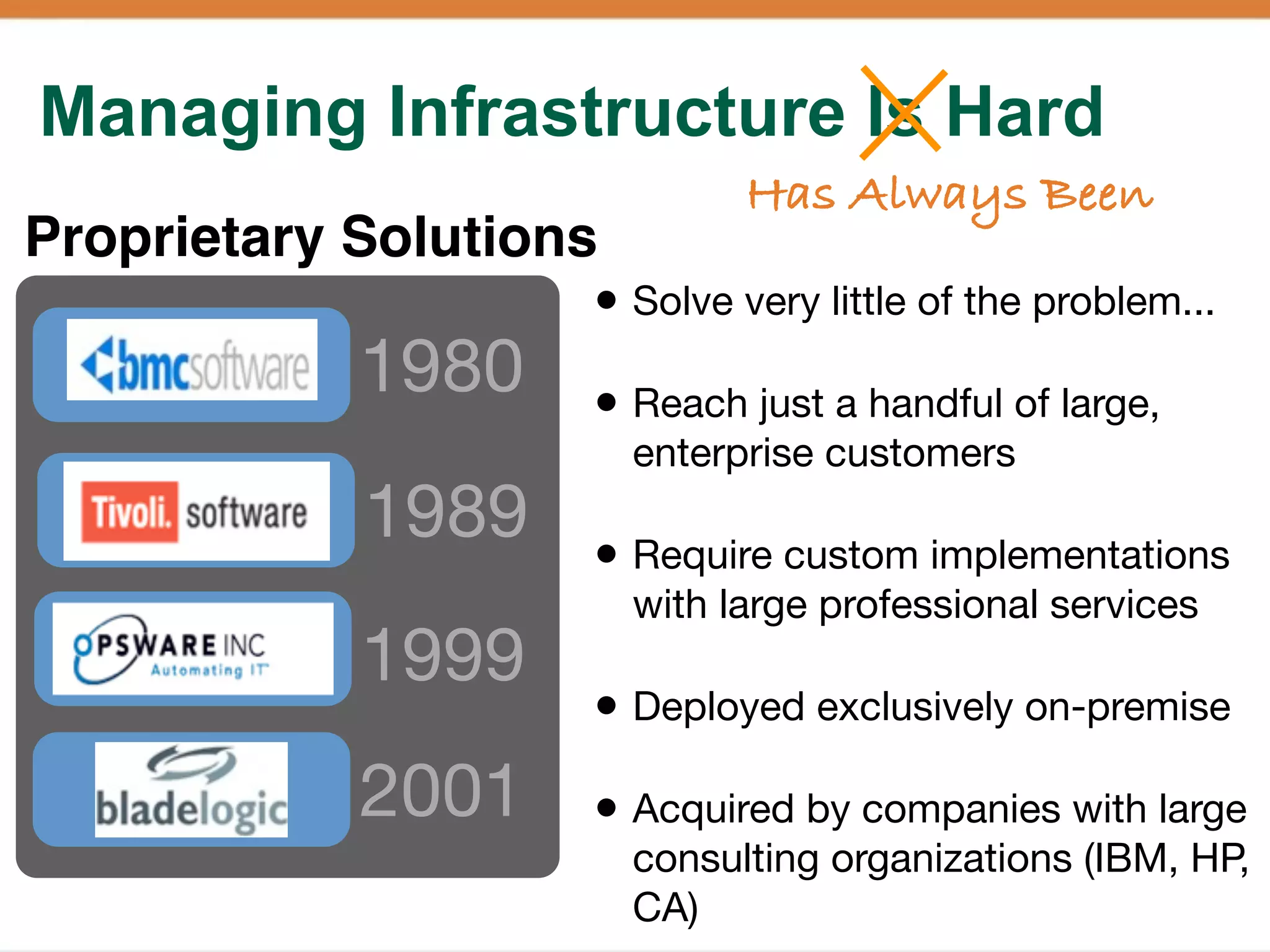
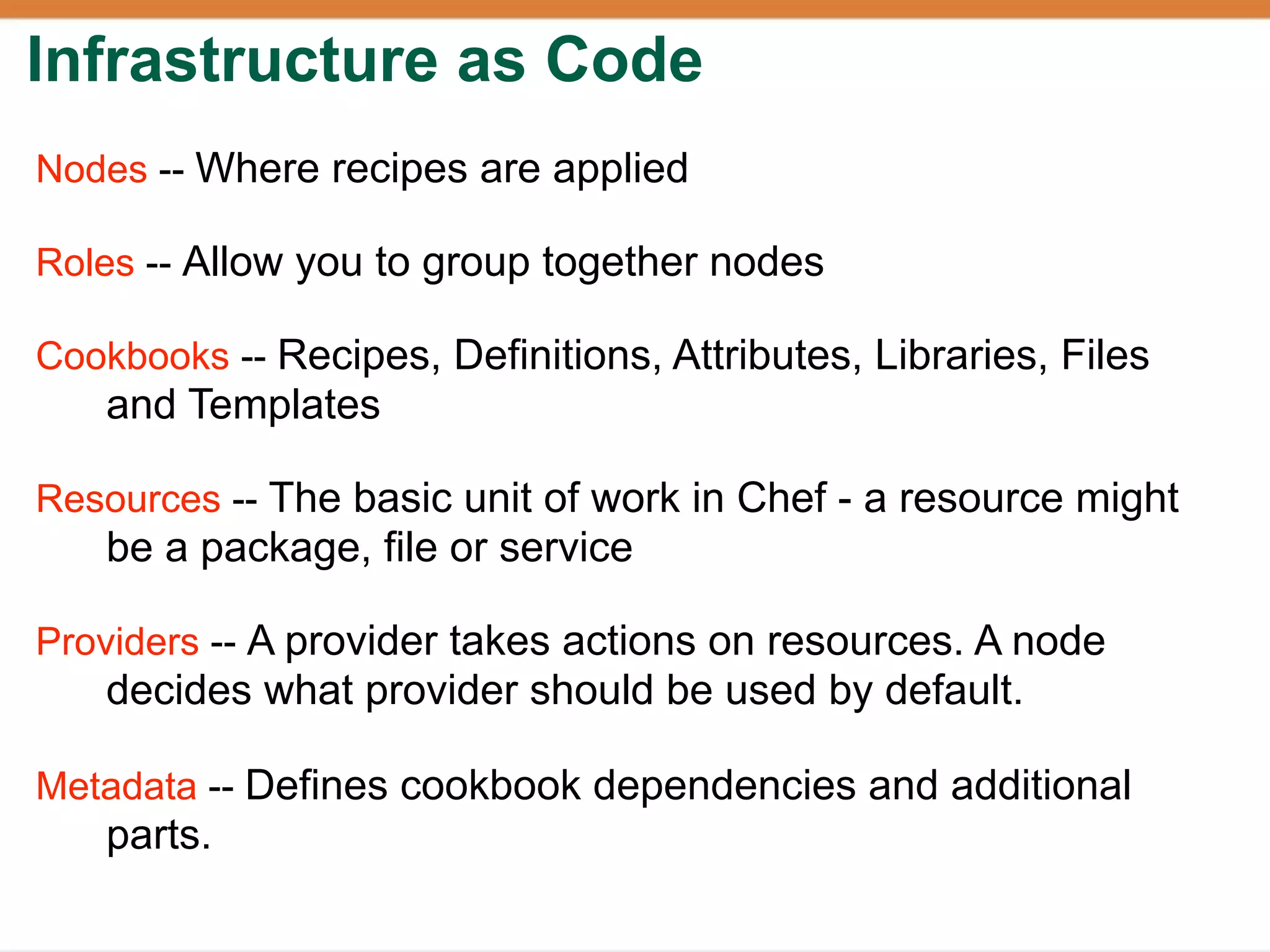
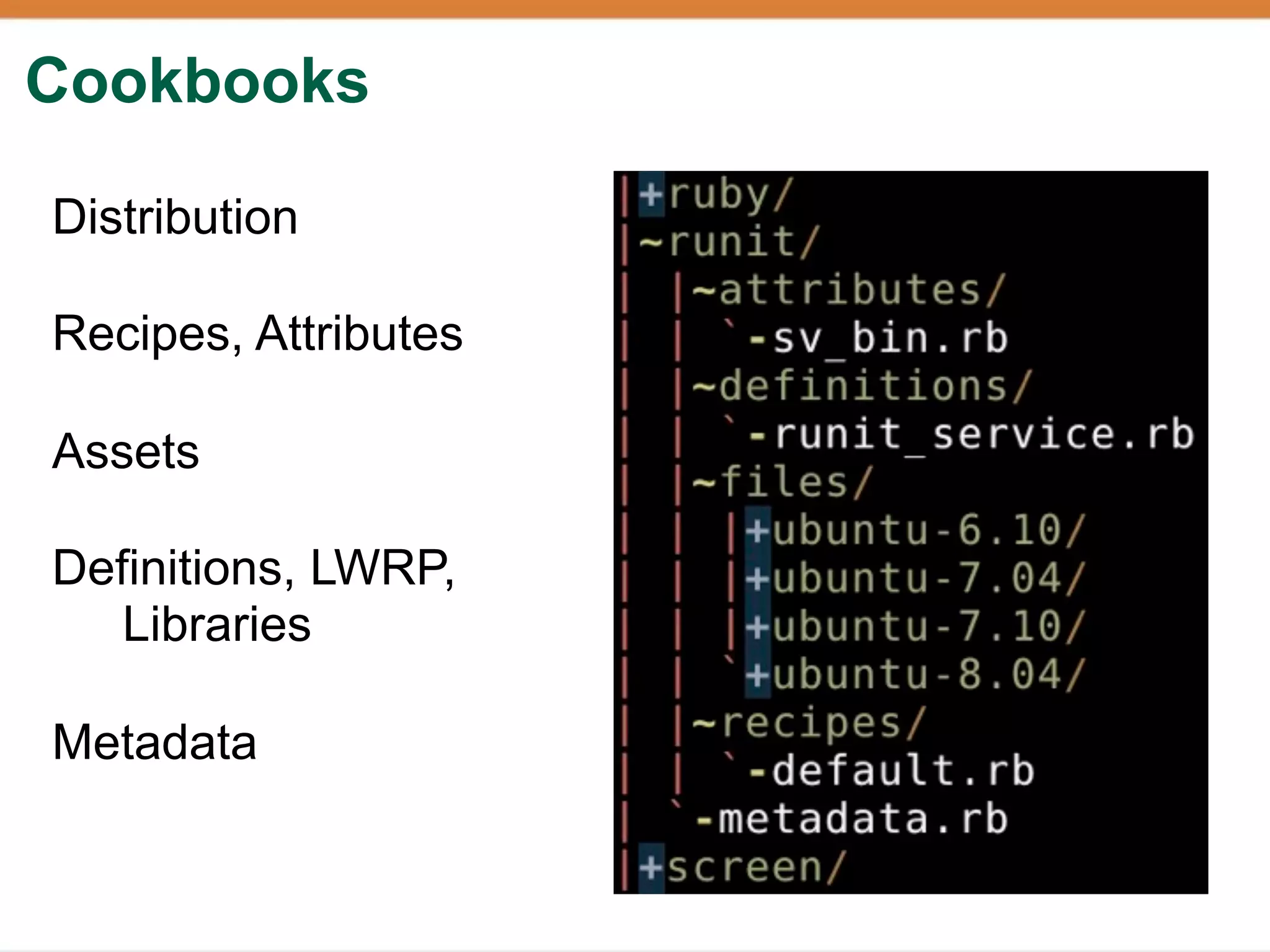
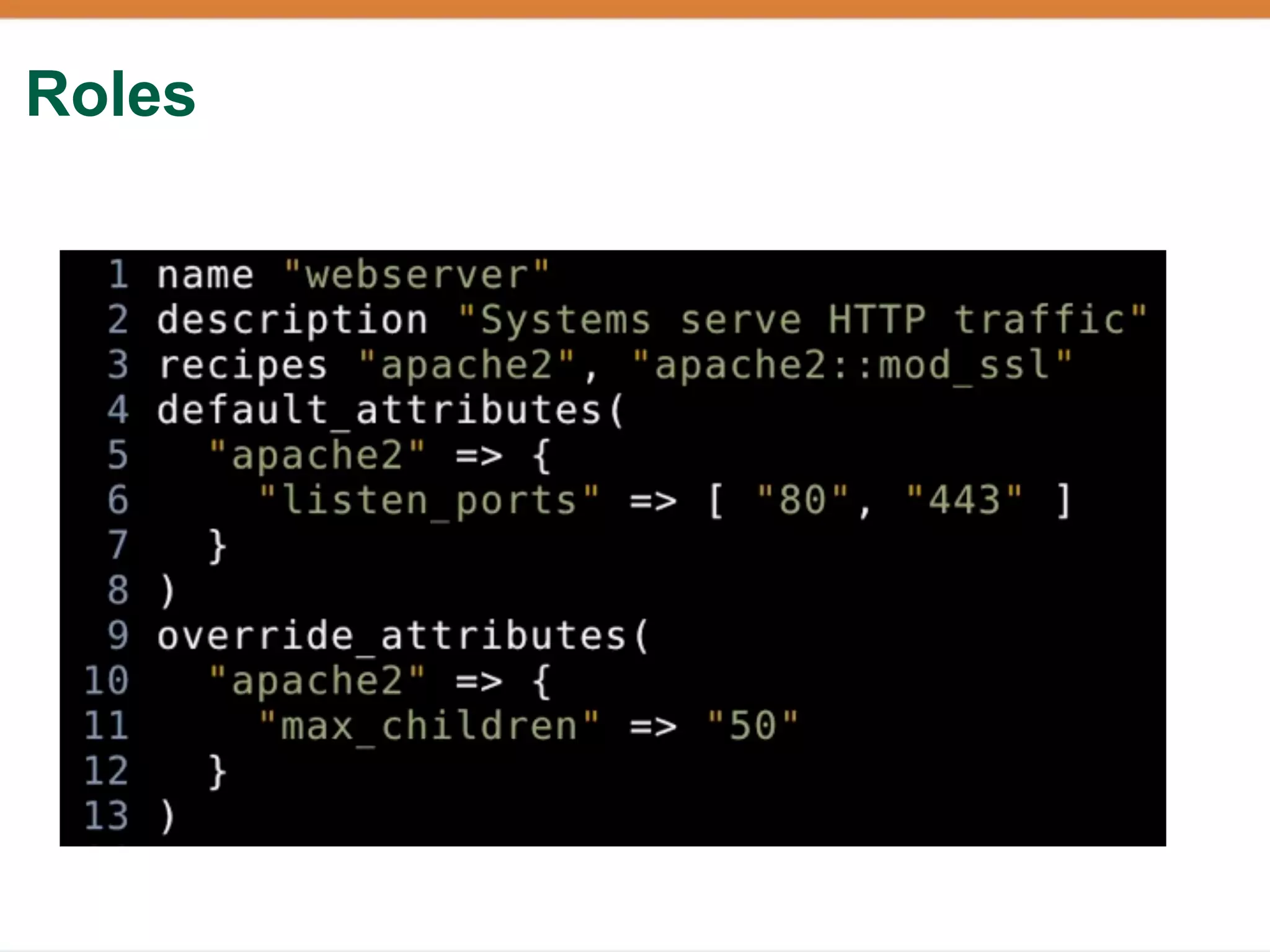
