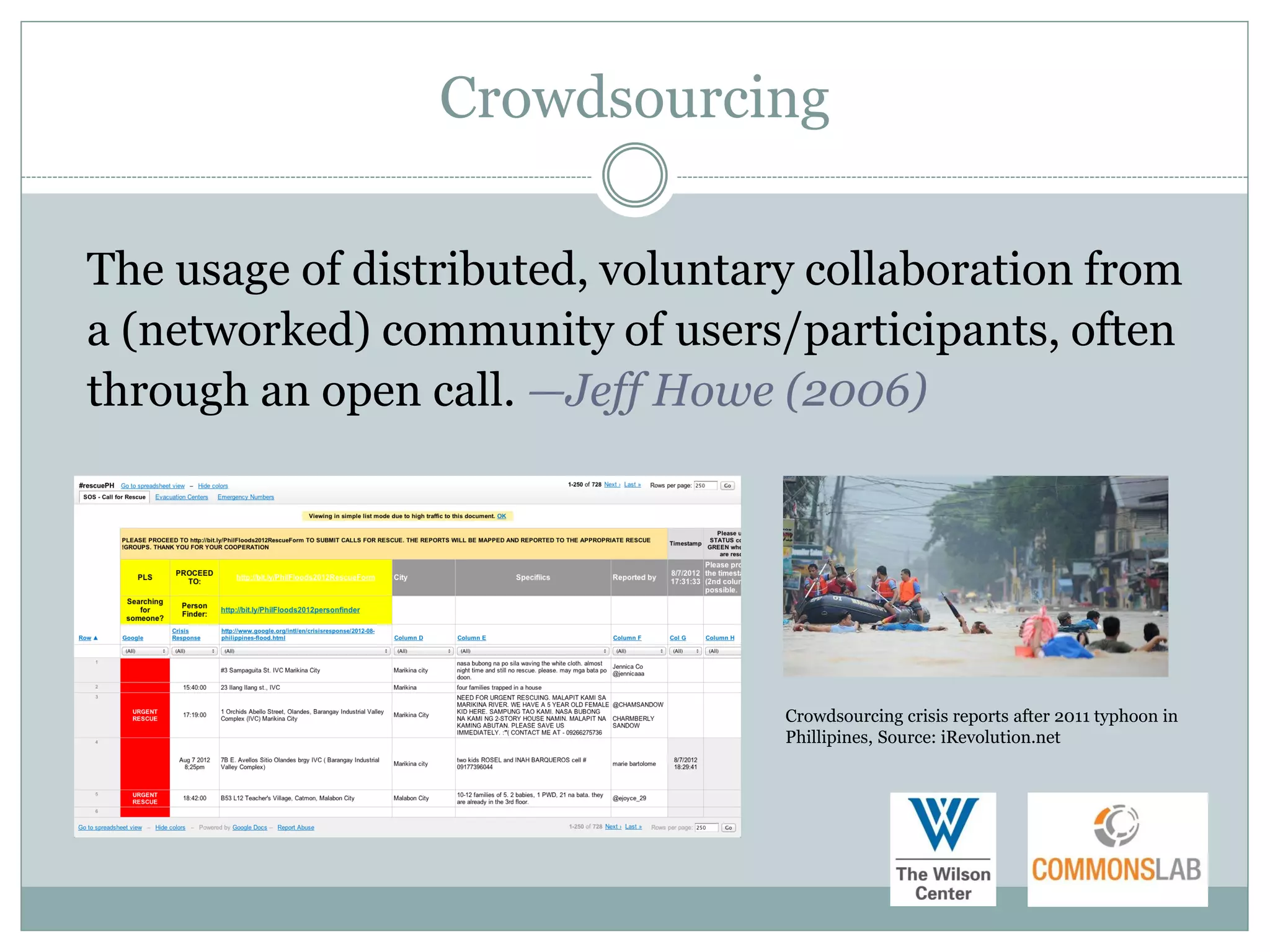
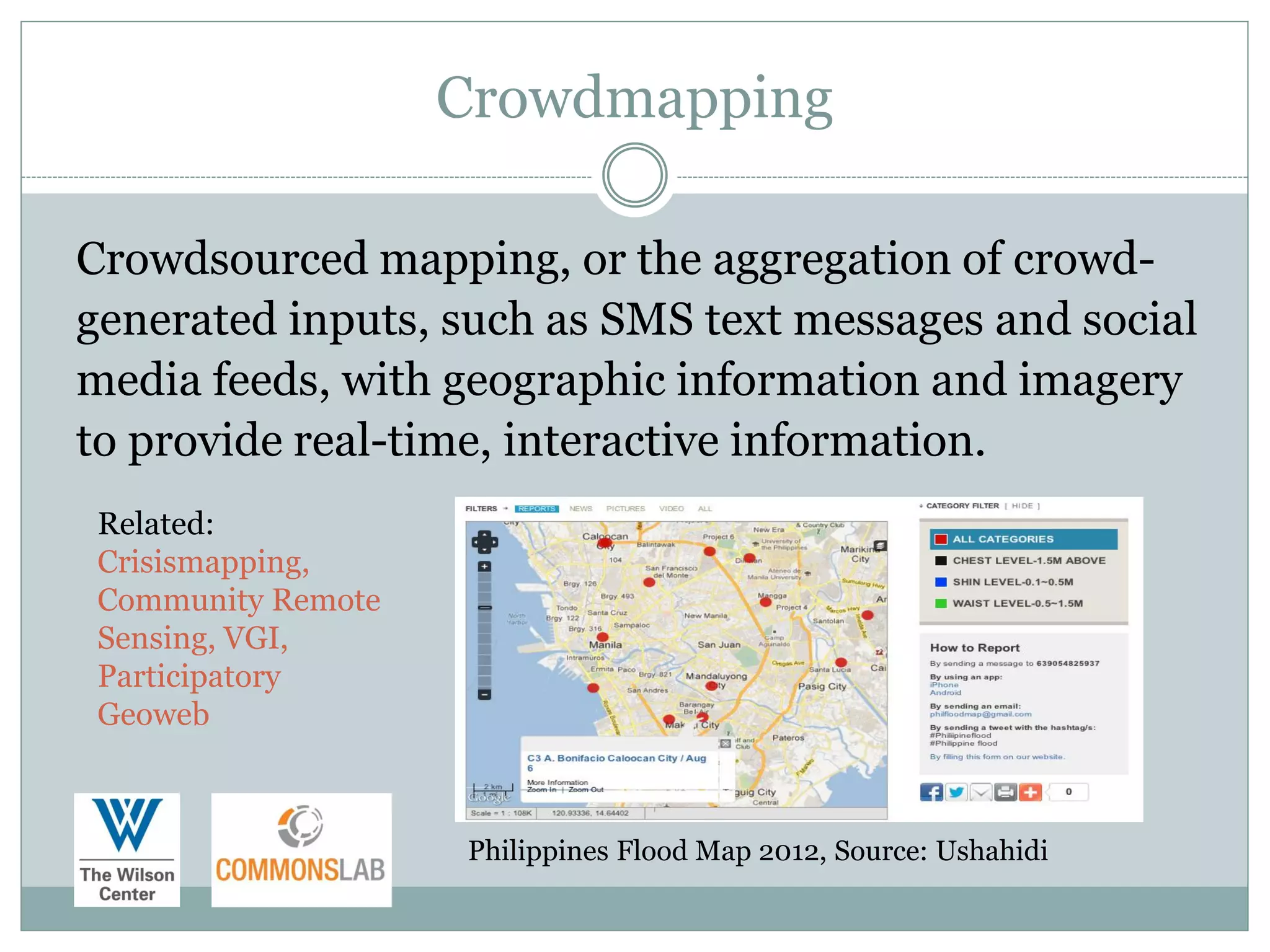
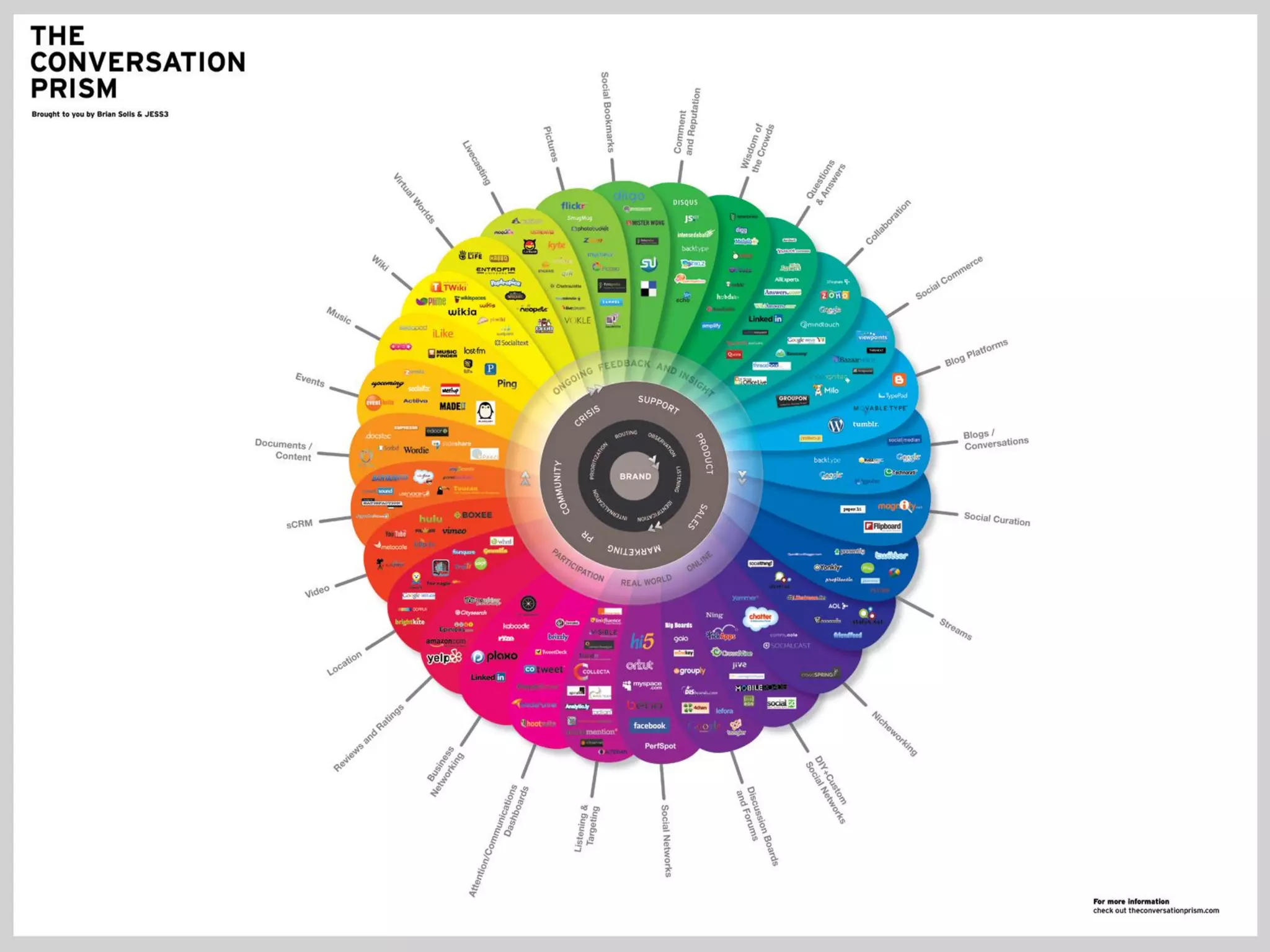
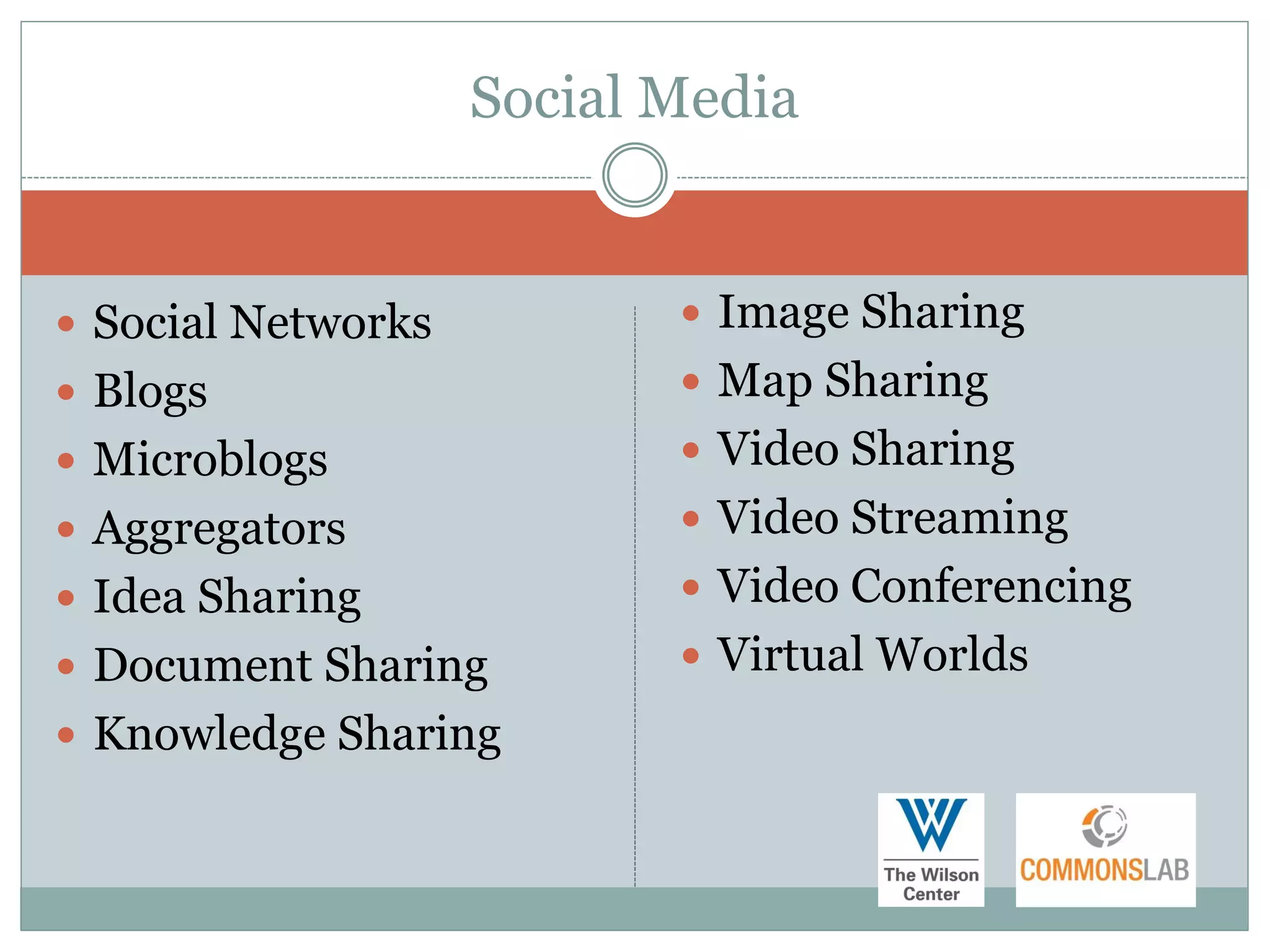
