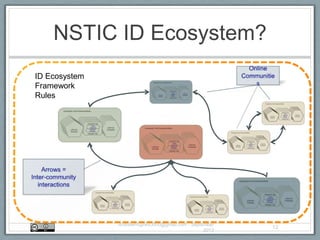
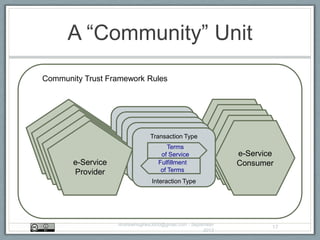
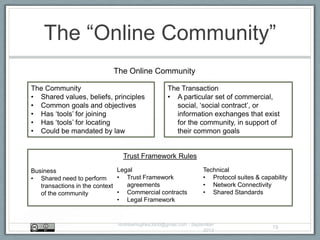
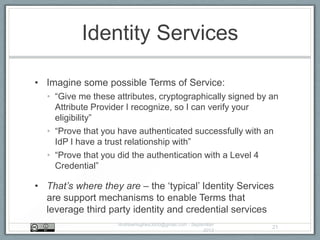
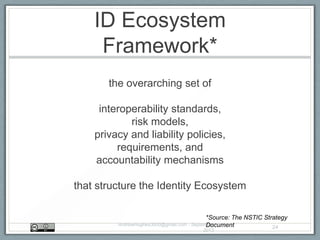
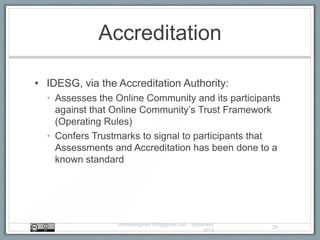
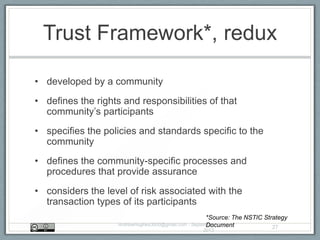
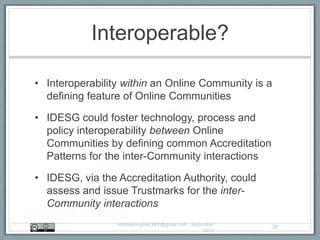
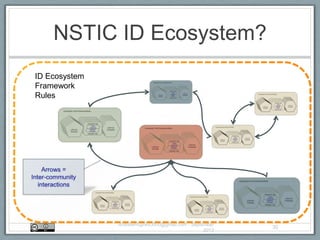
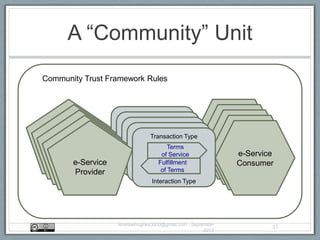
The document outlines a conceptual model for the NSTIC ID ecosystem, which emphasizes the role of online communities that utilize interoperable technologies for accessing identity solutions. It describes the ecosystem's framework, focusing on how these communities interact, define their own policies, and the accreditation process necessary for participation. The model aims to enhance access to online services while ensuring trust, privacy, and security among users.