Embed presentation
Downloaded 43 times

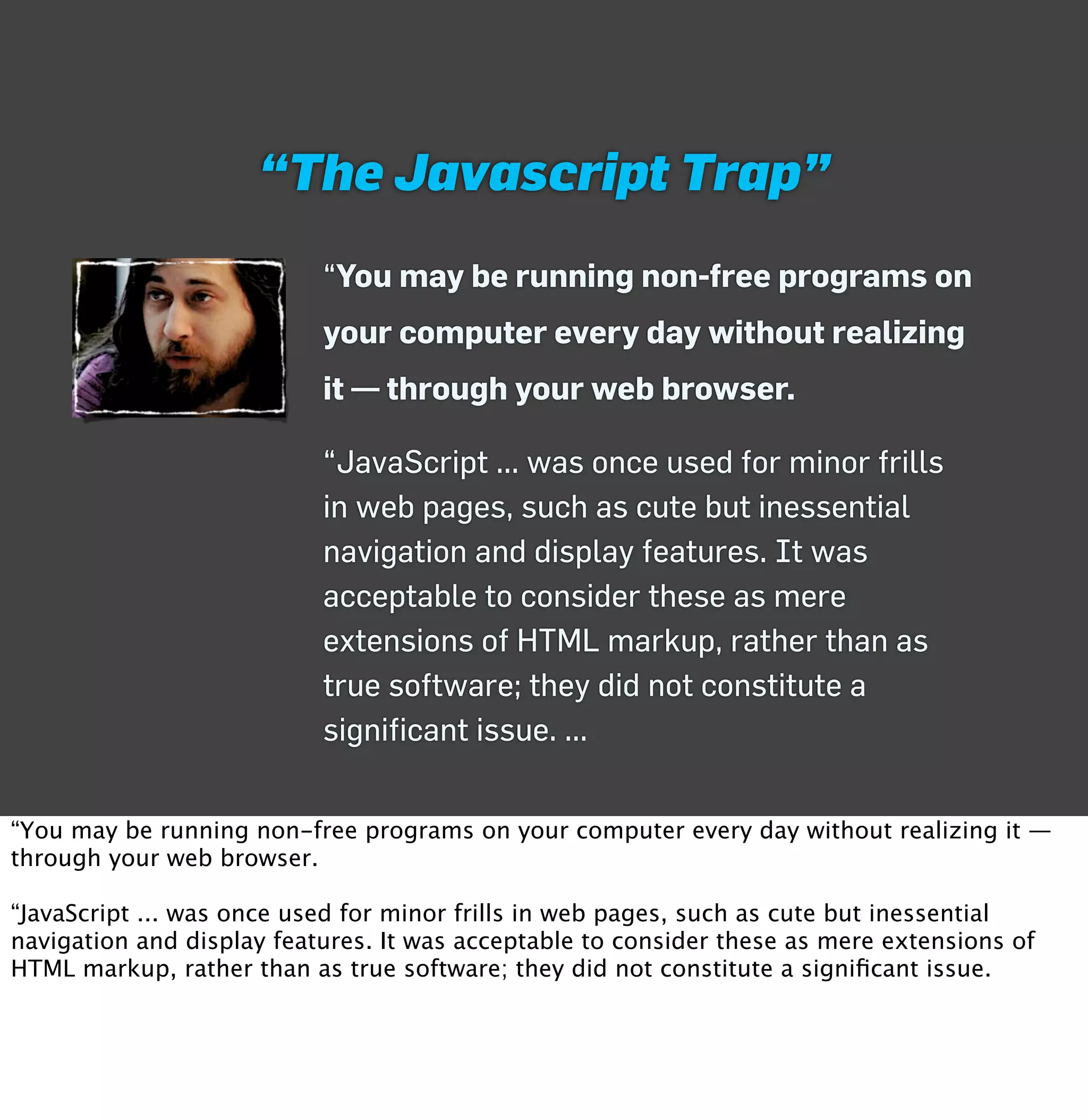
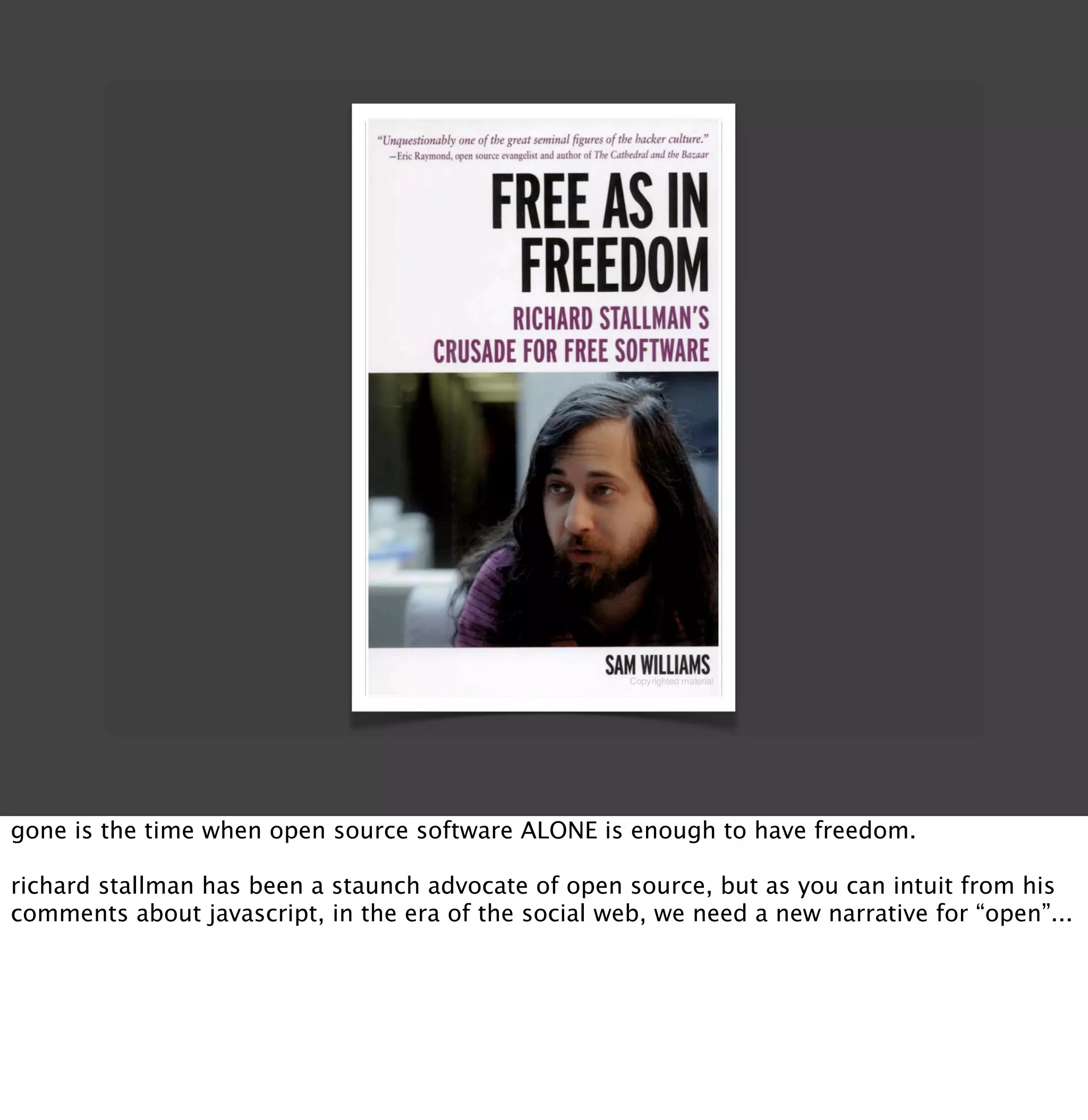
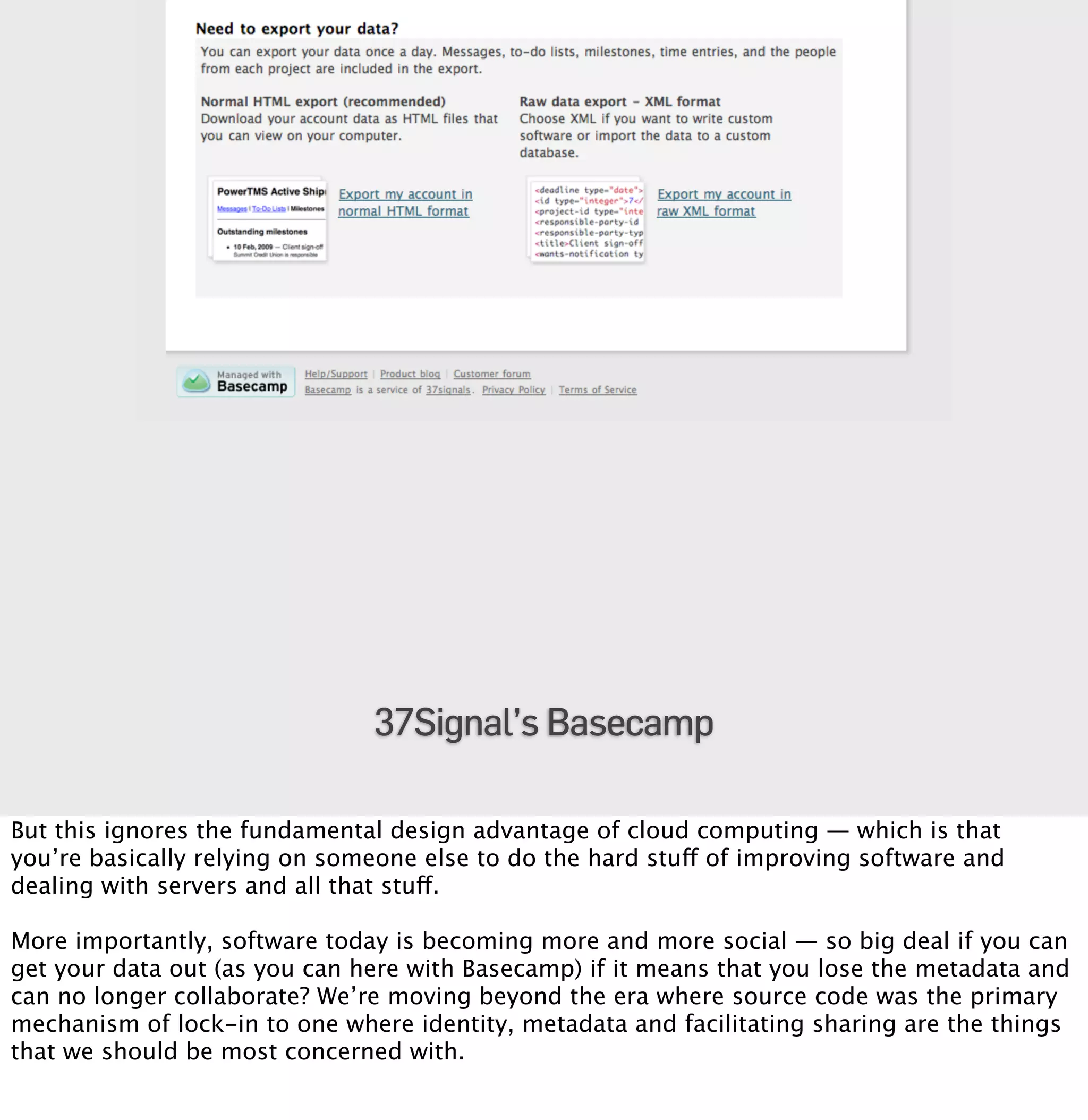
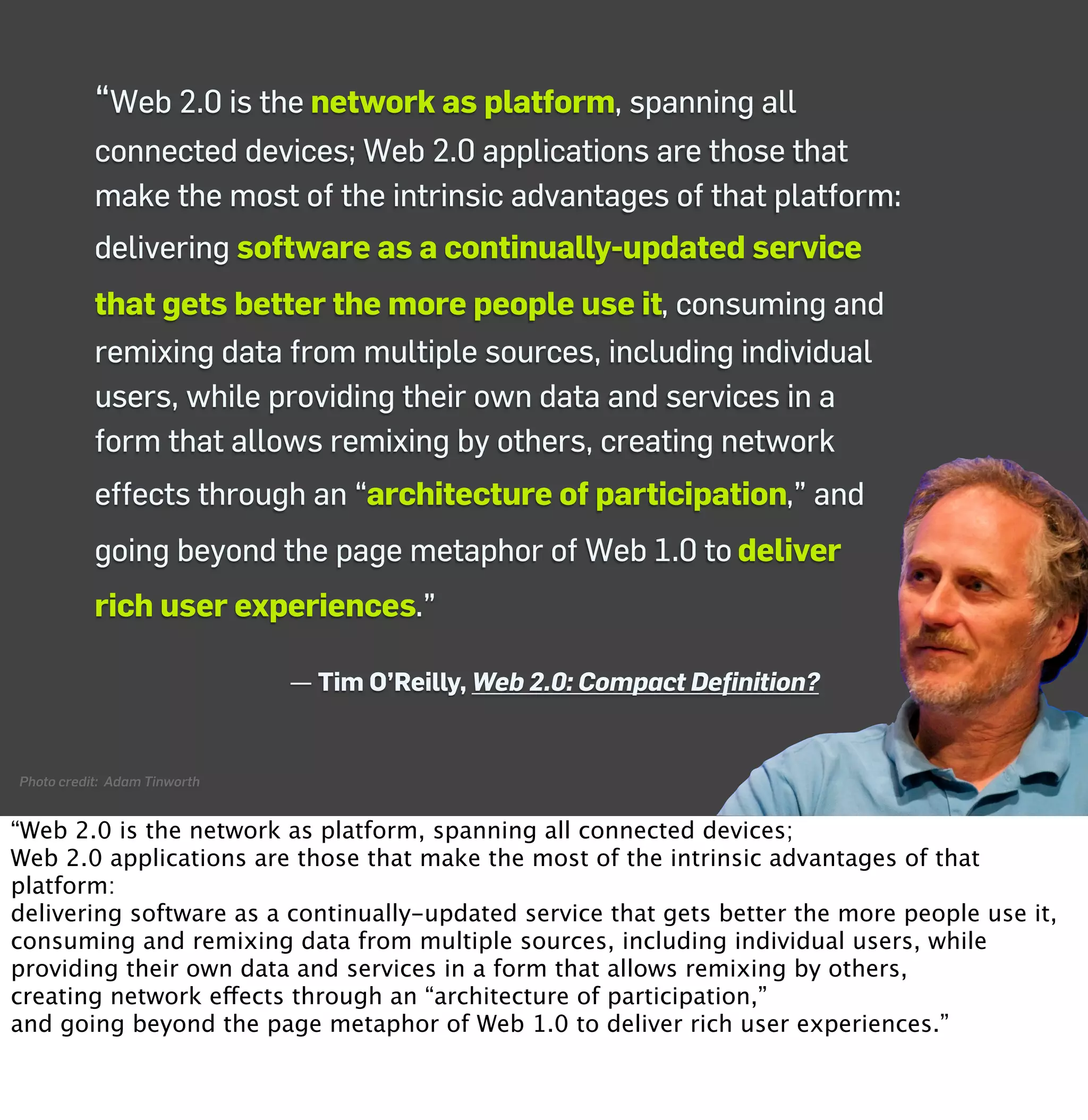
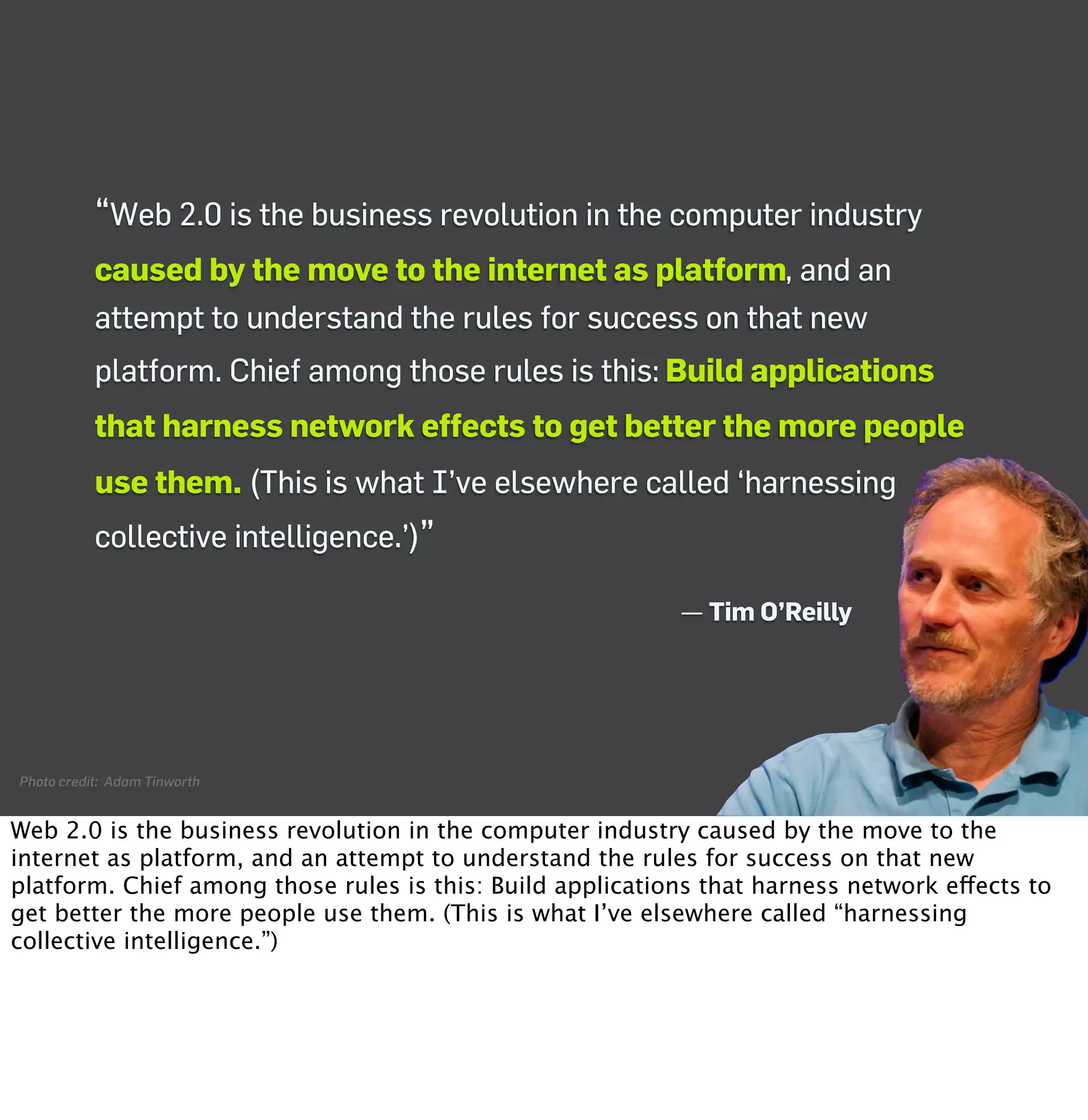
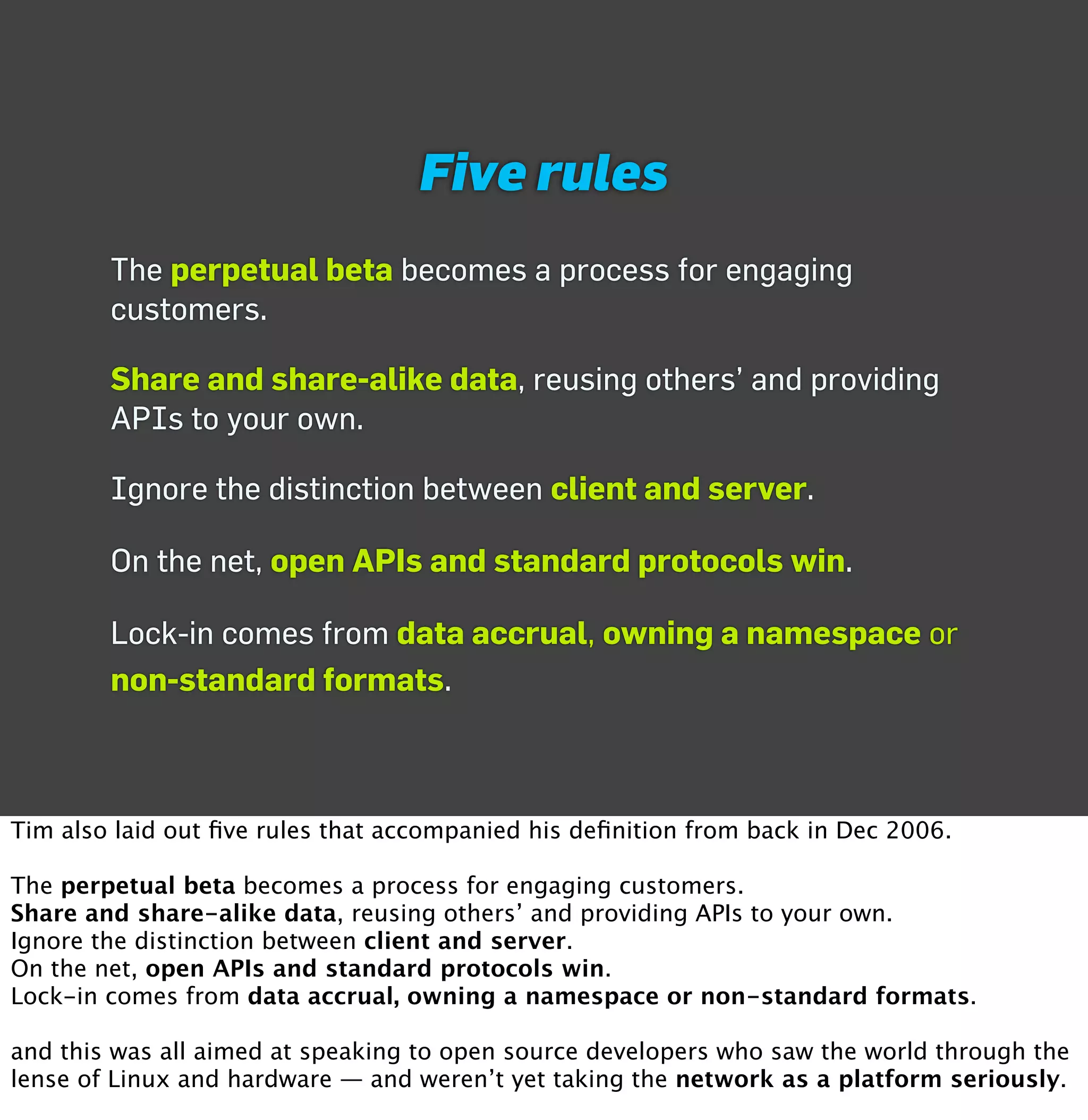

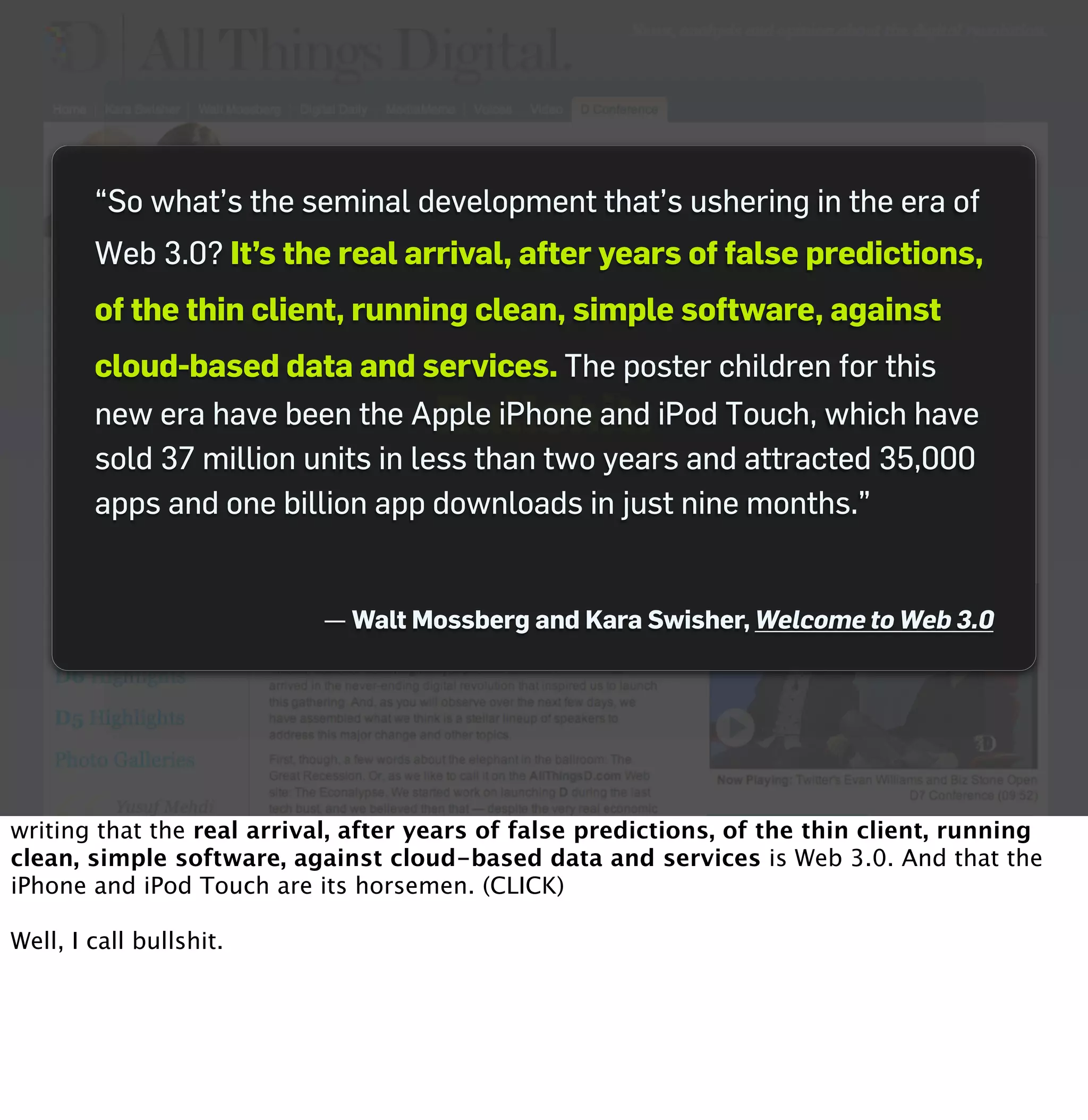
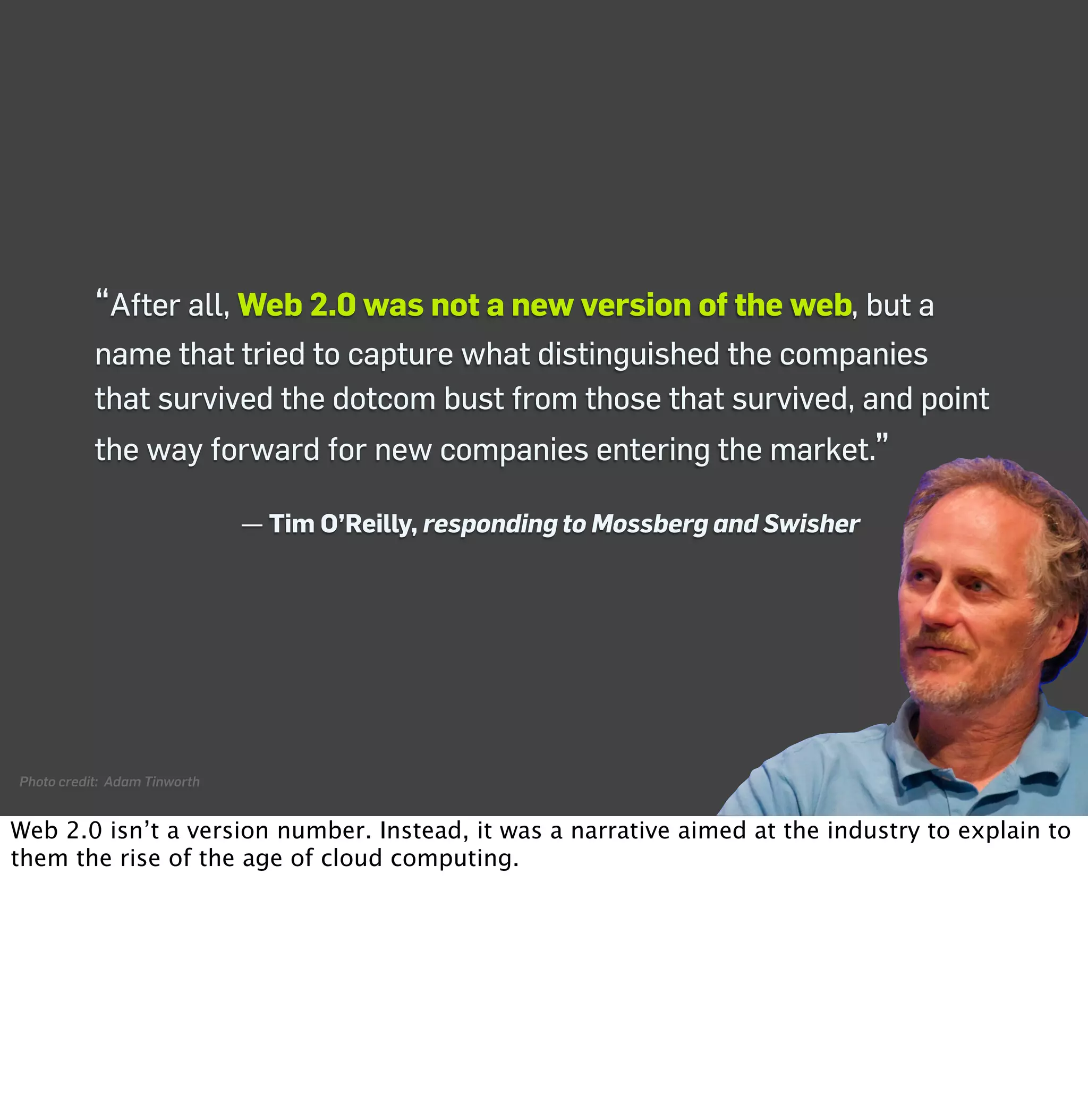
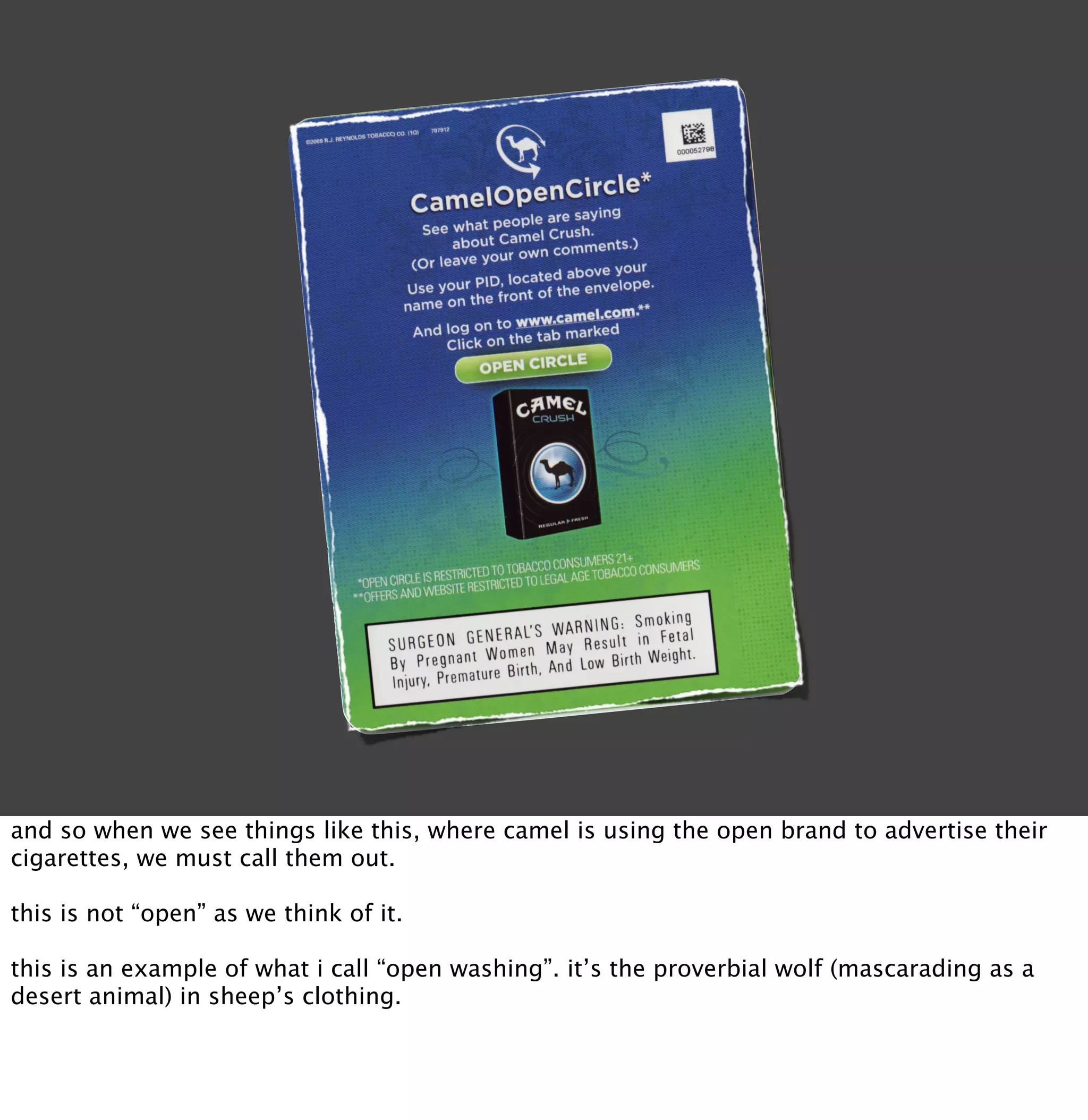