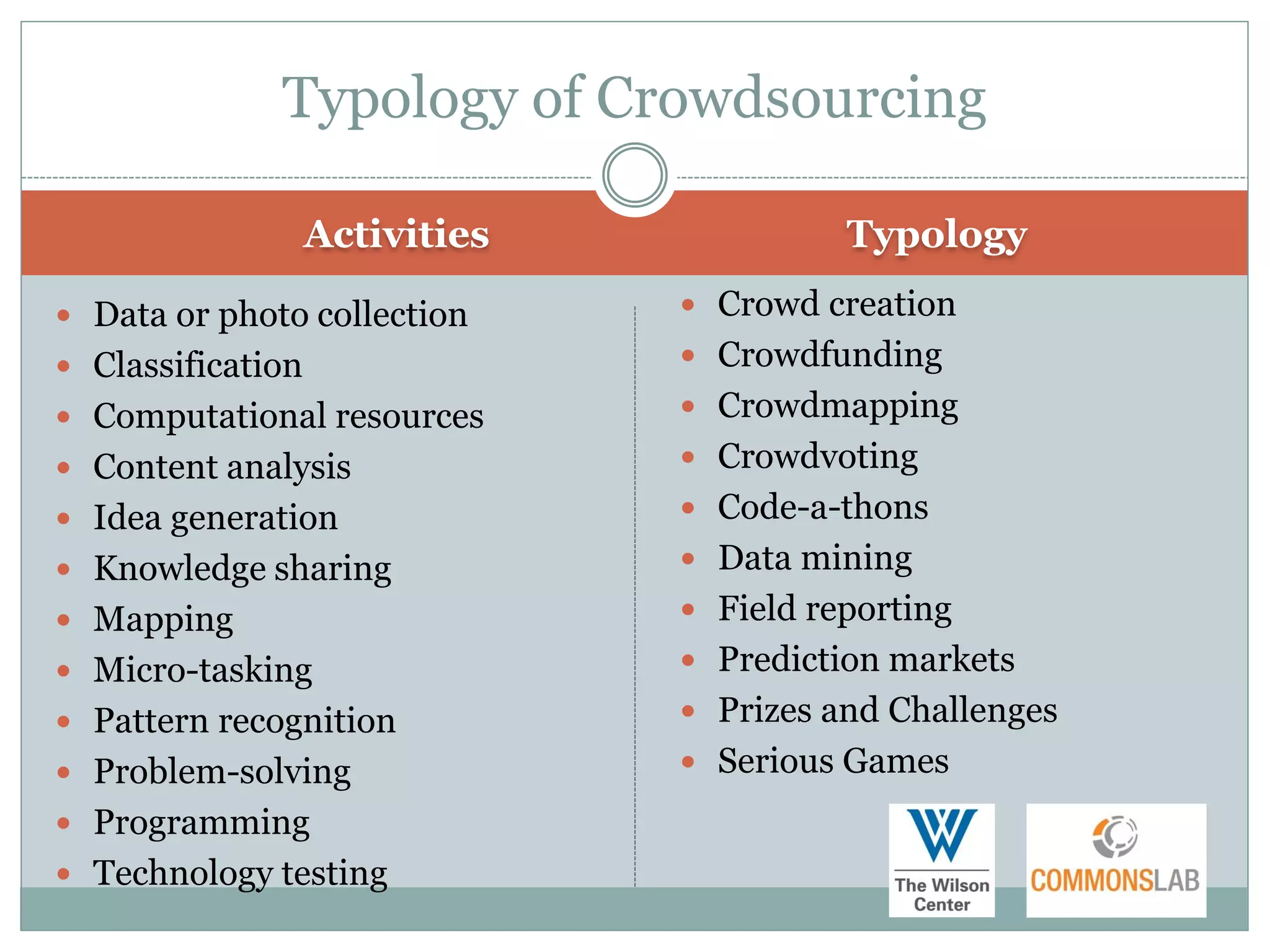
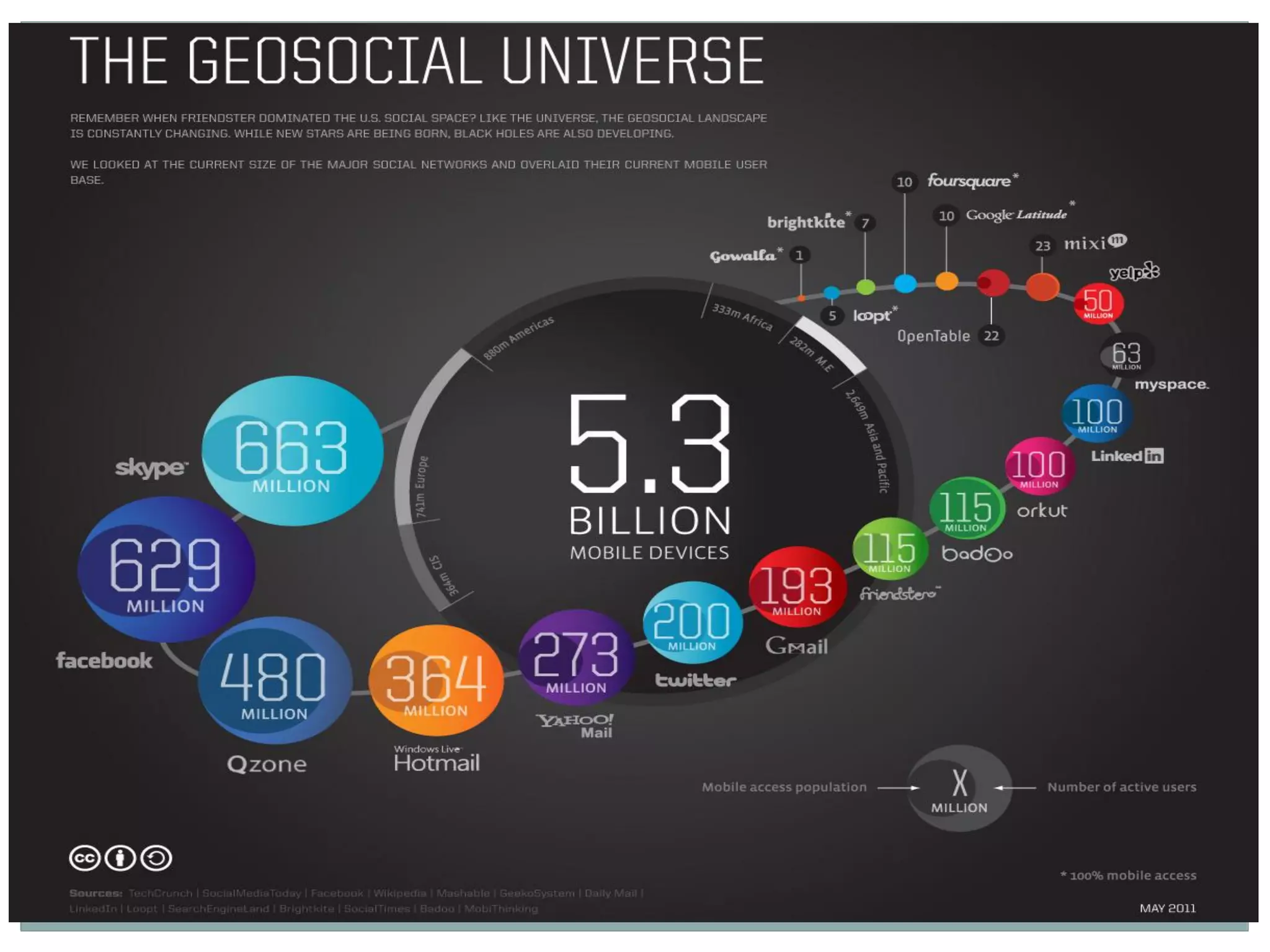
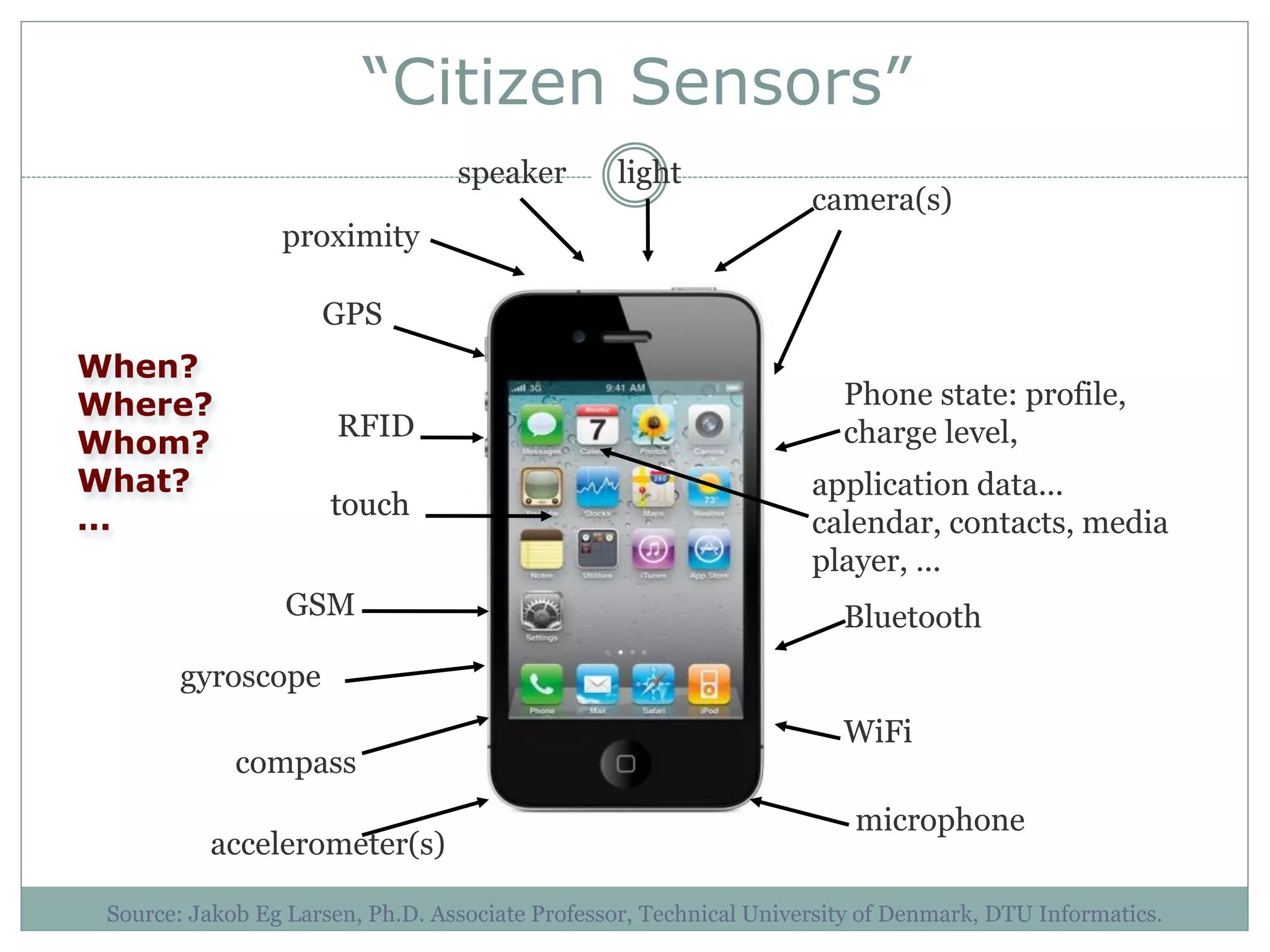