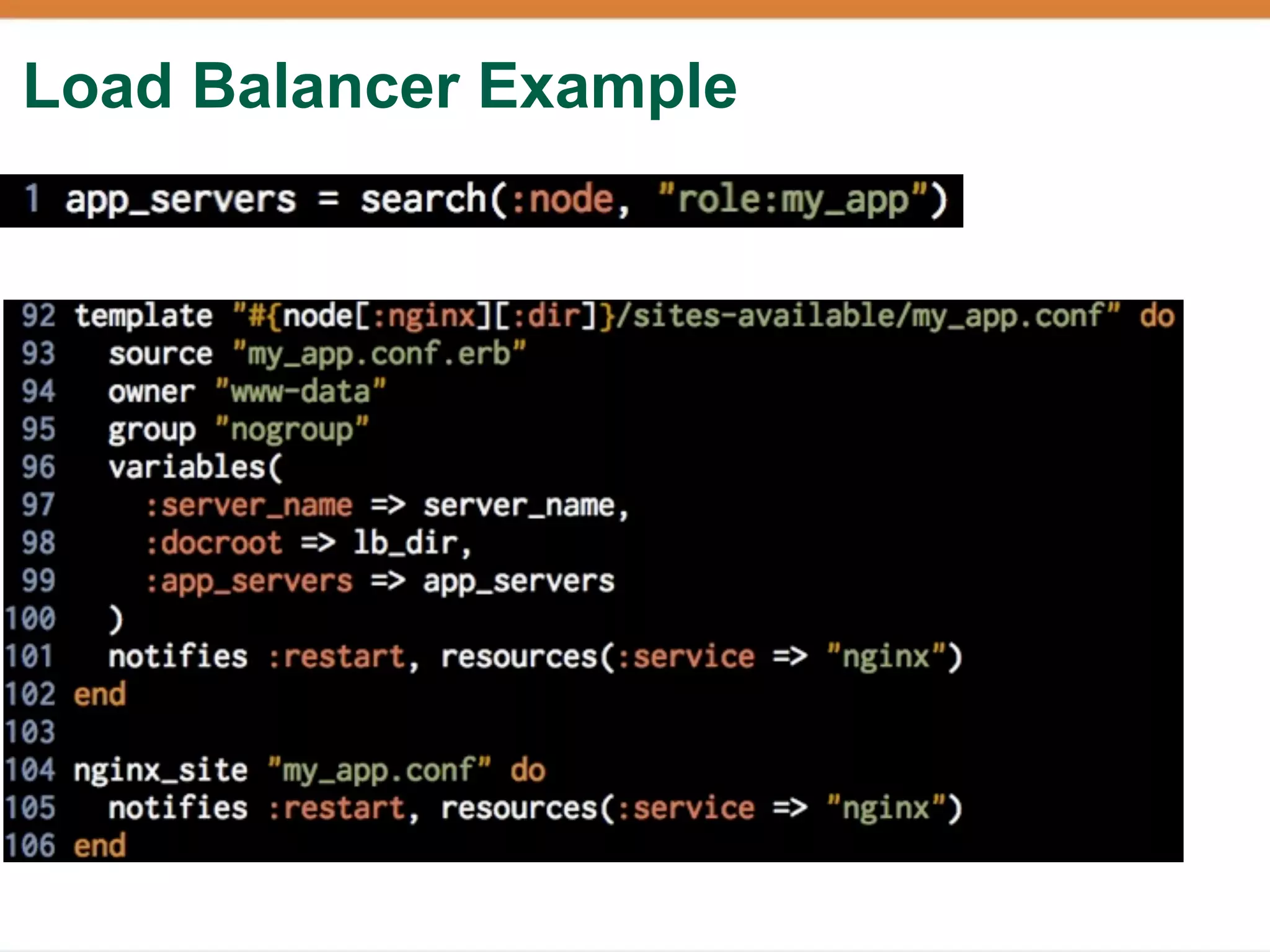
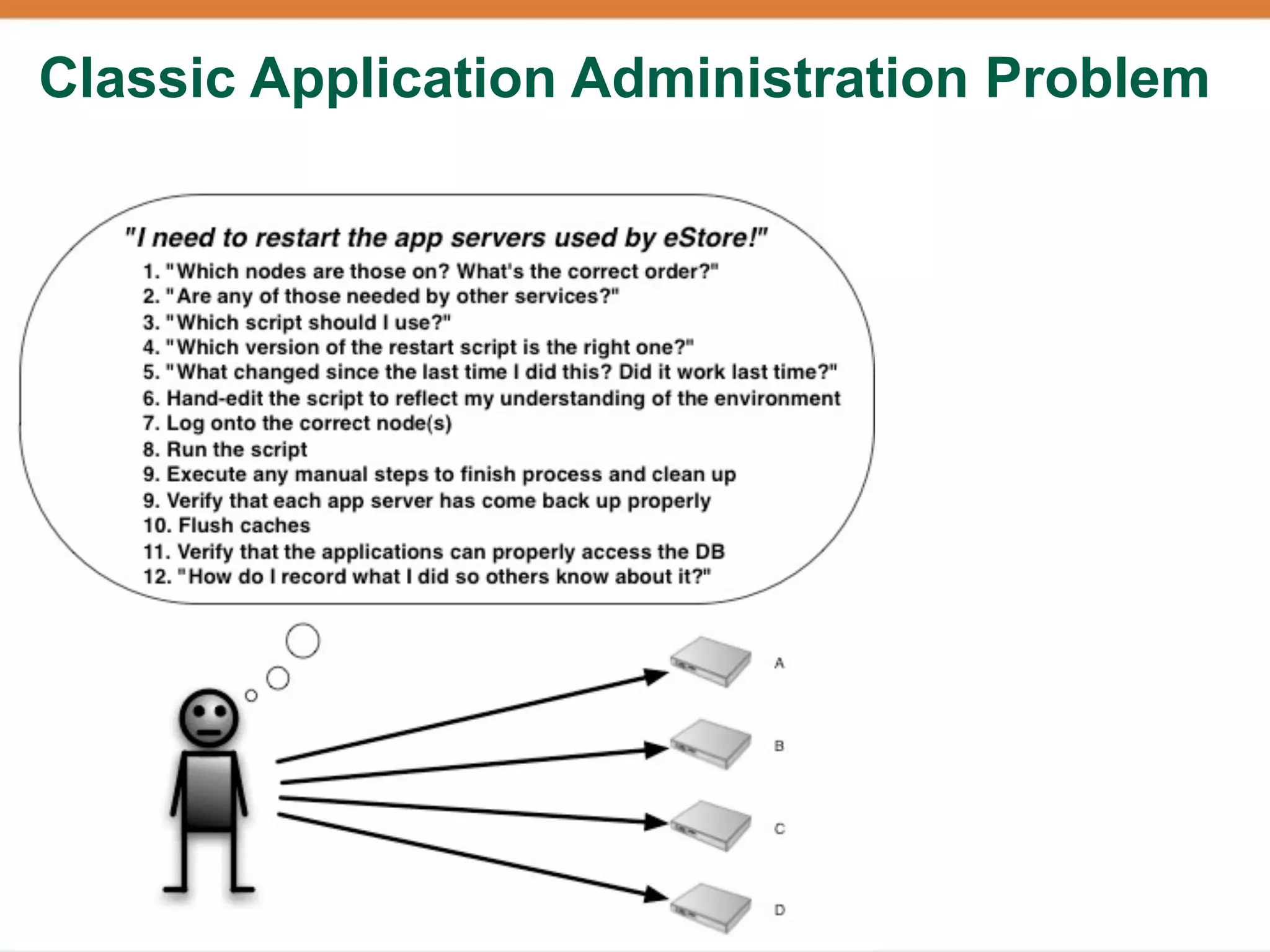
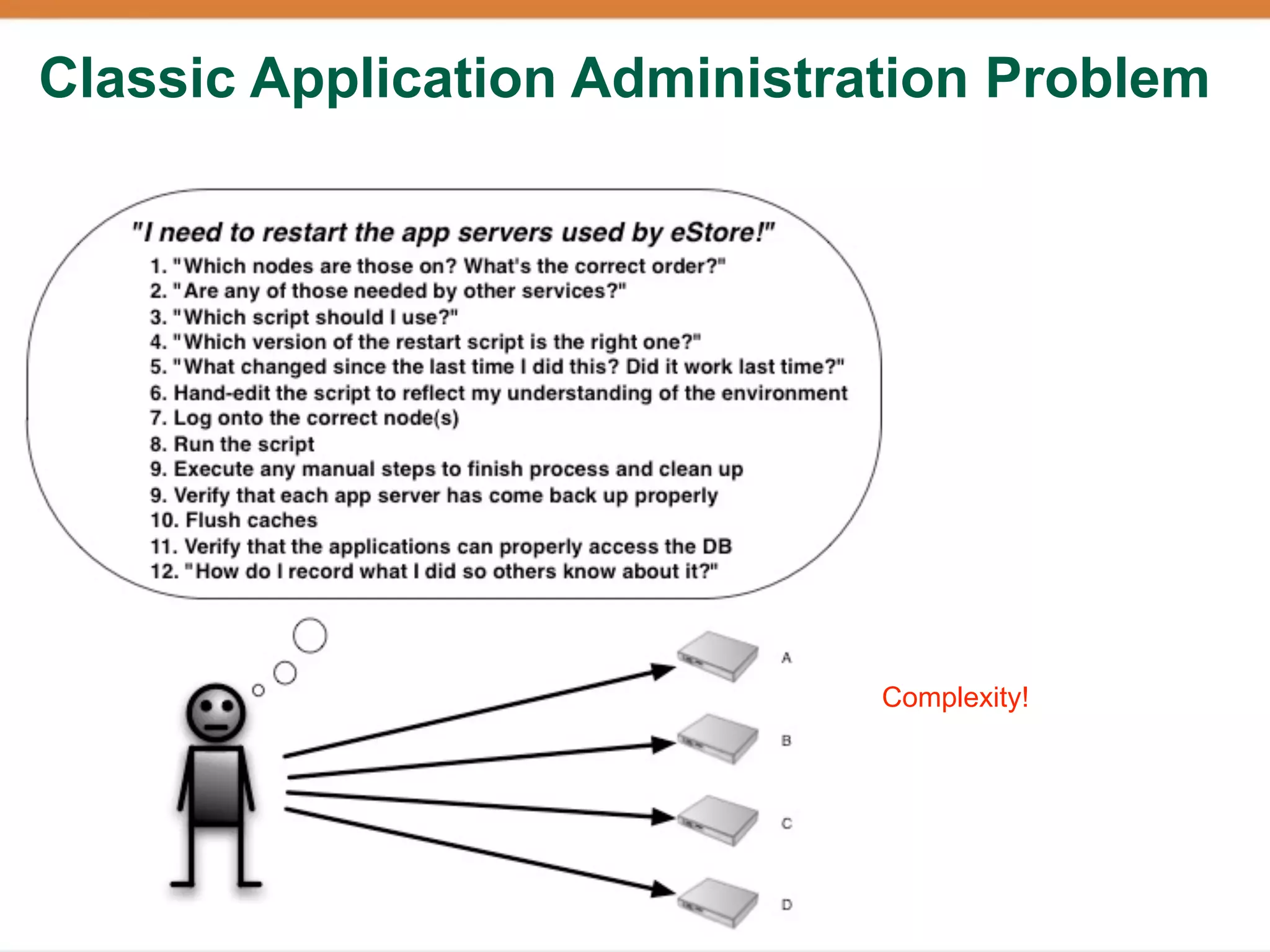
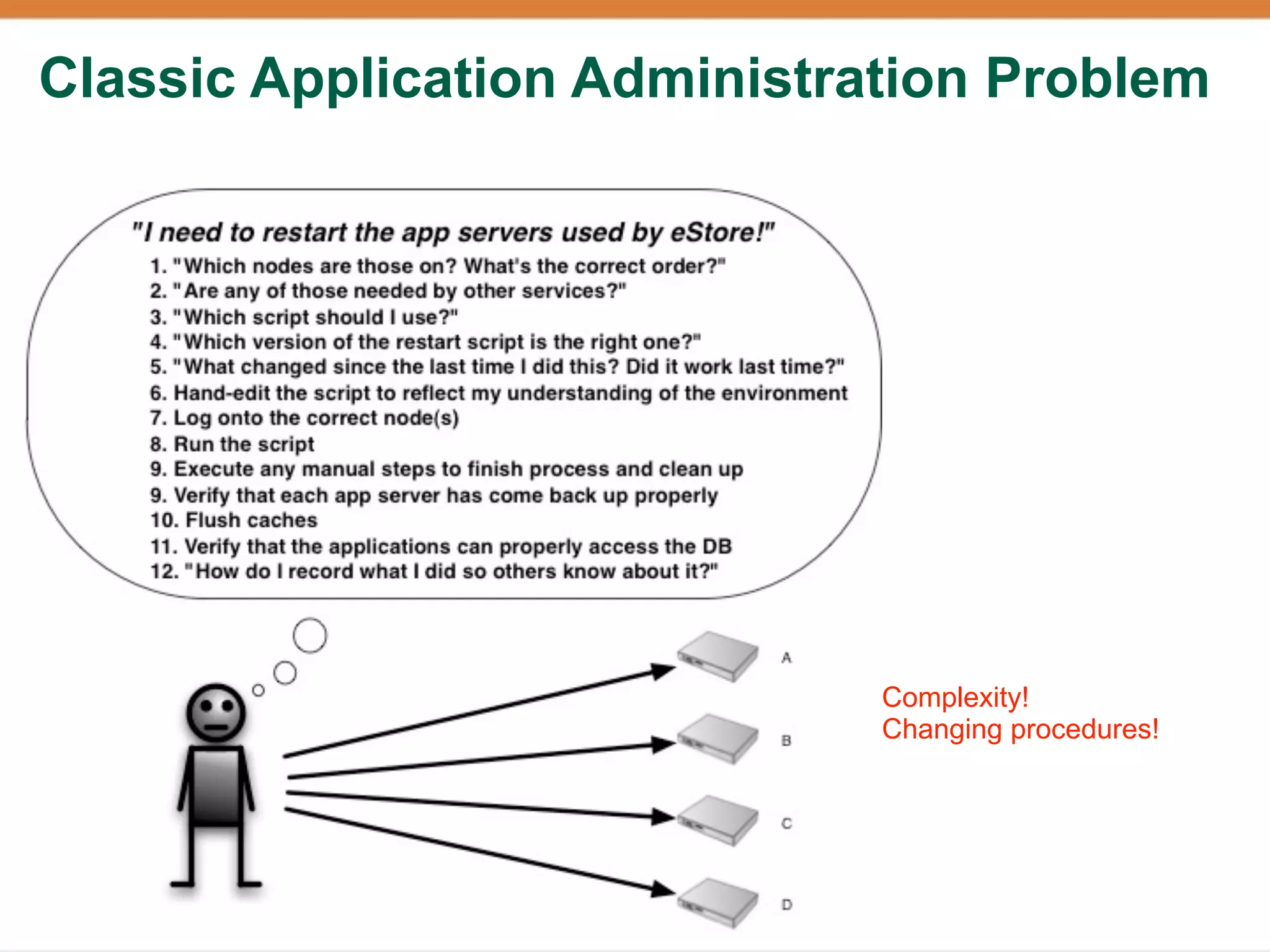
