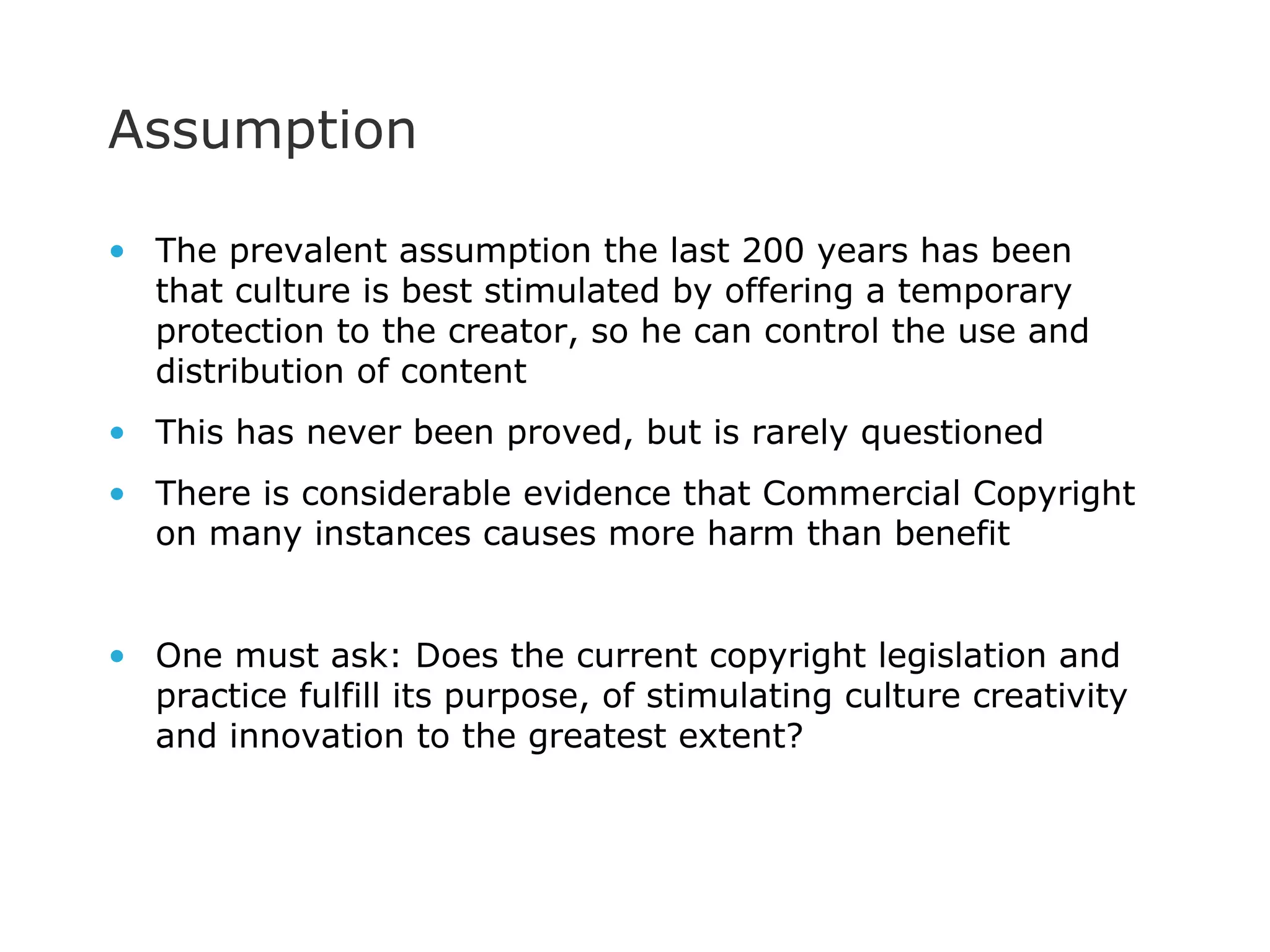
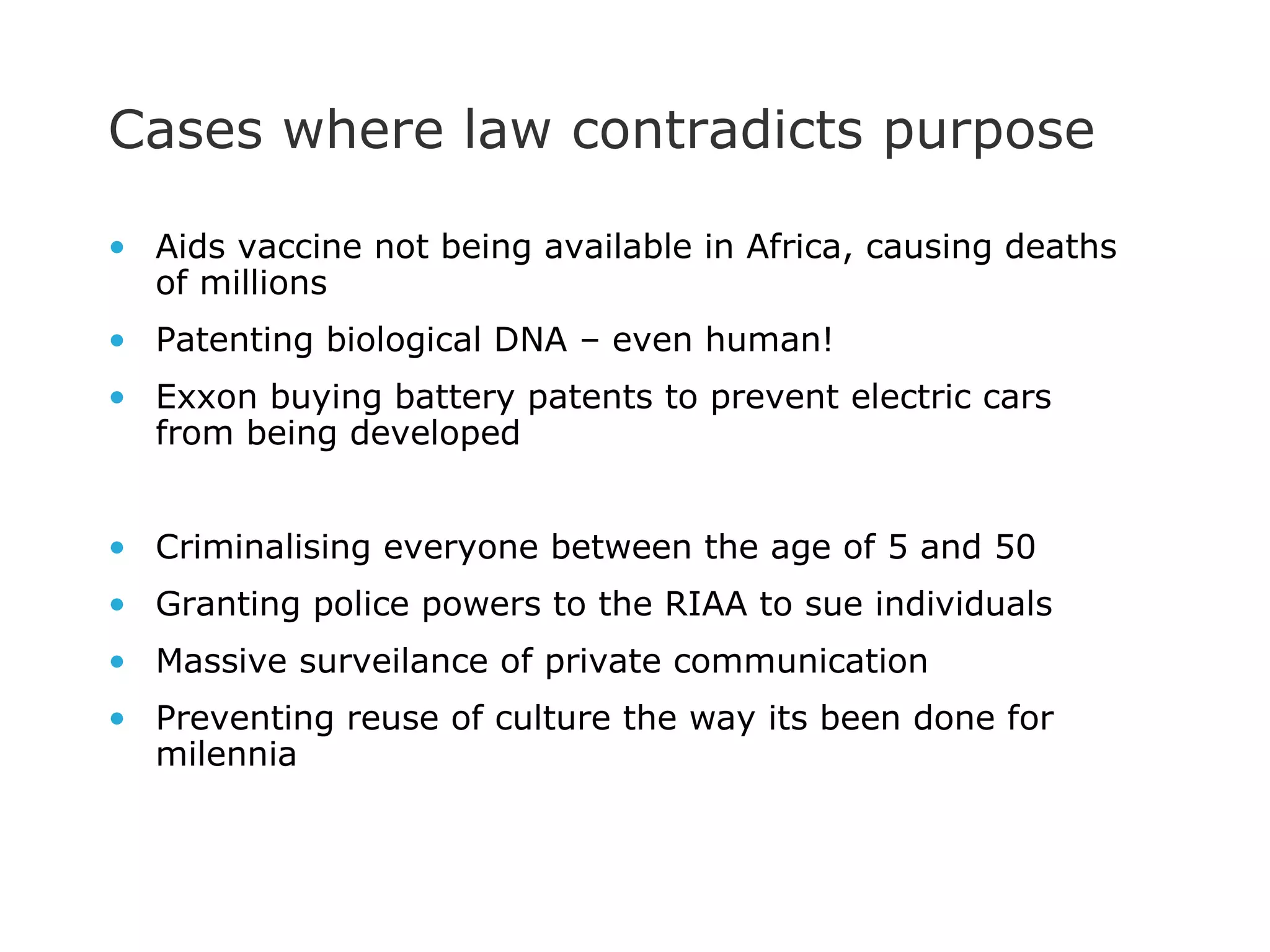