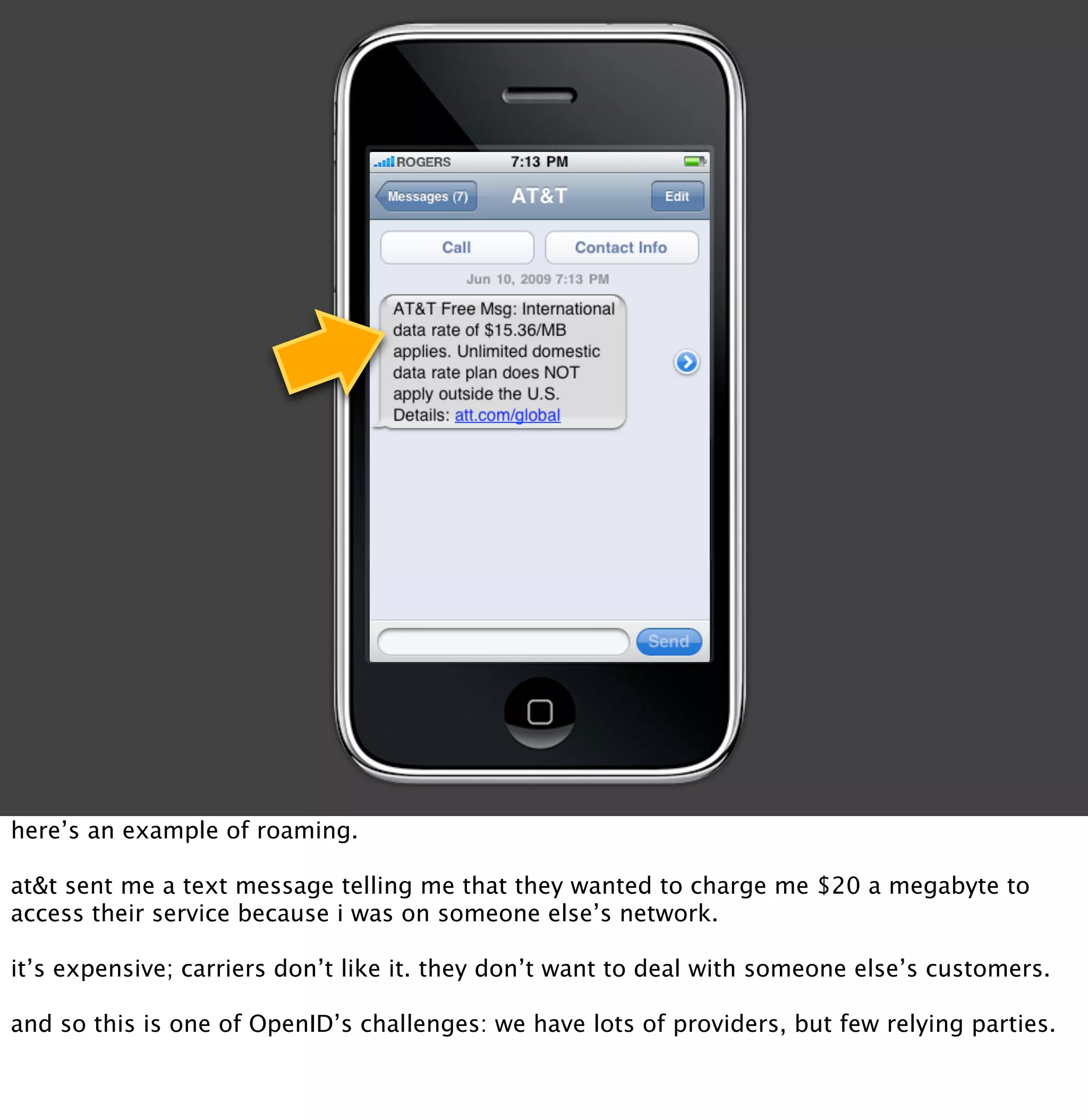
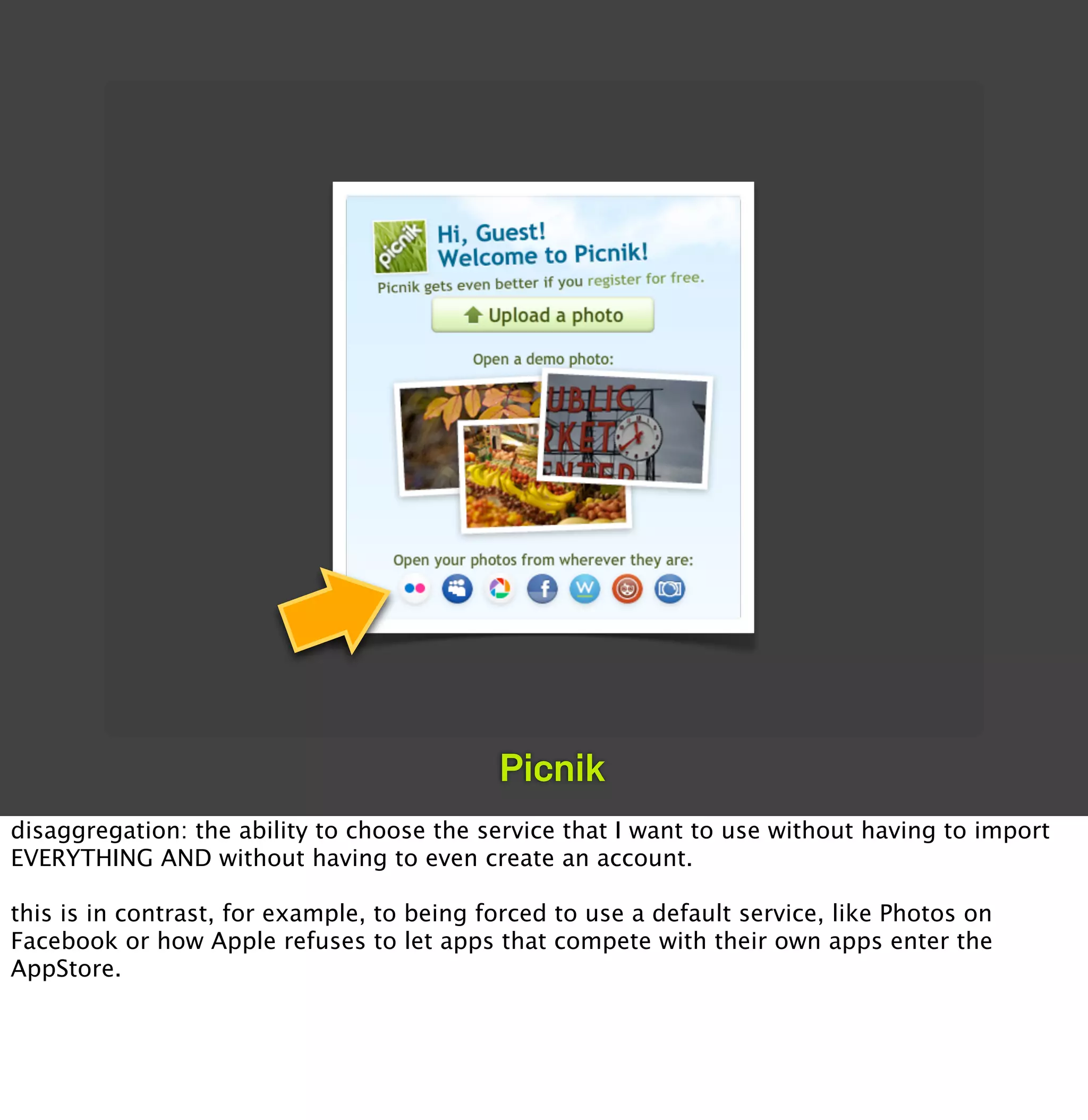
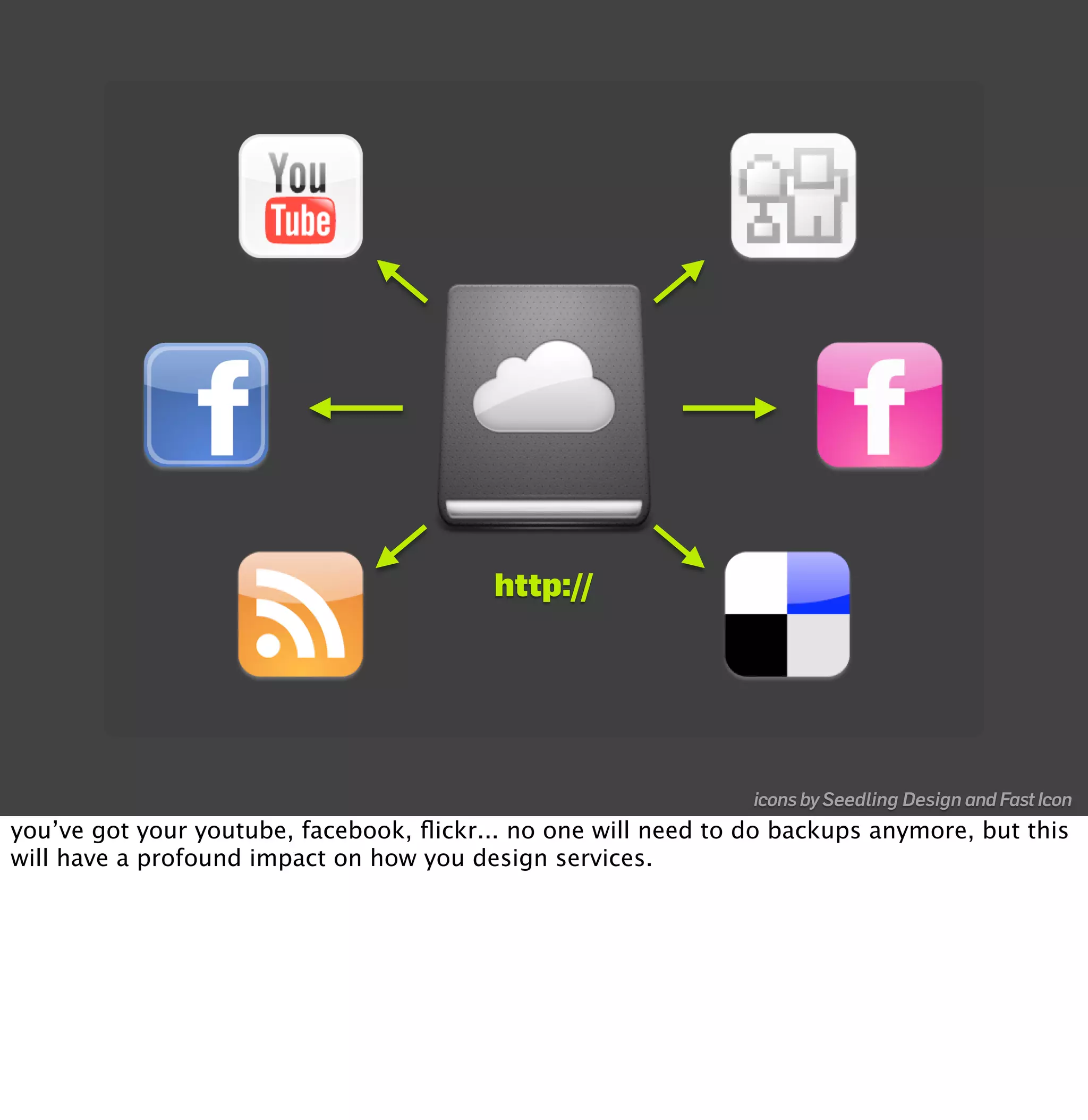
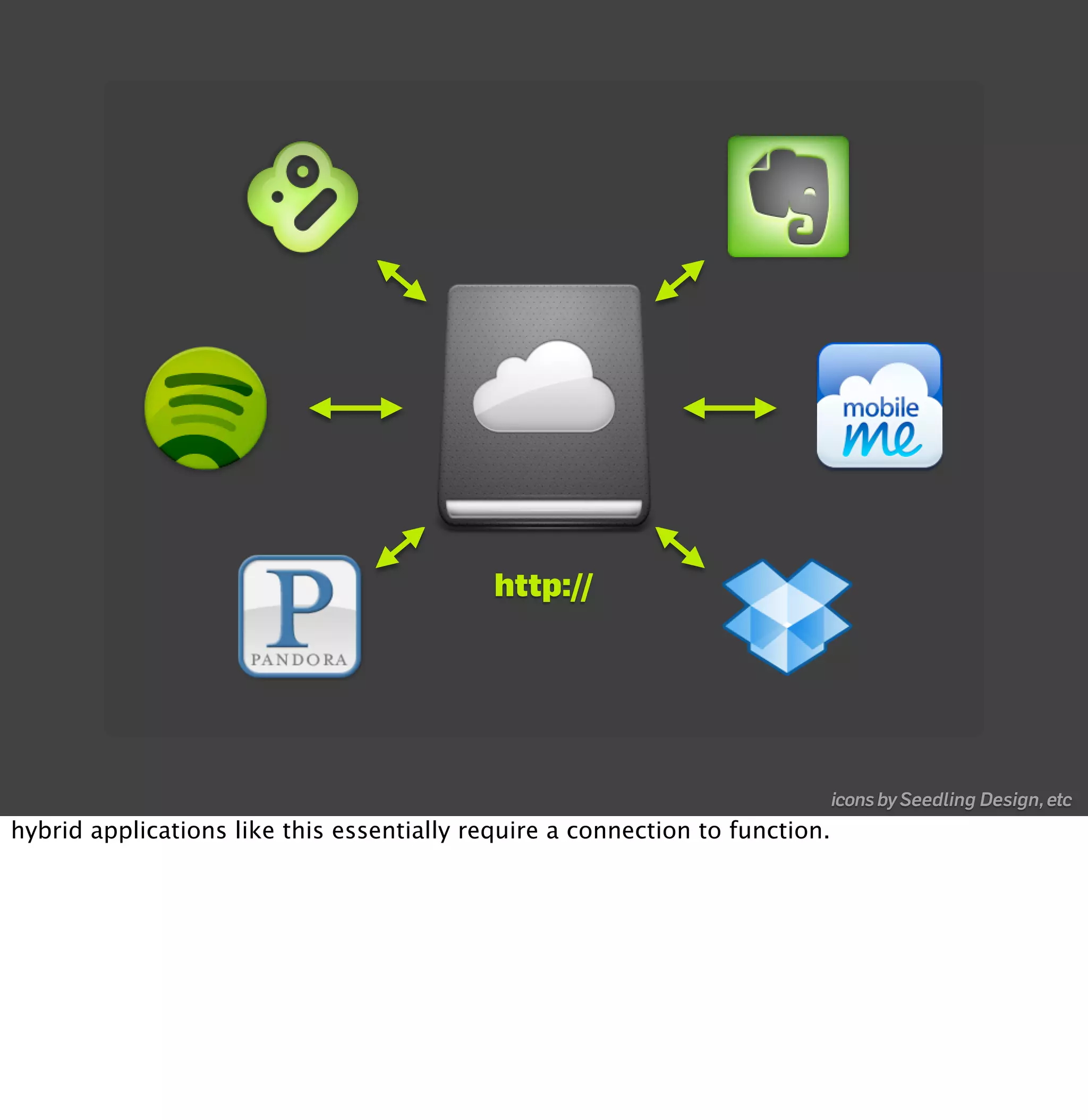
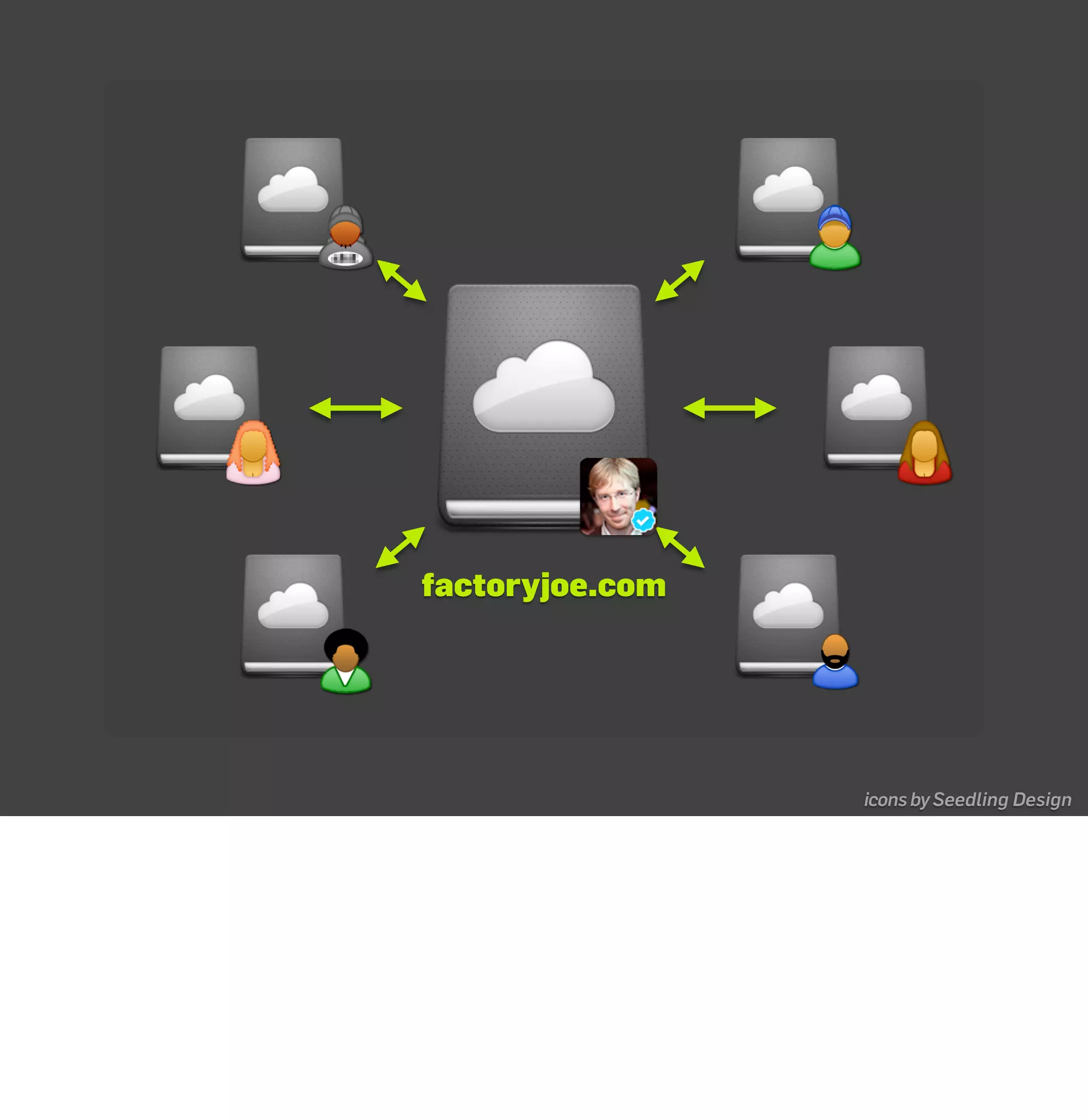
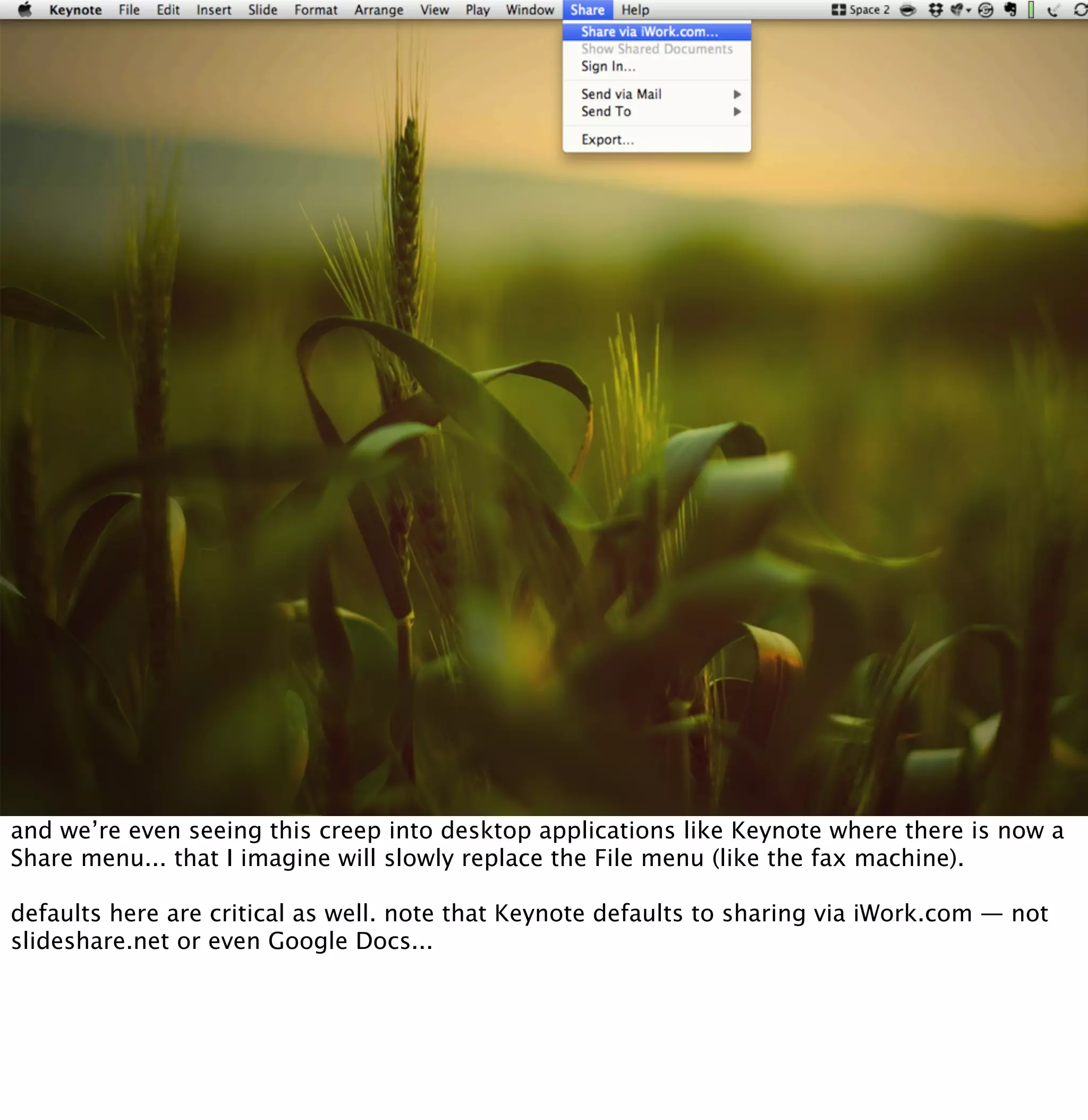
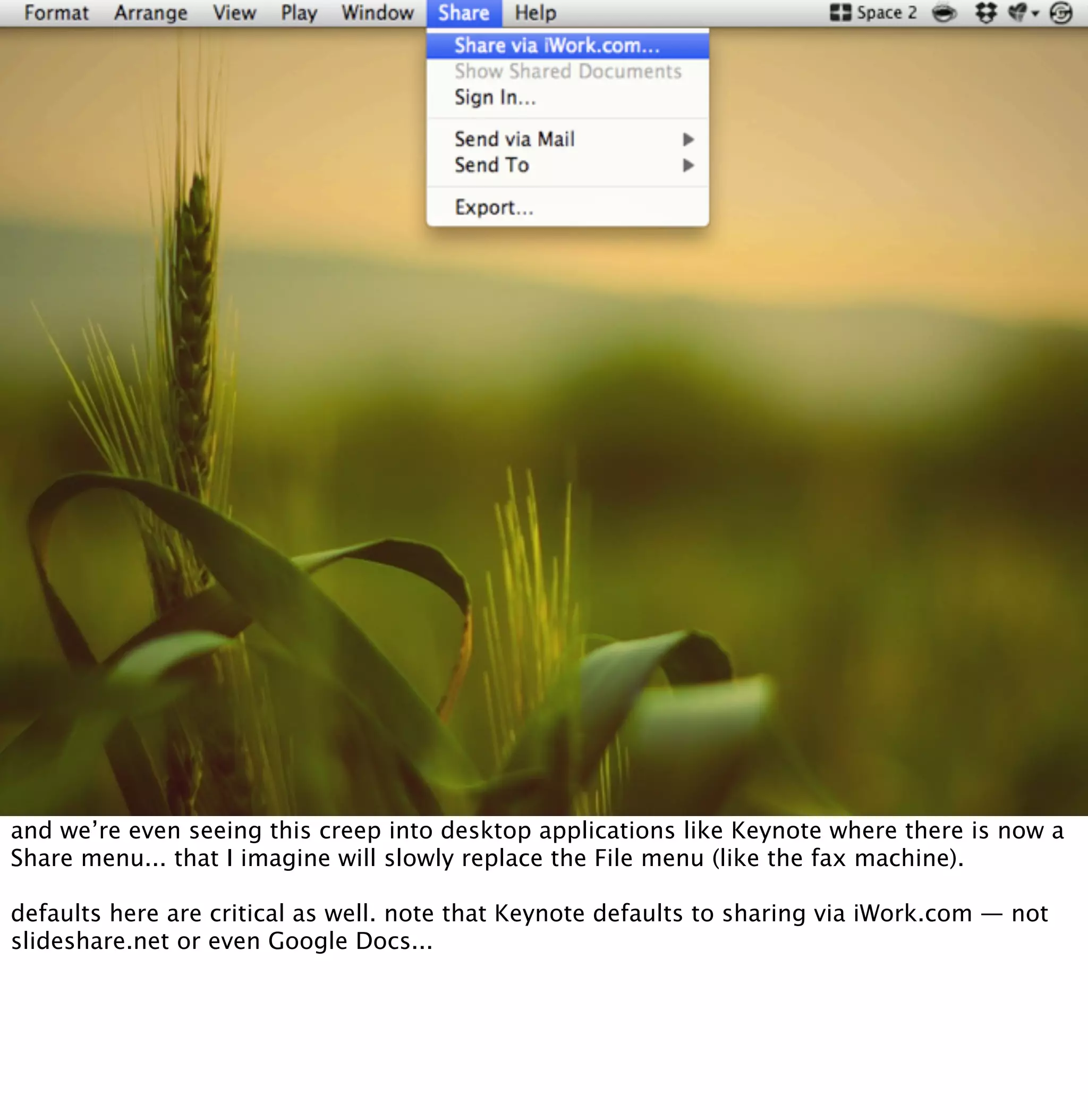





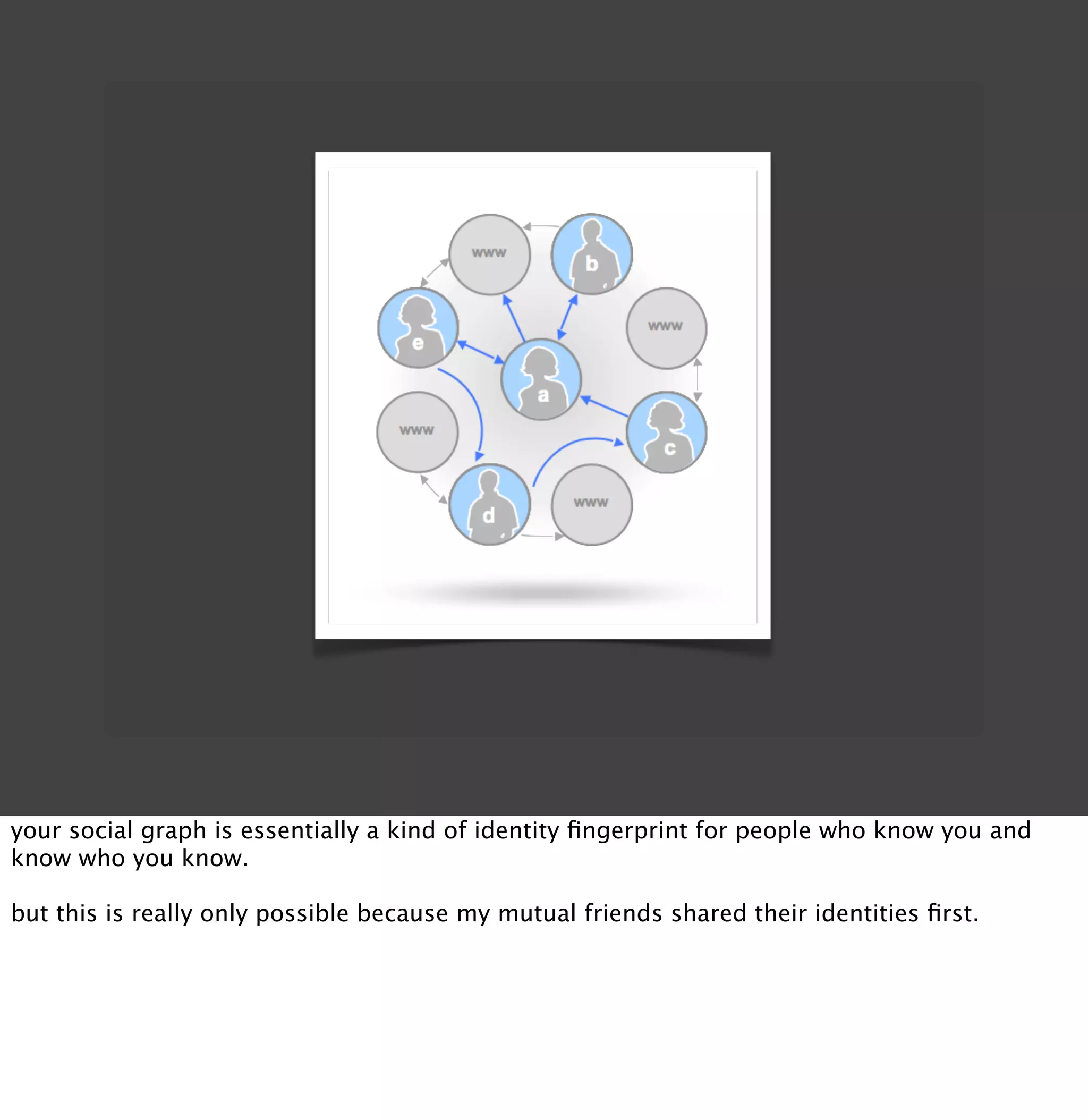
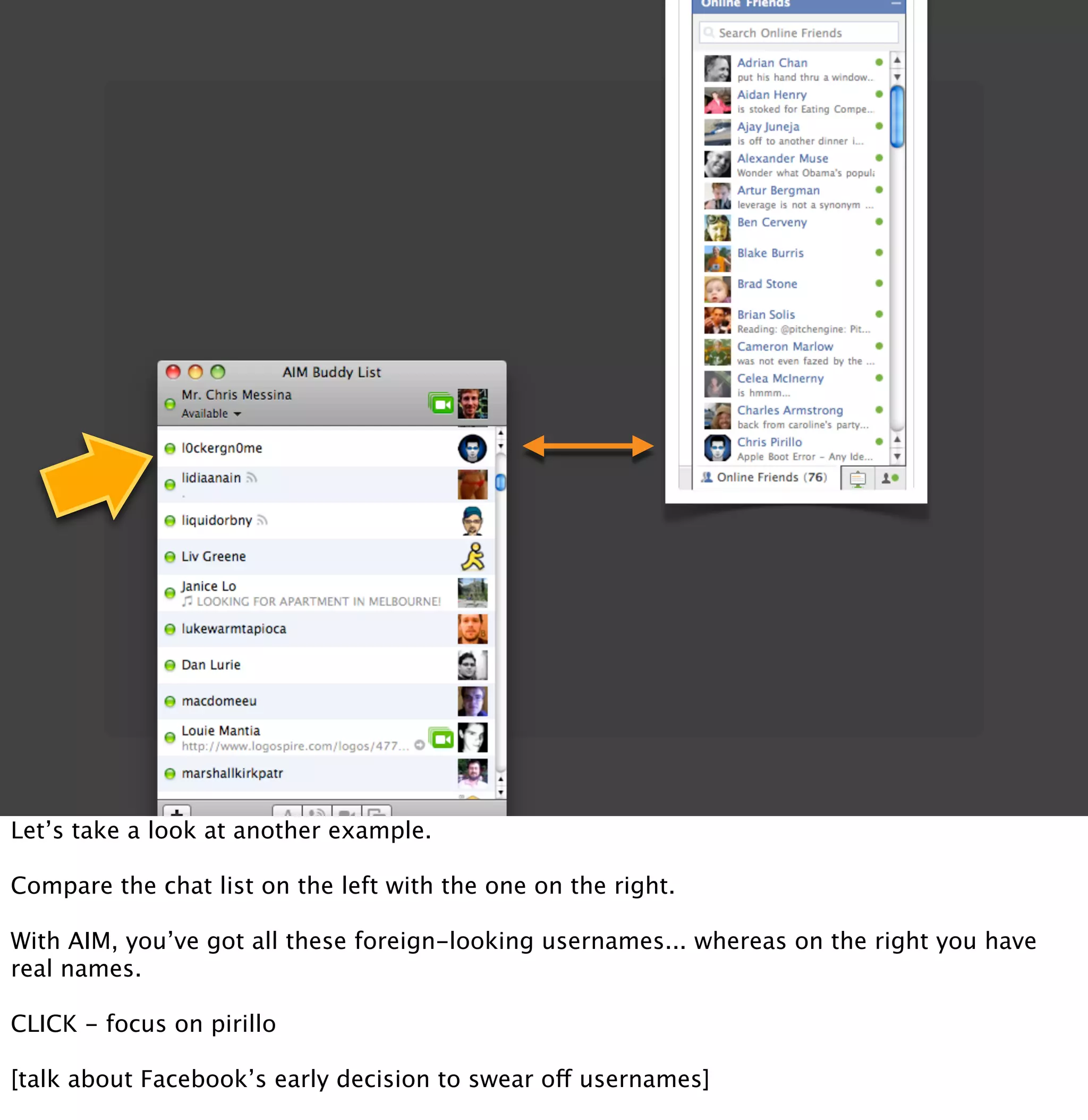
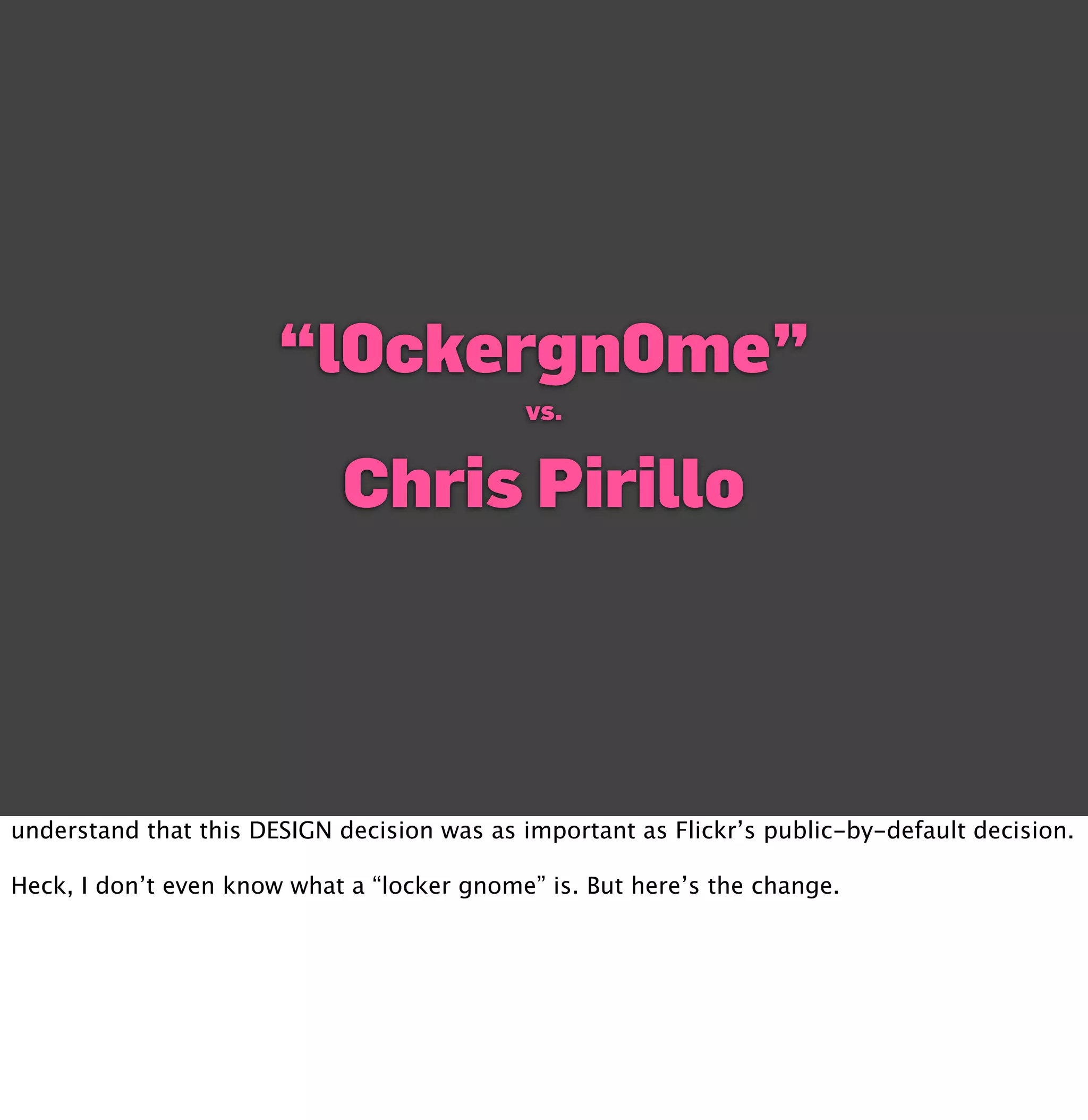
