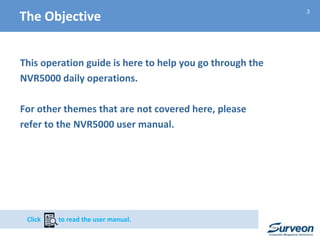
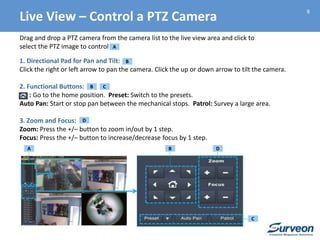
This 3-sentence summary provides an overview of the Surveon NVR5000 Operation Guide:
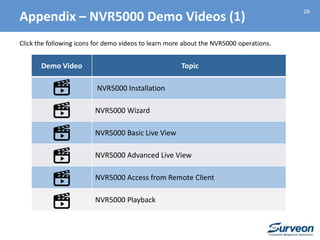
The document outlines how to operate the NVR5000 system for live viewing, playback, system configurations, maintenance, and troubleshooting. It describes the live view interface and controls for cameras, as well as how to perform playback by date or event. The appendix section lists additional useful resources and demo videos that are available on the Surveon website.

![11
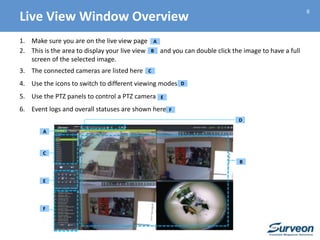
1. Make sure you are on the live view page
2. Right click on the selected camera image to see the options and select Instant Playback,
and then select [Time Length] (ex: 20 minutes)
3. A floating window will open with the desired playback
A
A
B C
B
C
Playback – Instant Playback from Live View](https://image.slidesharecdn.com/mscptn503nvr5000operationguide20150216-150216203319-conversion-gate02/85/Surveon-NVR5000-Operation-Guide-11-320.jpg)