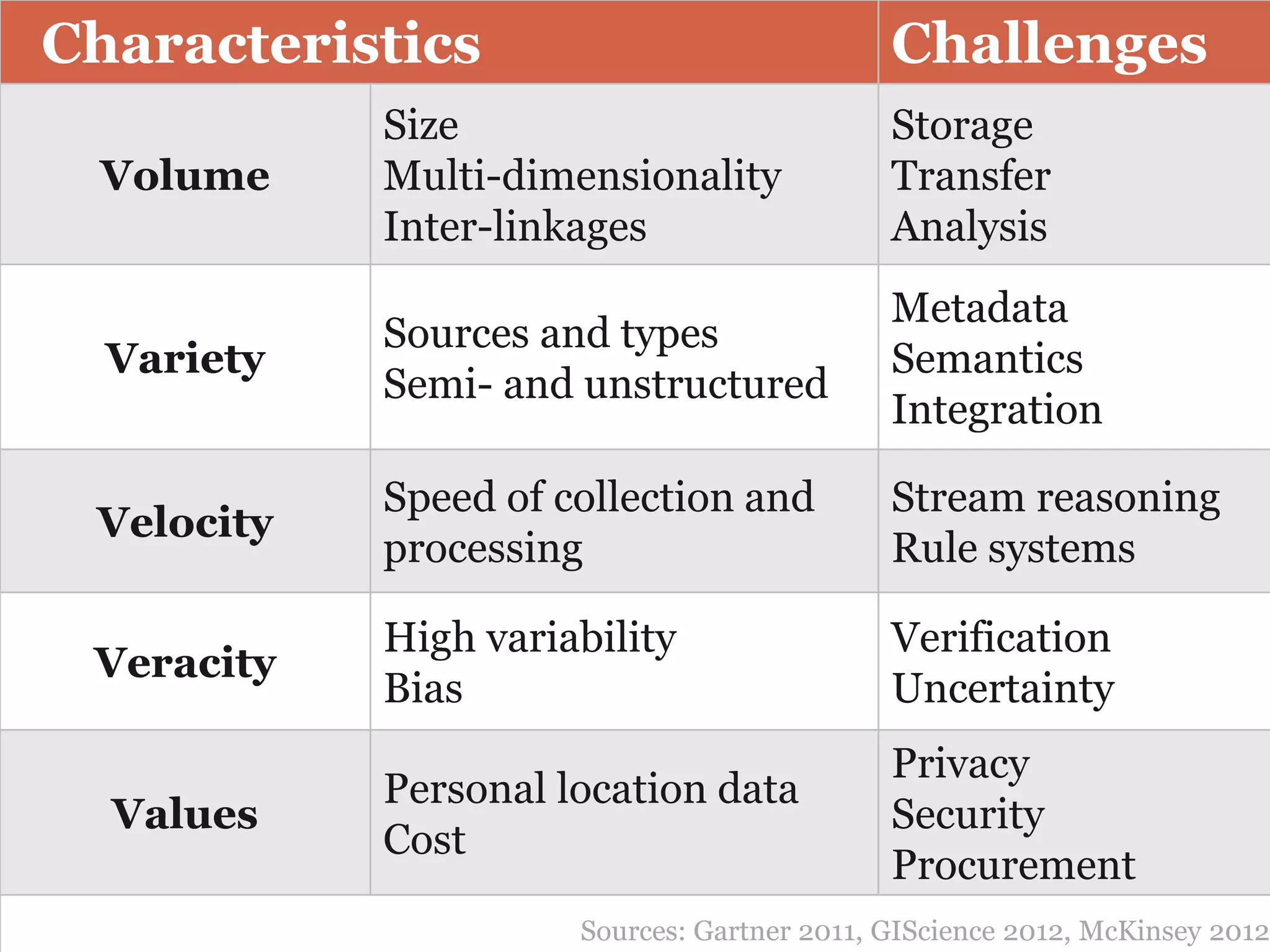
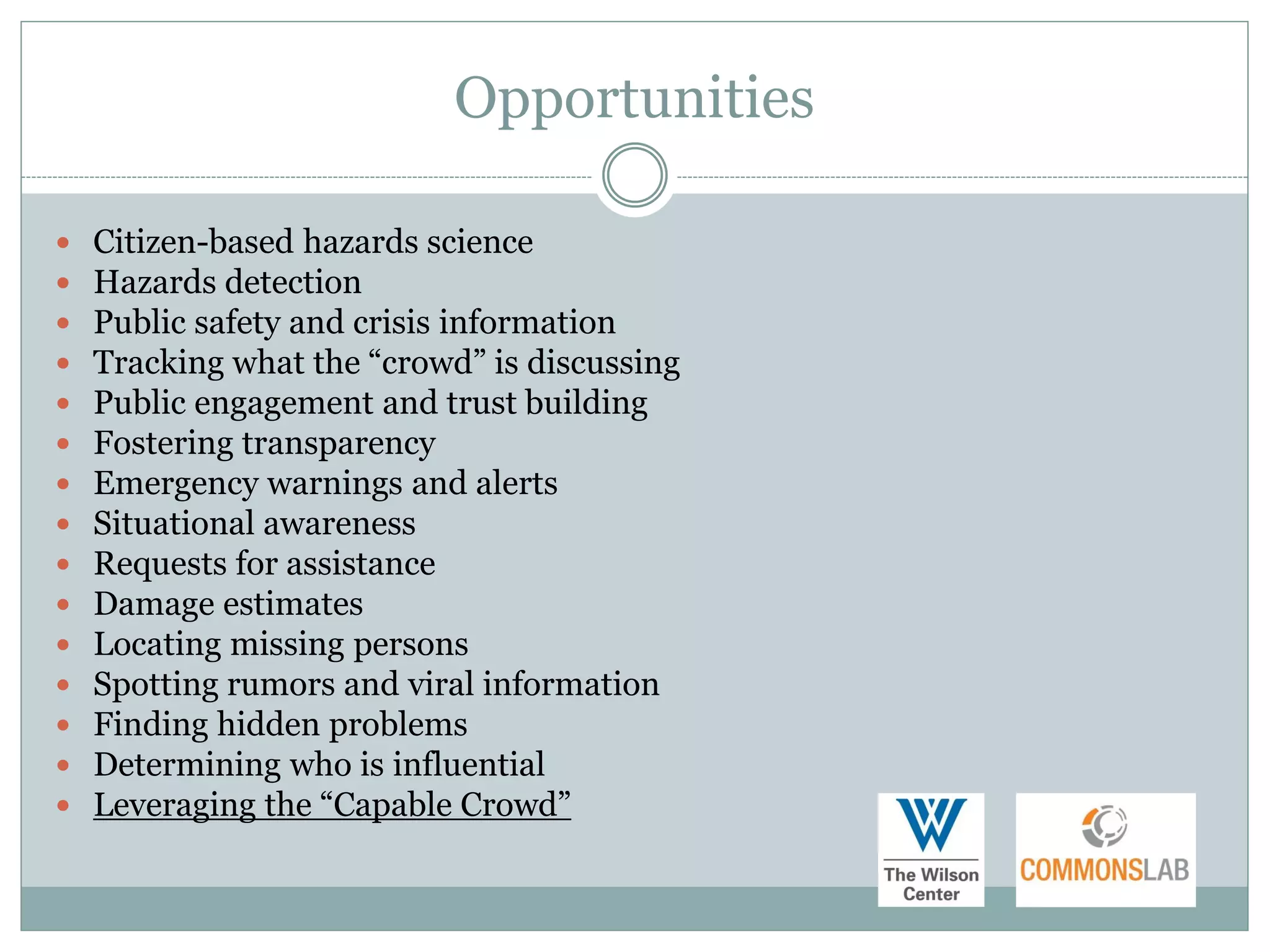
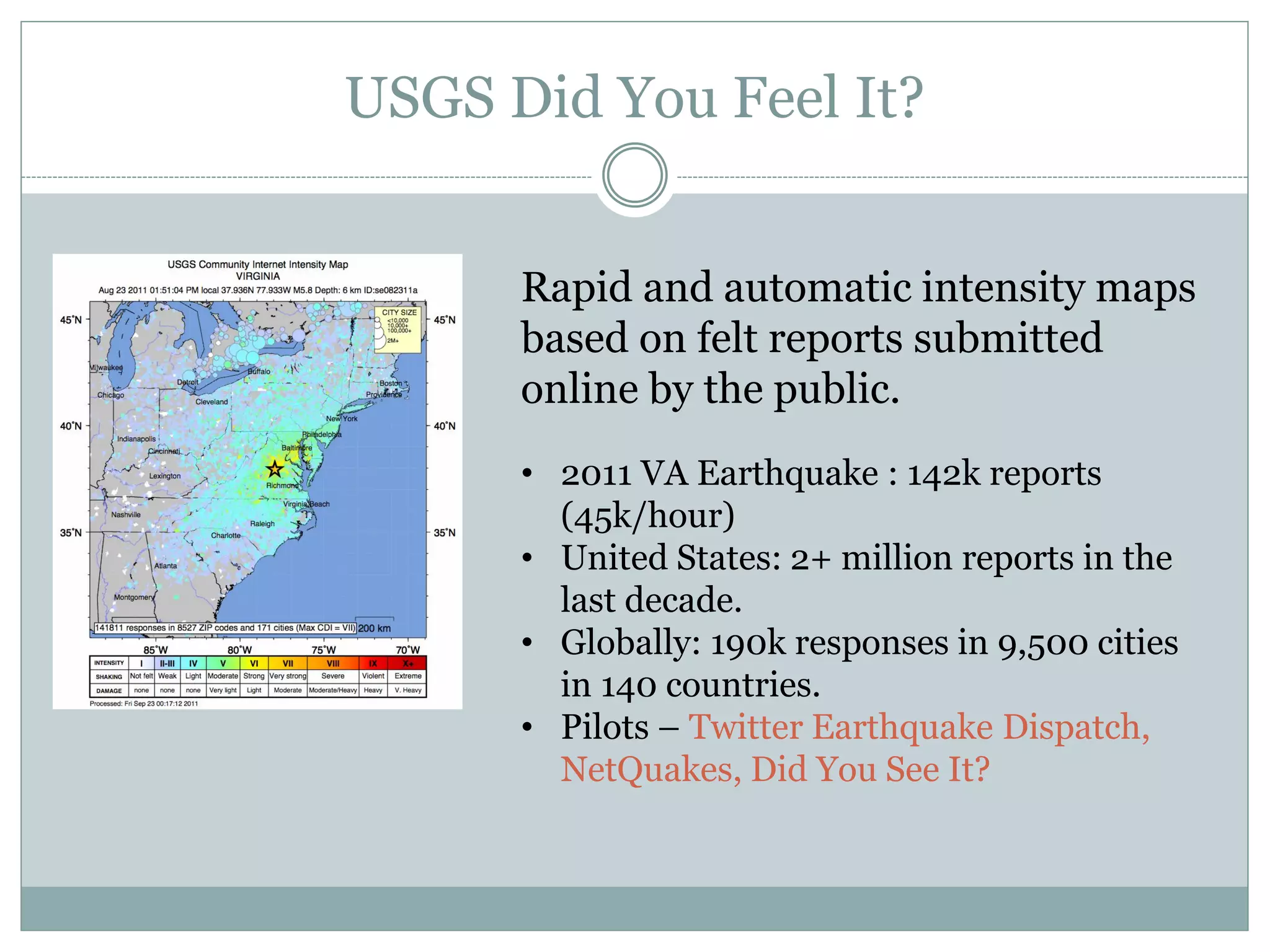
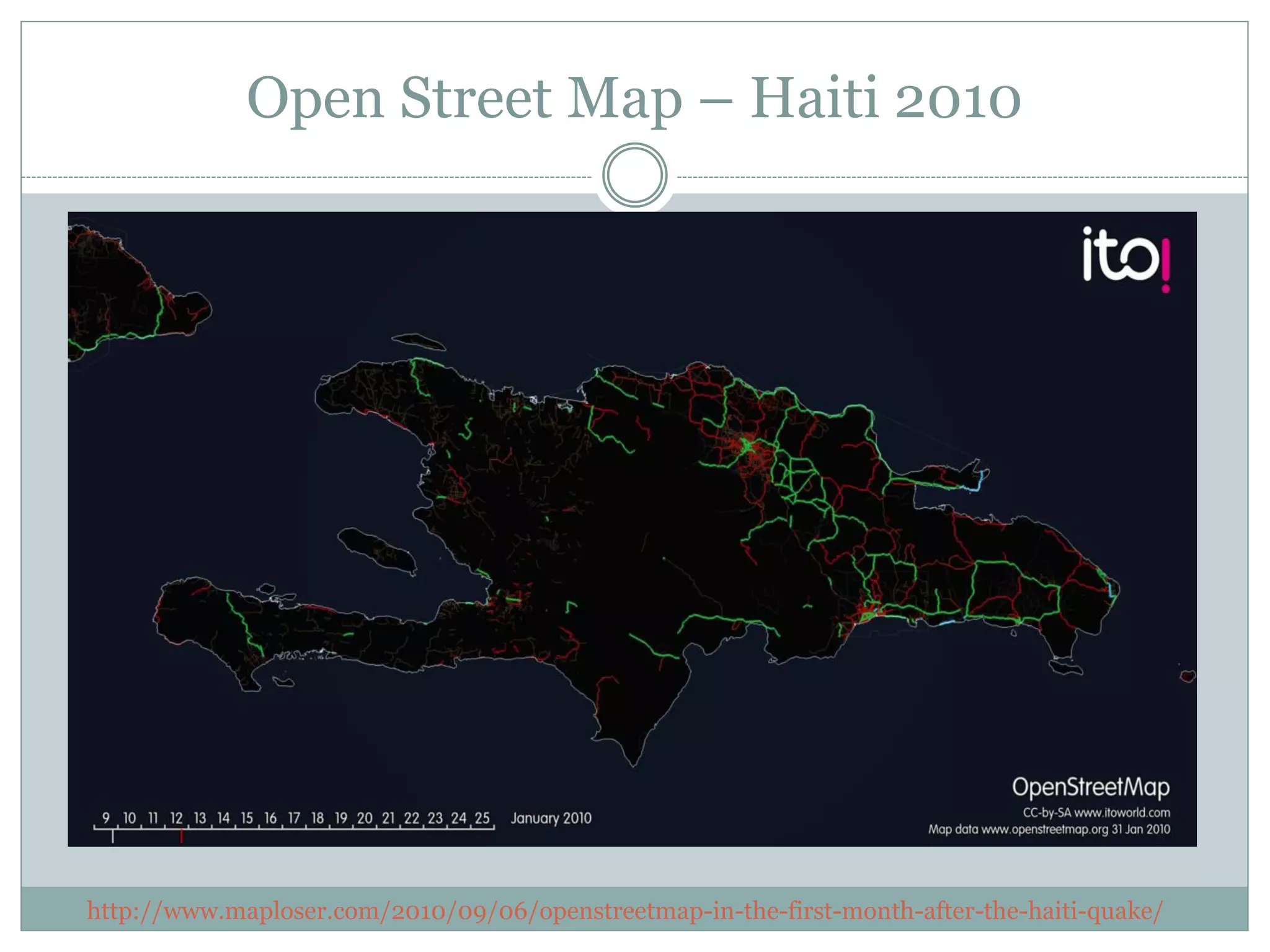