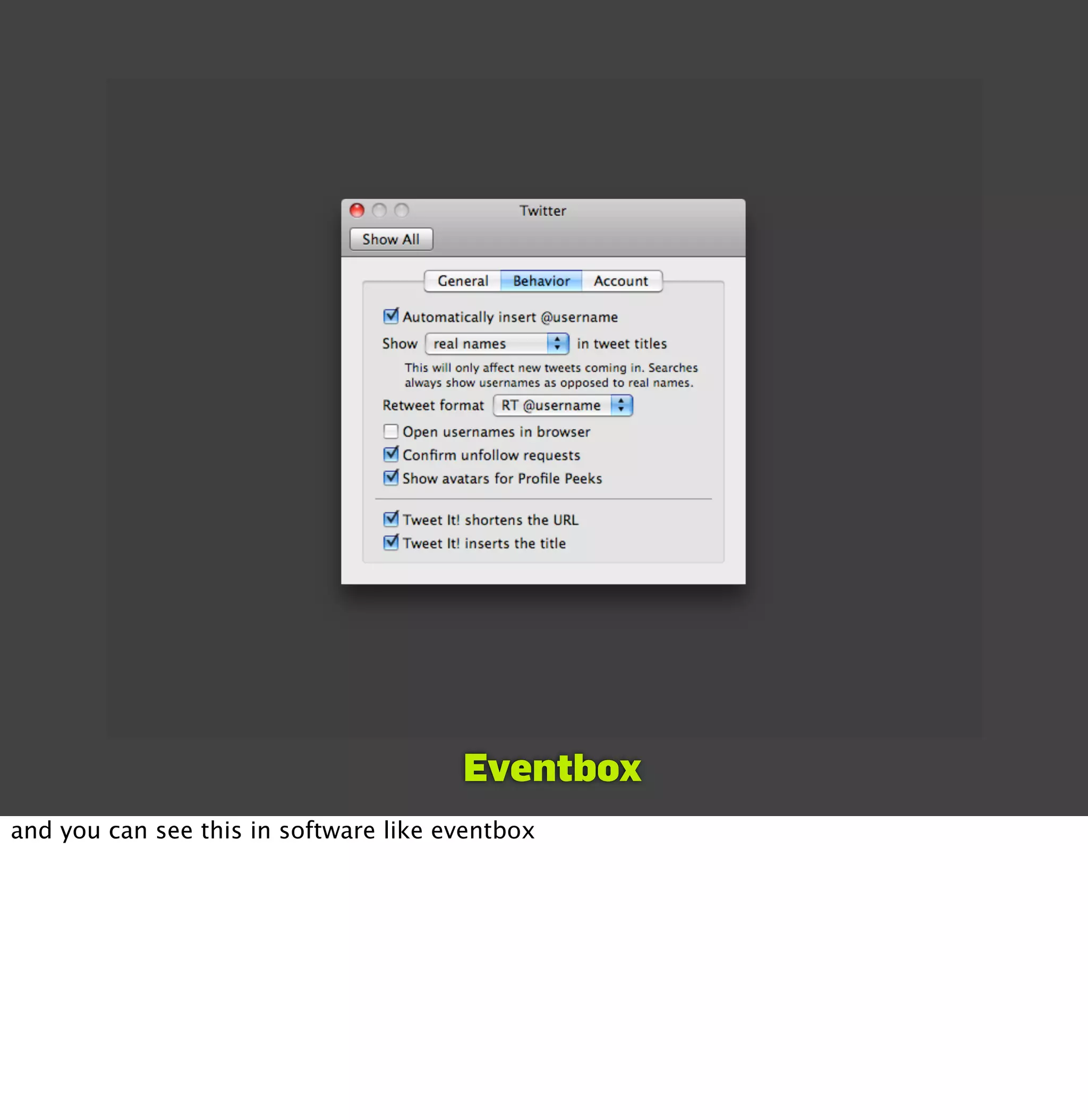
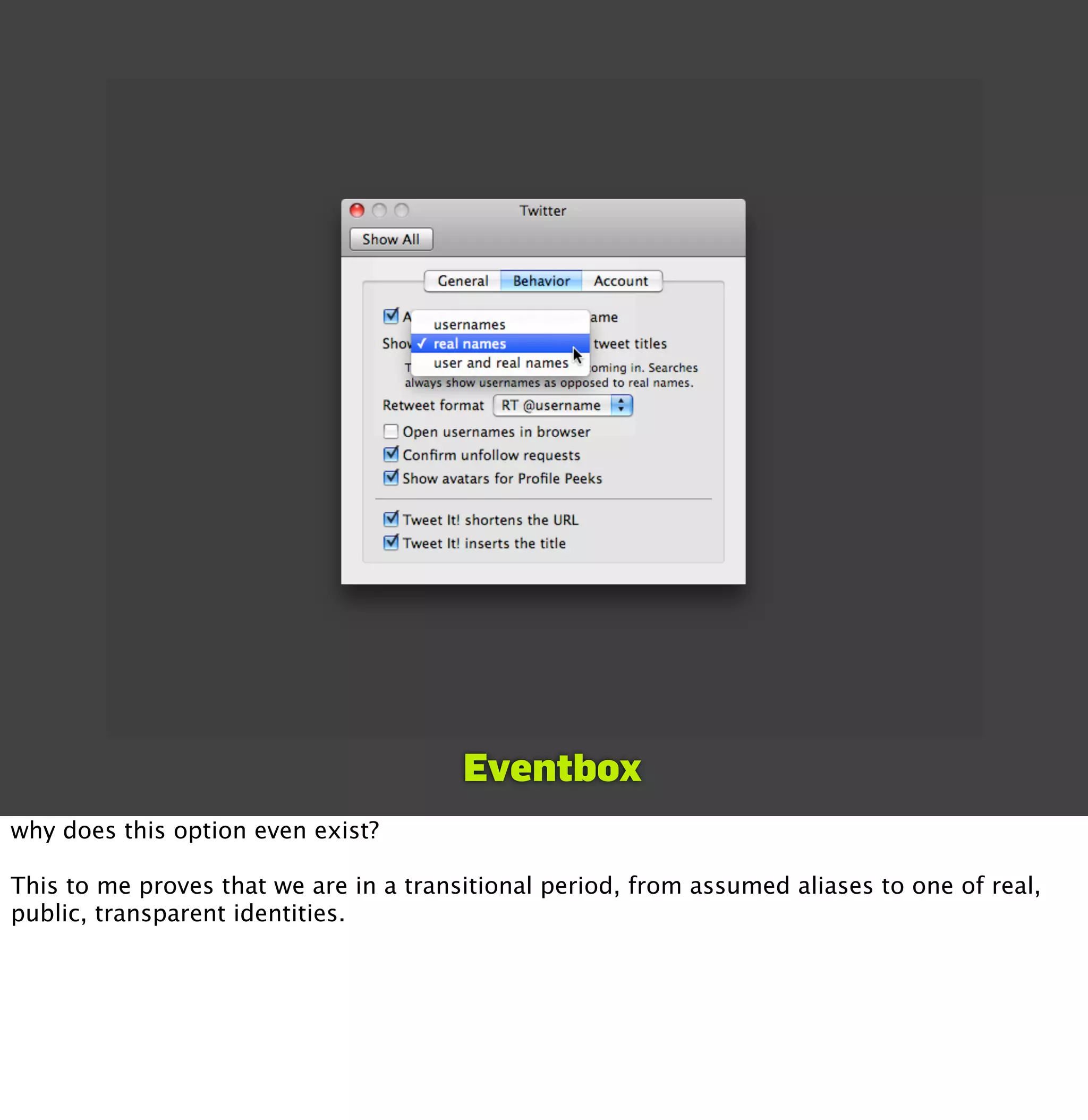
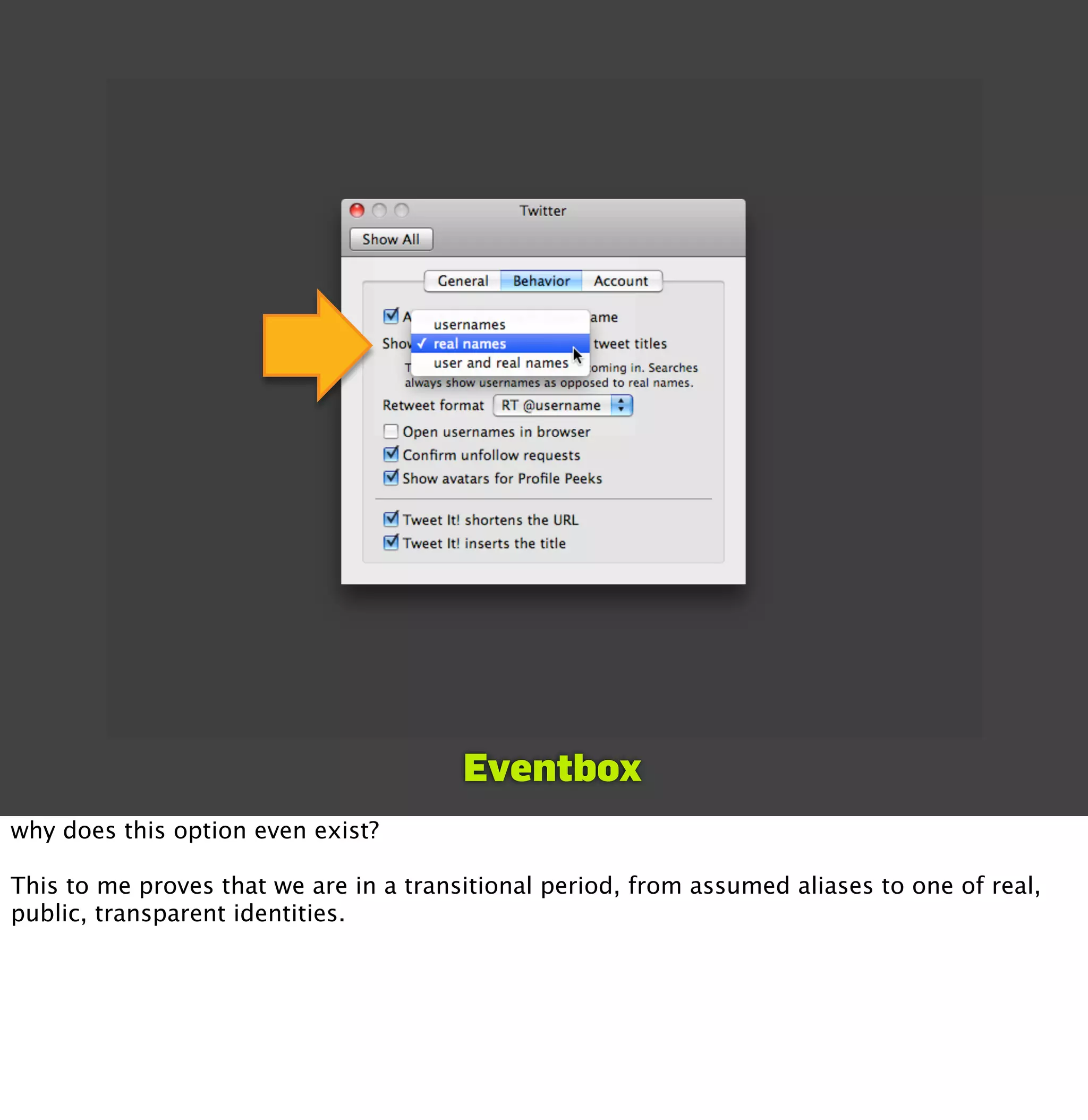
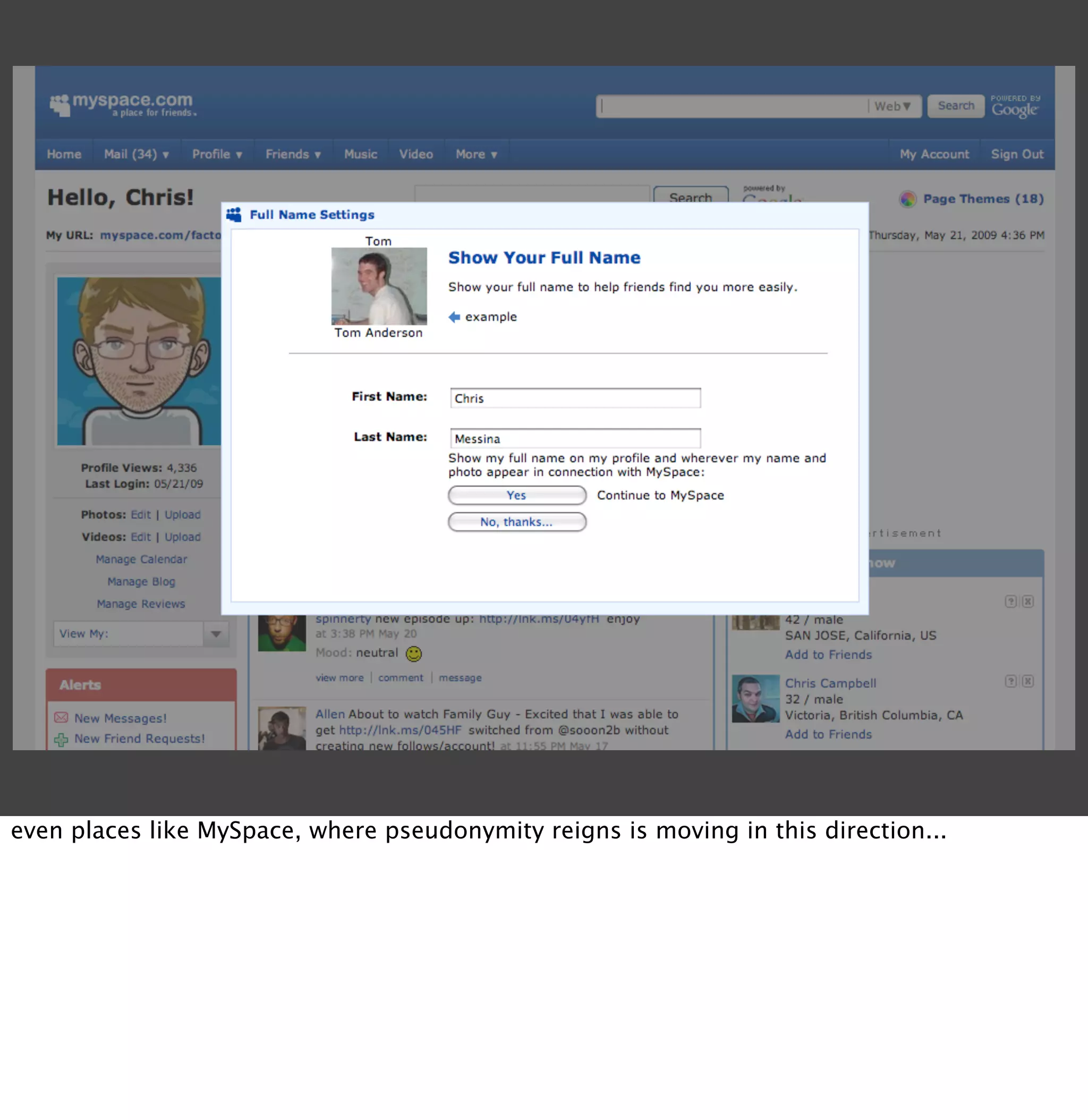
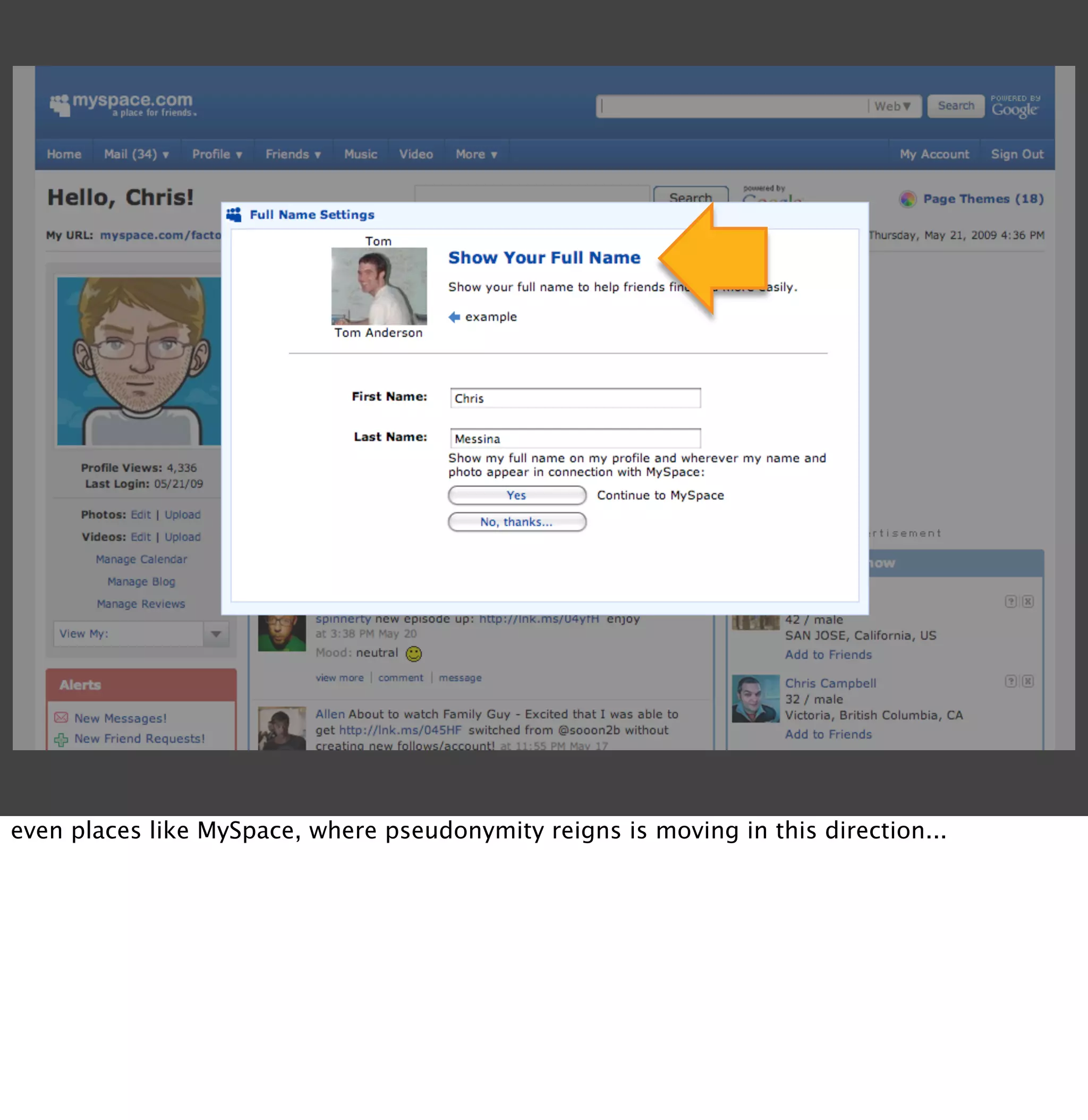
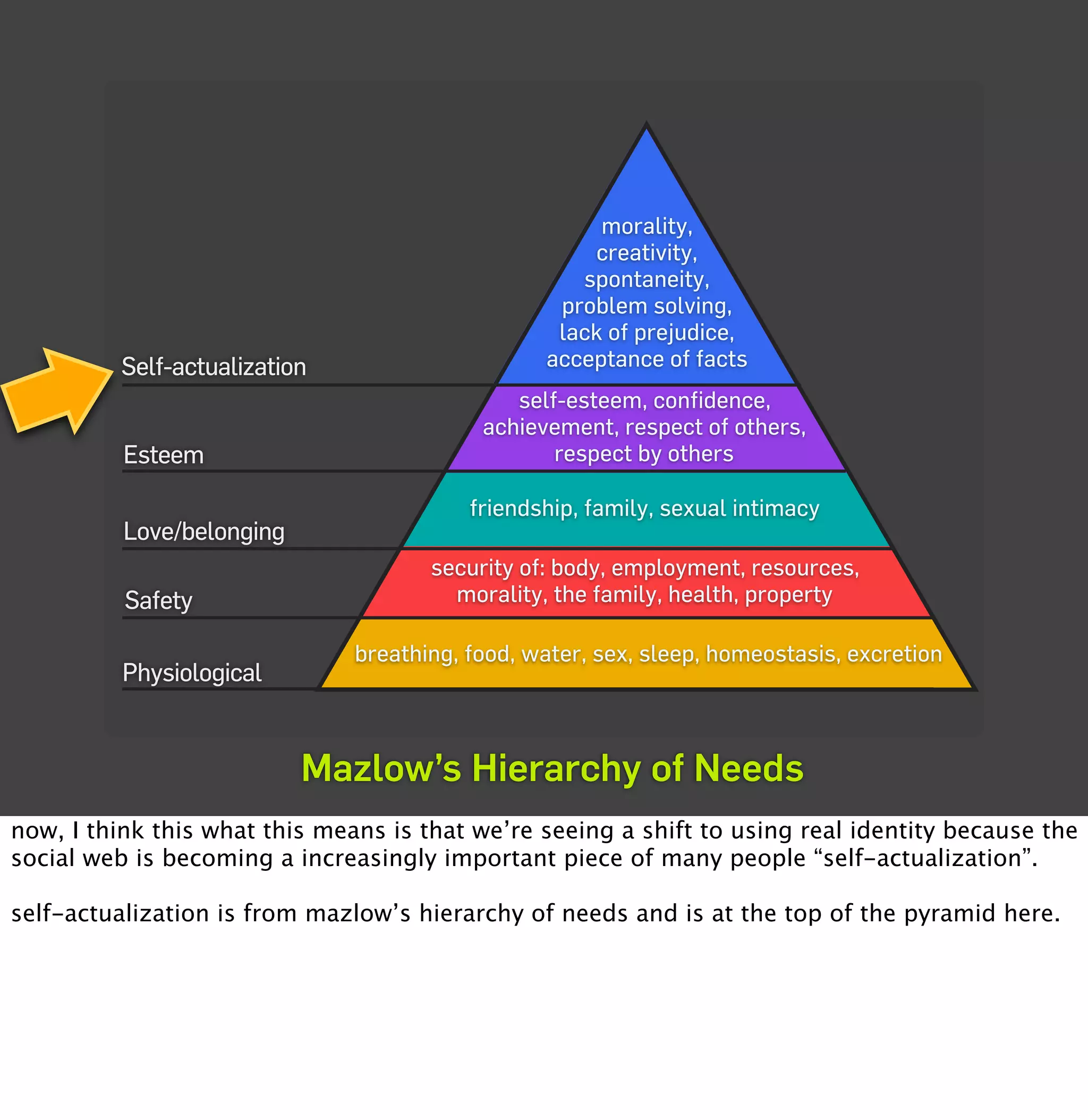
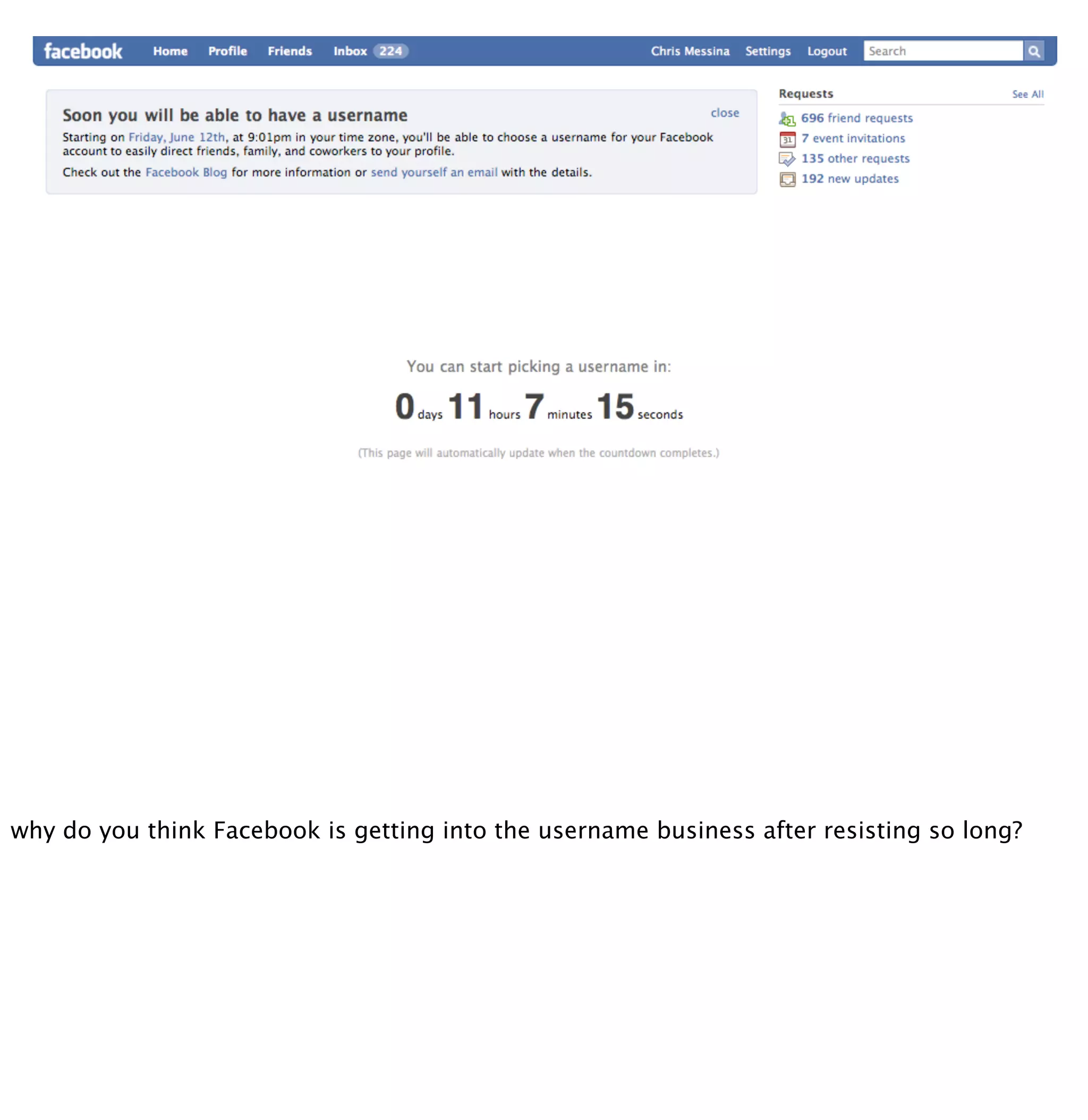
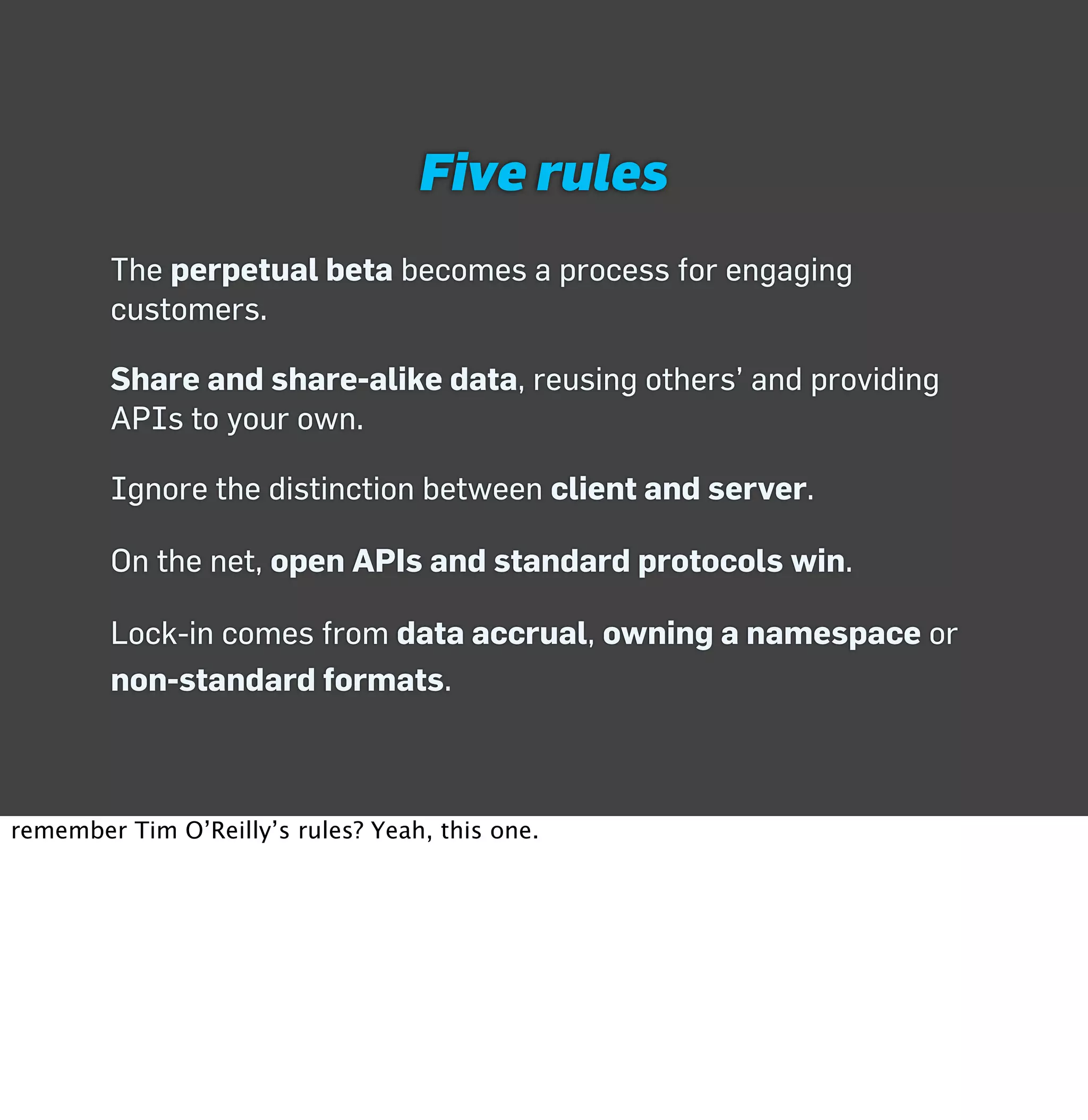
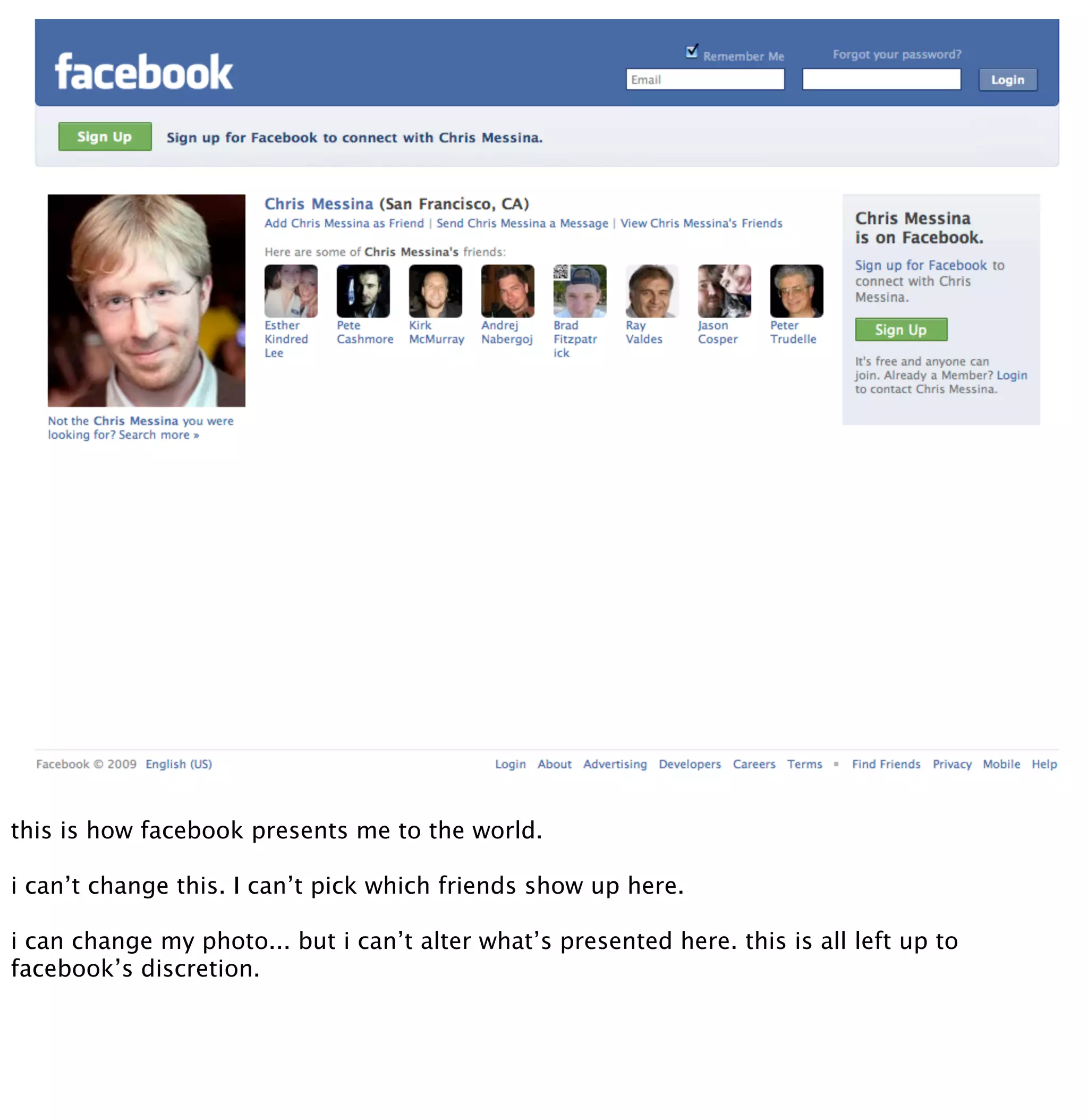
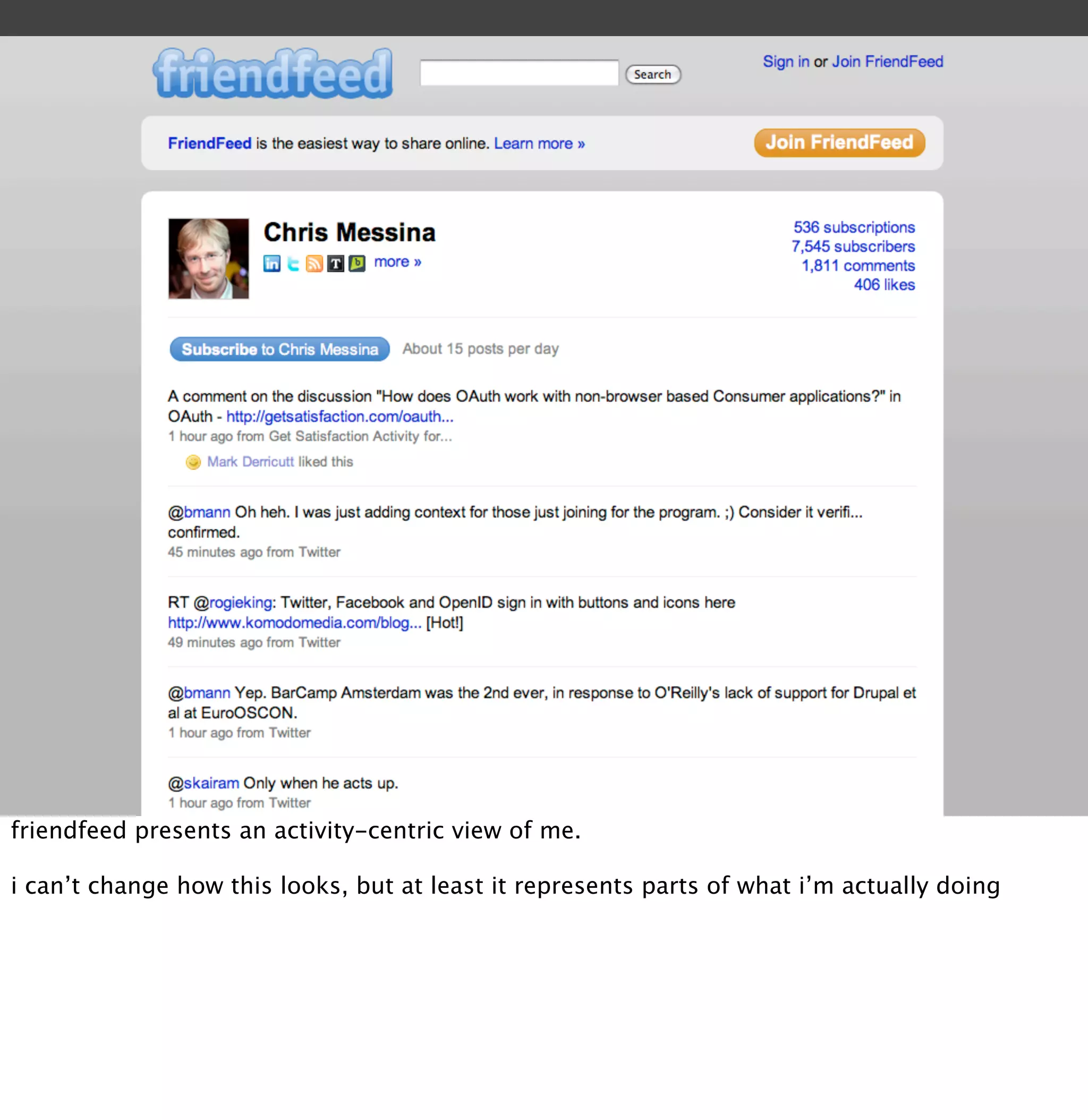
