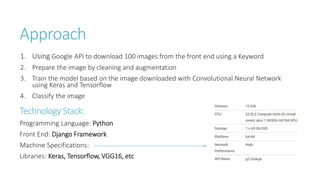
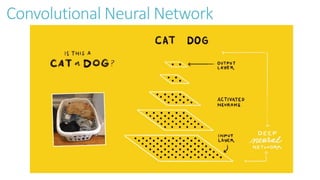
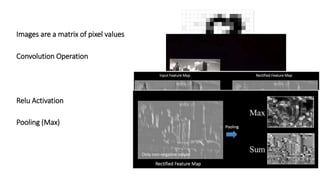
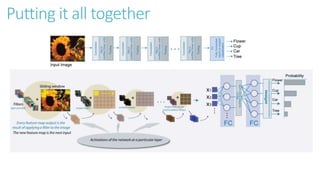
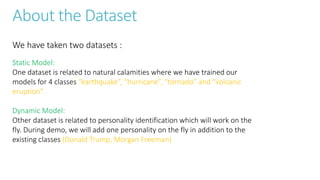
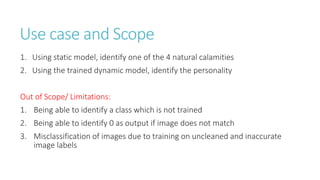
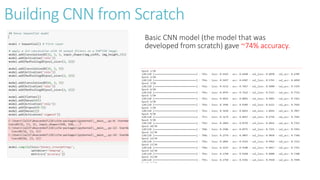
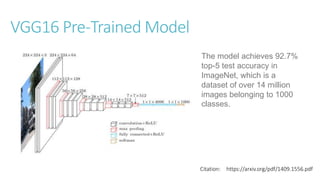
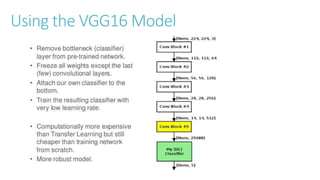
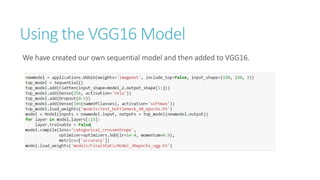
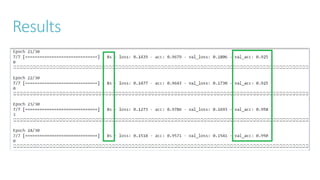
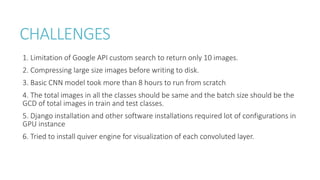
The document outlines a project focused on object classification using convolutional neural networks (CNN), involving the development of static and dynamic models to identify natural calamities and personalities. It details the technical approach, training process, improvements made through pre-trained models like VGG16, and challenges encountered during the project. Future research directions include applications such as facial keypoint detection and real-time criminal detection.