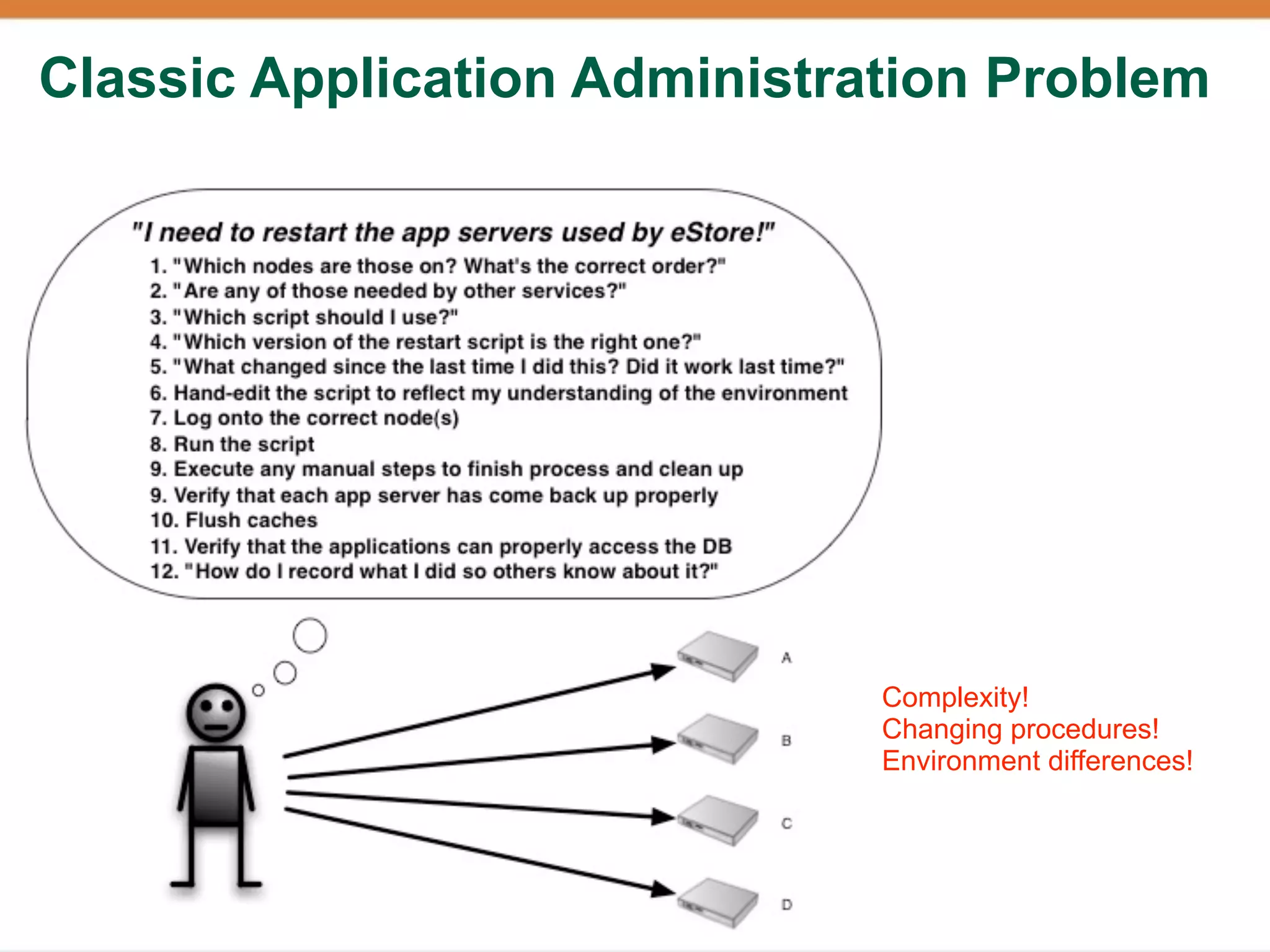
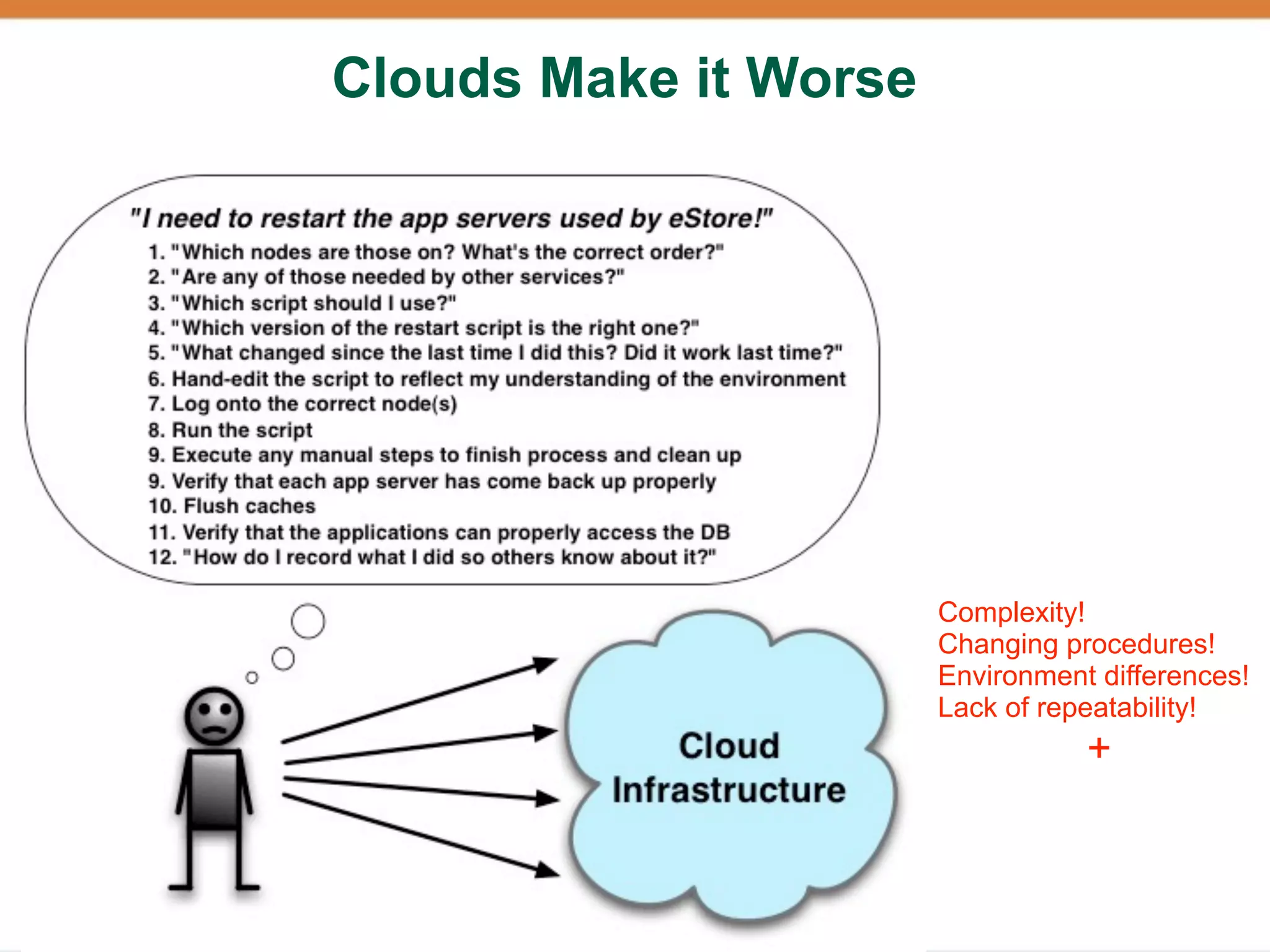
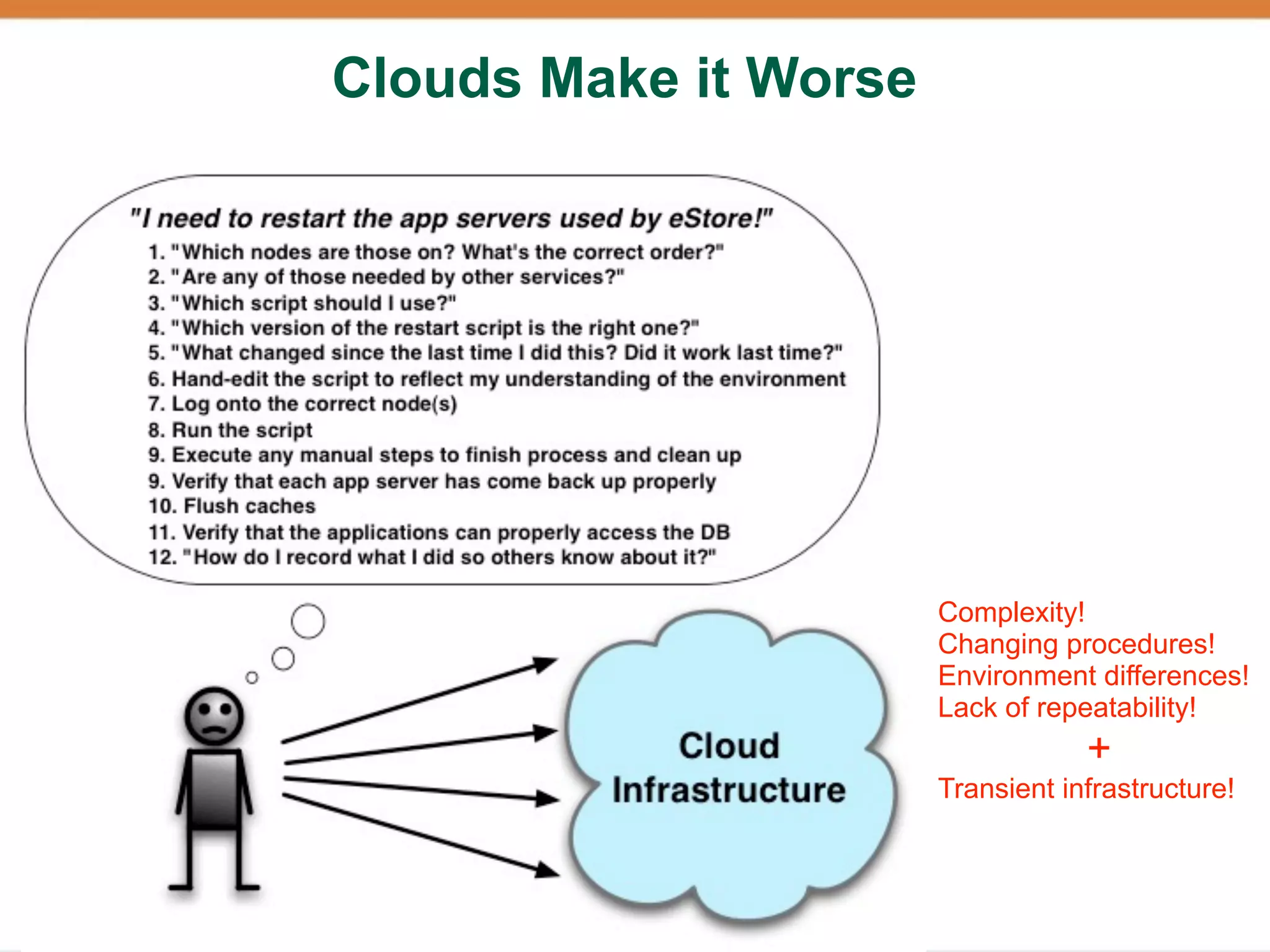
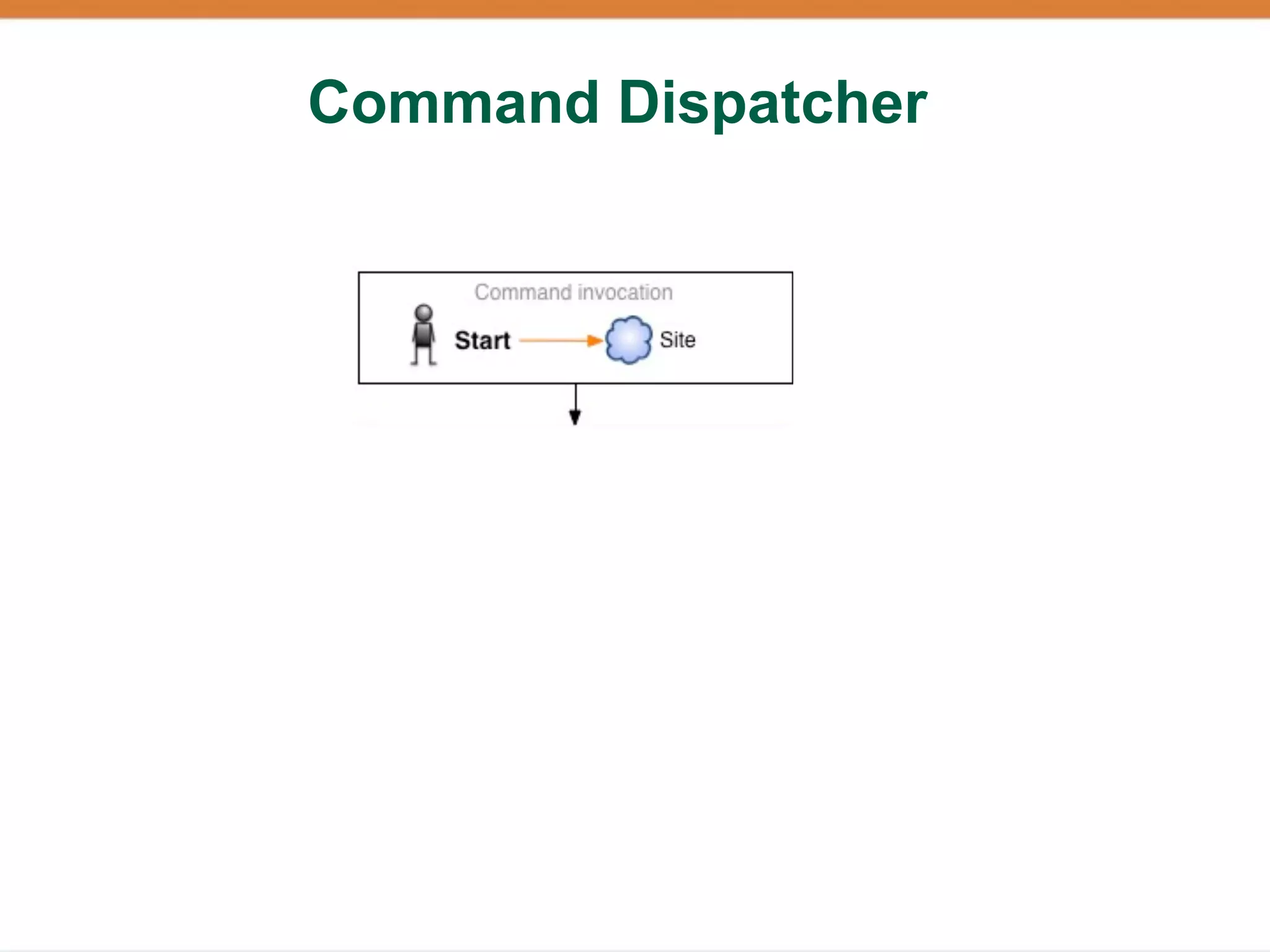