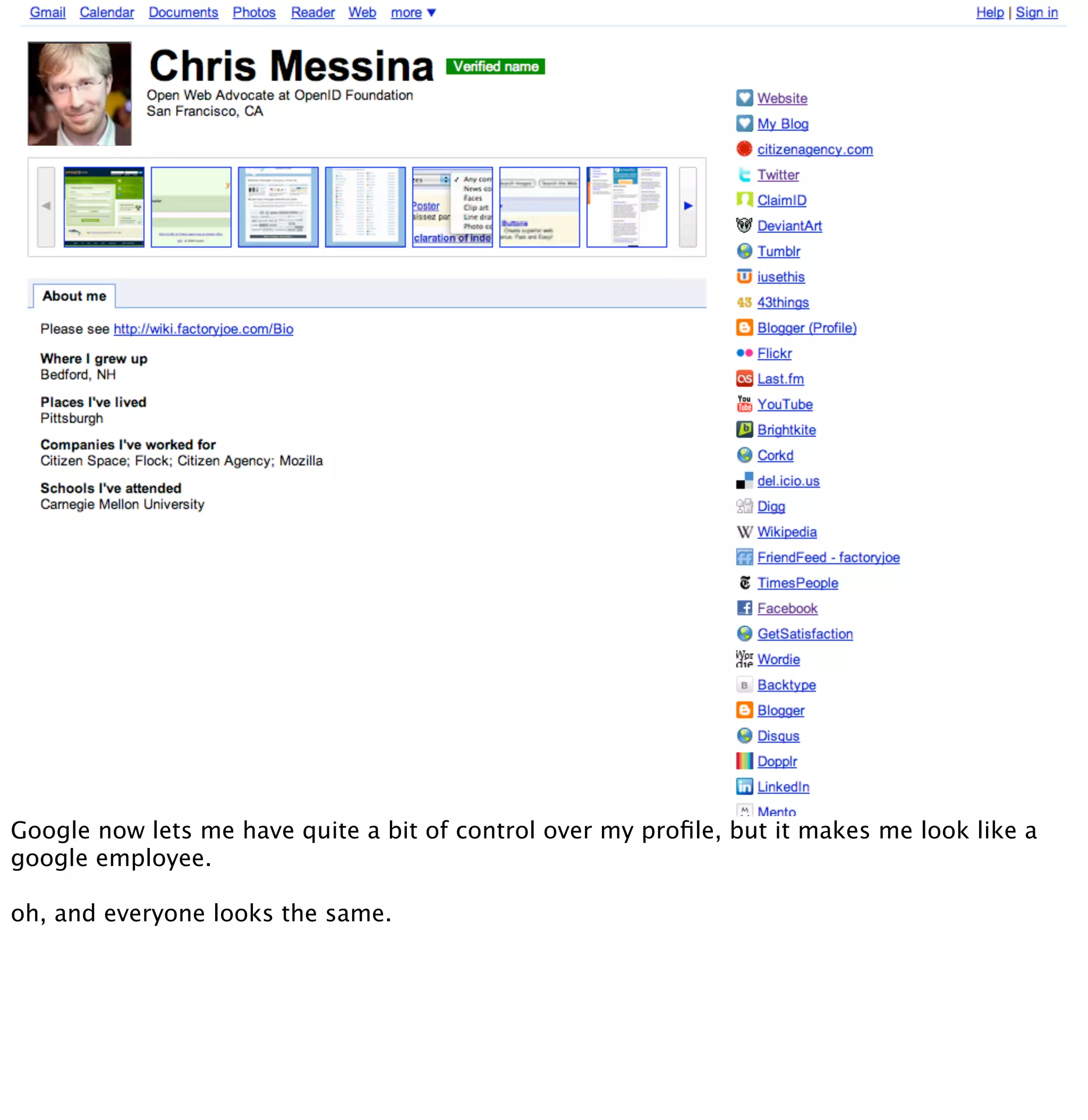

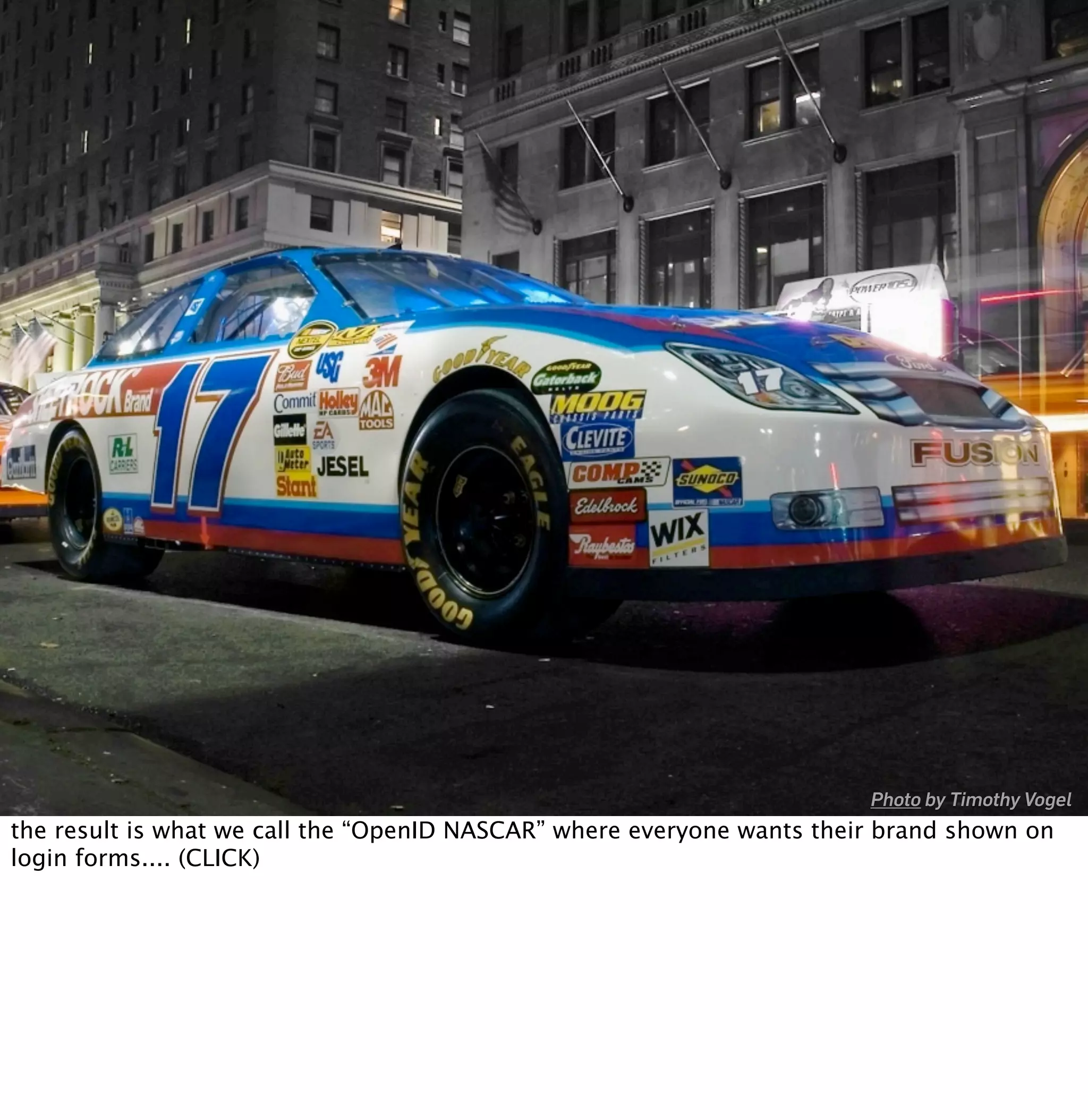


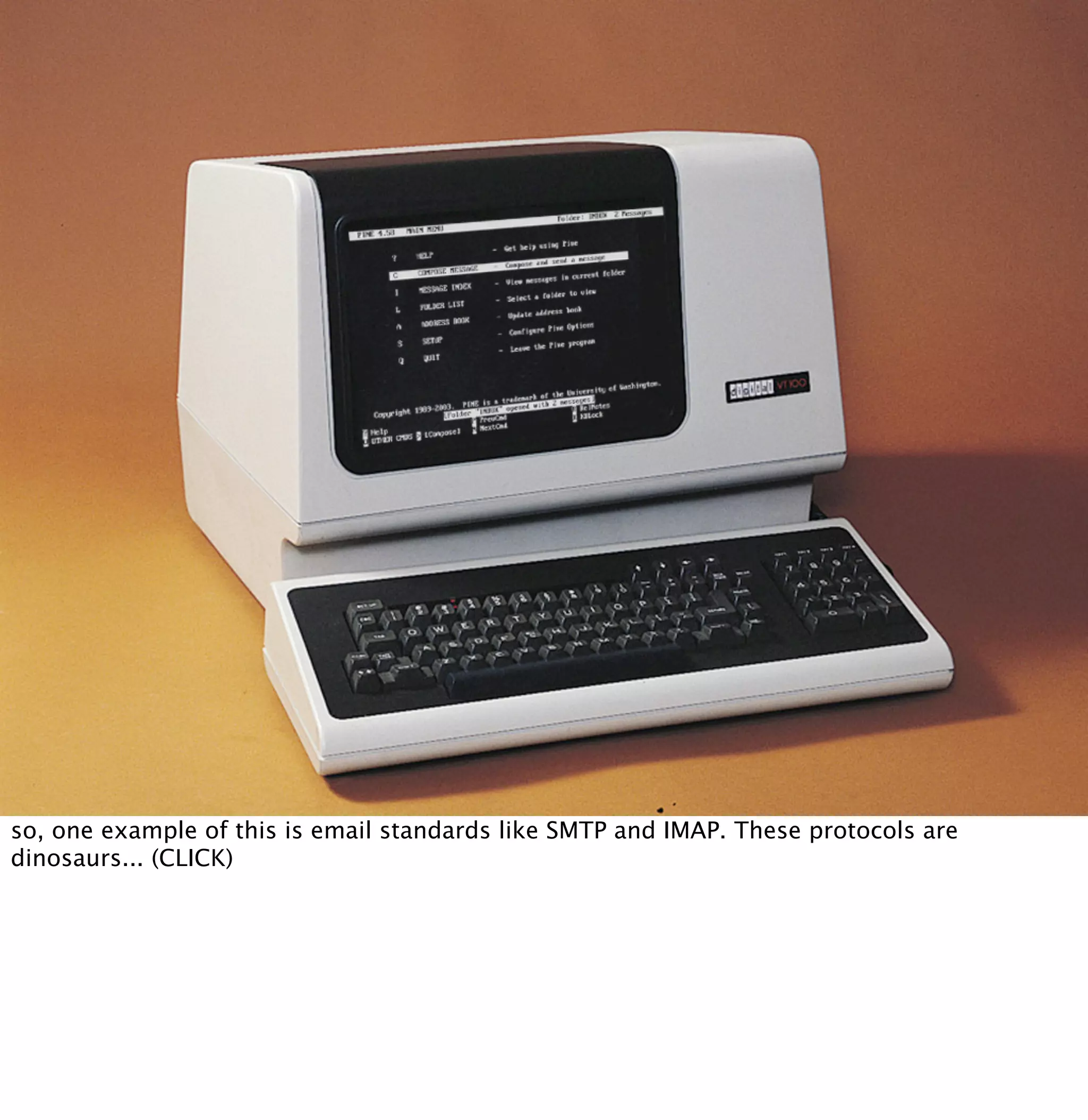
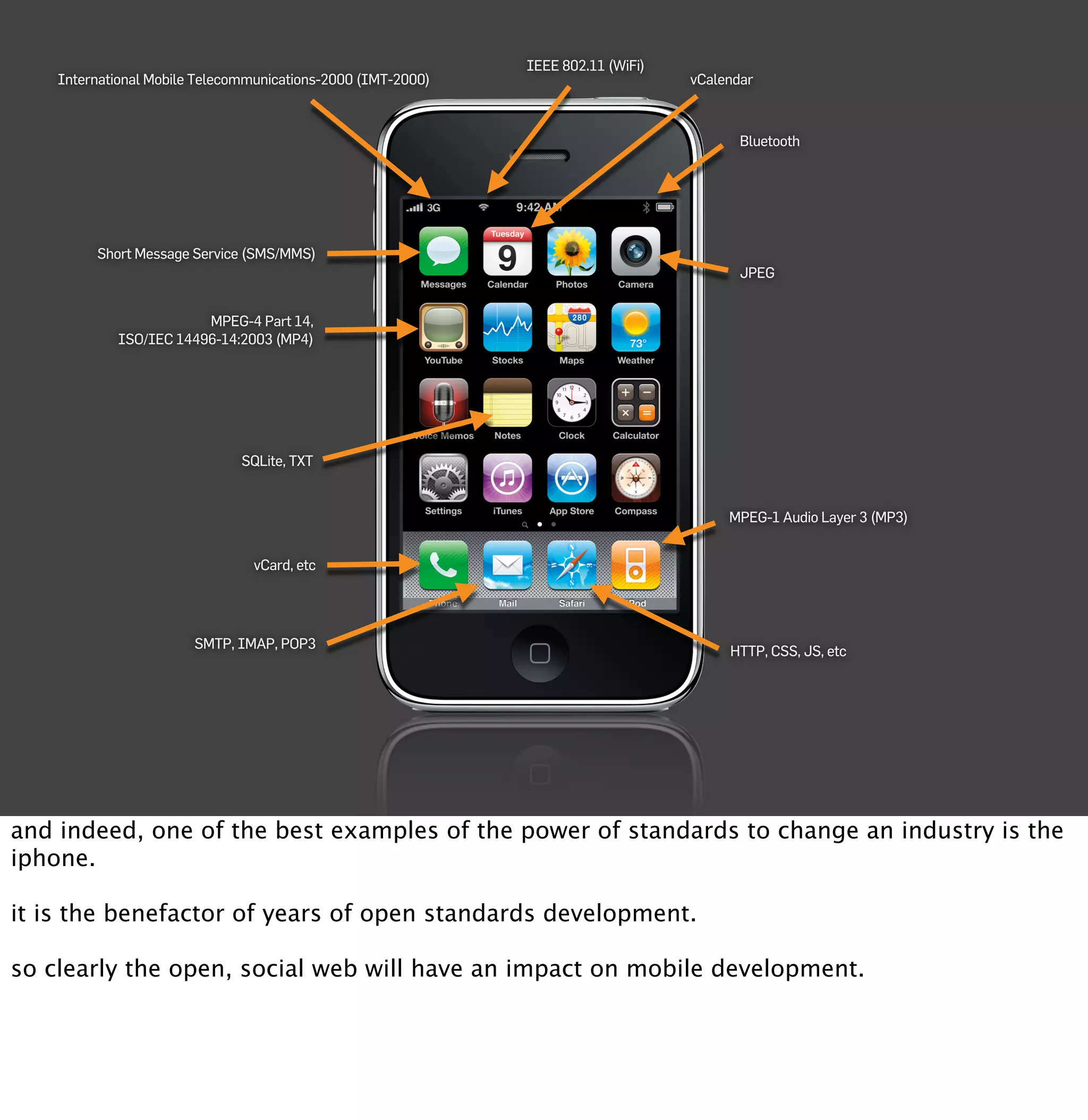




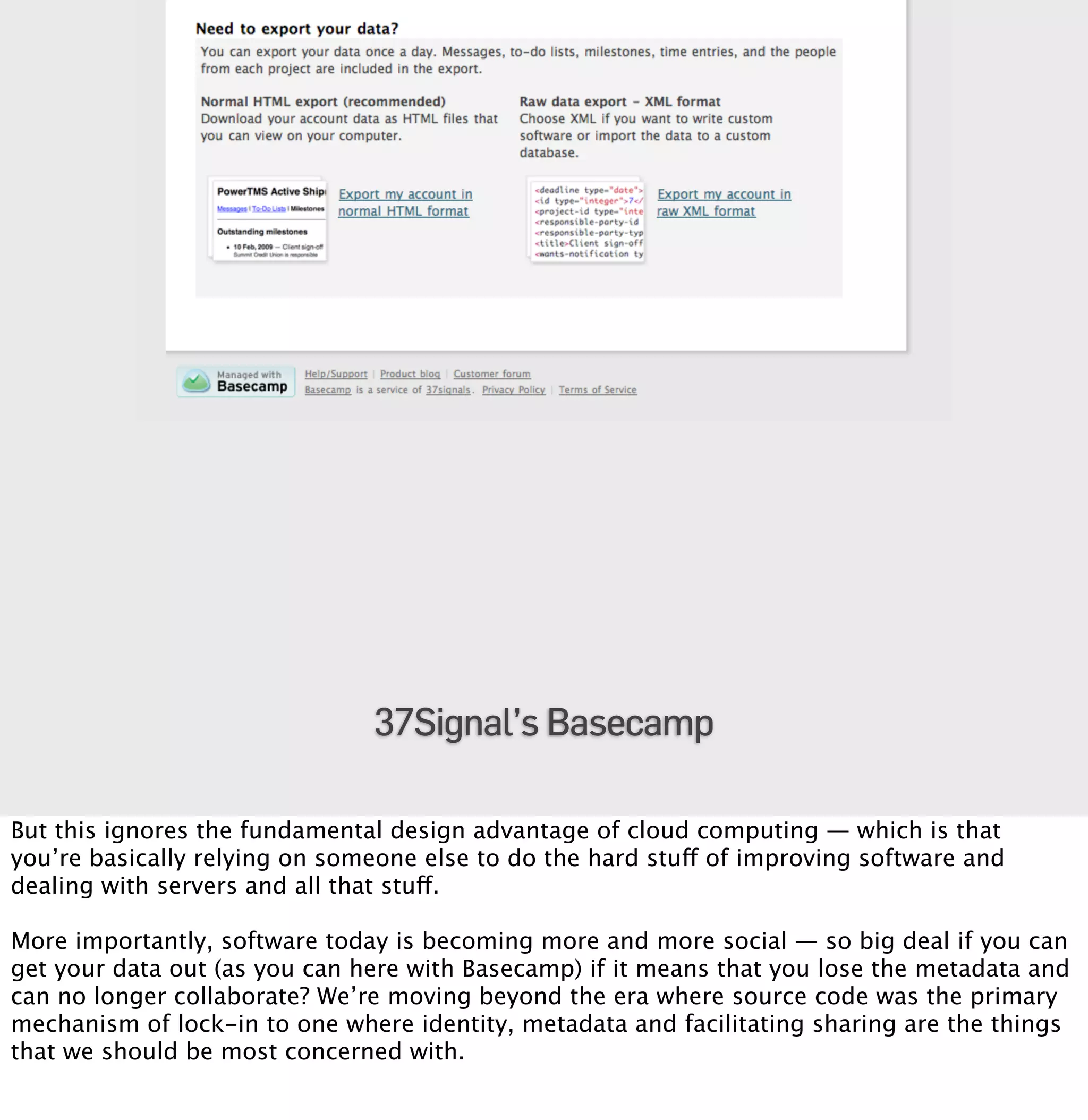
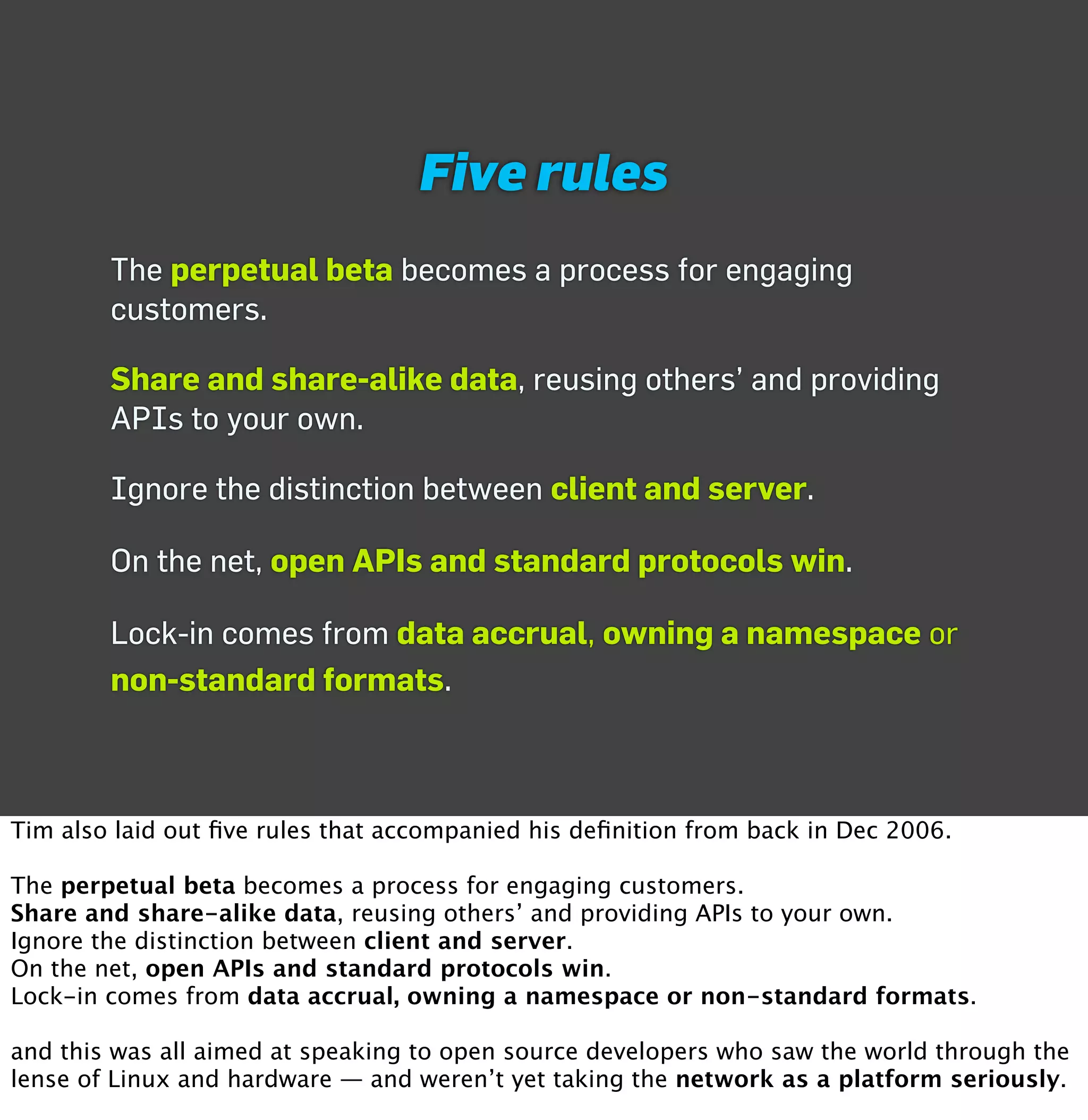
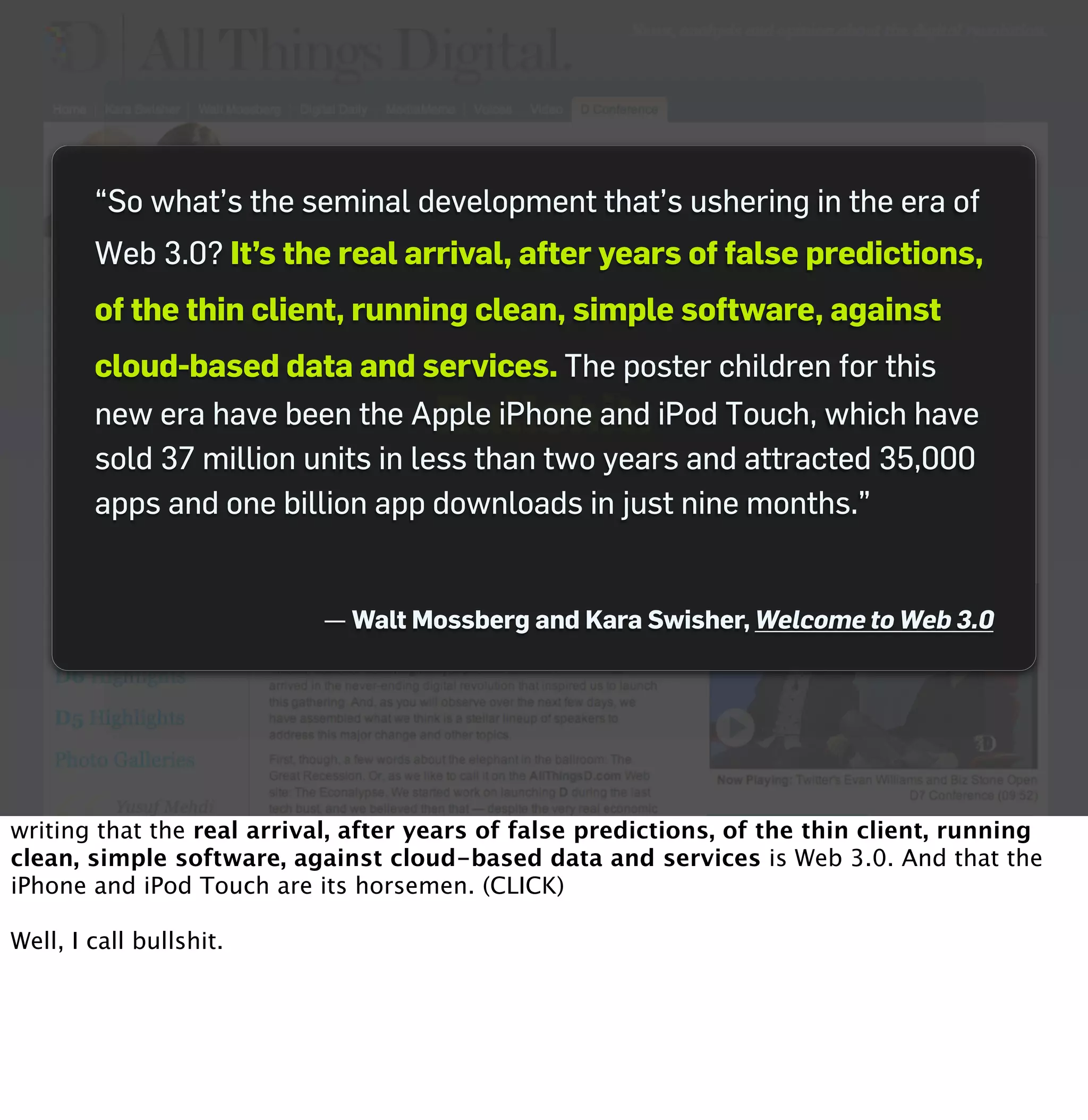
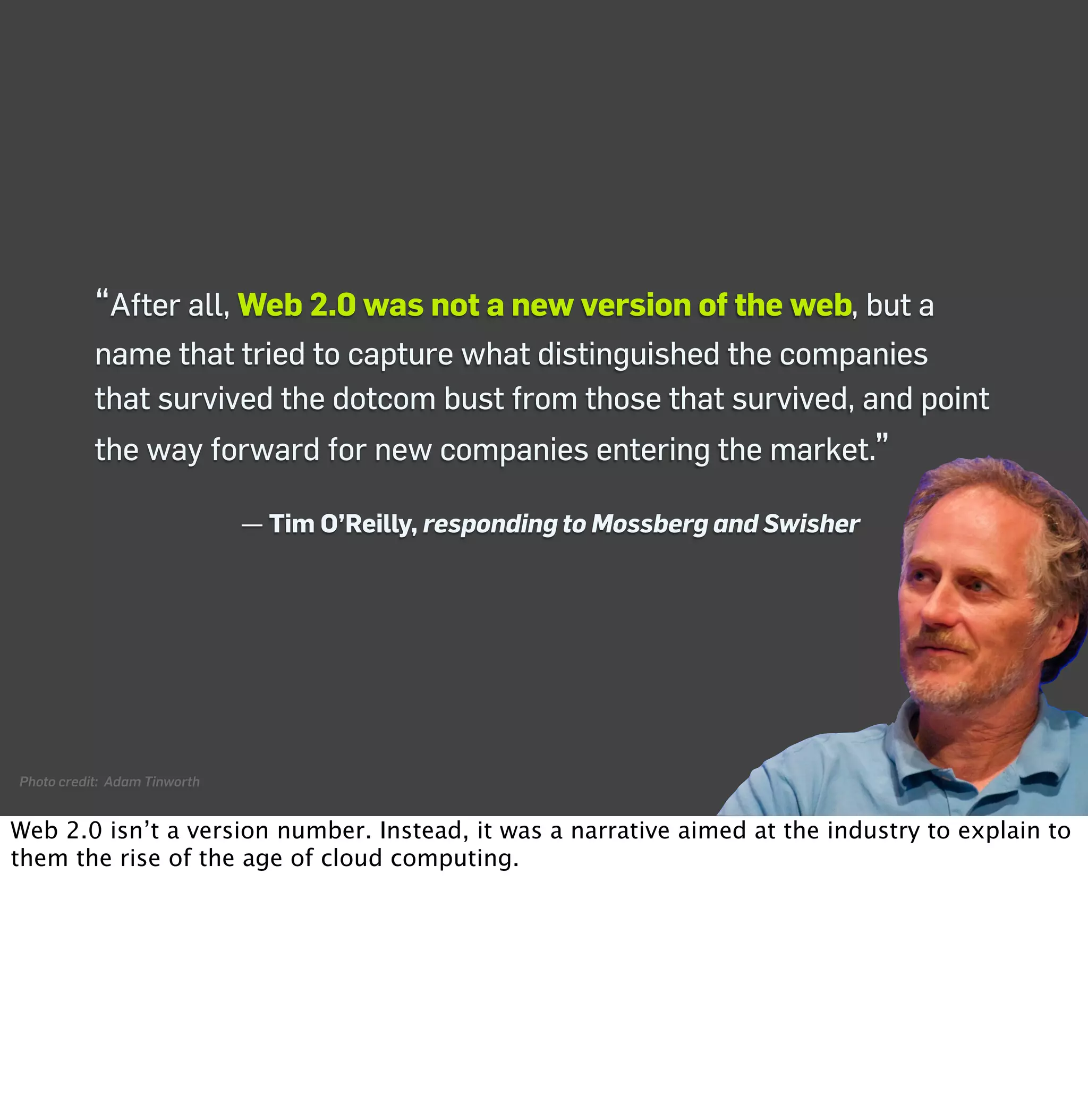
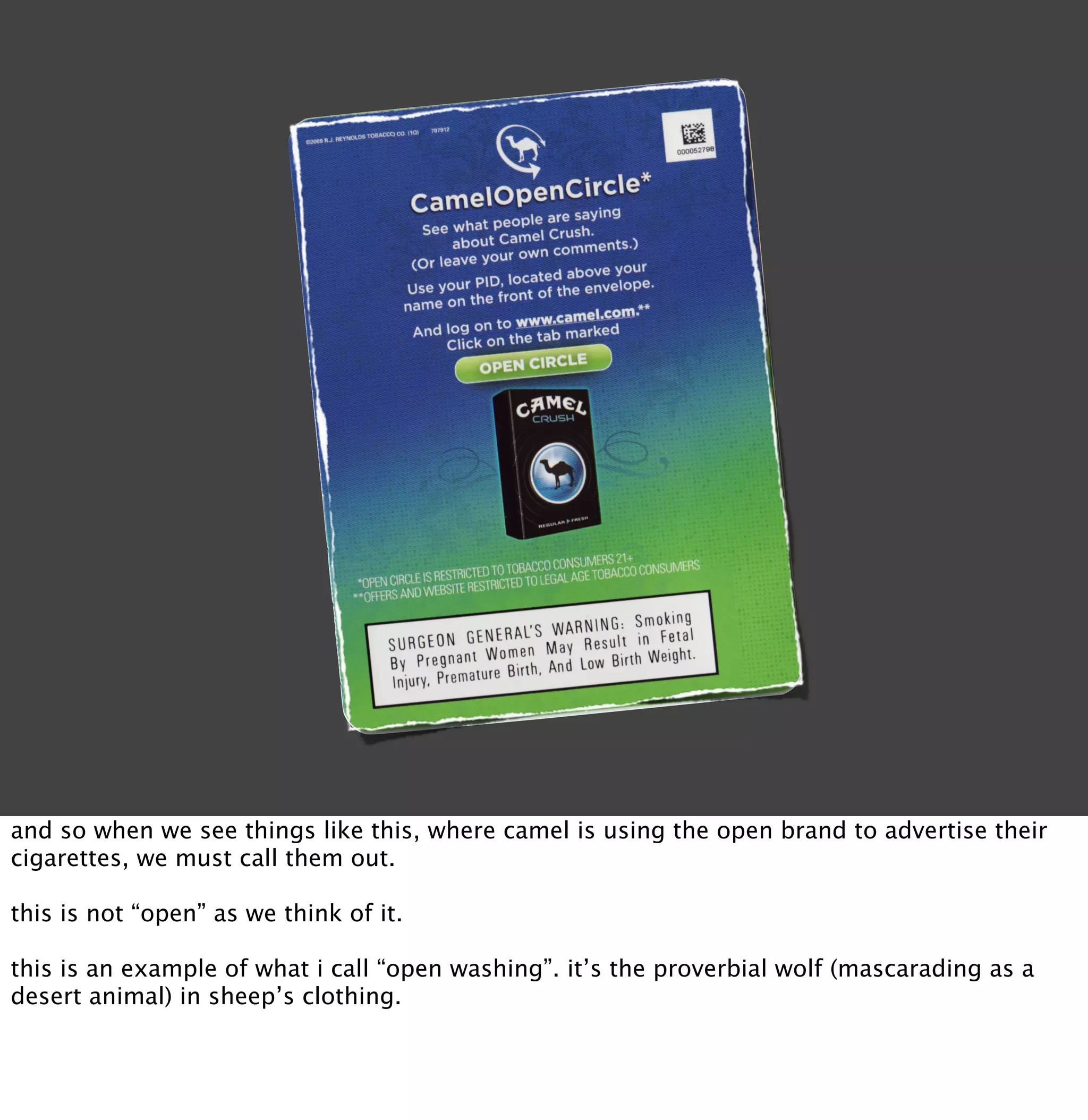
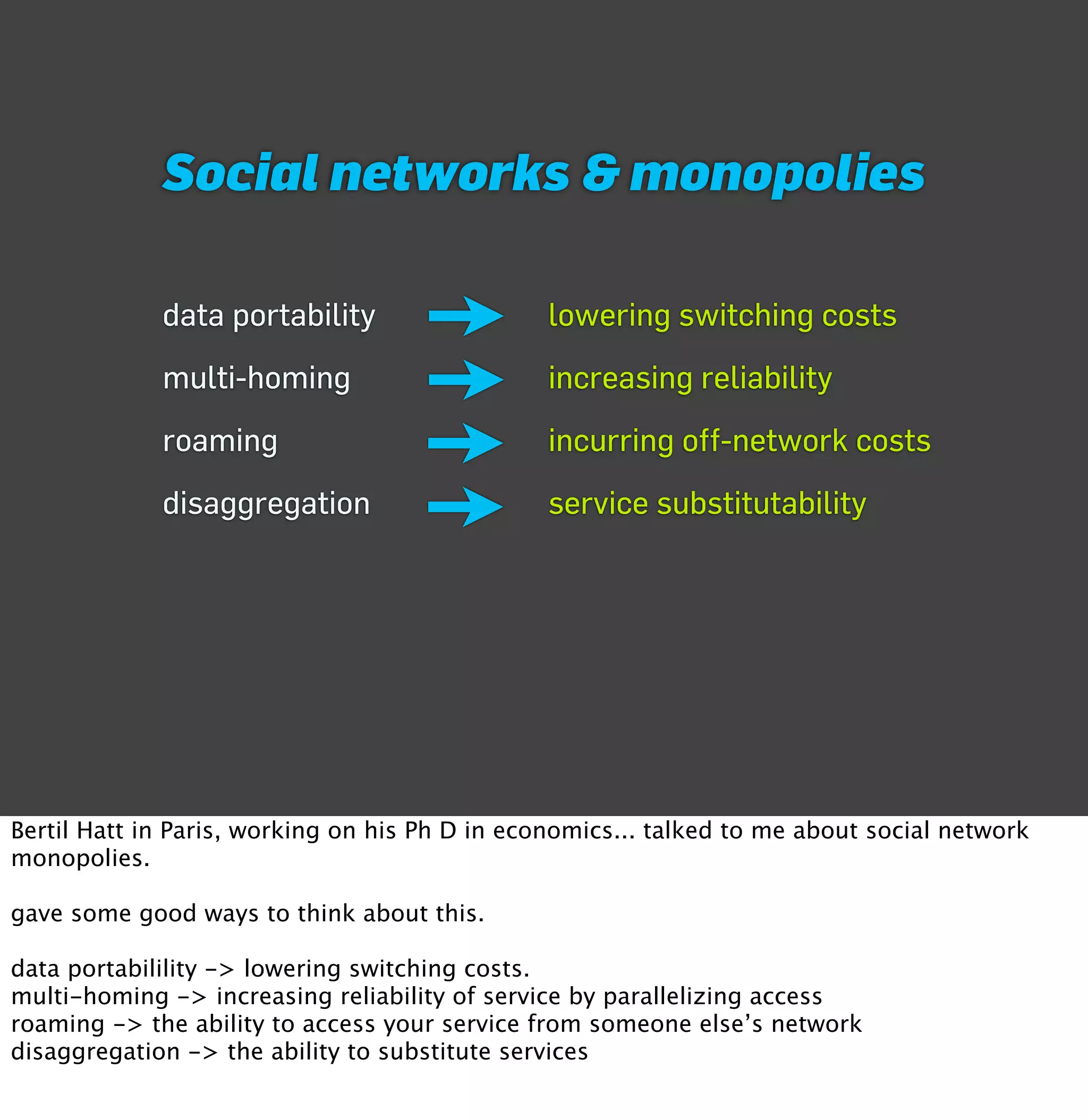