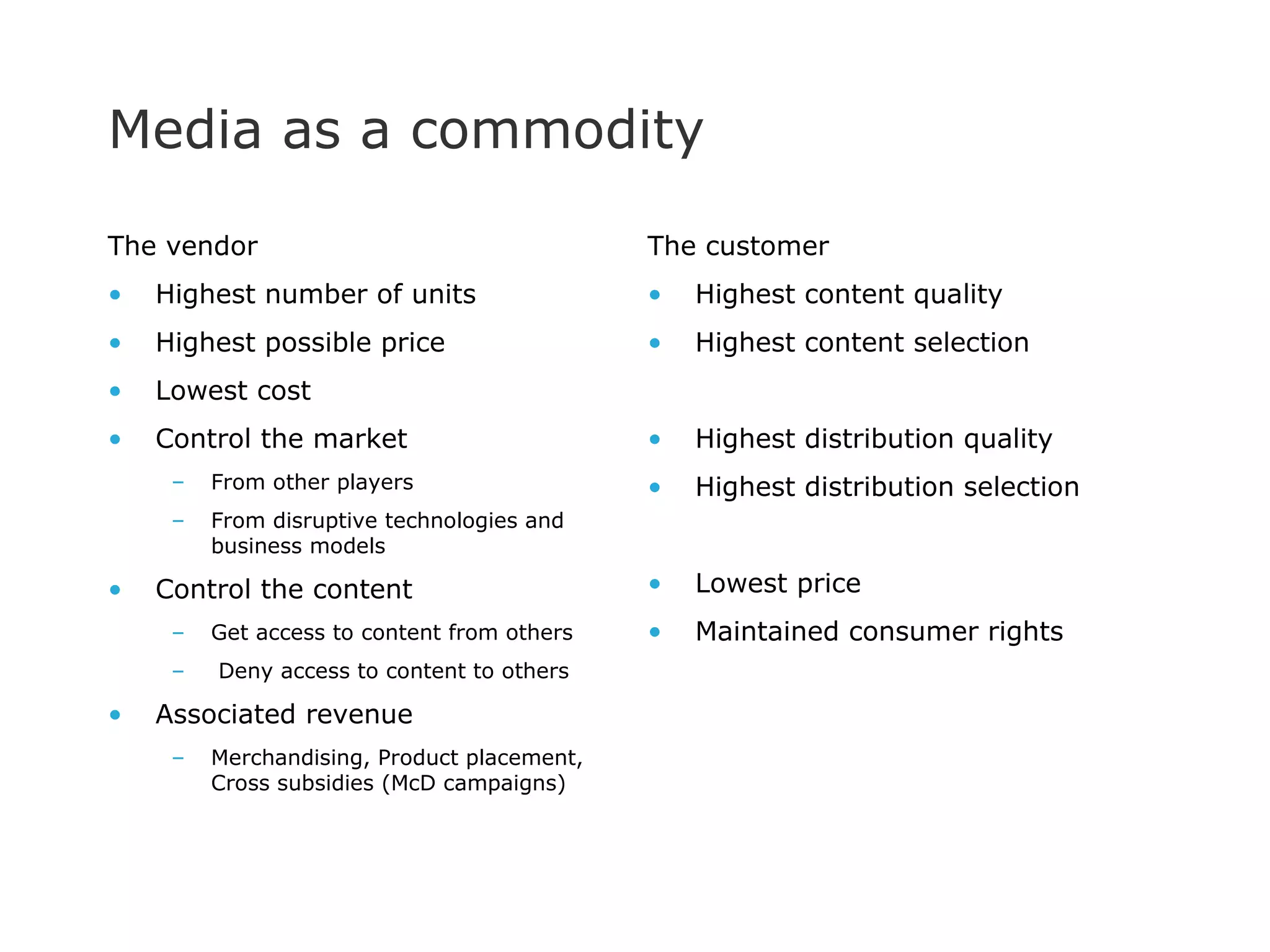
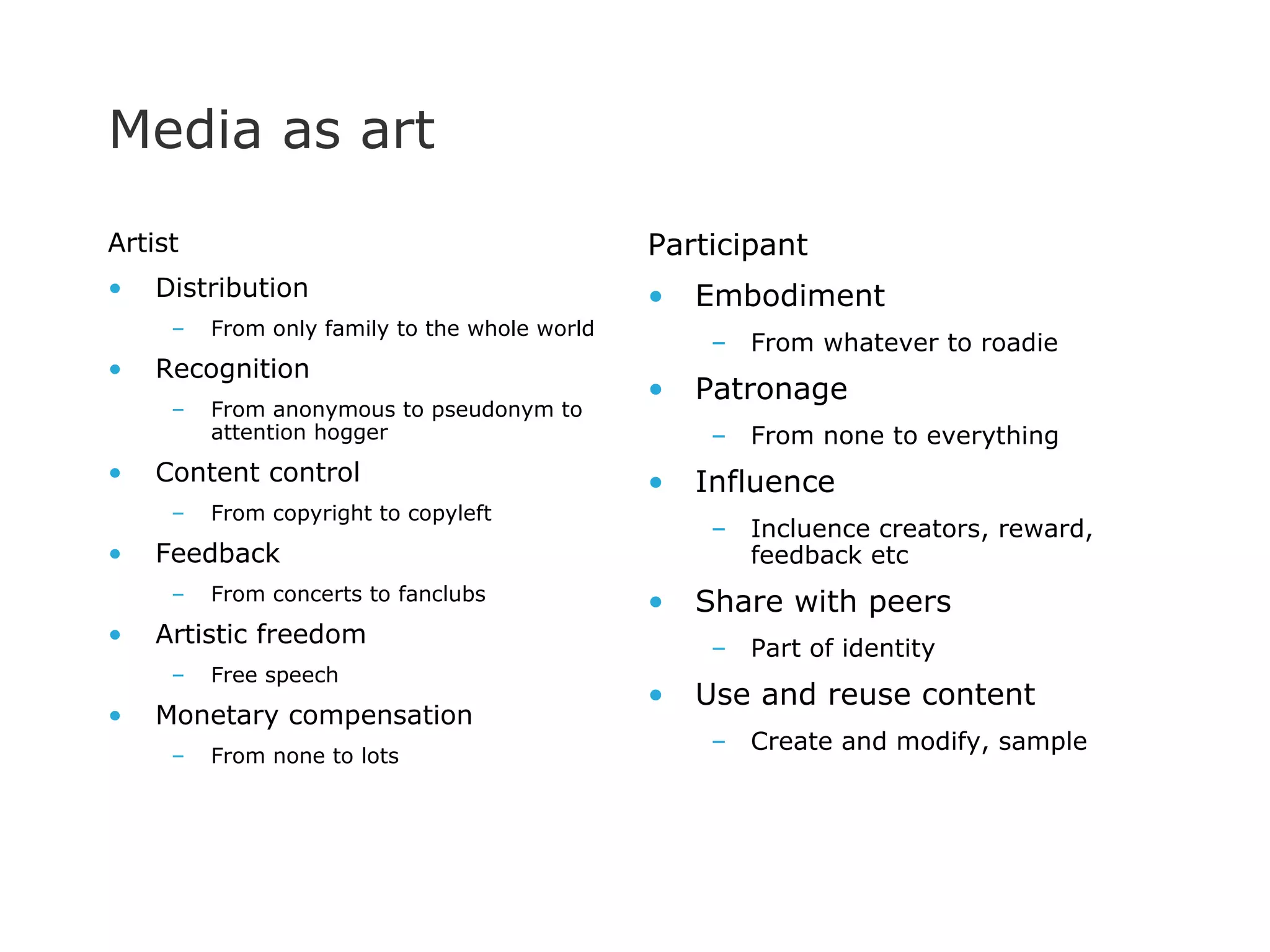