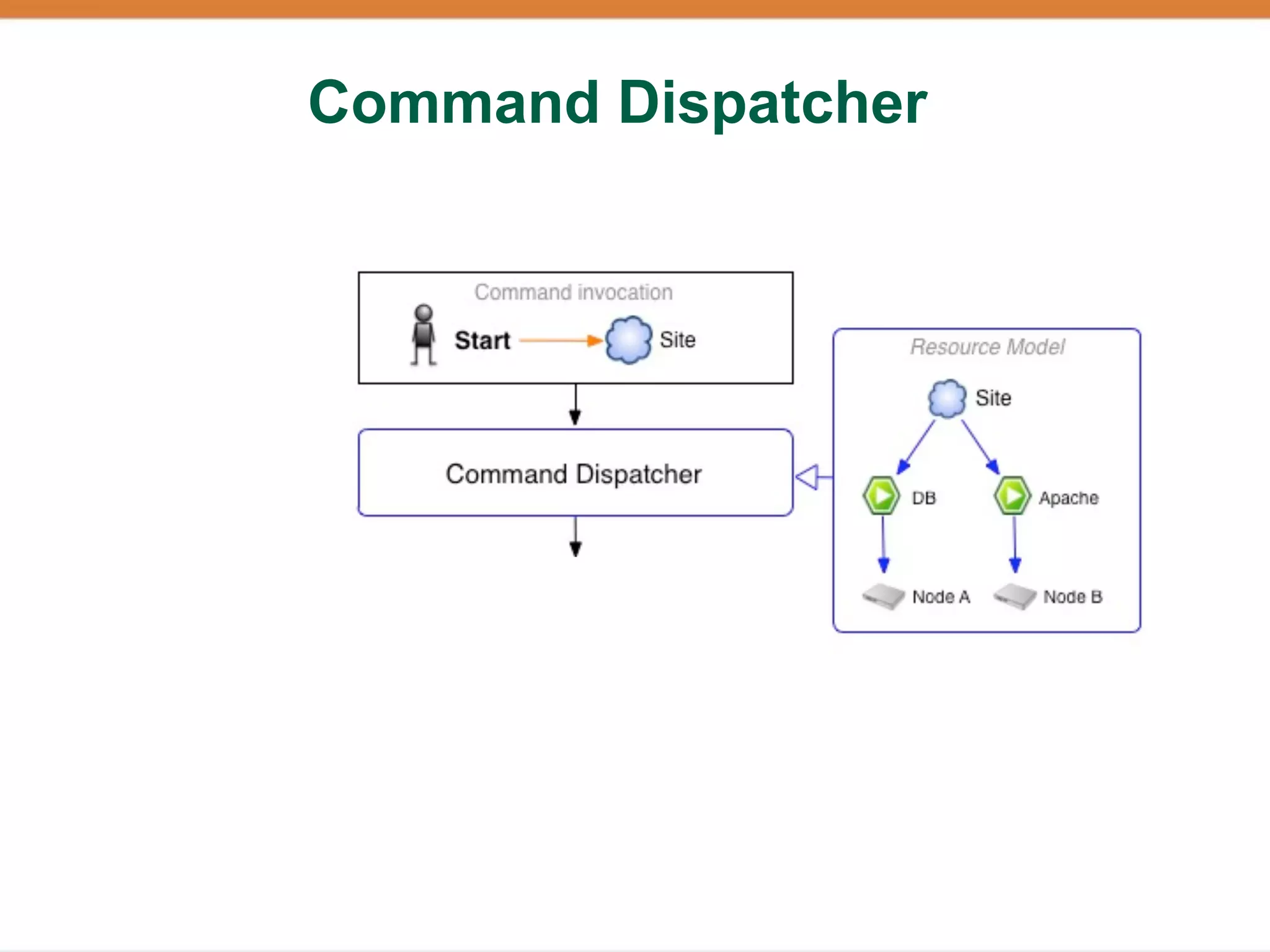
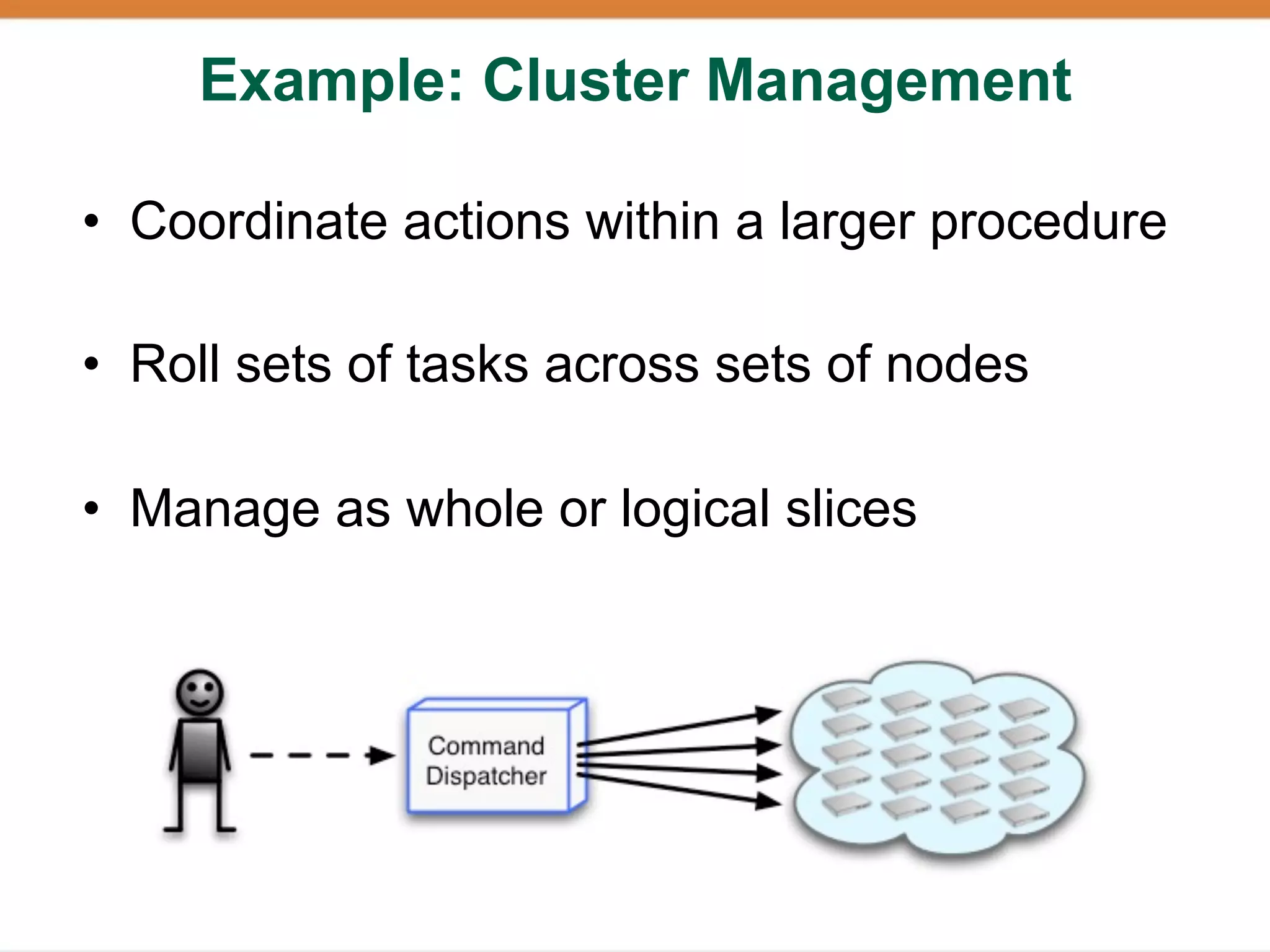
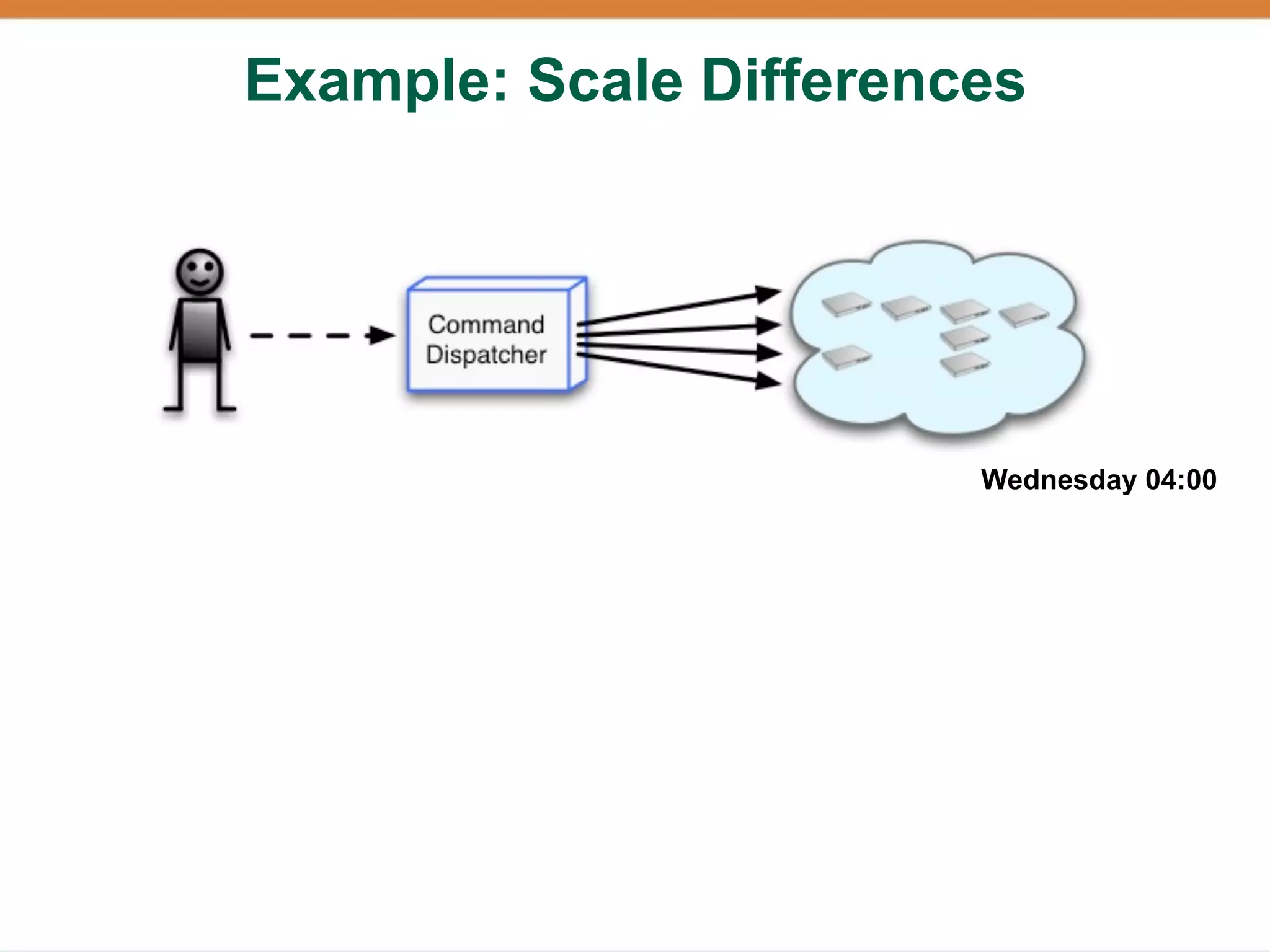
