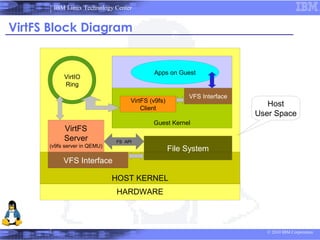
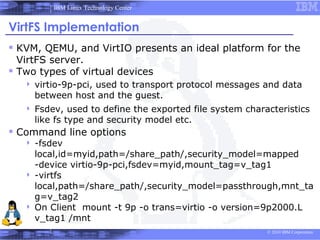
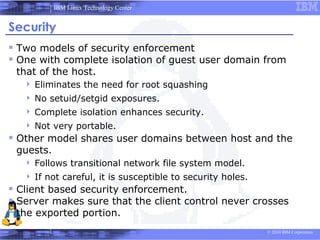
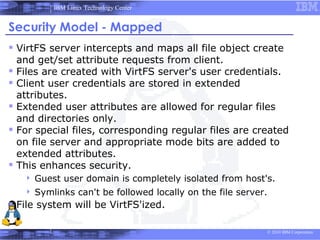
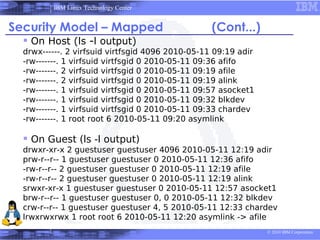
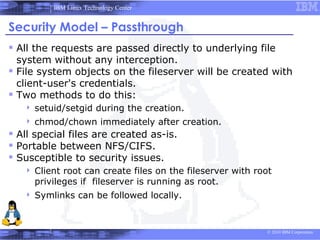
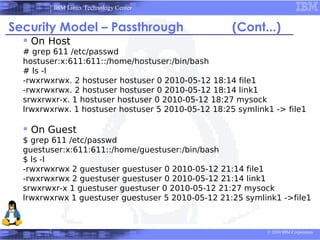
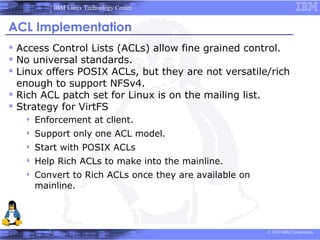
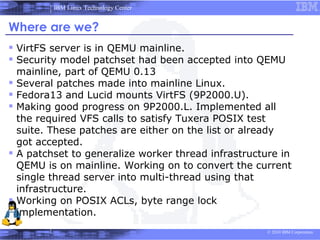
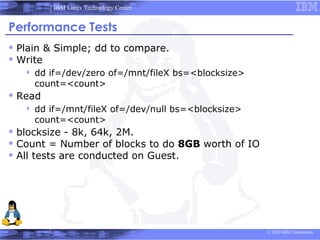
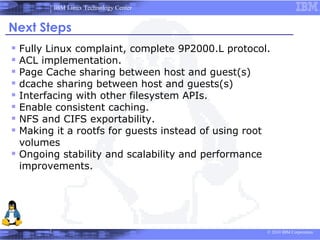
This document discusses VirtFS, a paravirtual file system that allows file system access between a KVM hypervisor and guest virtual machines. It uses the 9P protocol for communication and the VirtIO transport for efficient data transfer. The file system is exported from the host to guests using QEMU and provides security isolation of guest credentials from the host through user ID mapping.