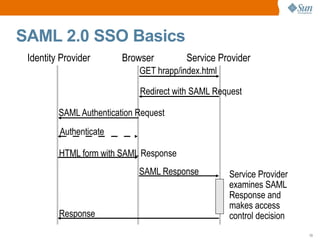
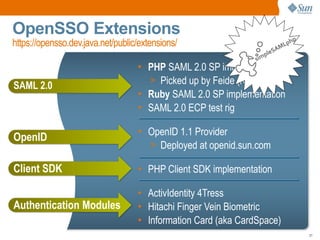
This document discusses identity management and single sign-on (SSO) within and between organizations. It introduces web access management and federation standards like SAML and WS-Federation that enable SSO beyond a single enterprise. OpenSSO is presented as an open source SSO solution that implements these standards and supports access management, federation, and identity services. The document encourages participation in the OpenSSO community and provides additional resources.