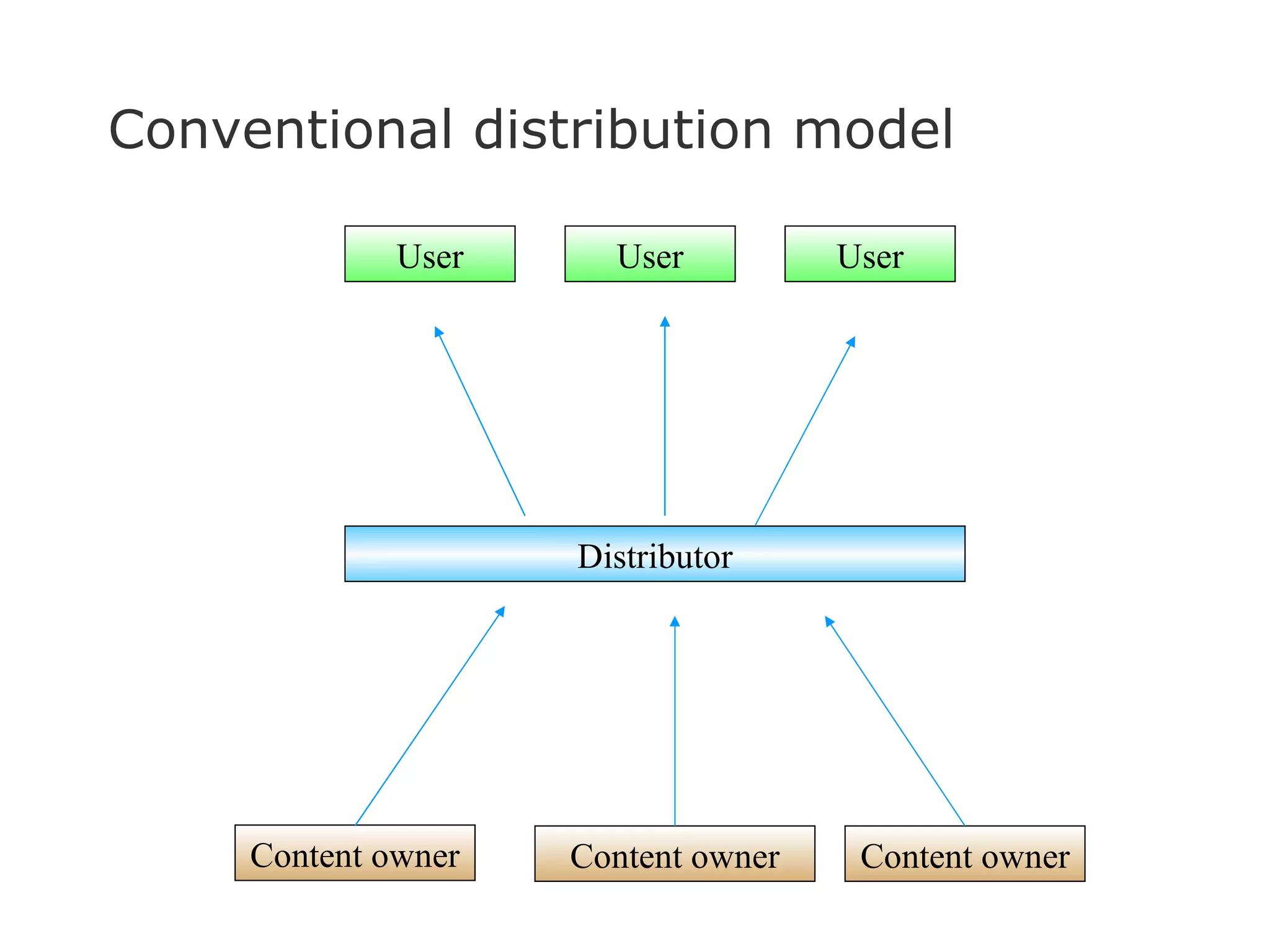
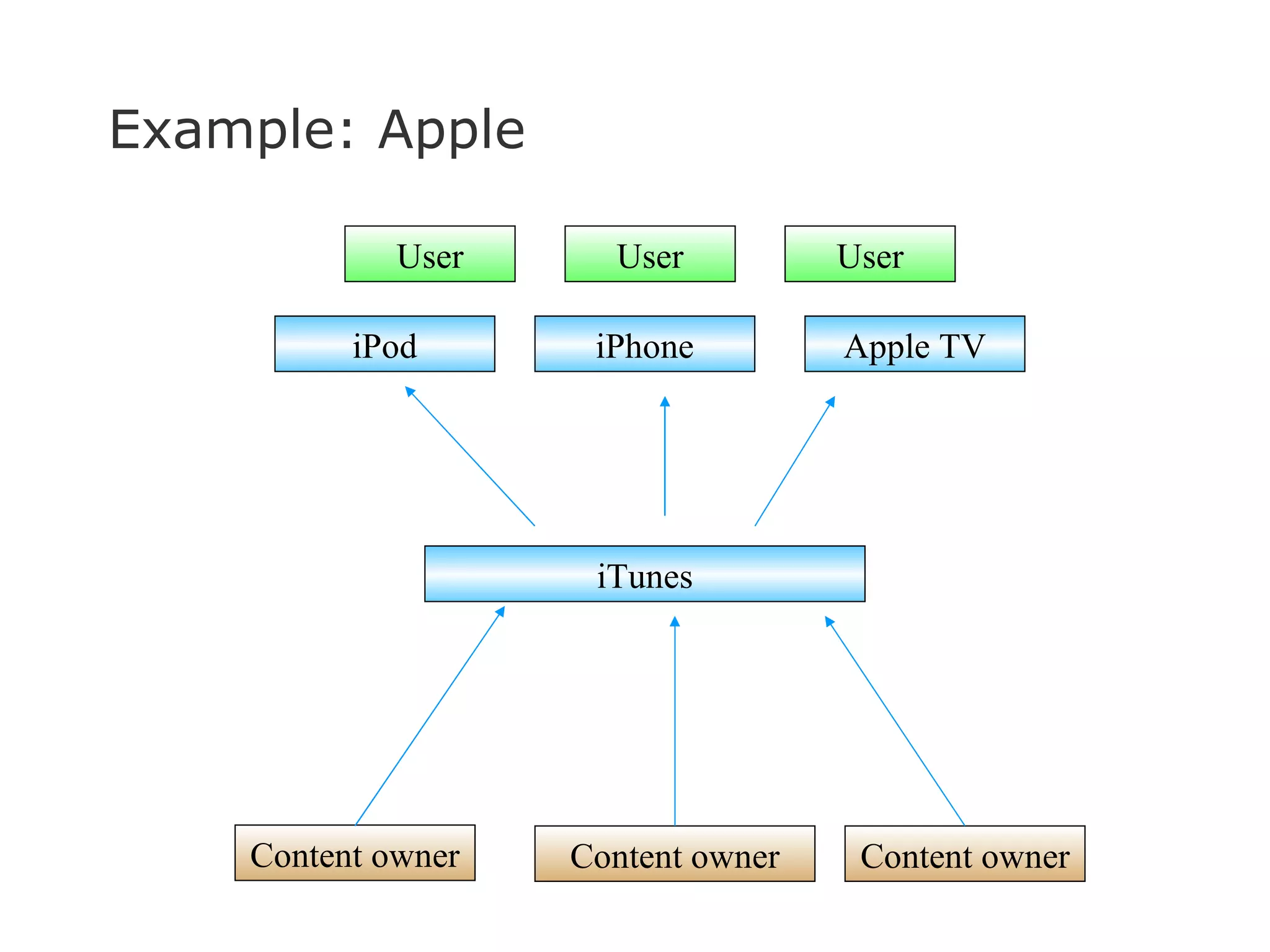
