Embed presentation
Download to read offline
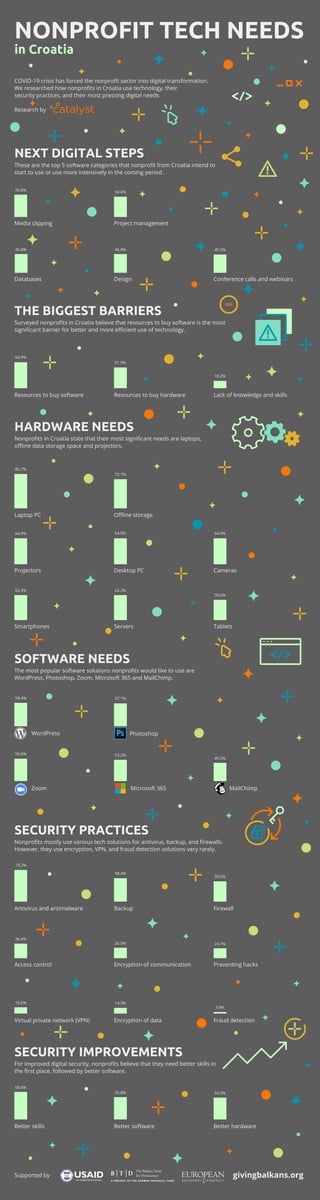

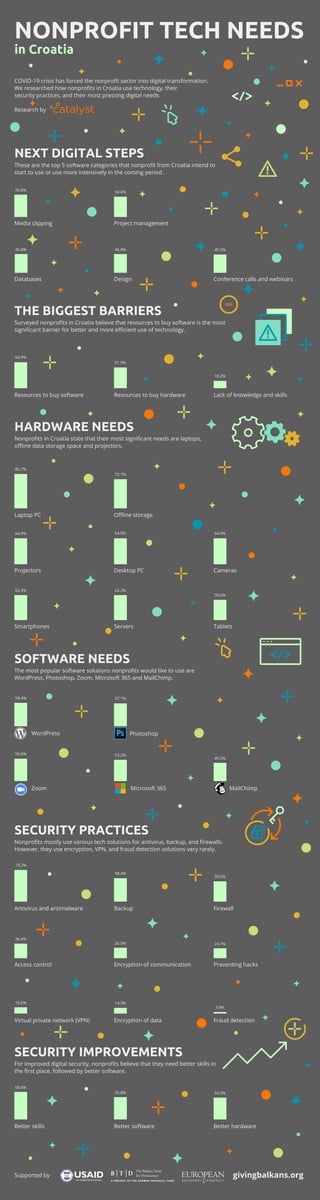
Research on digital needs among nonprofits in Croatia reveals that significant barriers to technology use include a lack of resources to purchase software and hardware, as well as insufficient digital skills. The most desired software includes platforms like Microsoft 365, Photoshop, and Zoom, while security practices such as encryption and VPN are rarely employed. The COVID-19 crisis has expedited the digital transformation in the sector, emphasizing the necessity for improved security practices and software usage.