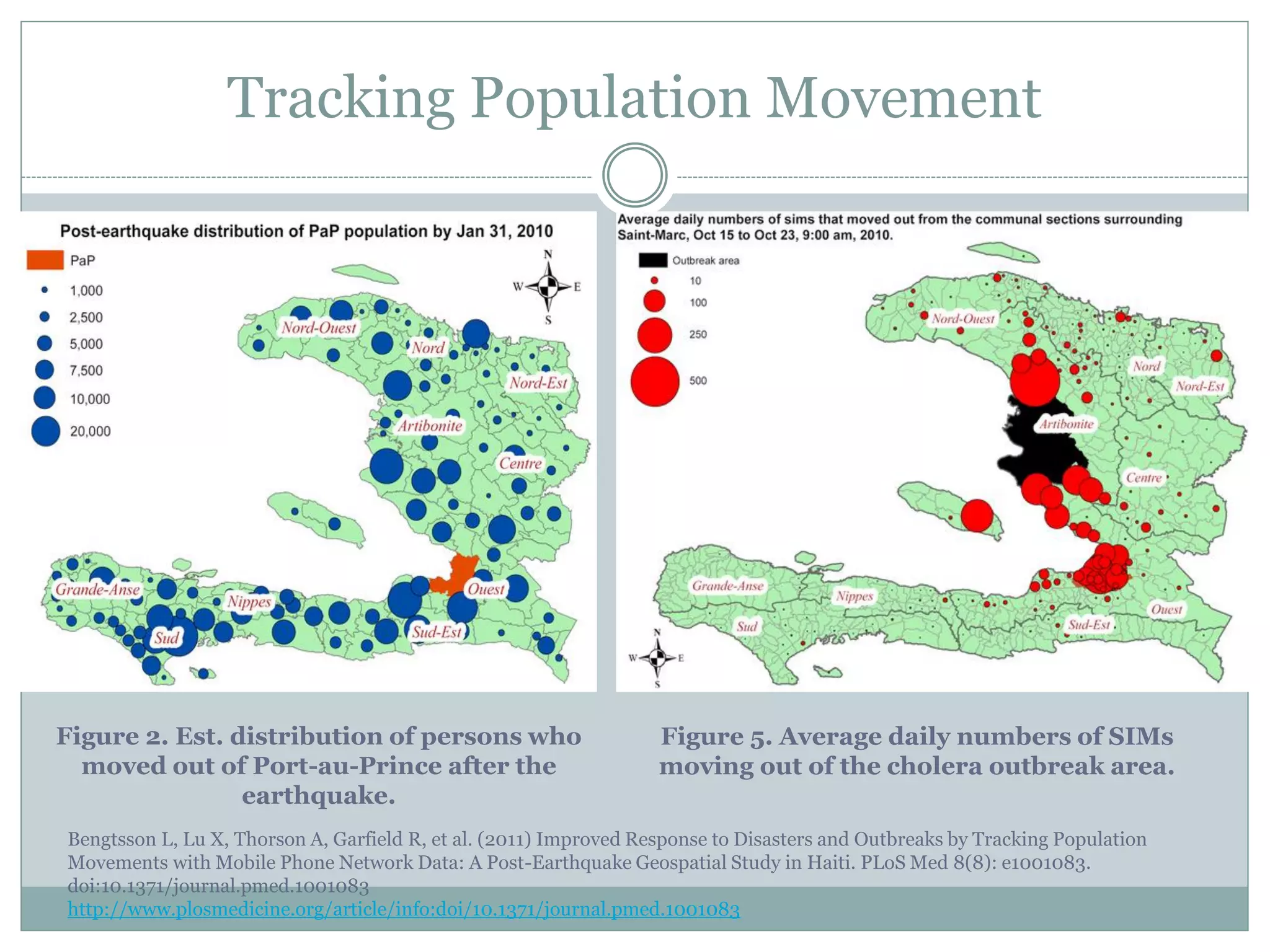
This document outlines opportunities and challenges in crisis informatics, which is an integrated approach to the technical, social, and informational aspects of crises. It begins with definitions of key terms like crisis informatics and crowdsourcing. It then discusses types of social media and ways crowdsourcing is used during crises. Opportunities of crisis informatics include citizen-based hazard science, situational awareness, and damage estimates. Challenges include ensuring data quality, integrating crowdsourced and authoritative data, and addressing legal/policy issues. The document concludes by identifying priority research challenges such as developing validation methods and best practices for data integration.