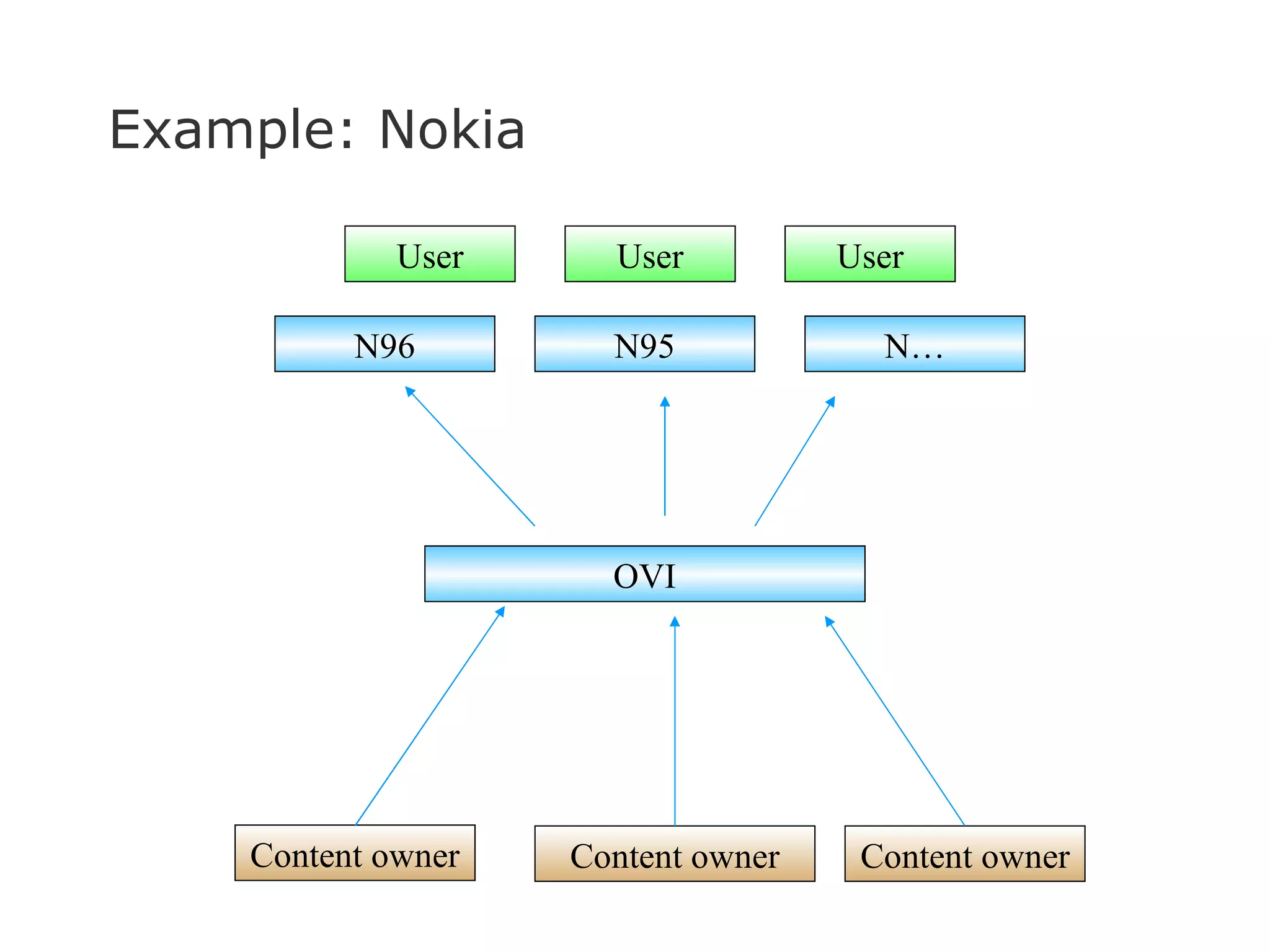
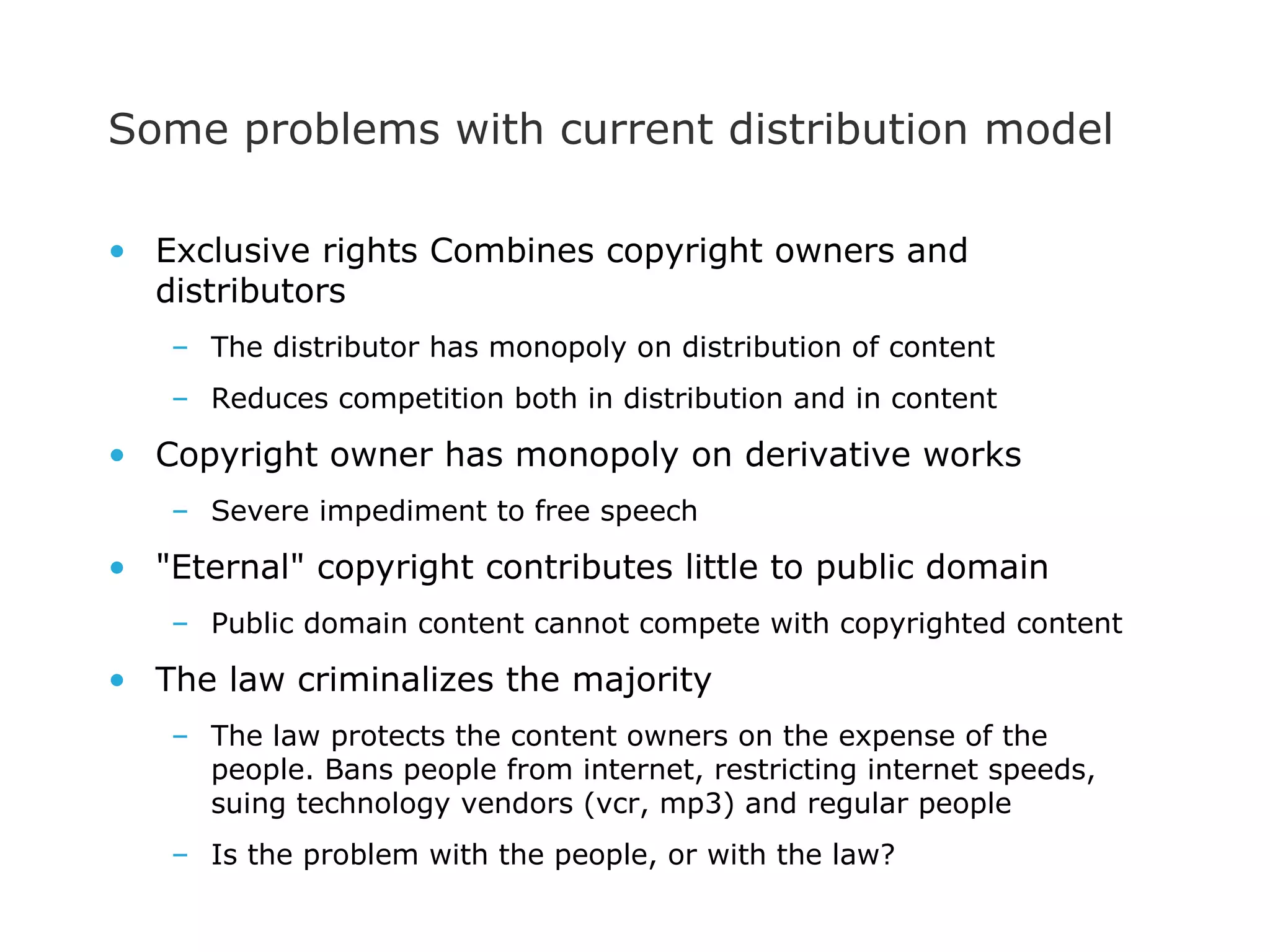