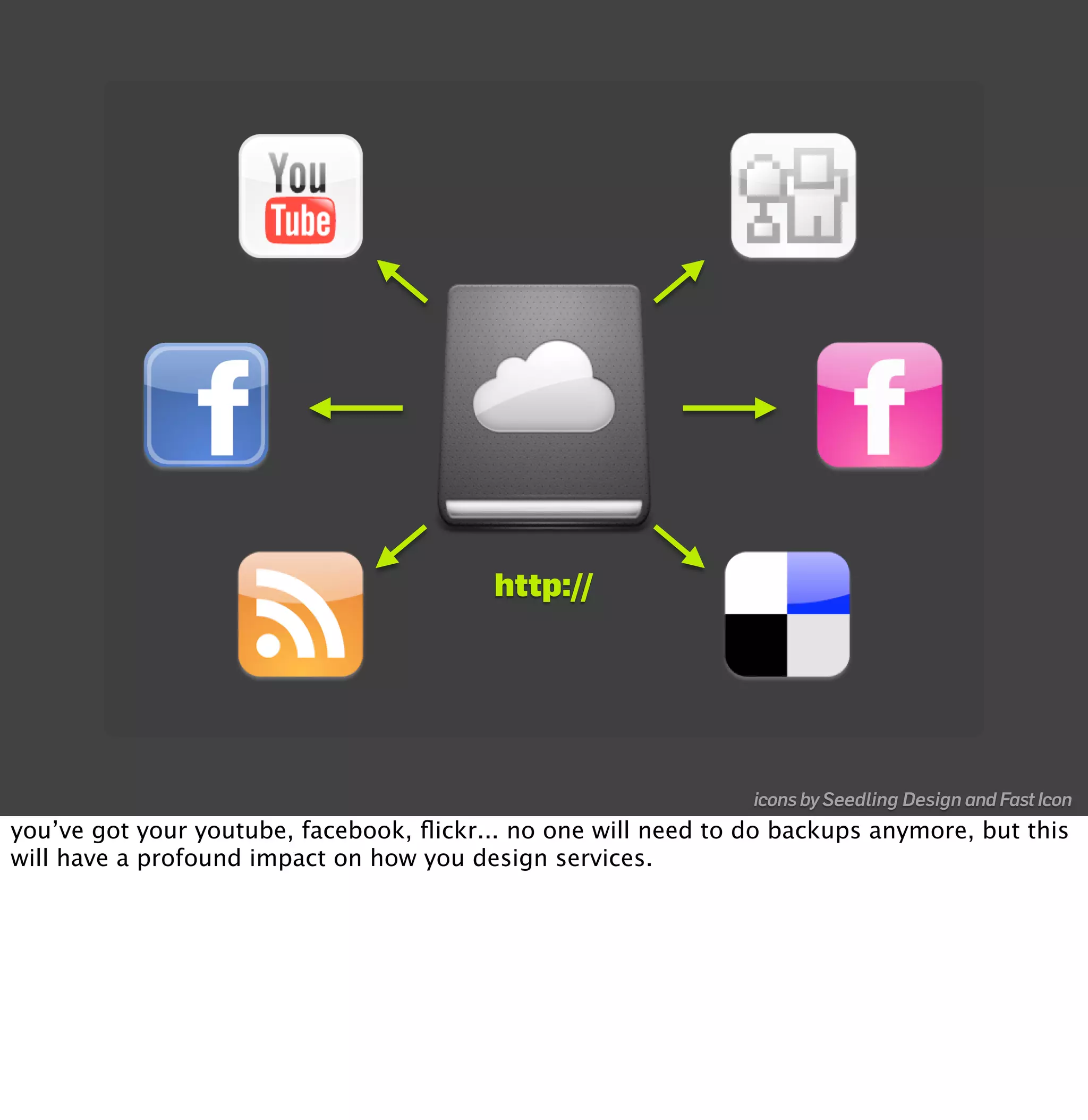
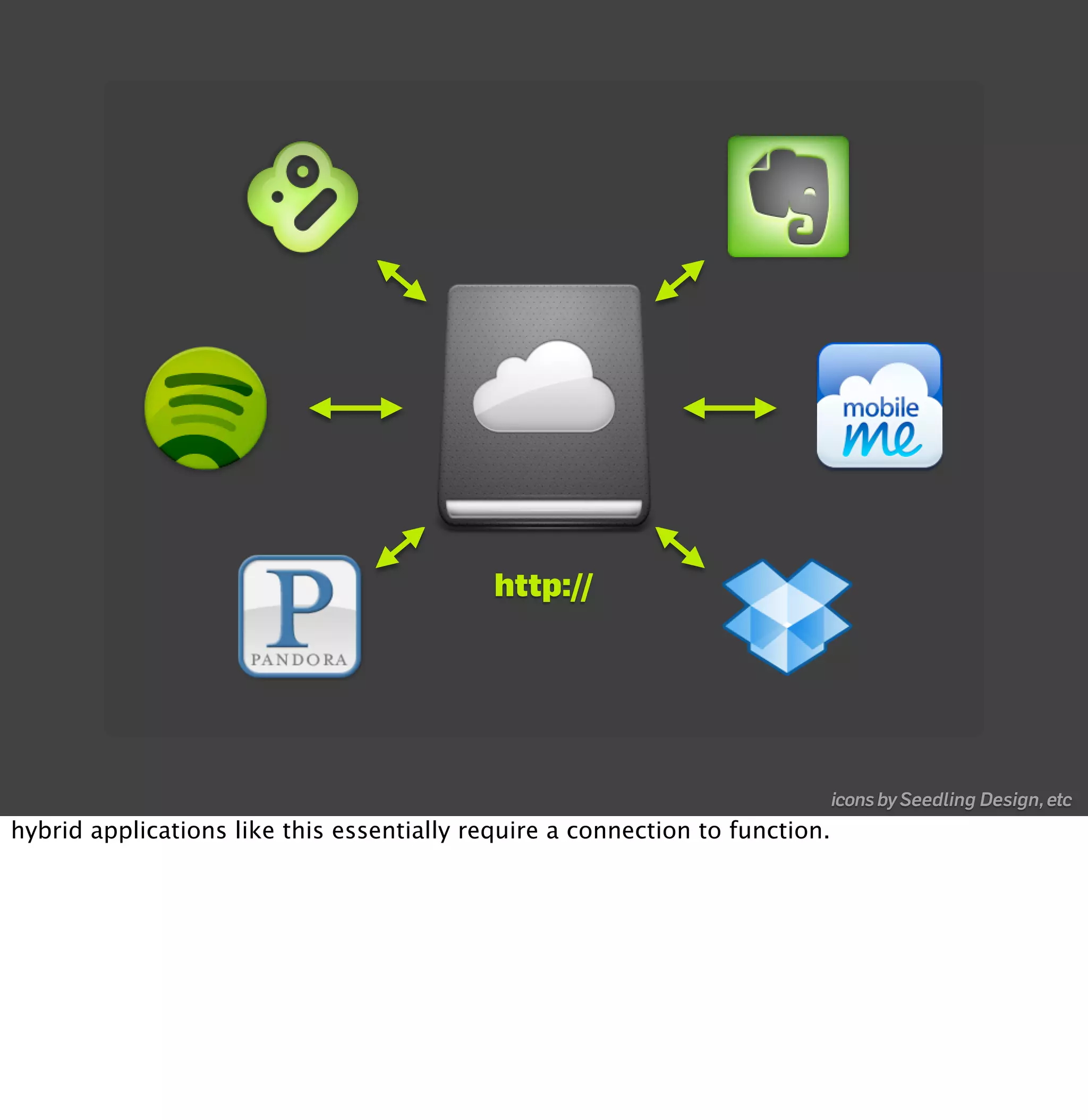
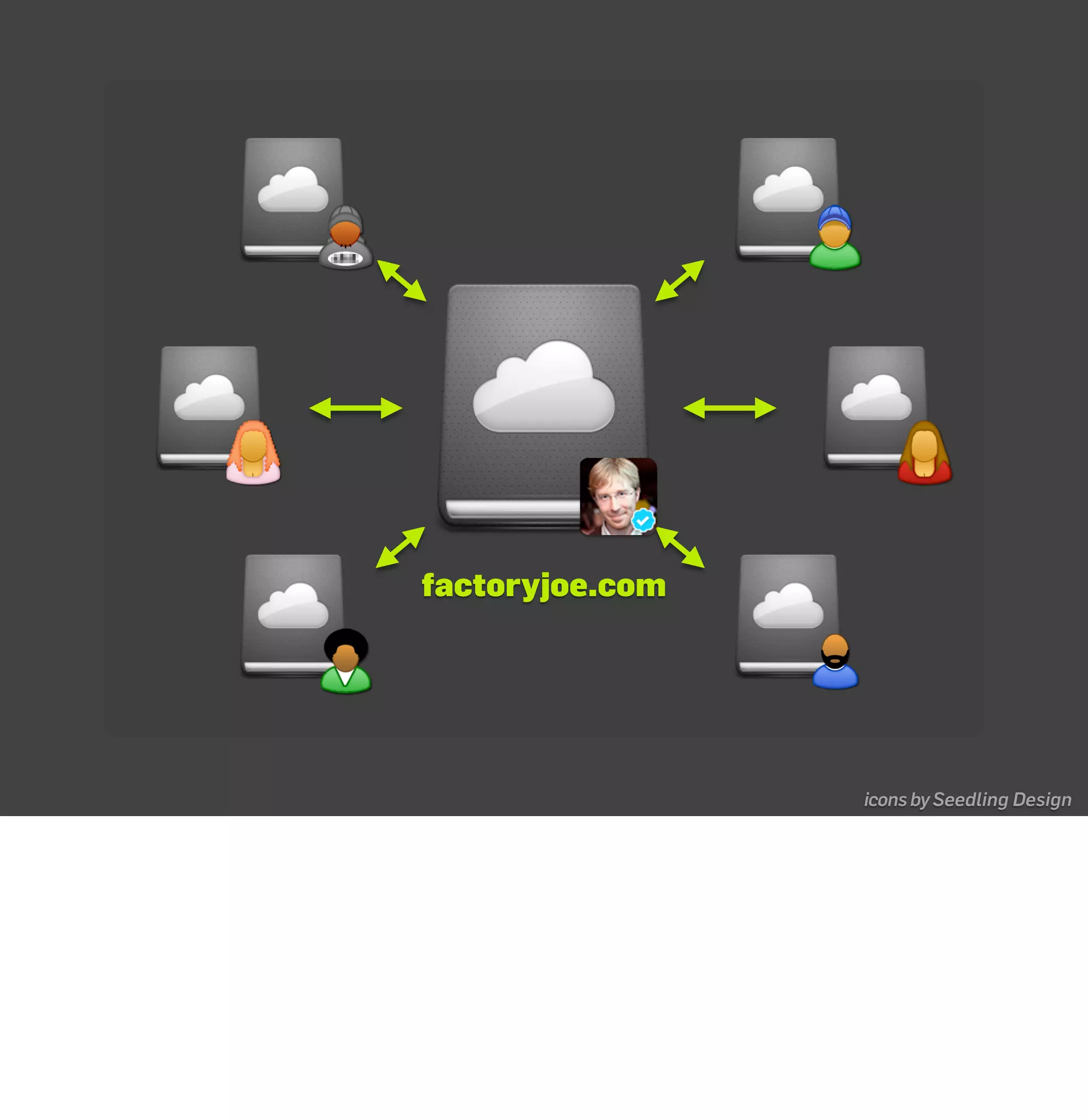
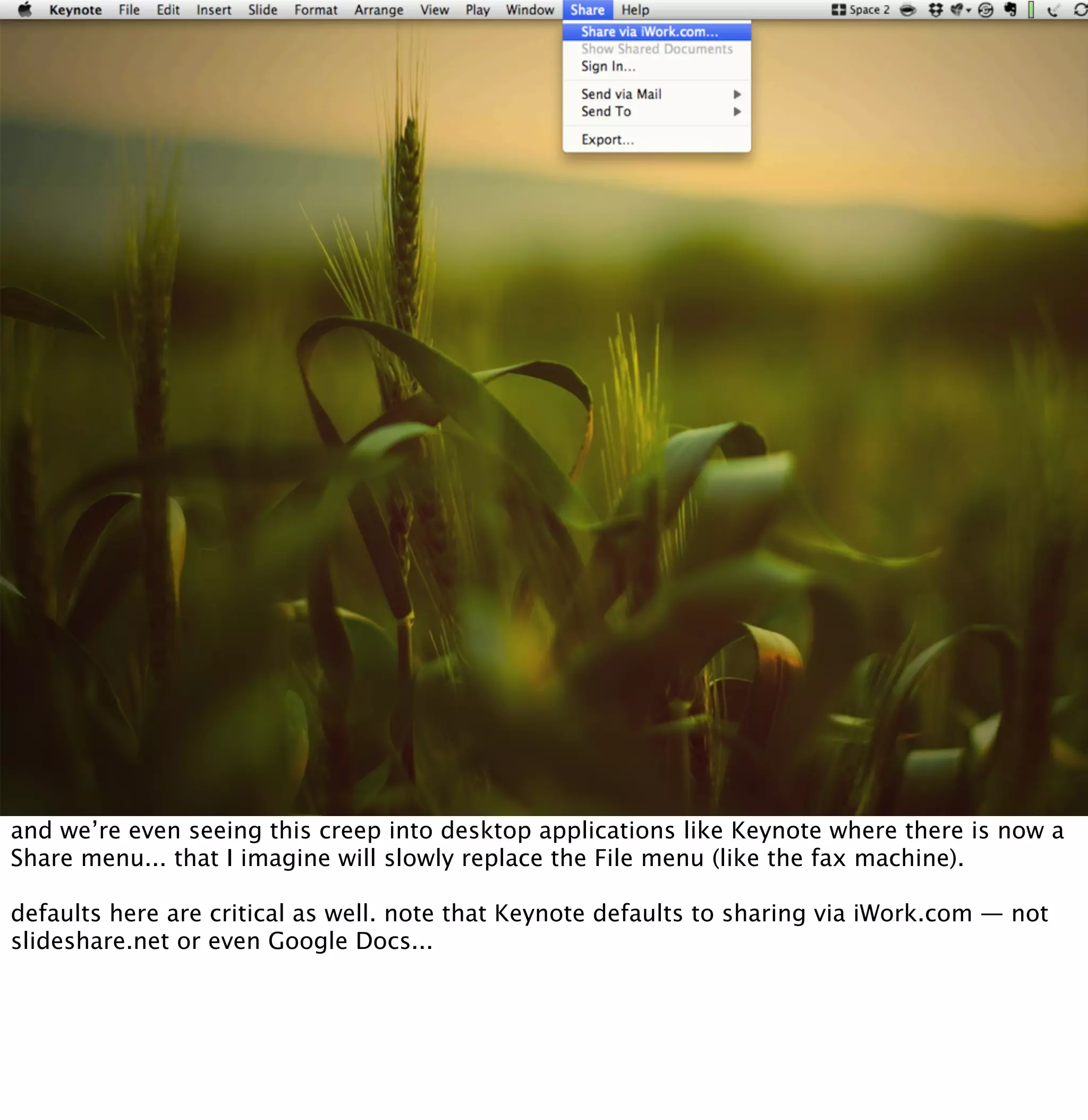
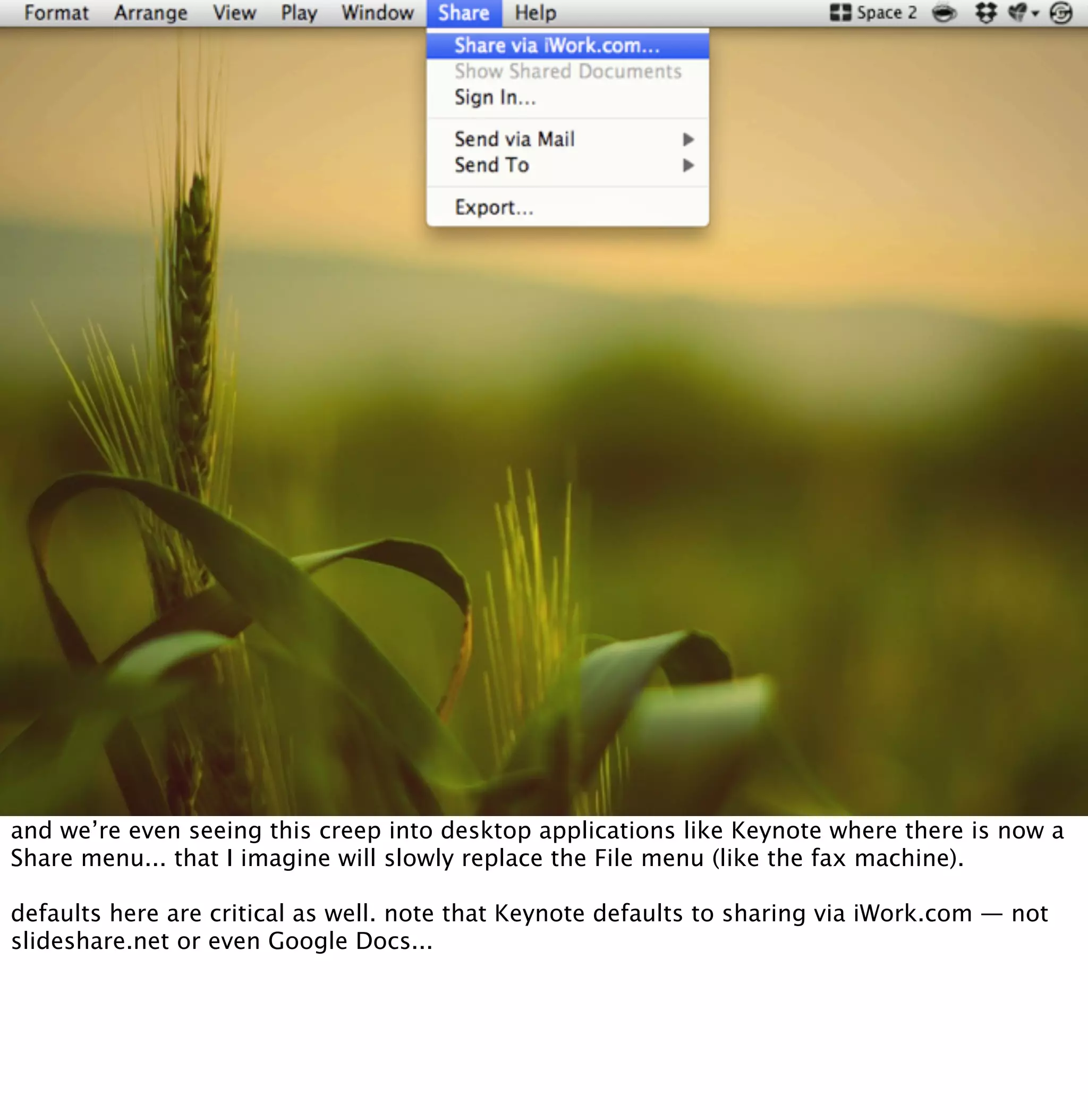
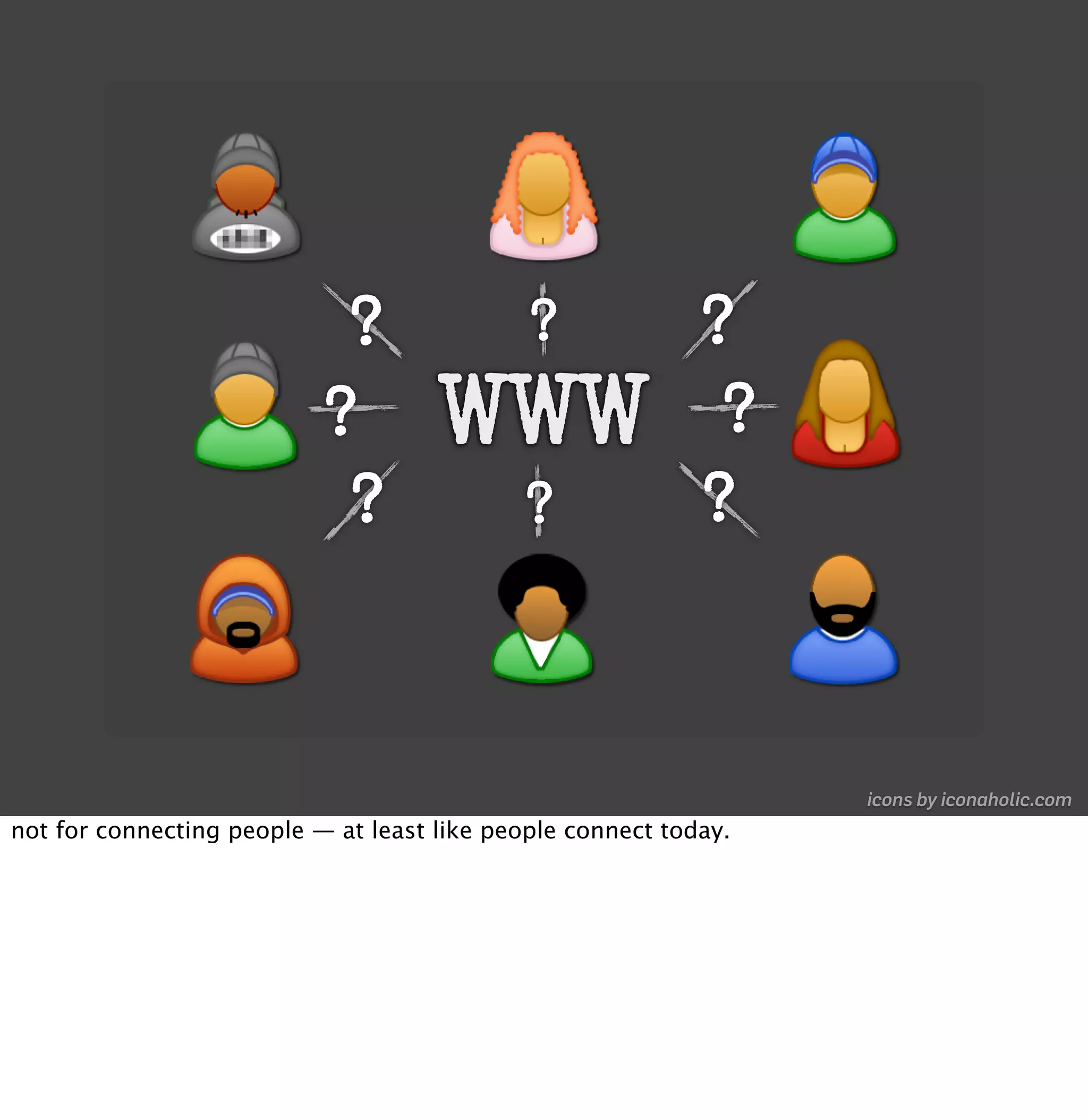
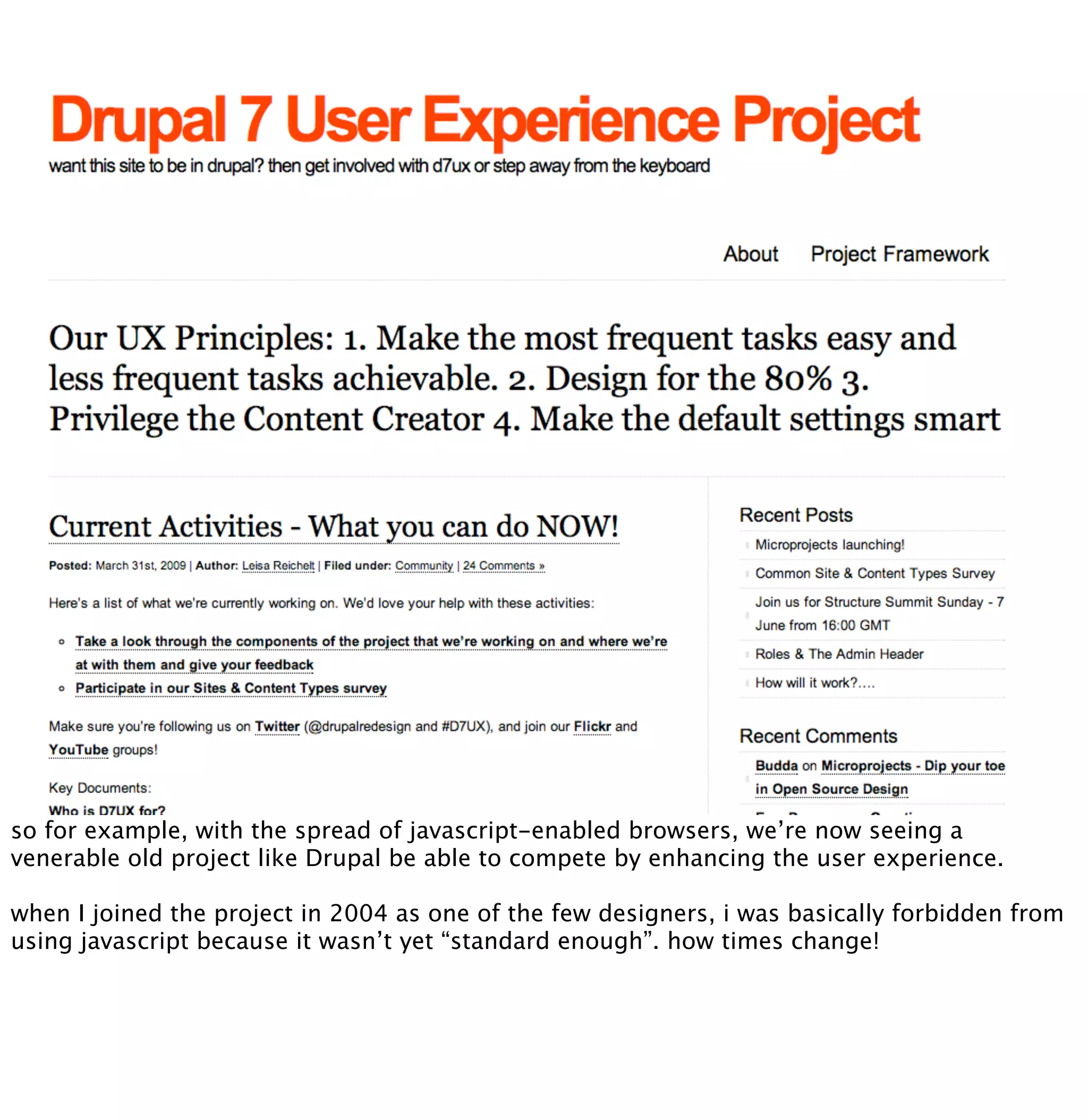
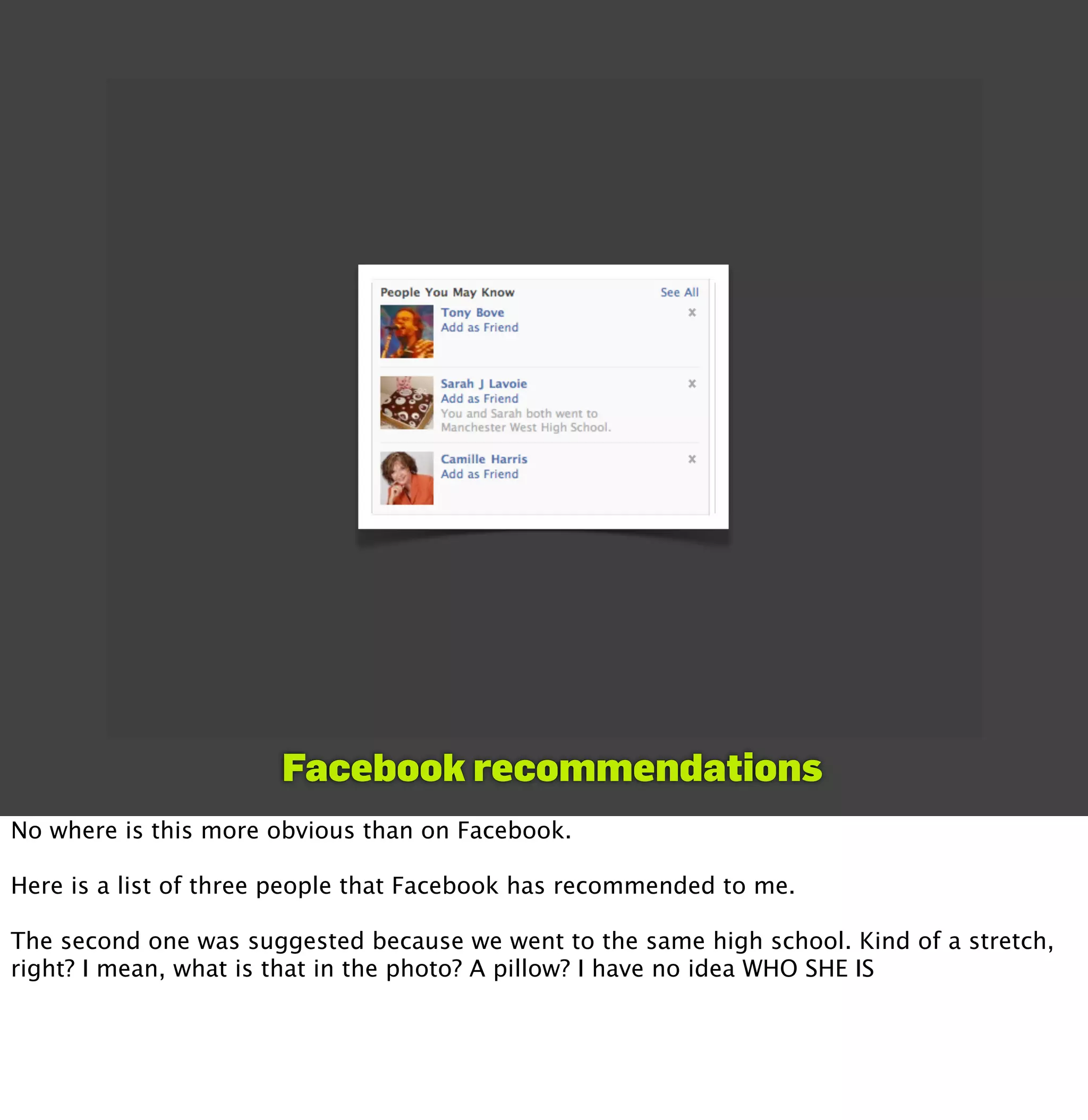
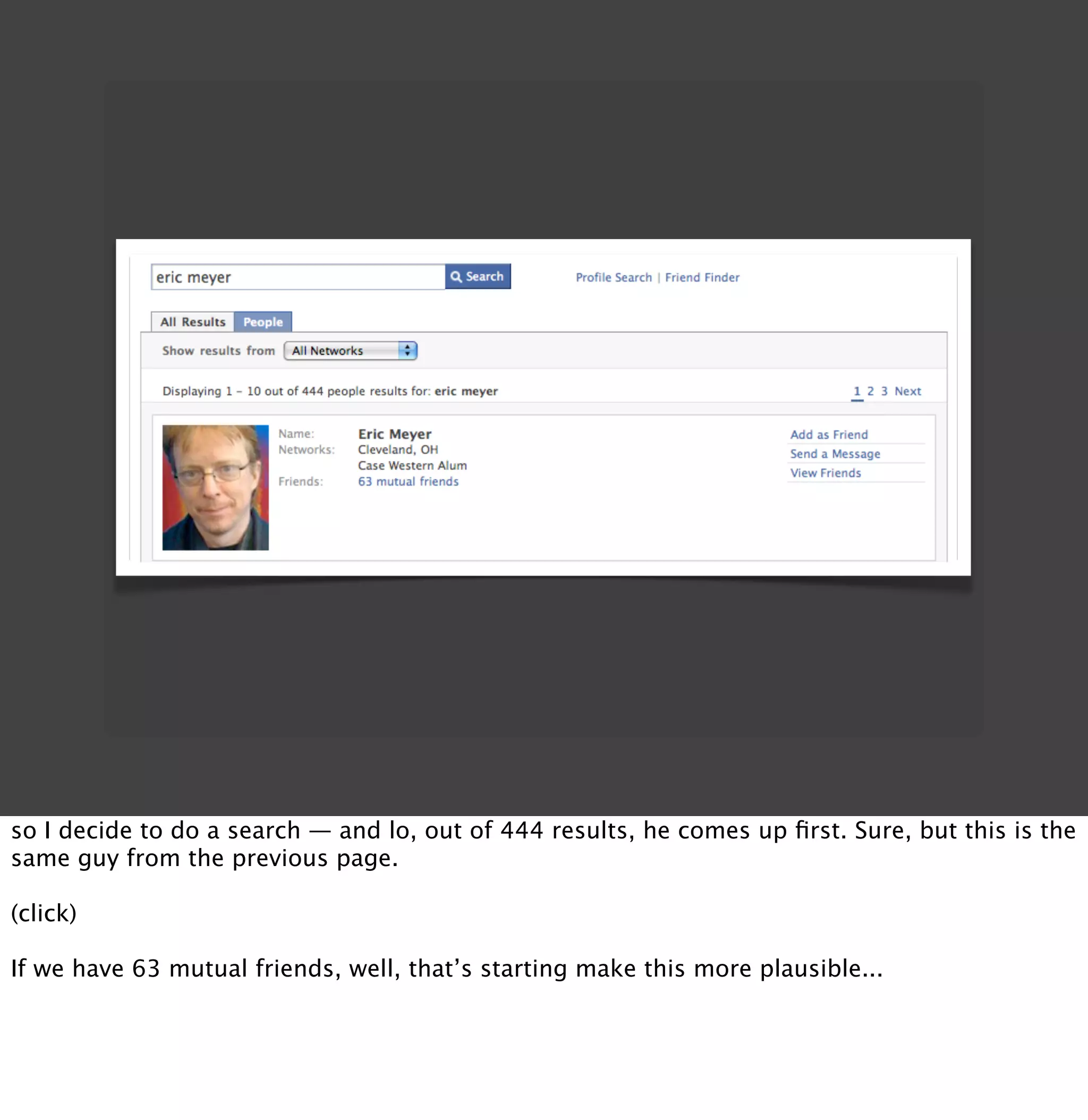
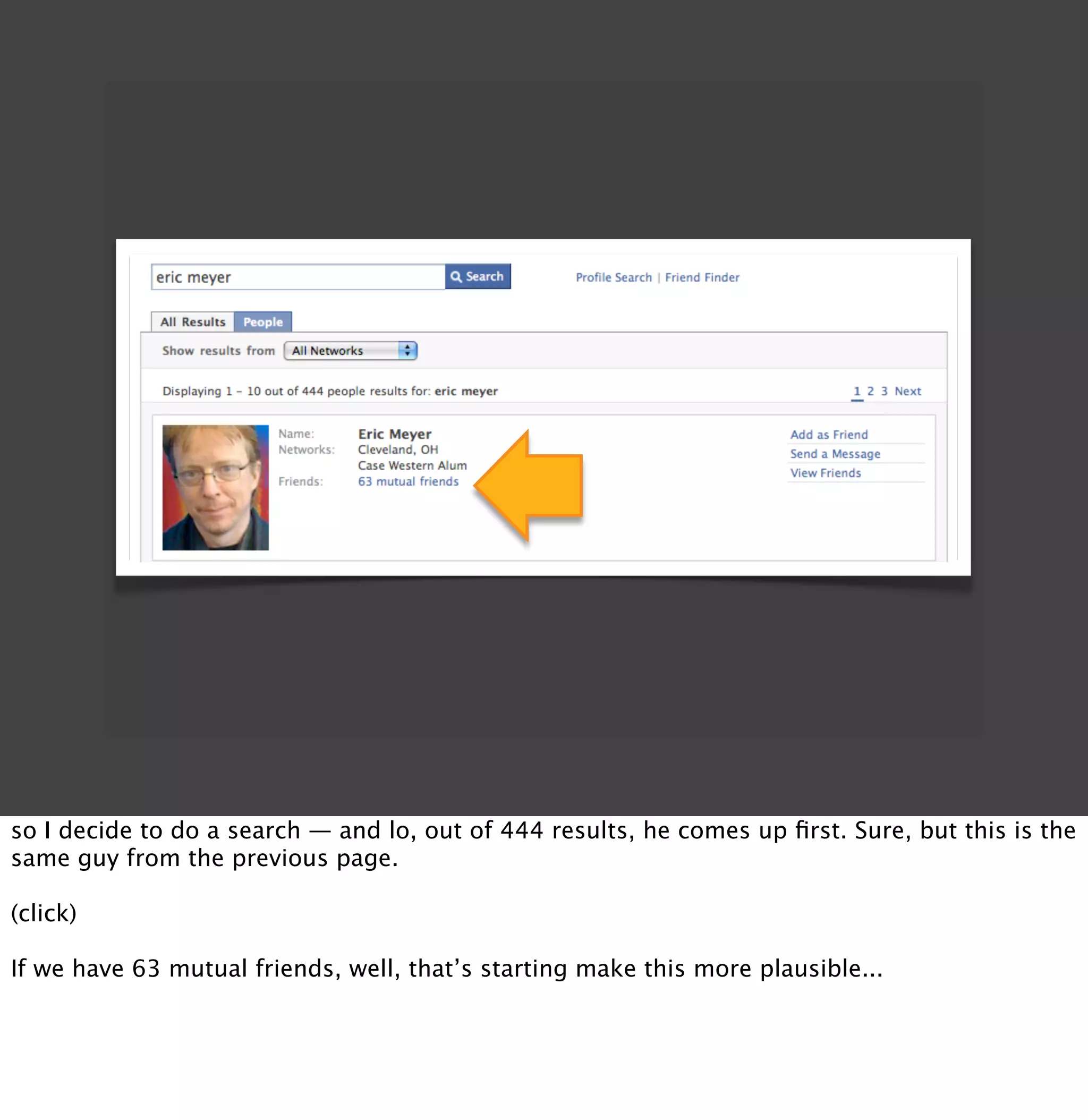