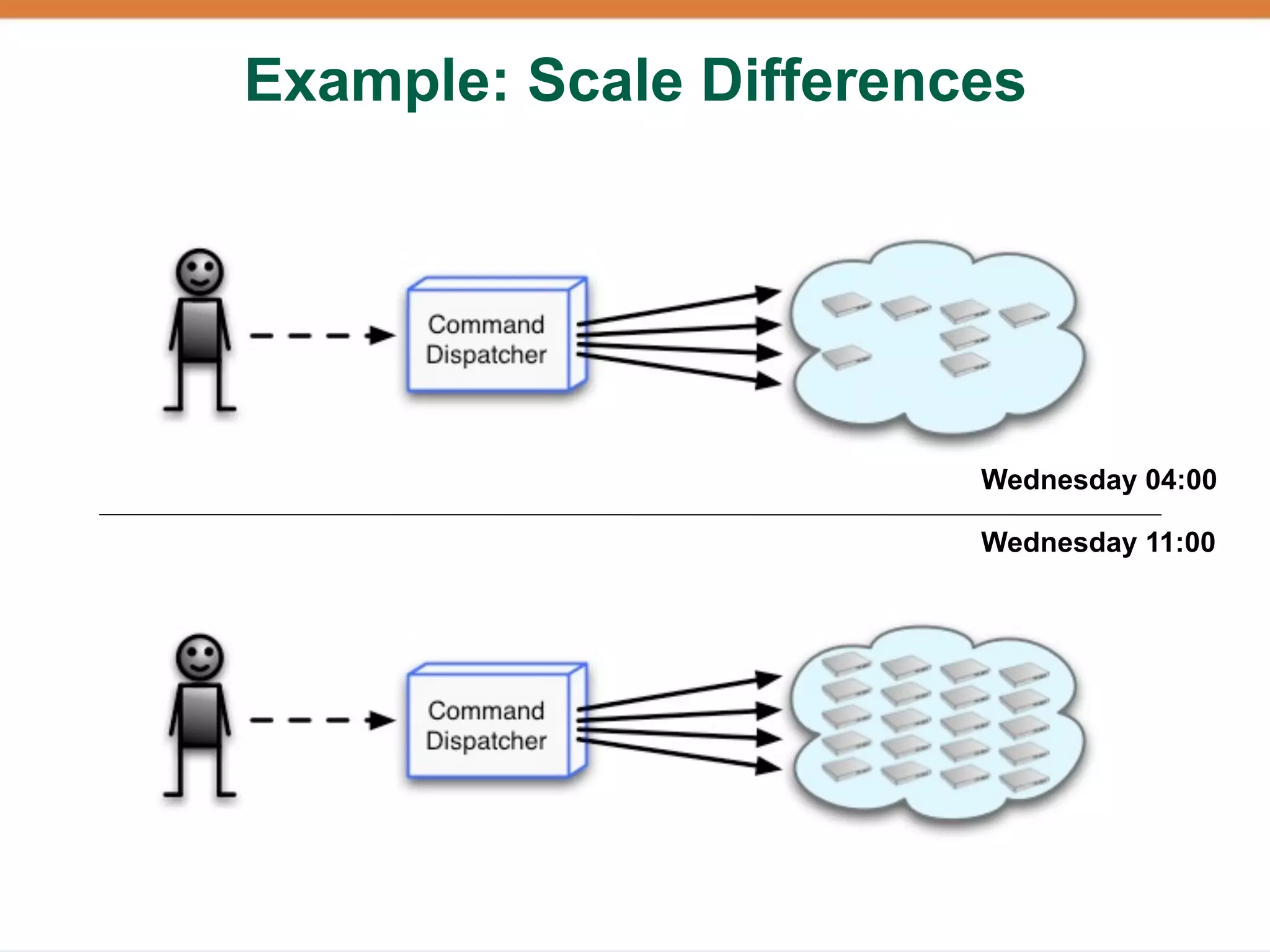
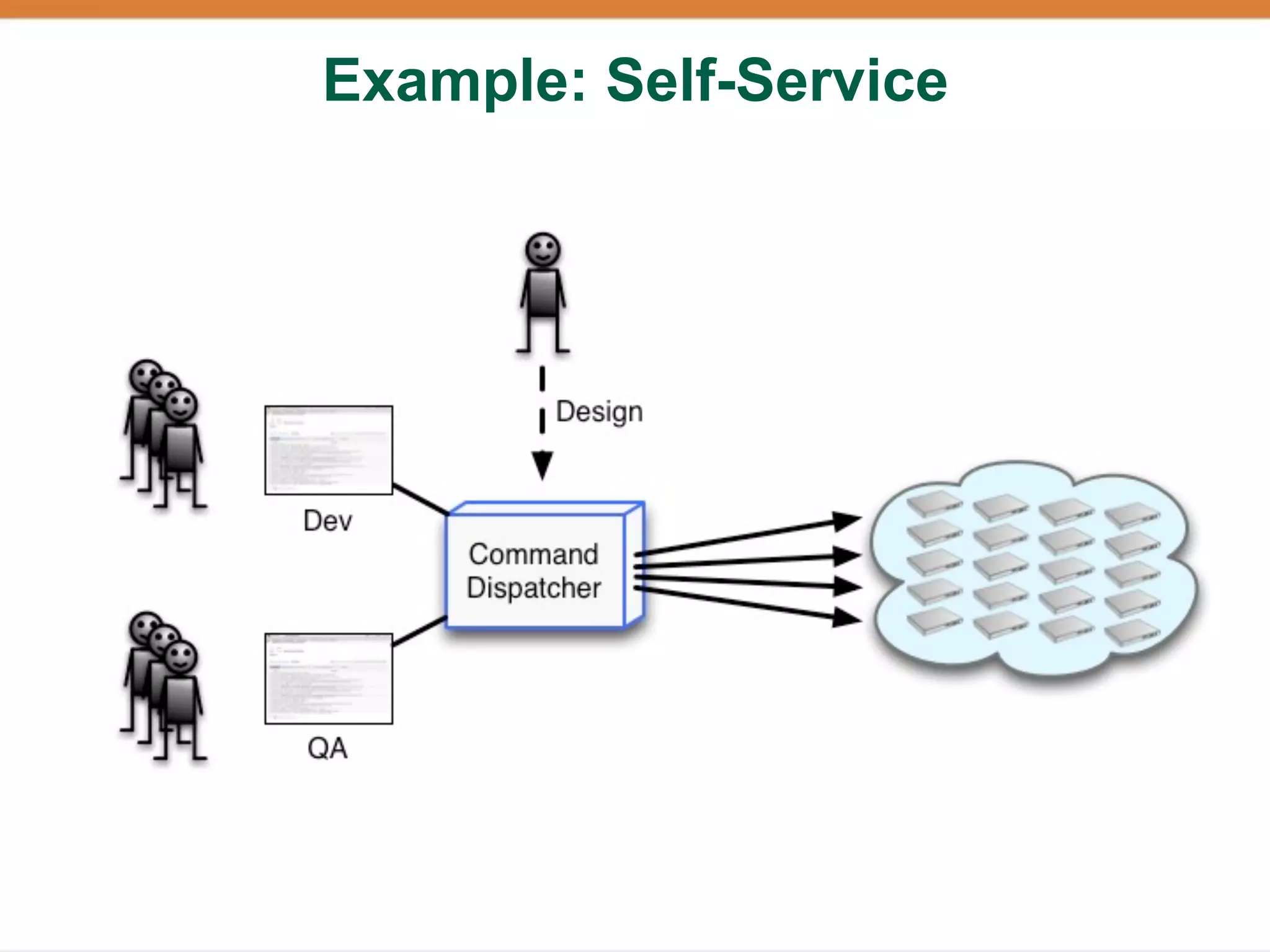
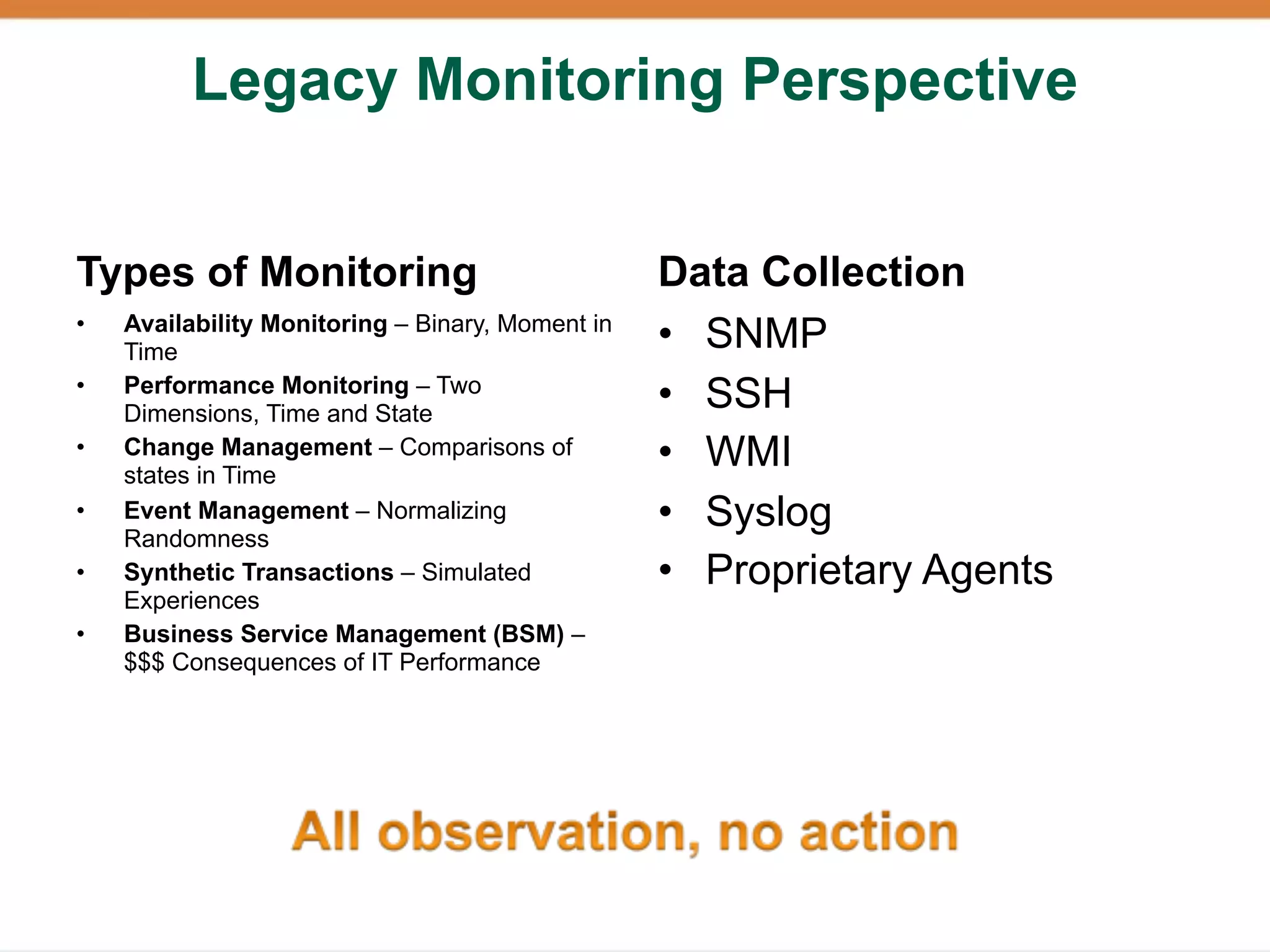
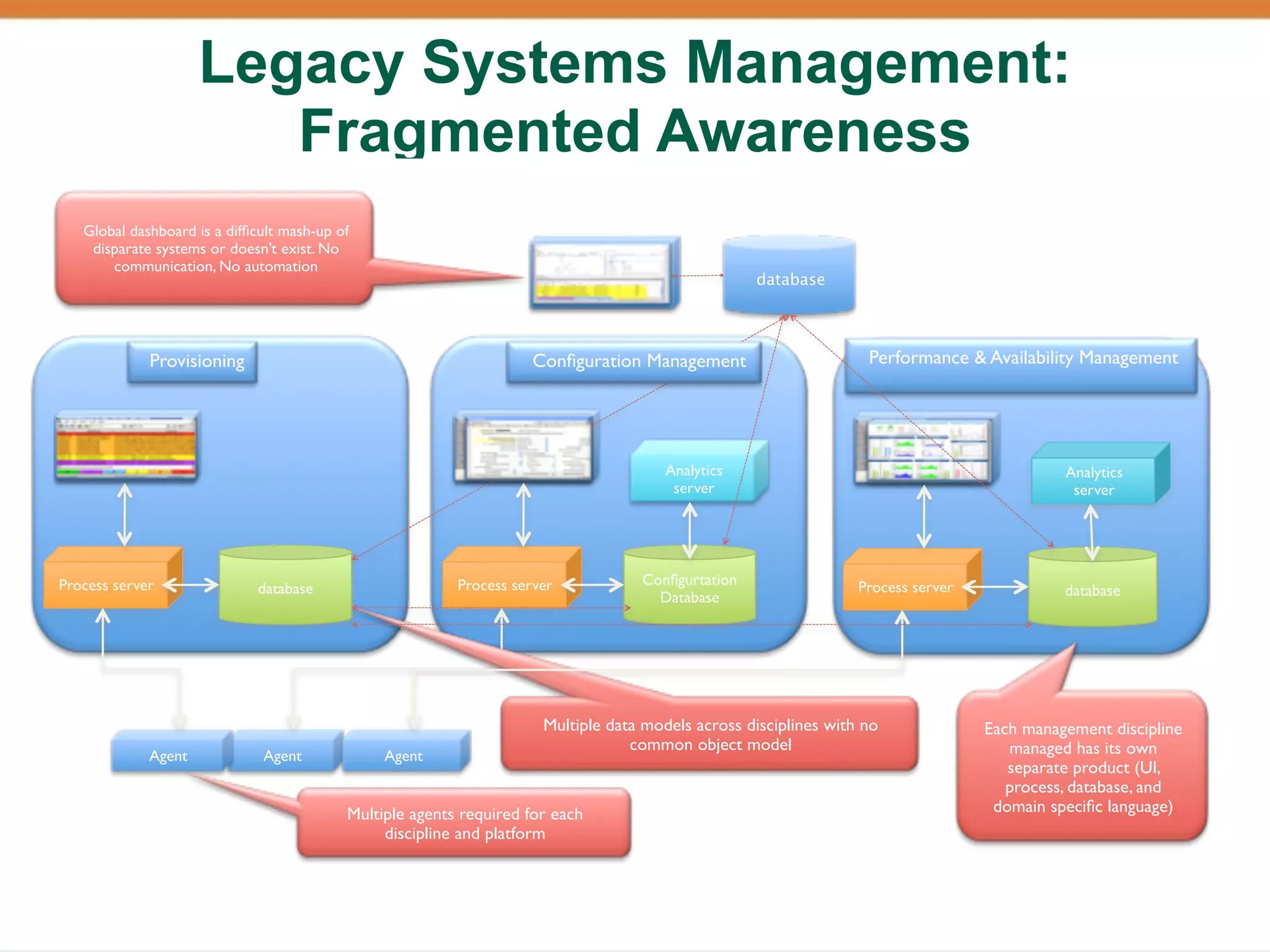