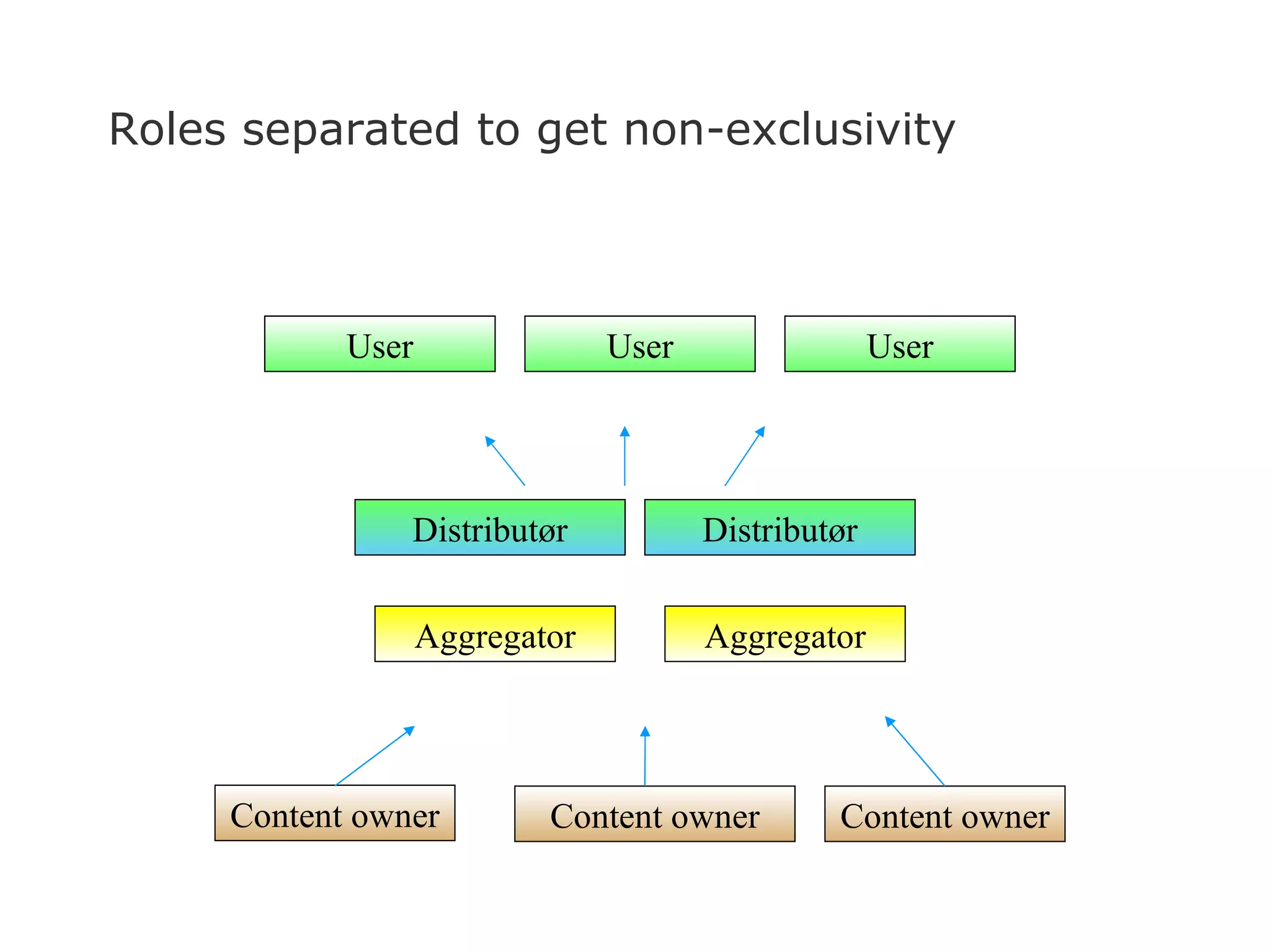