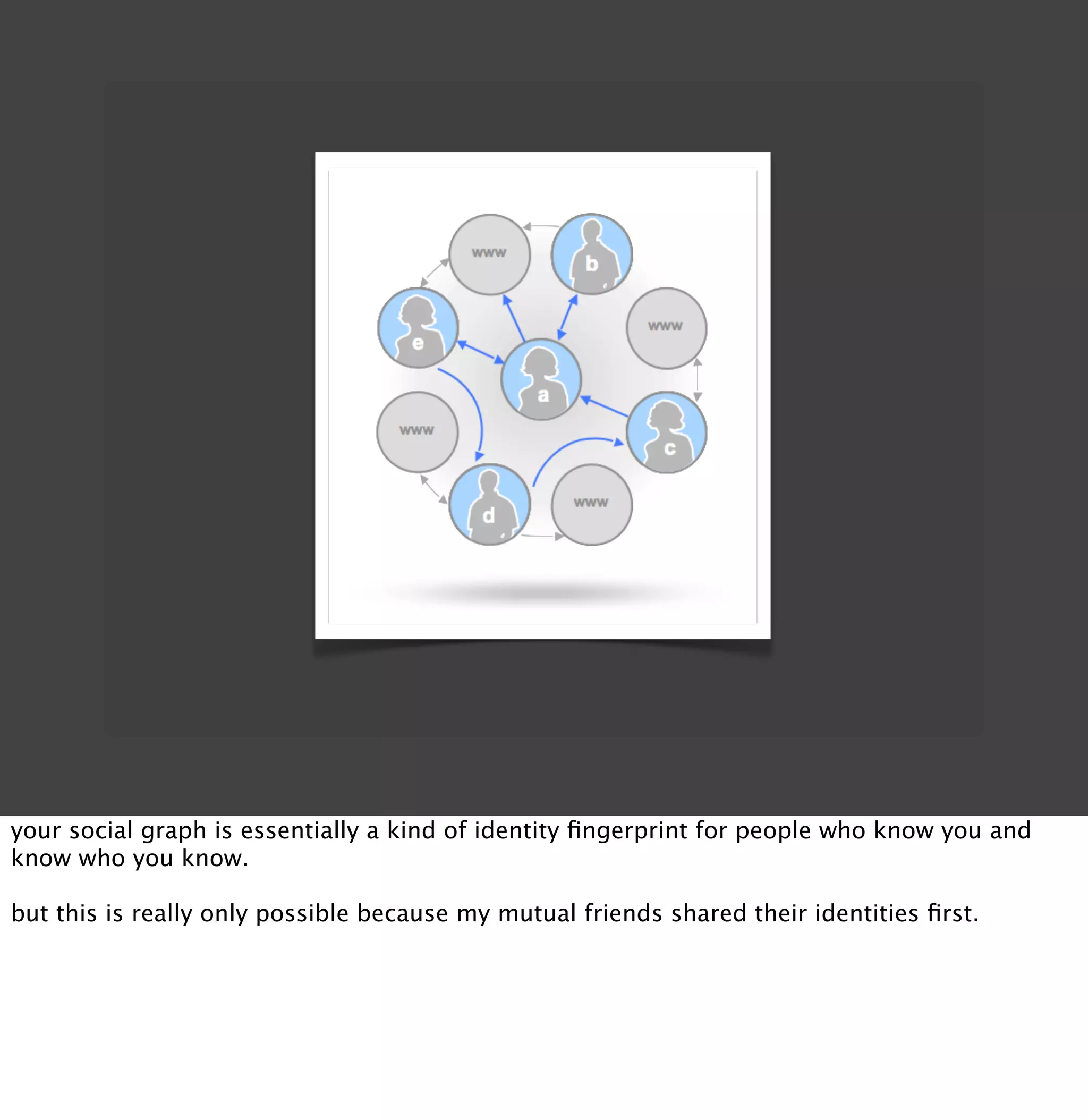
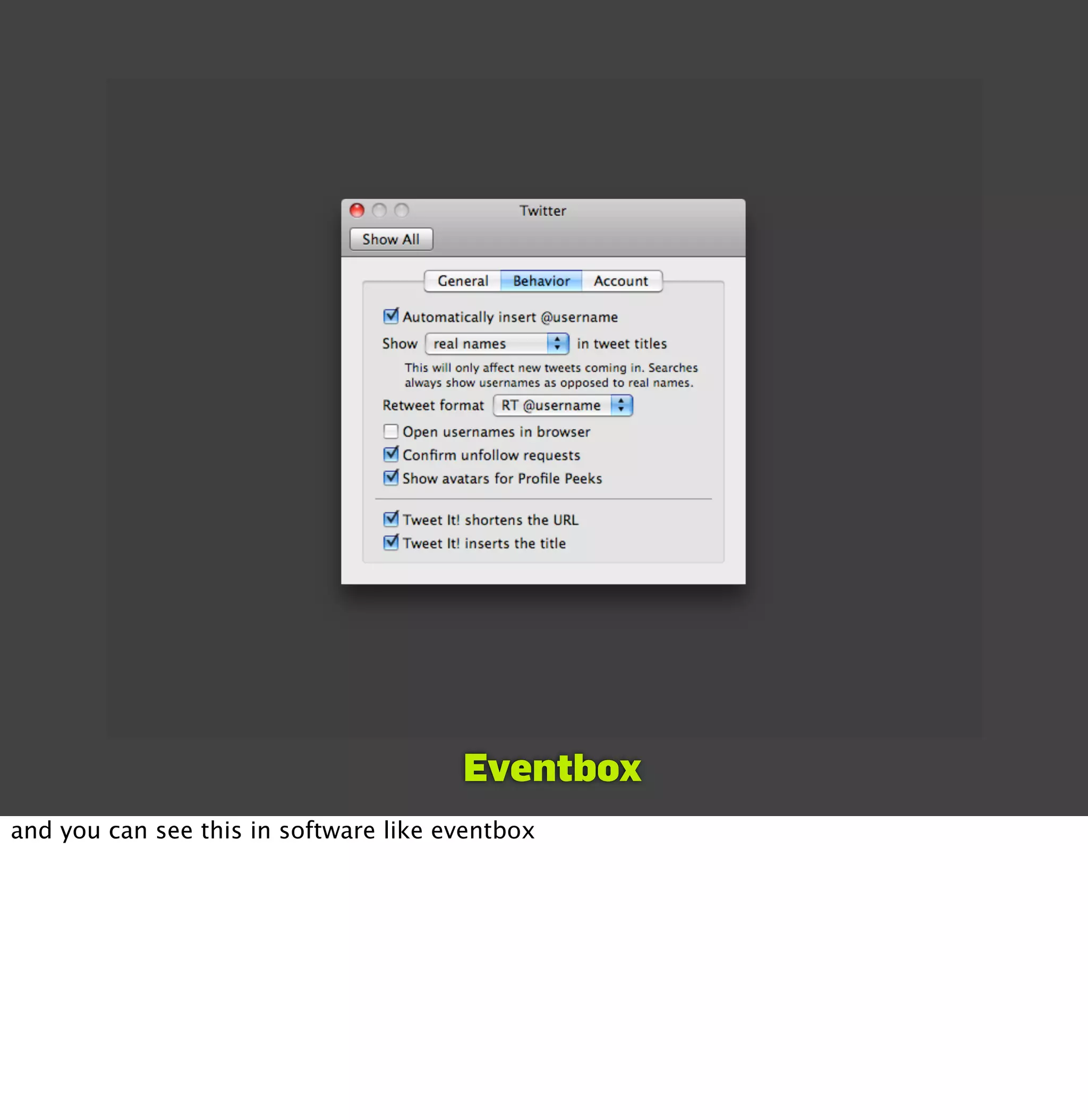
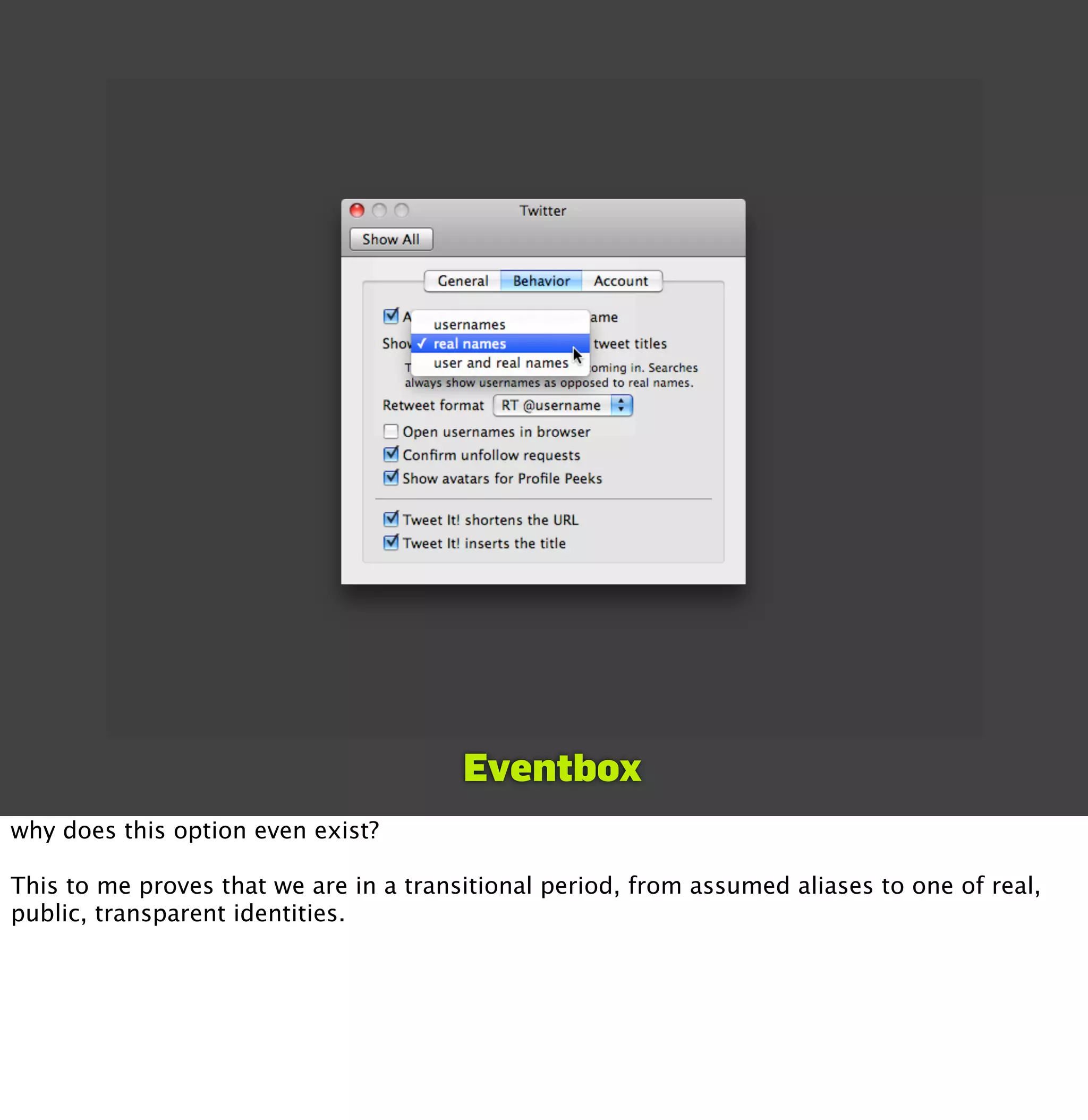
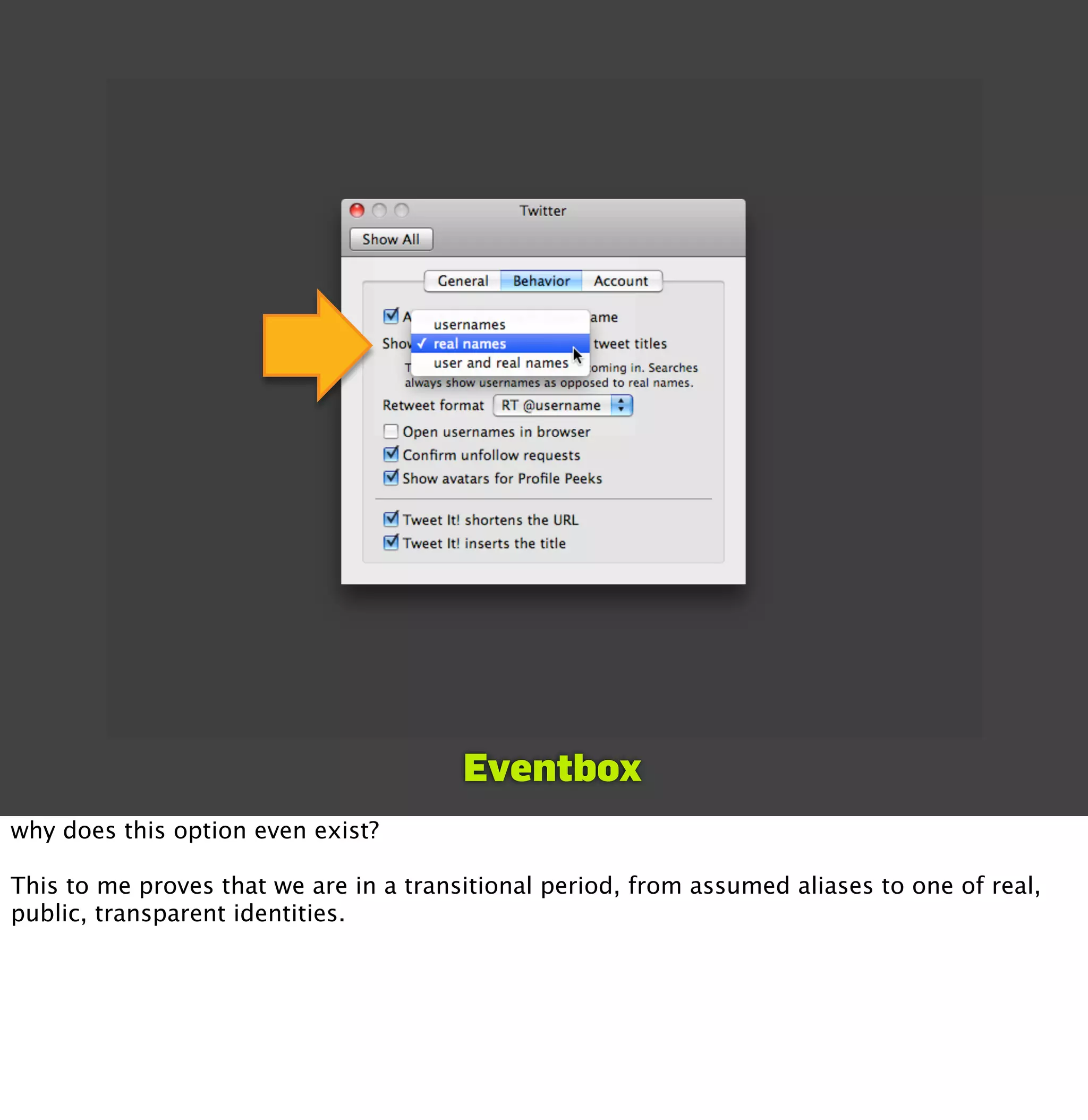
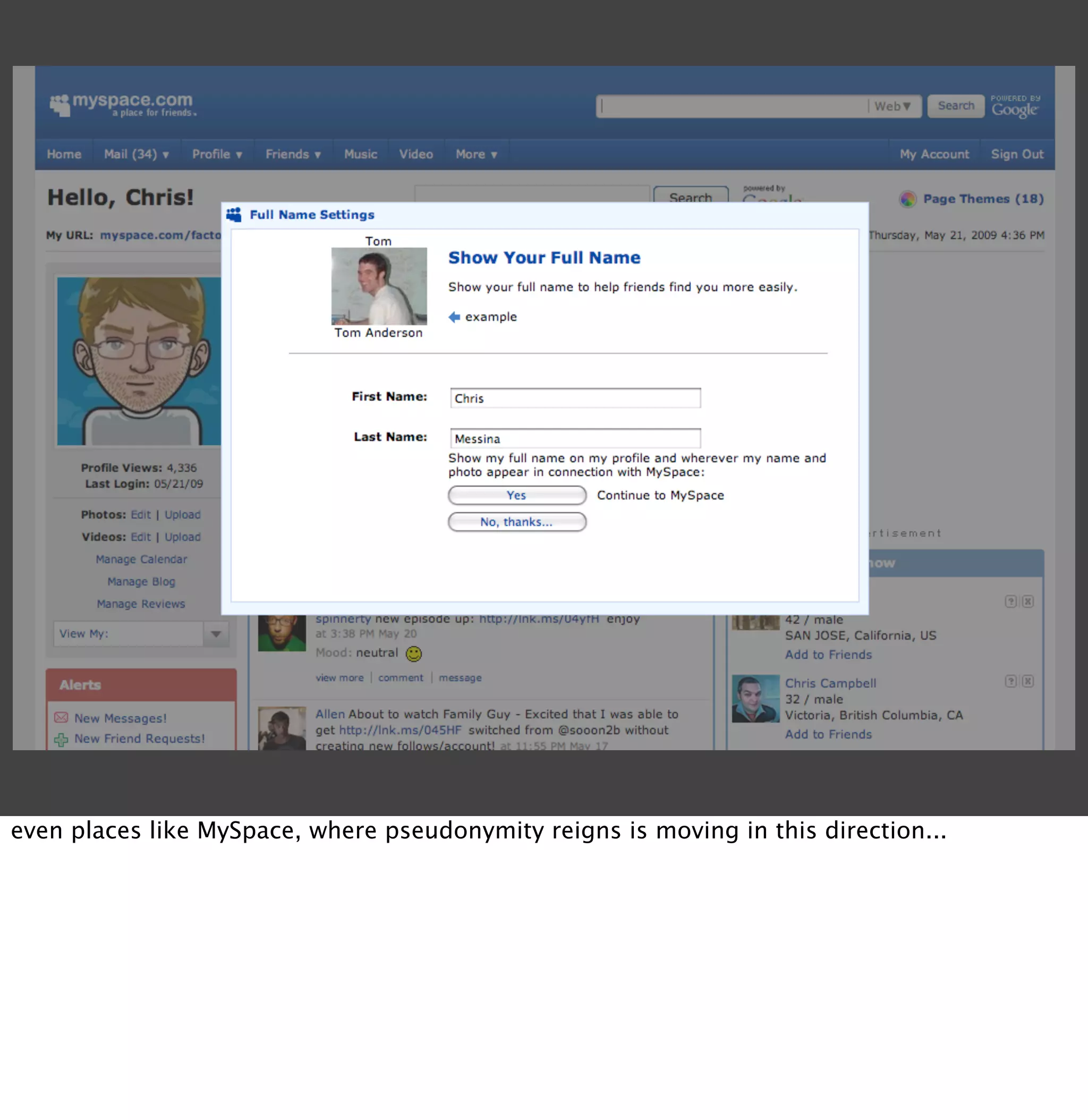
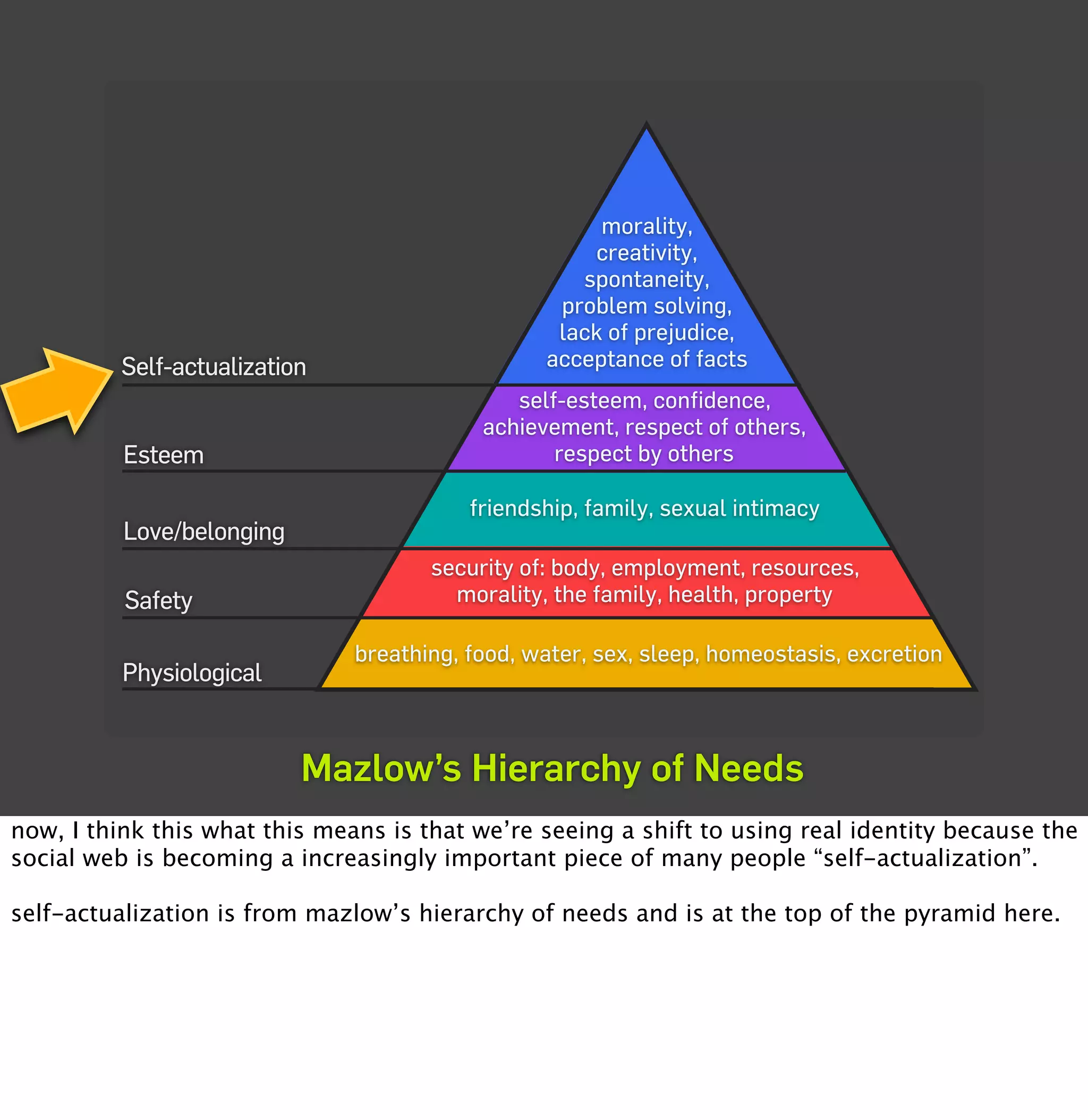
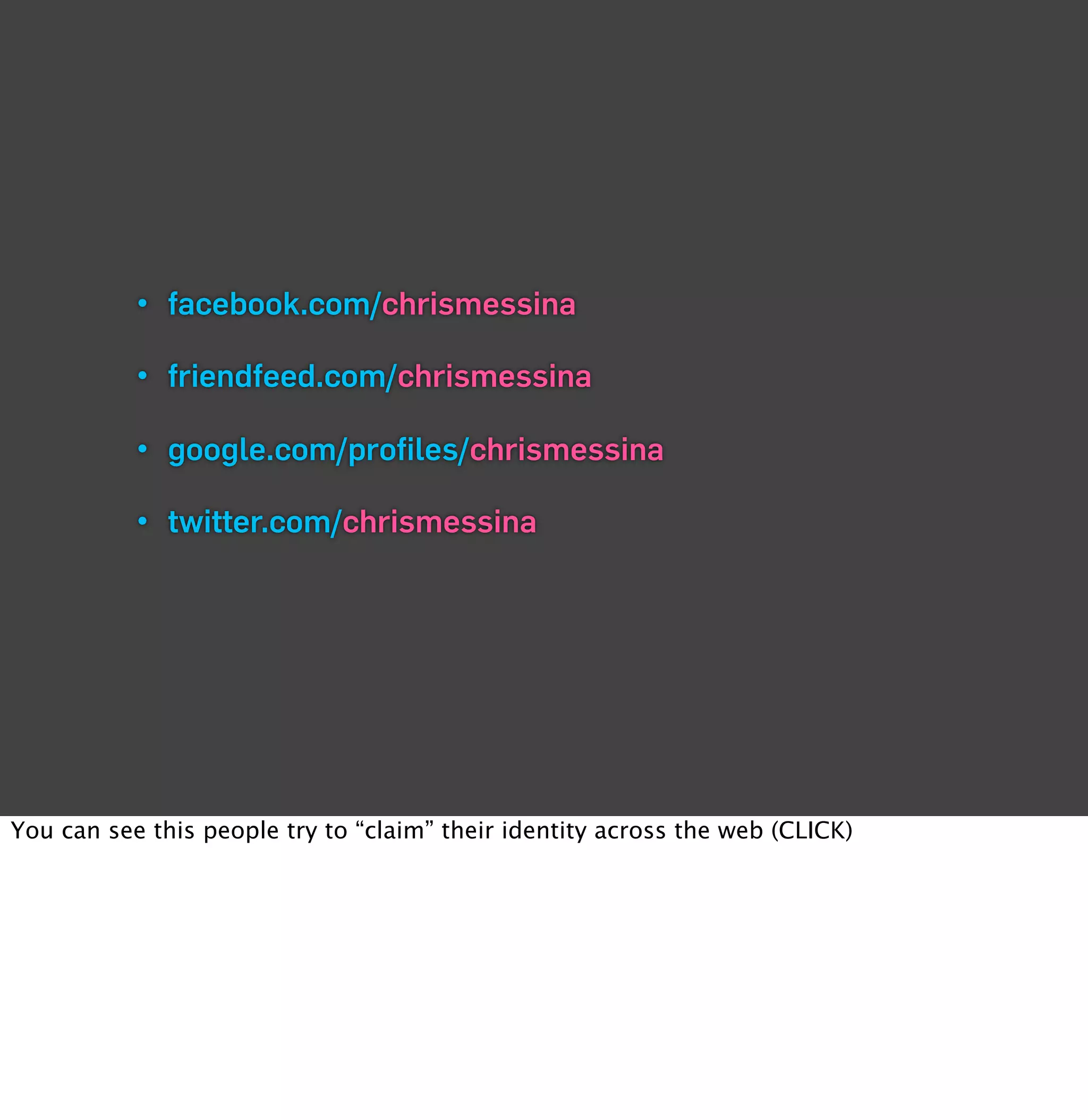
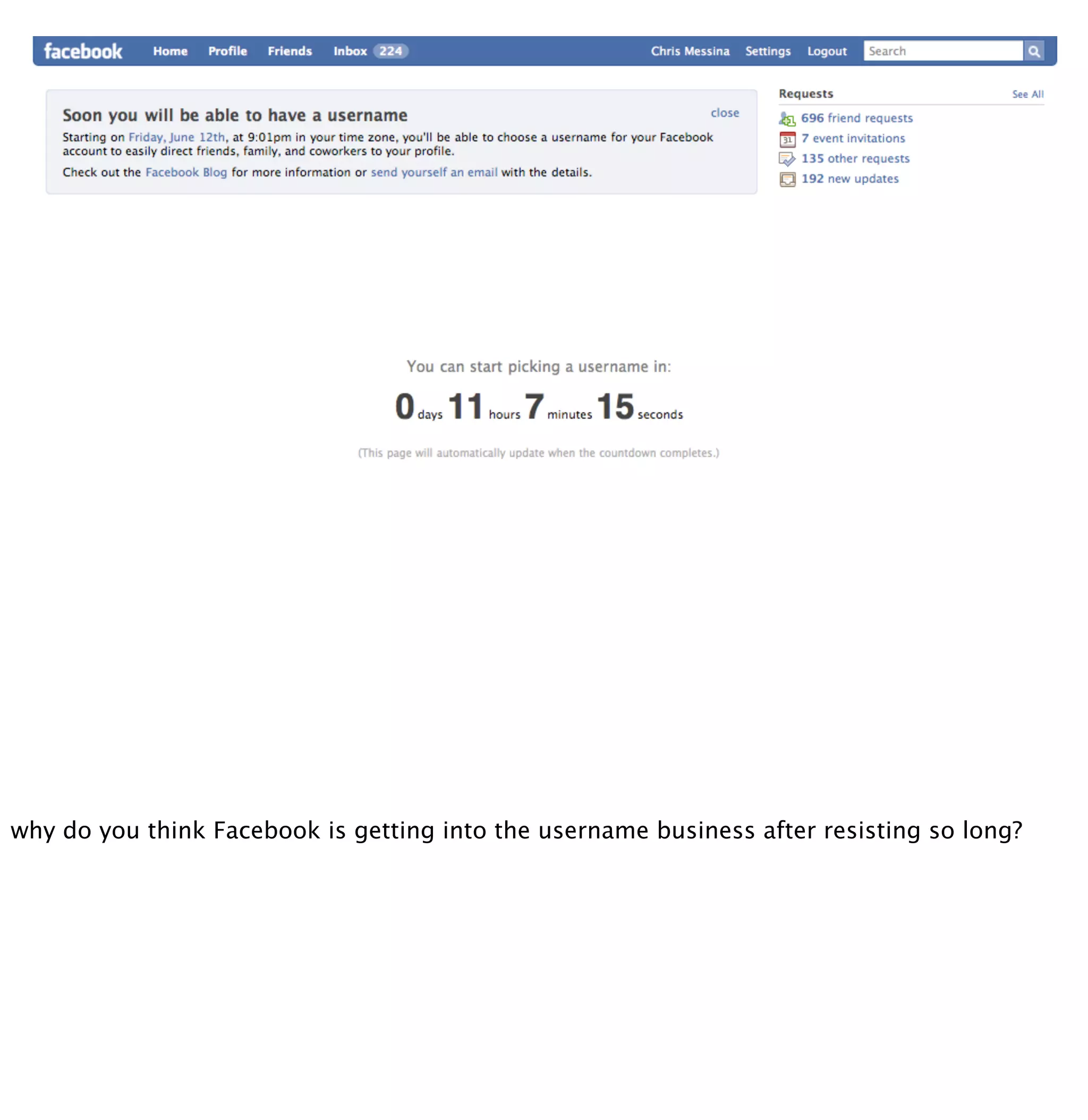
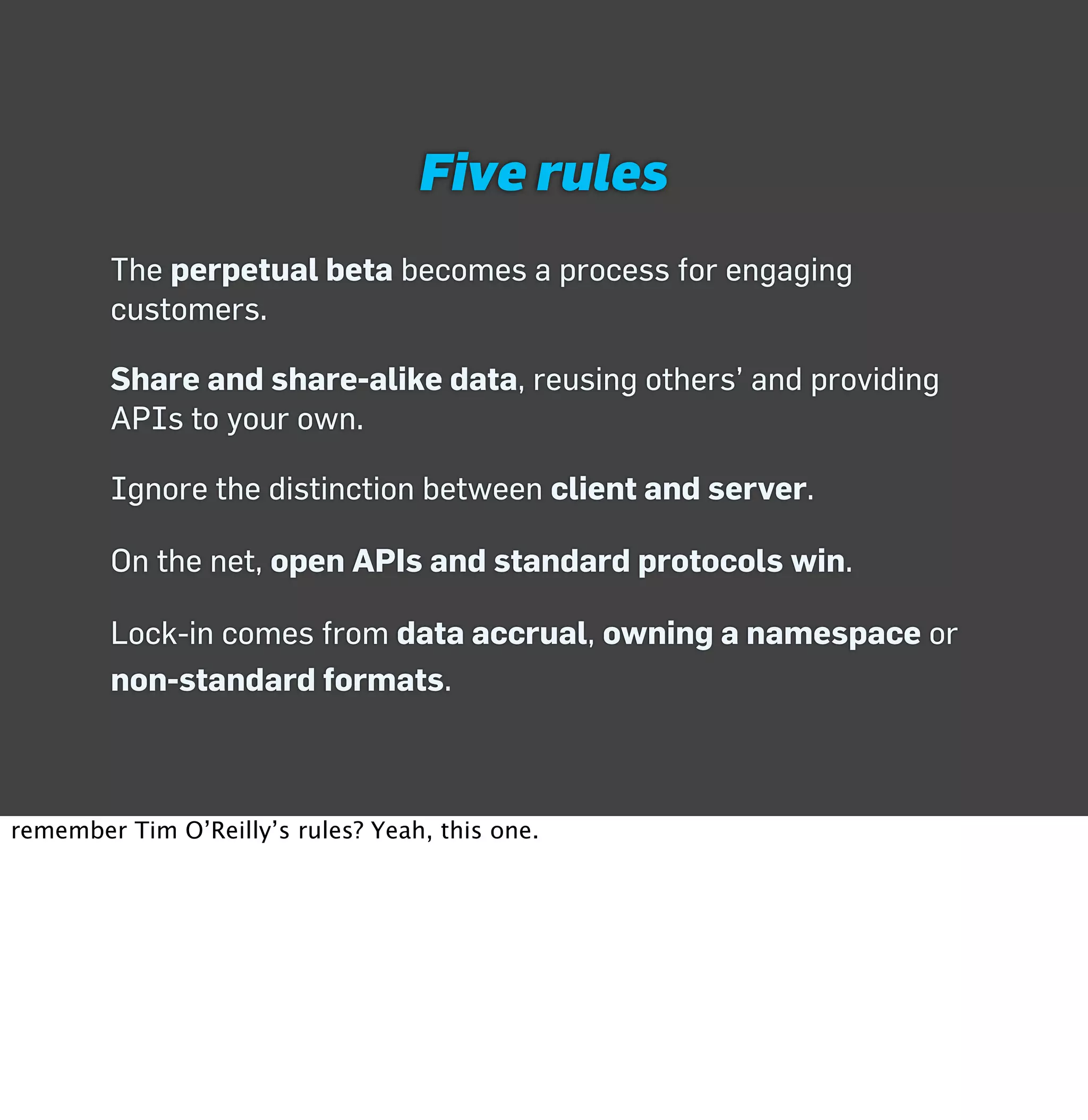
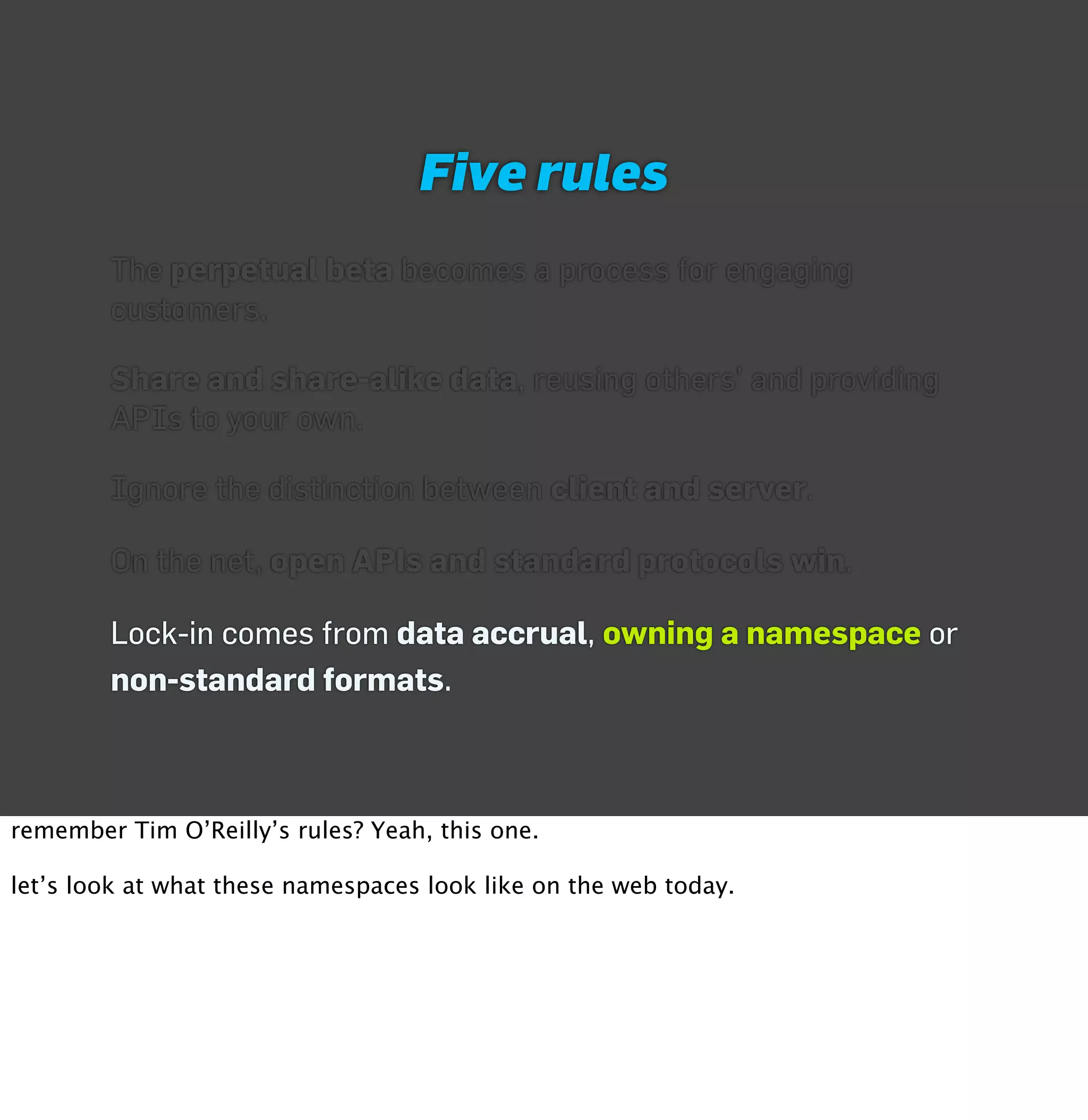