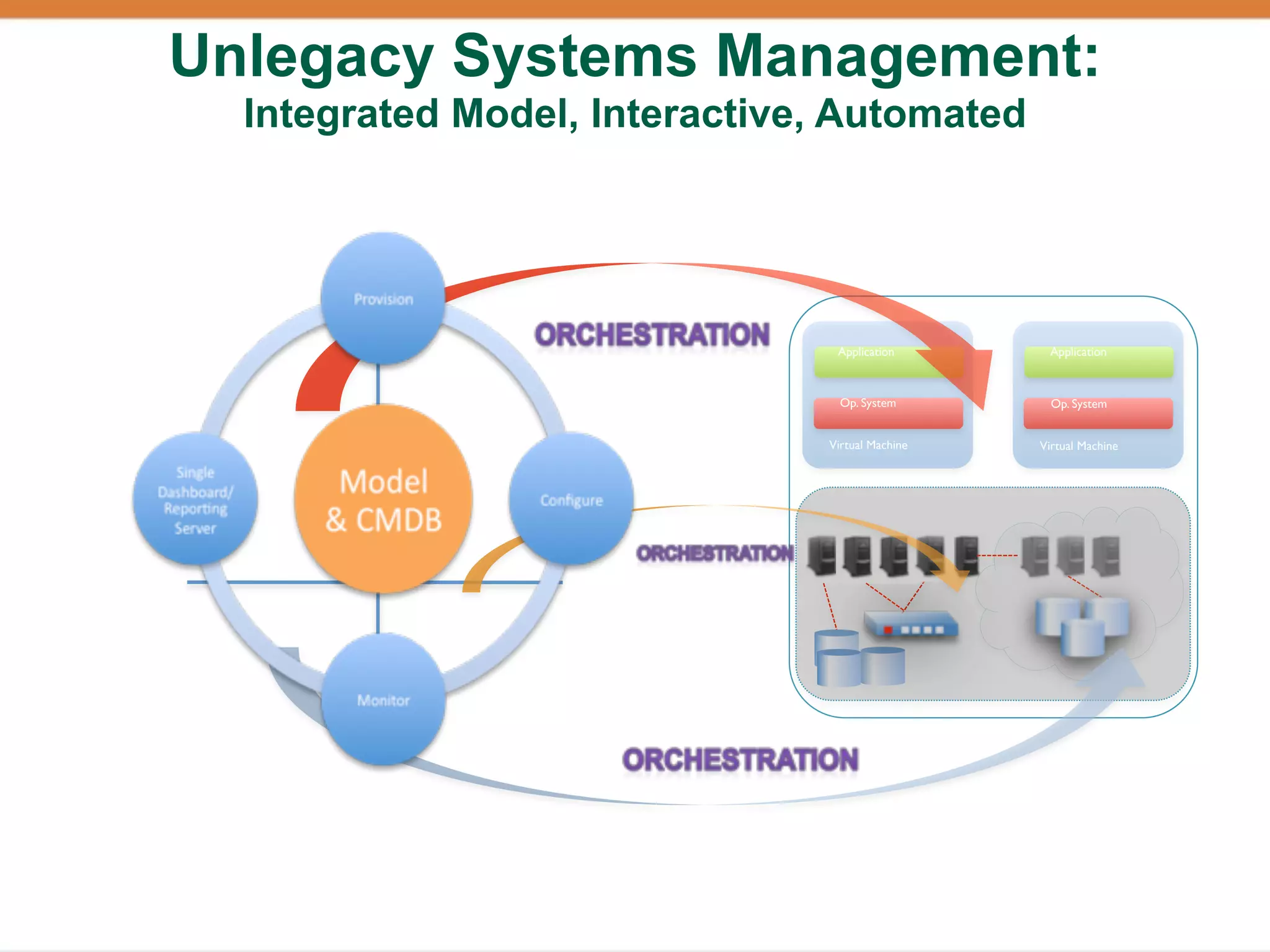
The document discusses orchestration in cloud applications, emphasizing the need for alignment between development, operations, and business practices. It covers the evolution of infrastructure management from proprietary solutions to open-source tools and highlights the complexity introduced by cloud environments. The importance of application mobility and integration of various systems for efficient cloud management is also stressed.