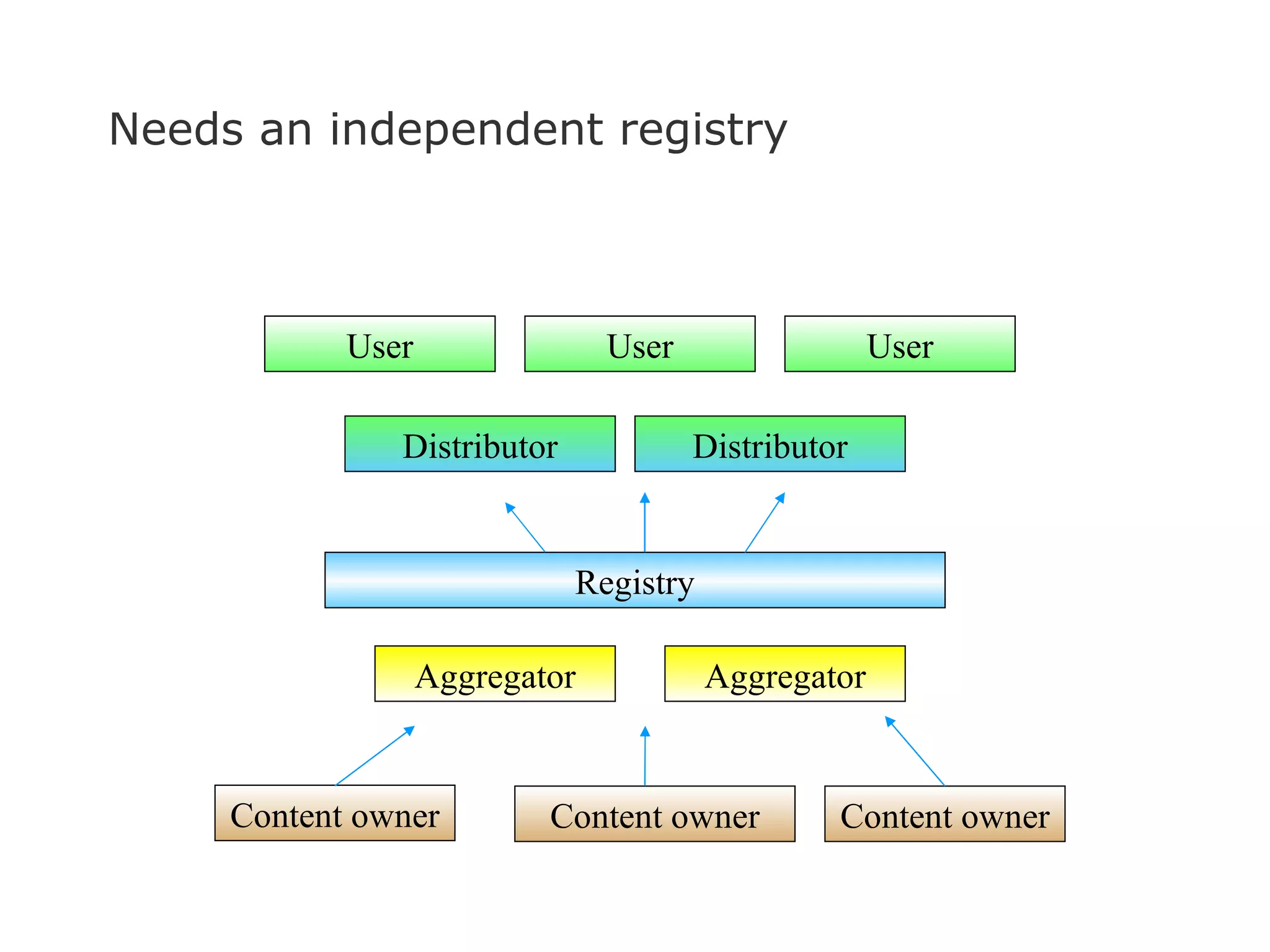
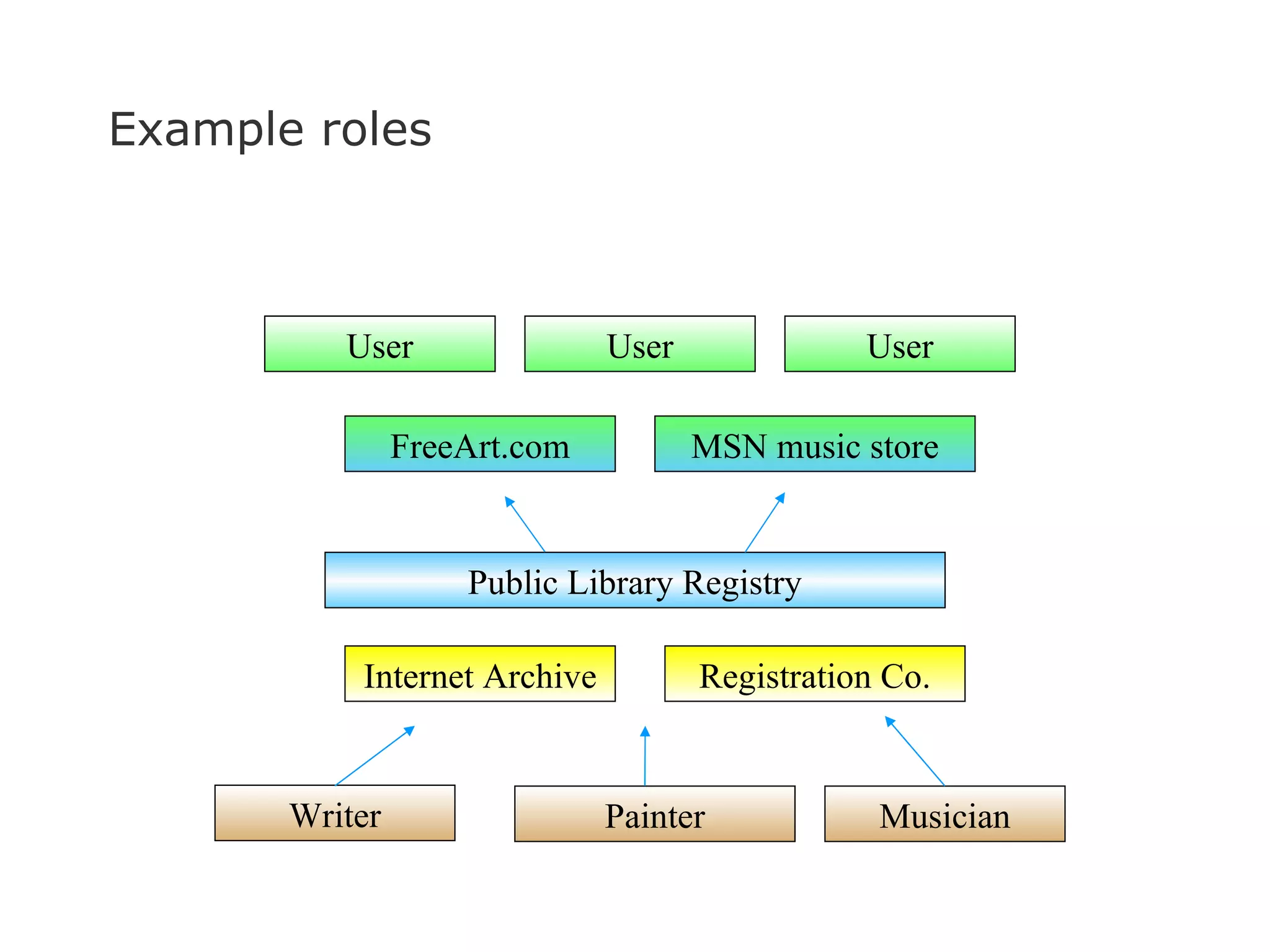