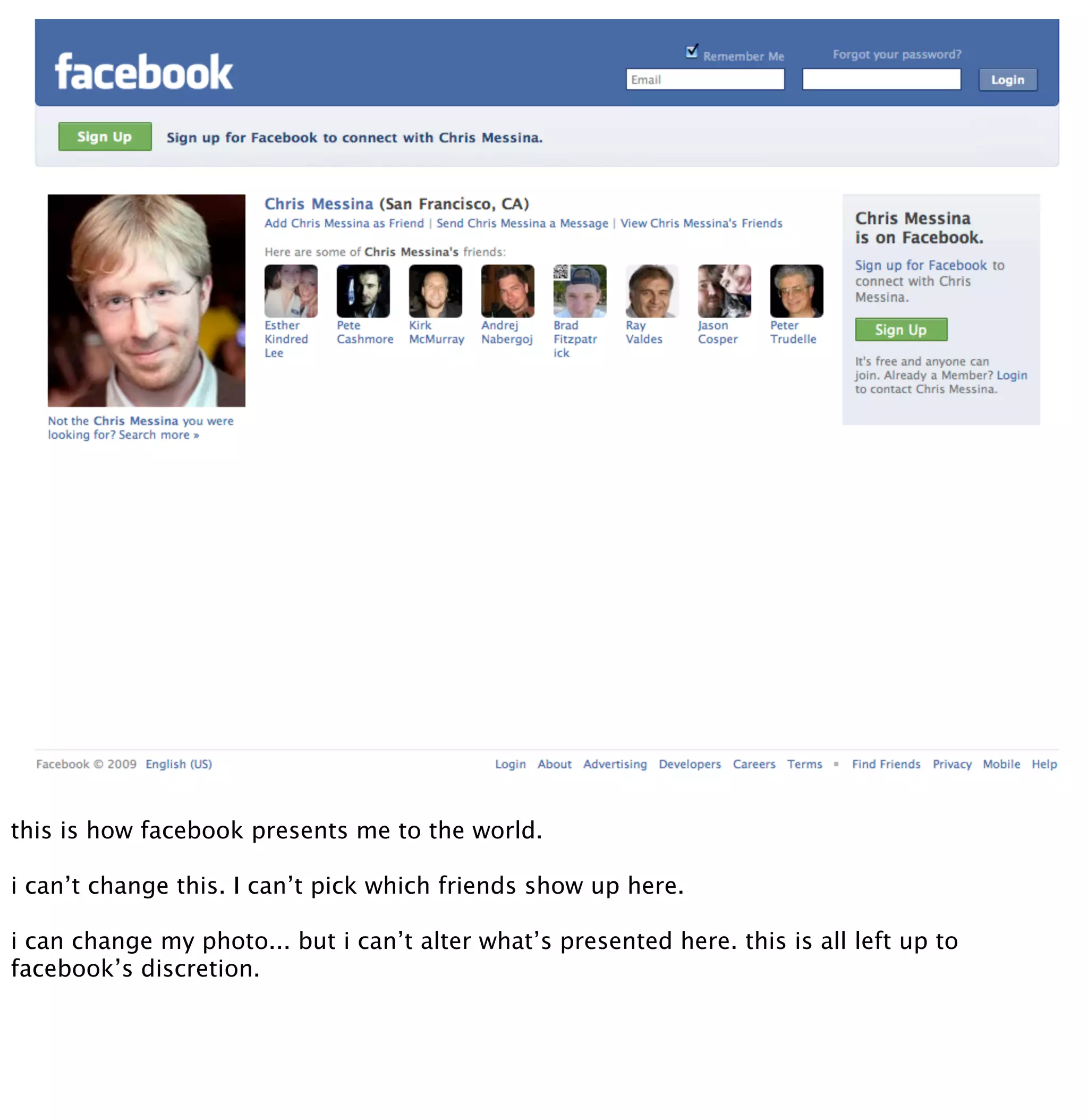
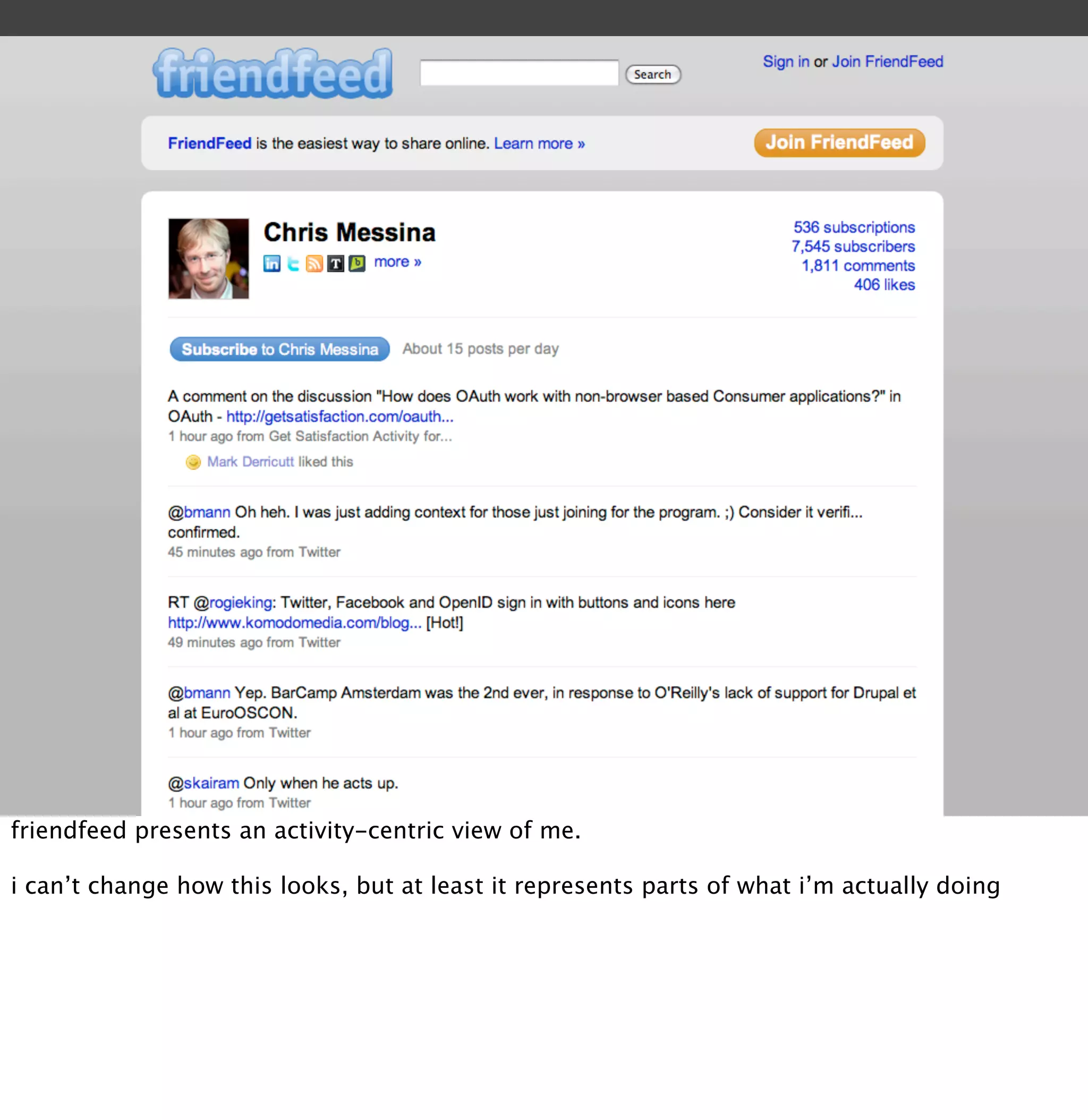
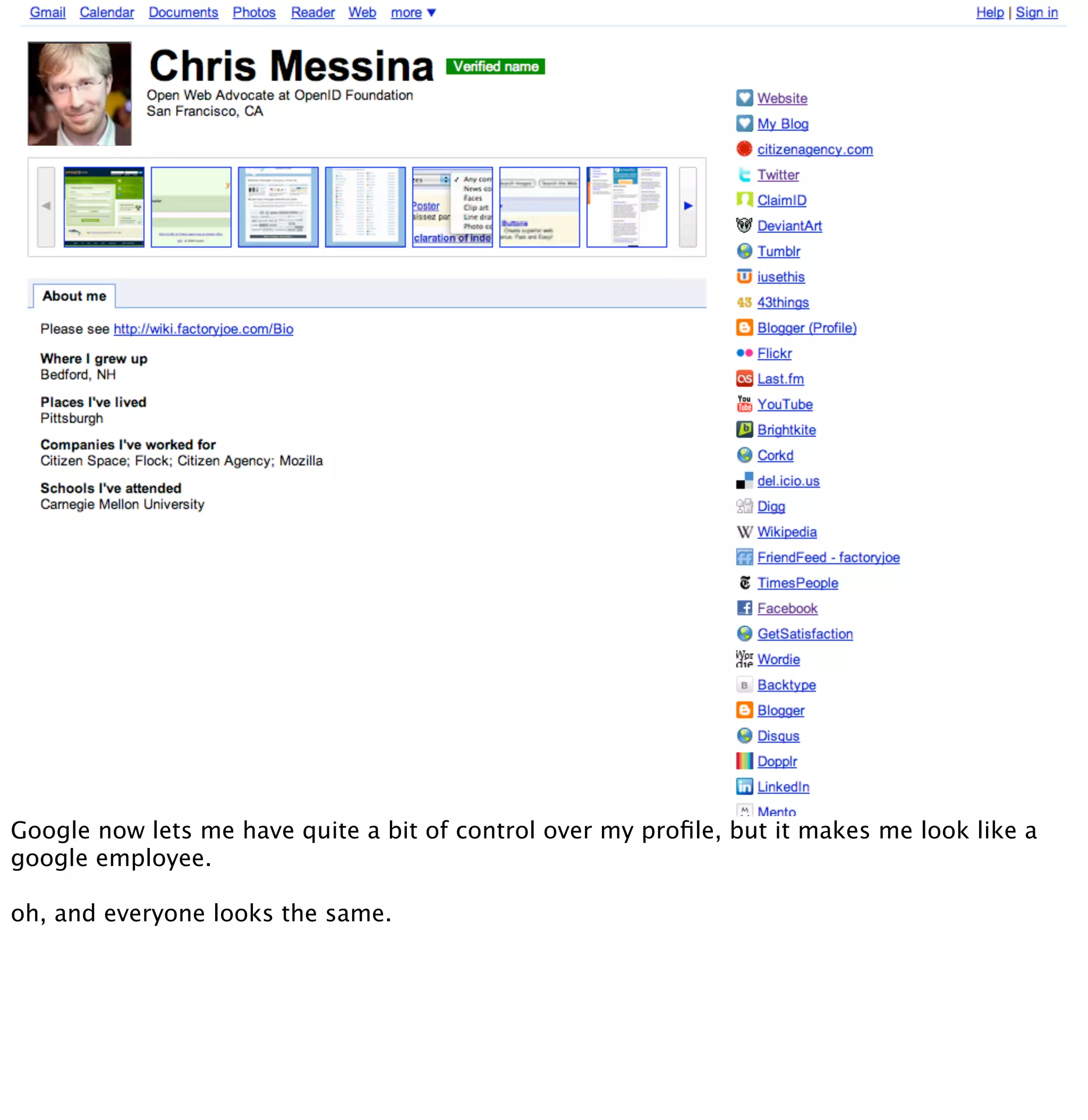
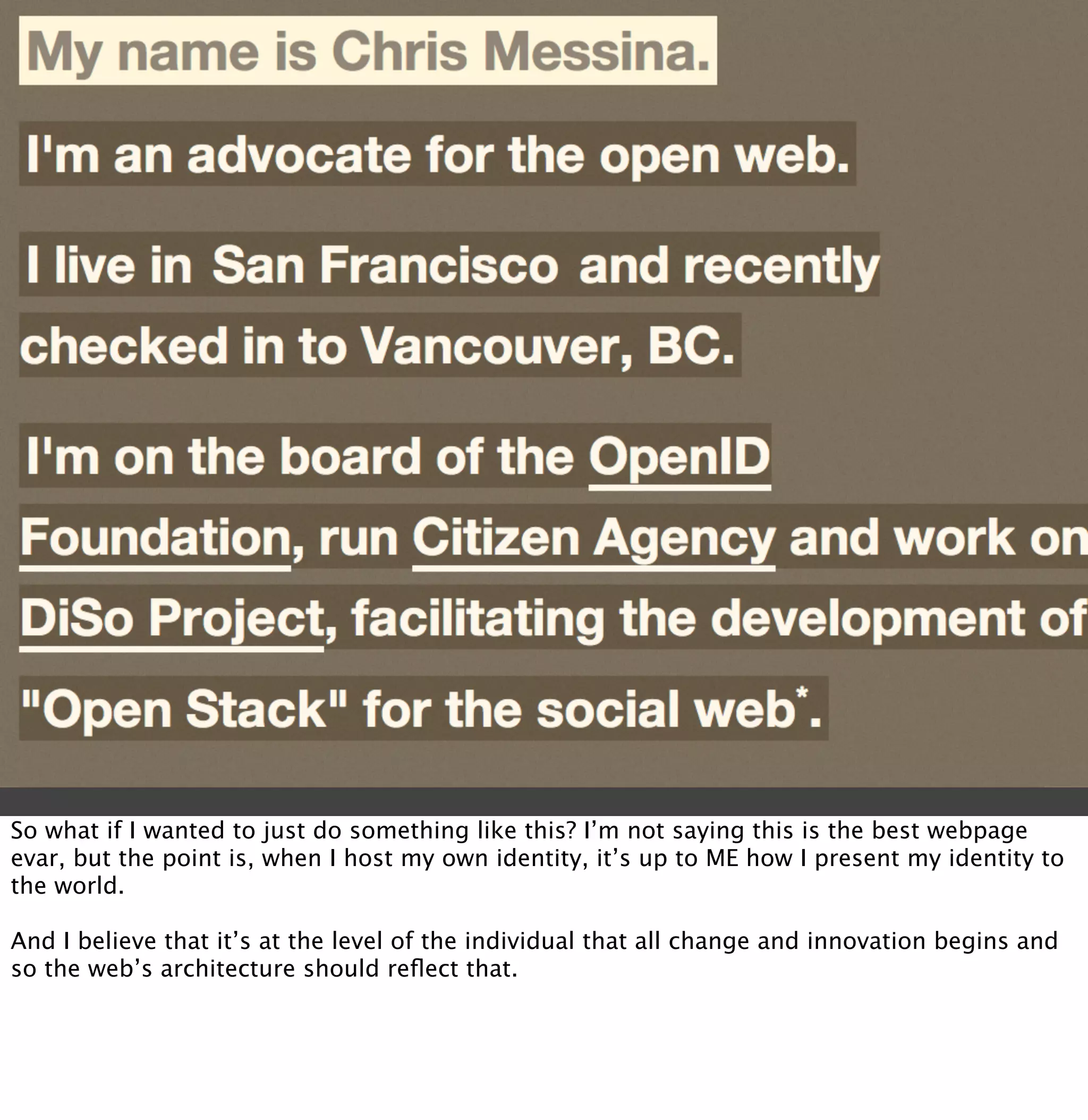
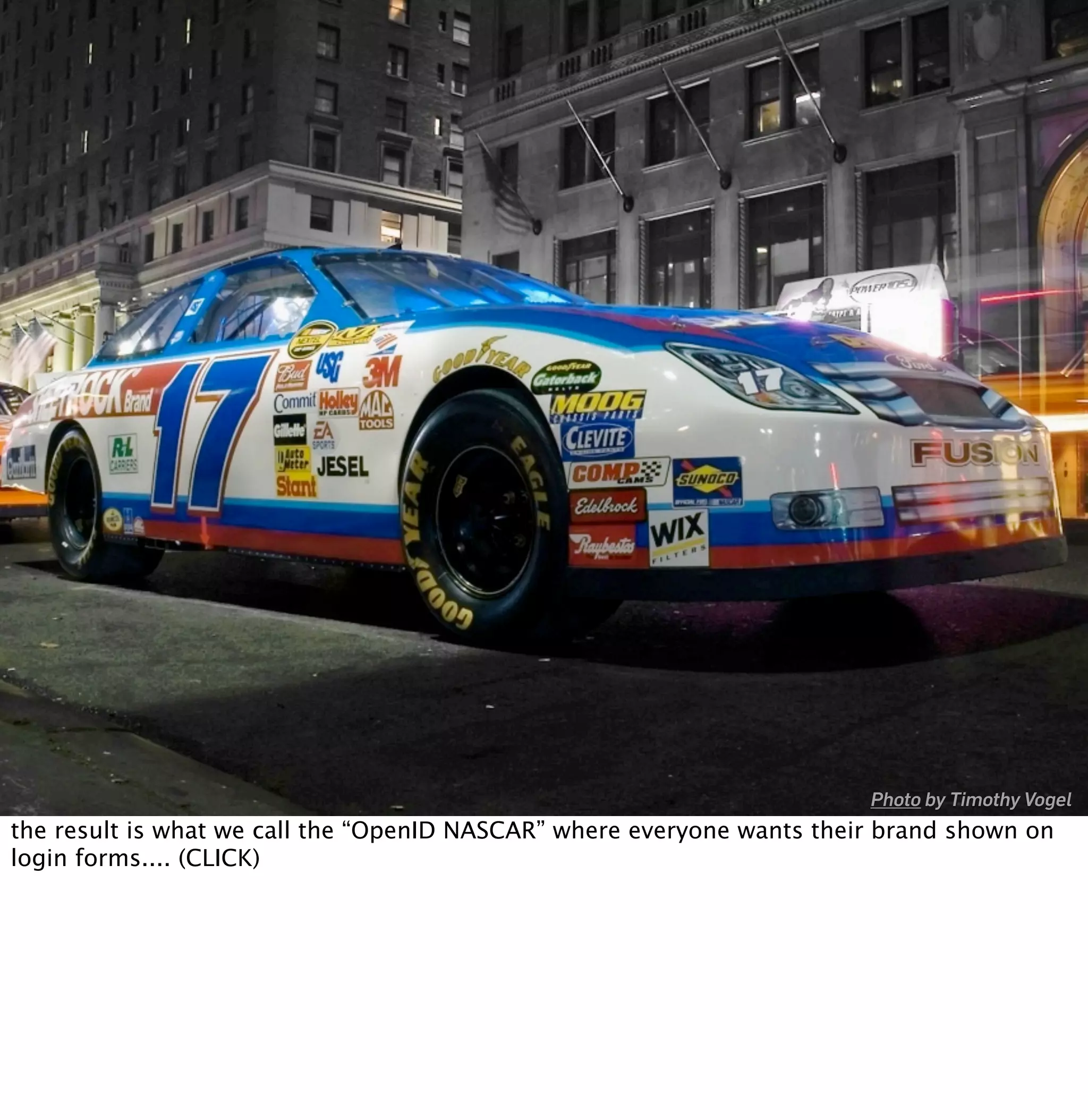
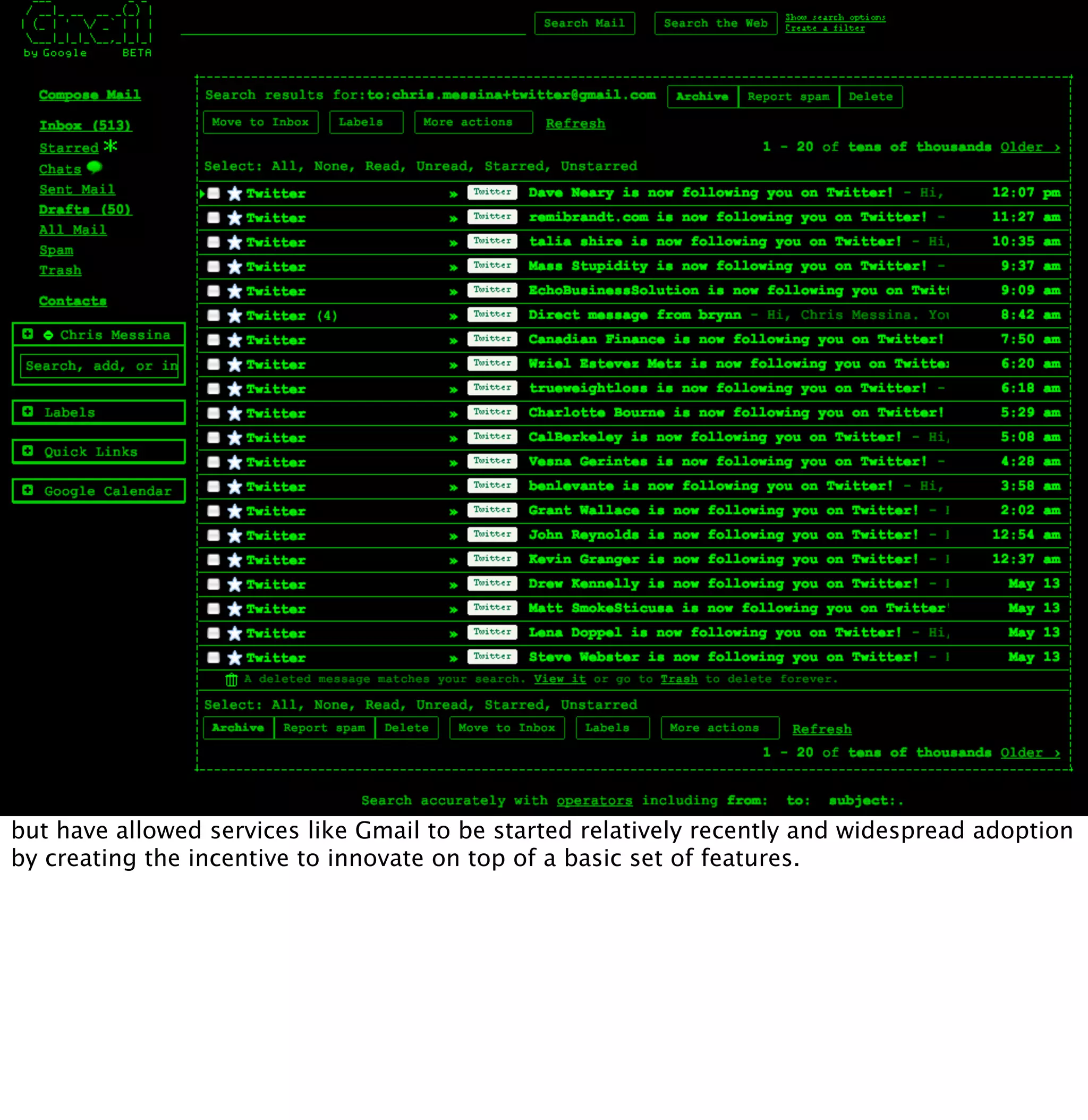
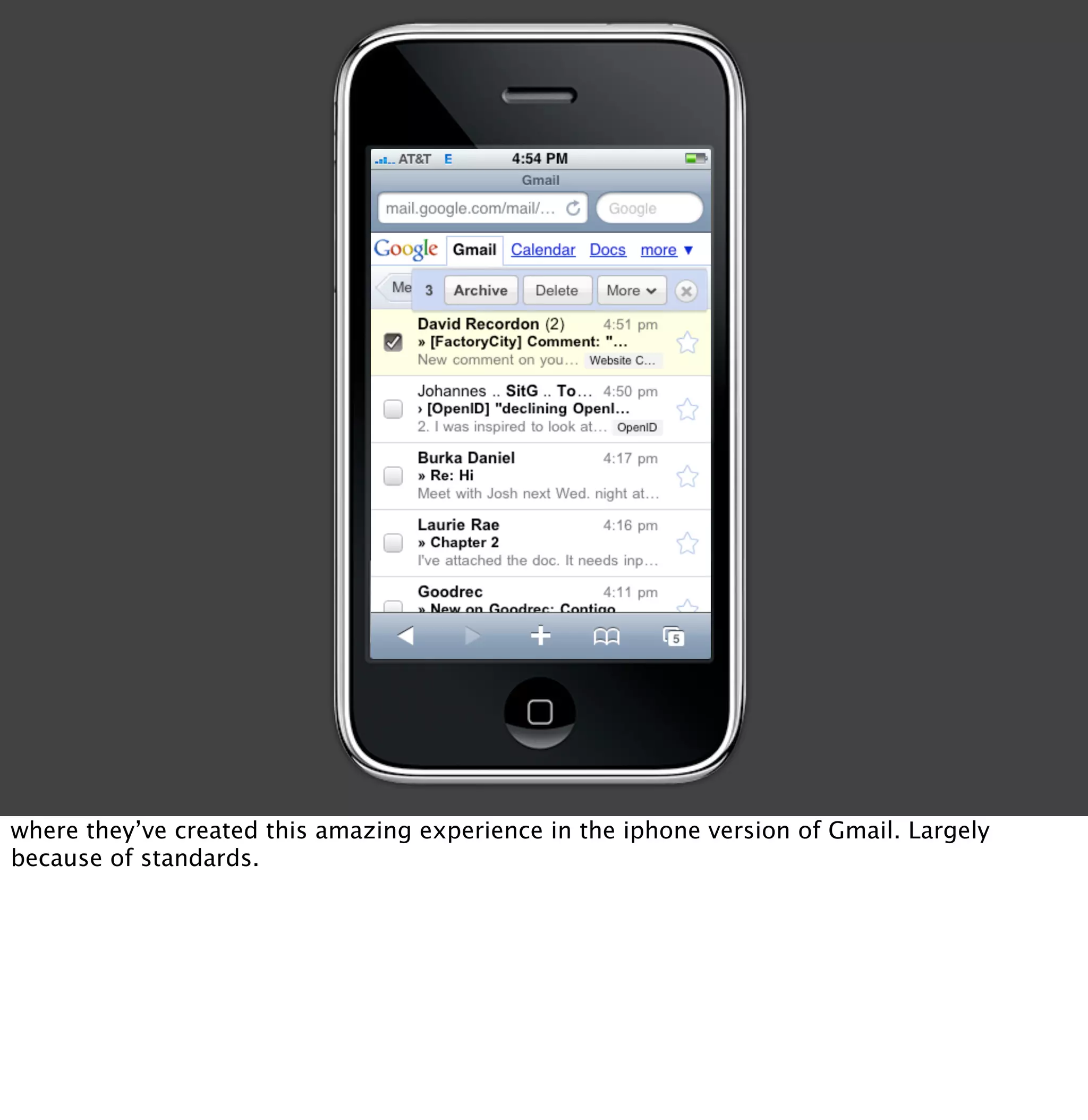
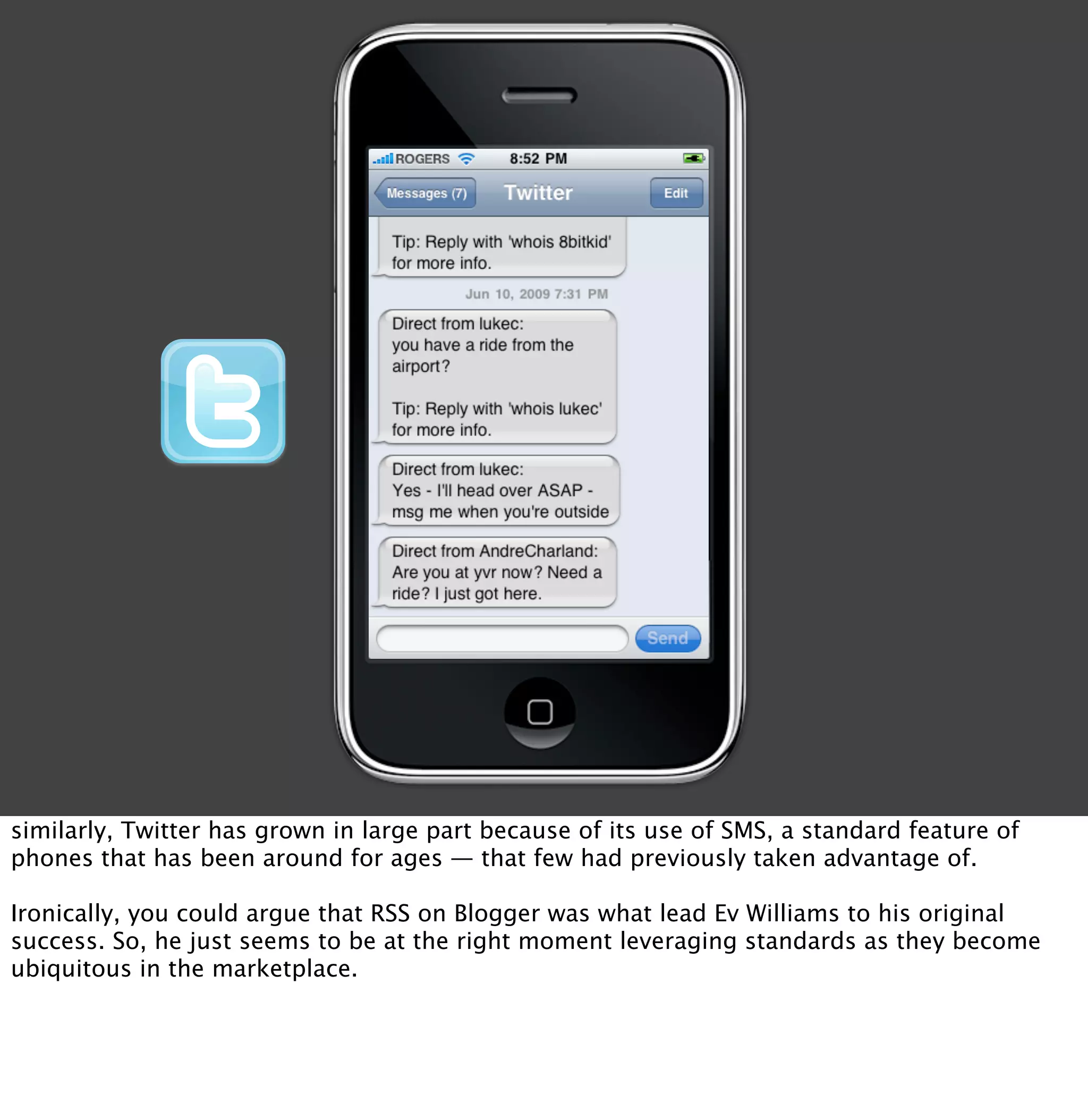
The document discusses the changing meaning of "openness" in the era of social computing. It notes that while open source software was once enough to ensure freedom, the rise of JavaScript, cloud computing, and social networks means individuals inherently rely on others. The talk aims to get the audience to reconsider what openness means today. It questions whether source code availability alone is sufficient, given issues around data, identity, and collaboration on social platforms.