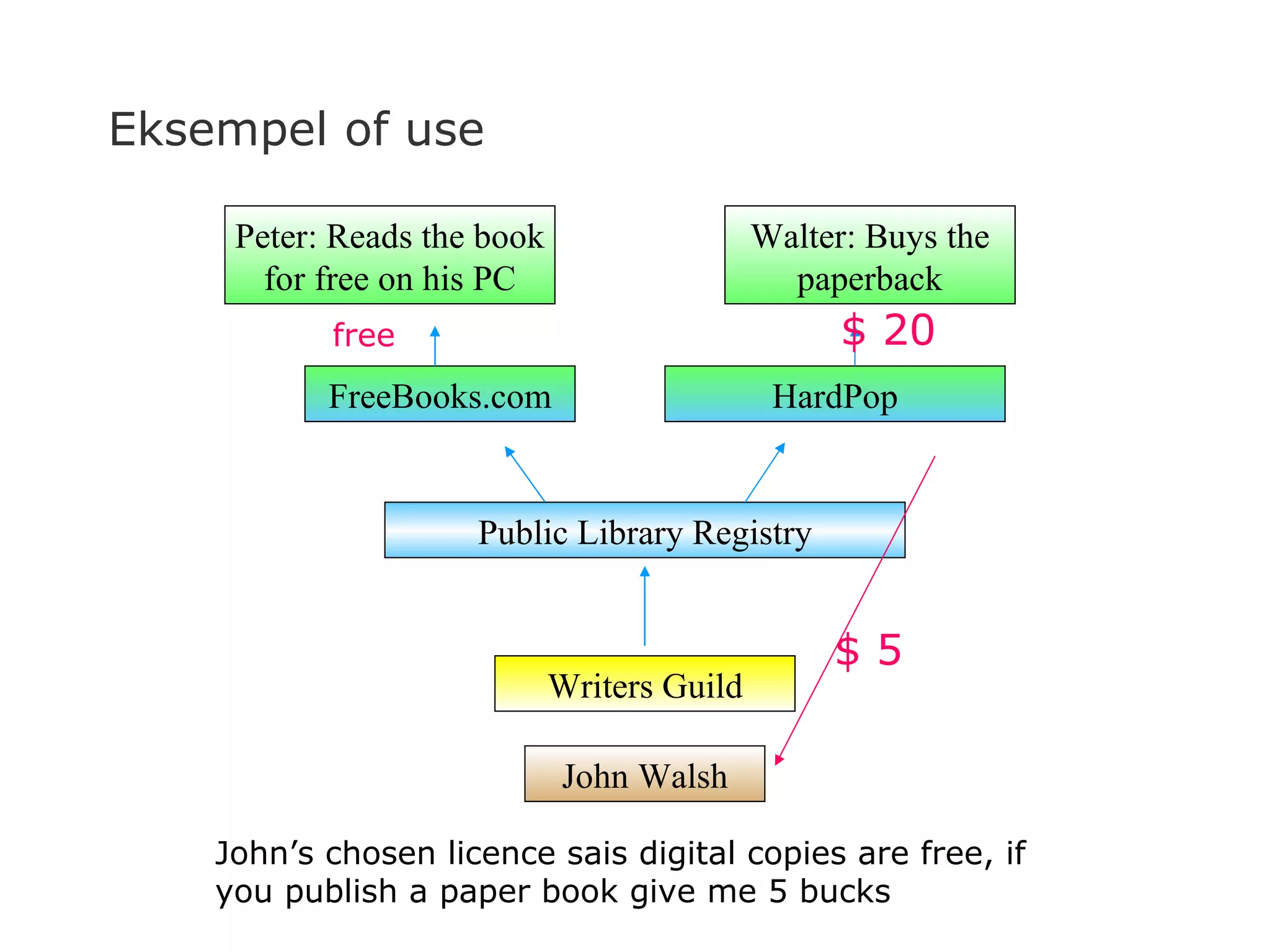
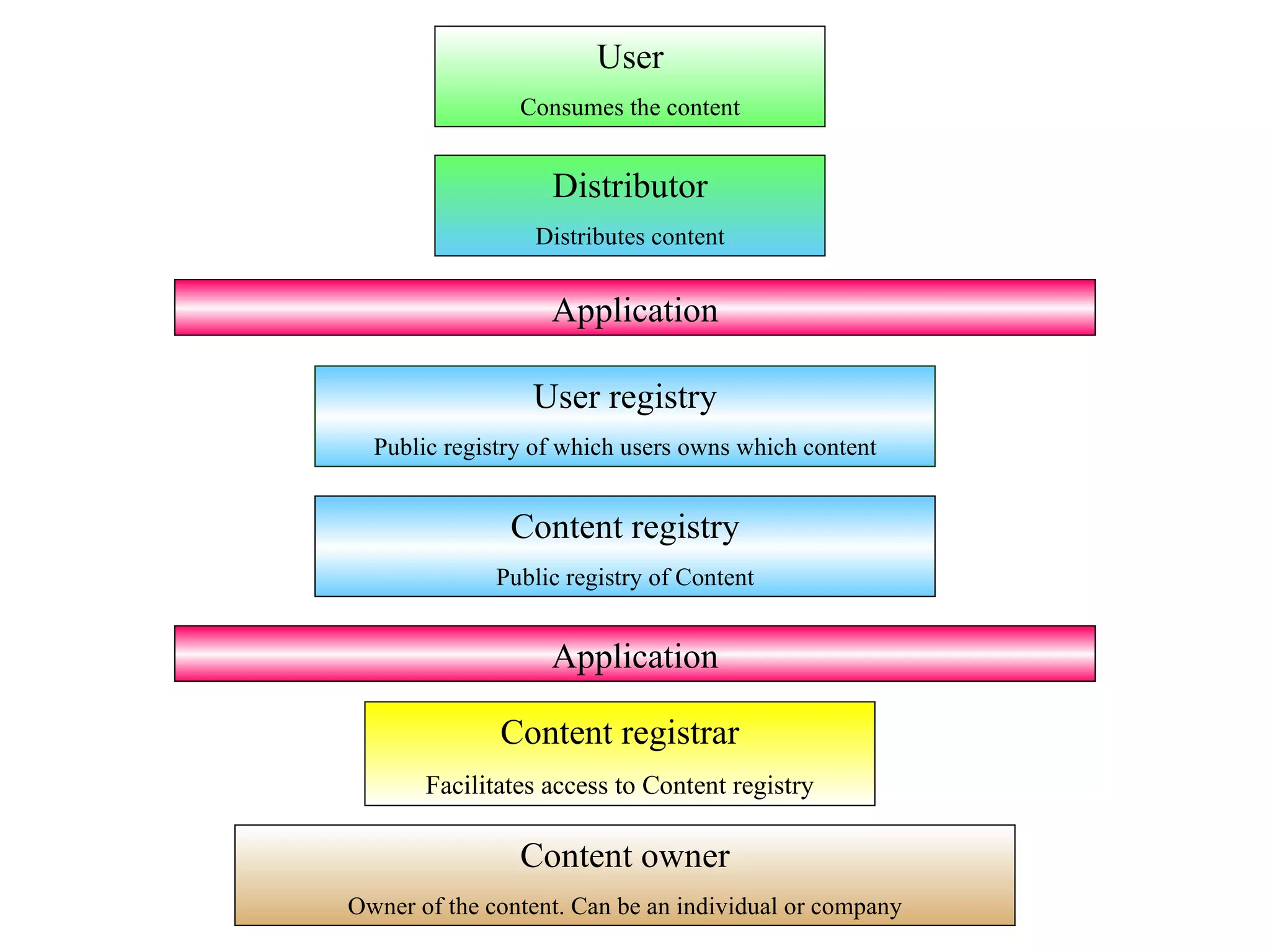
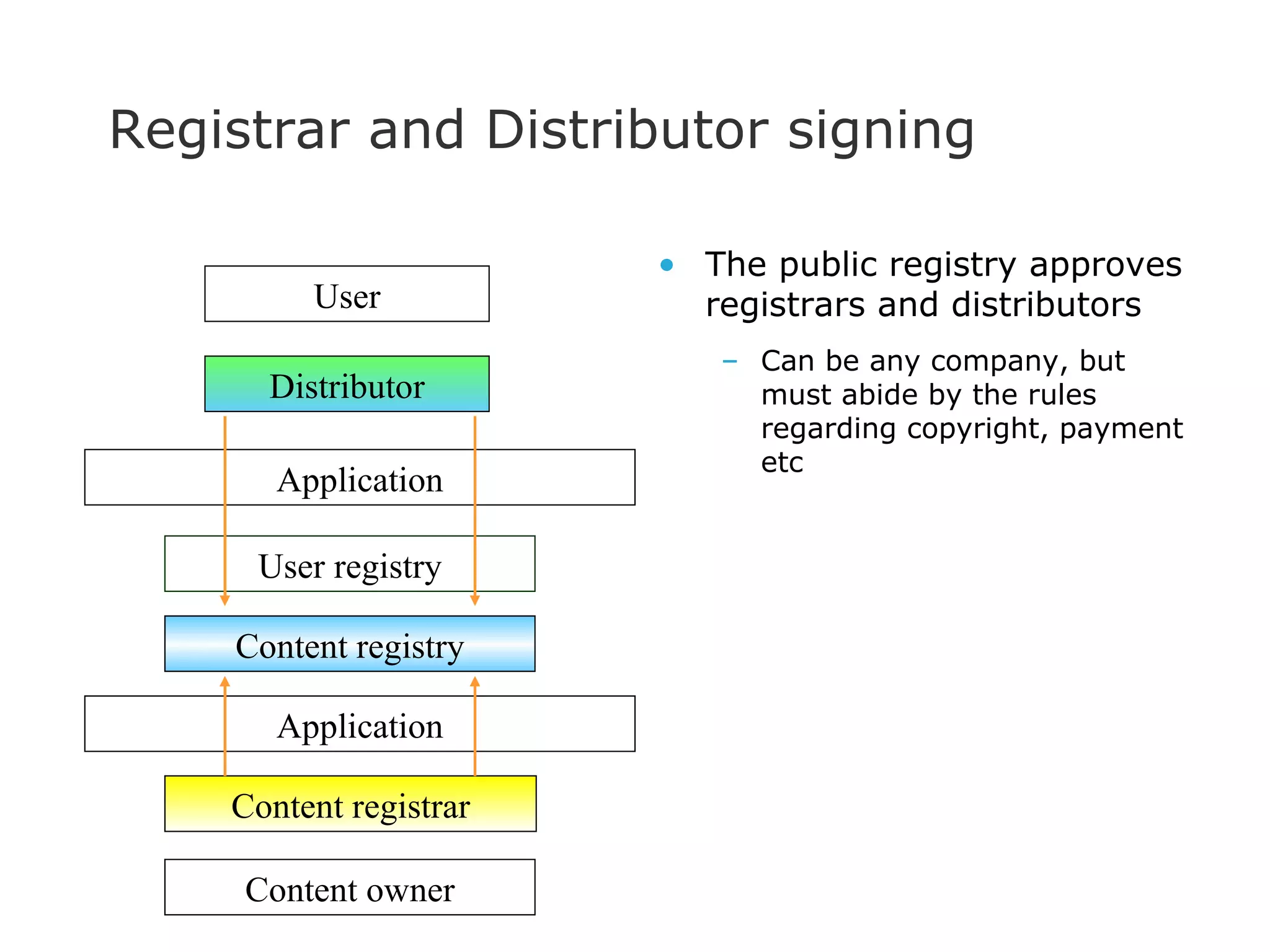
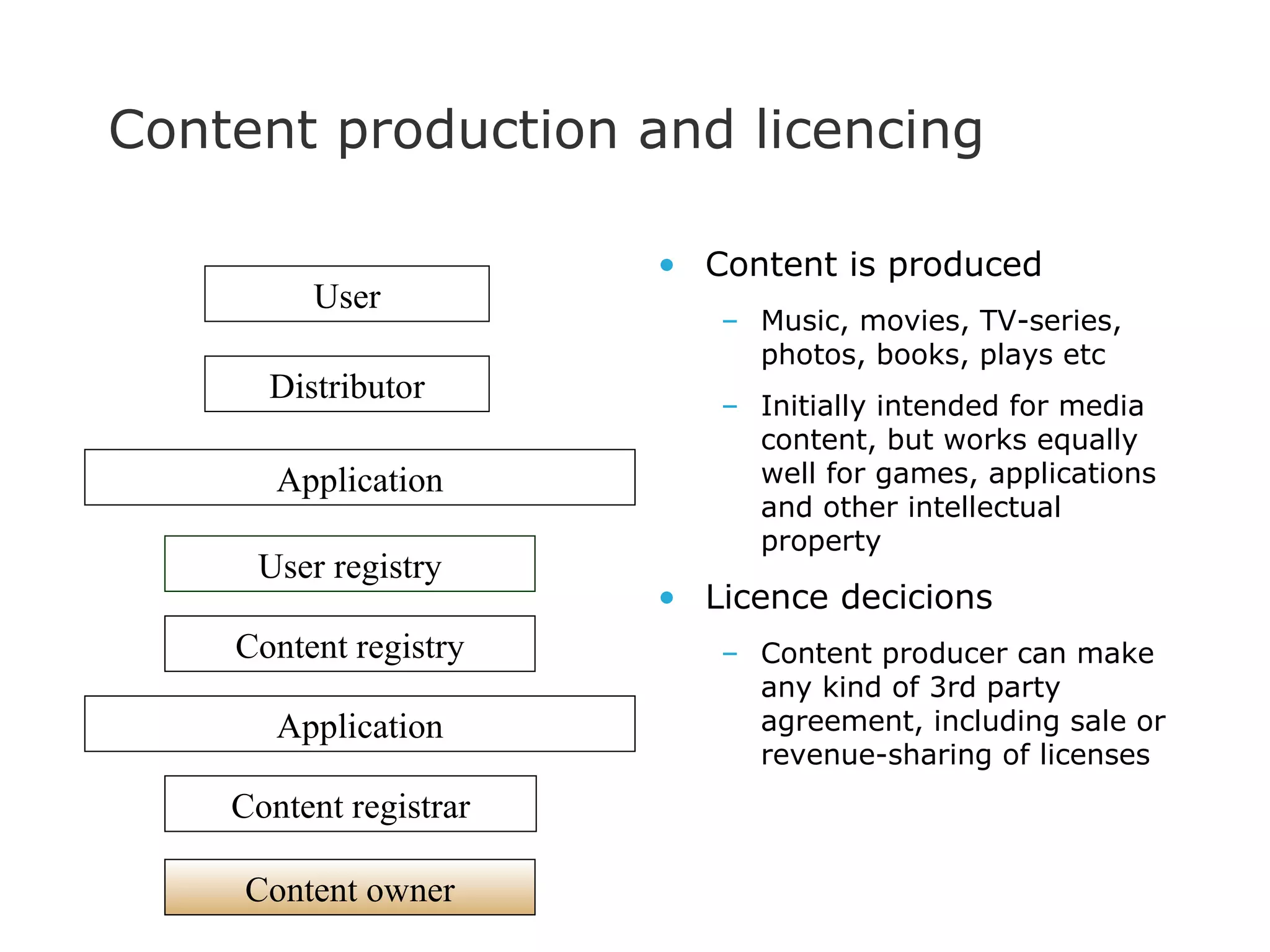
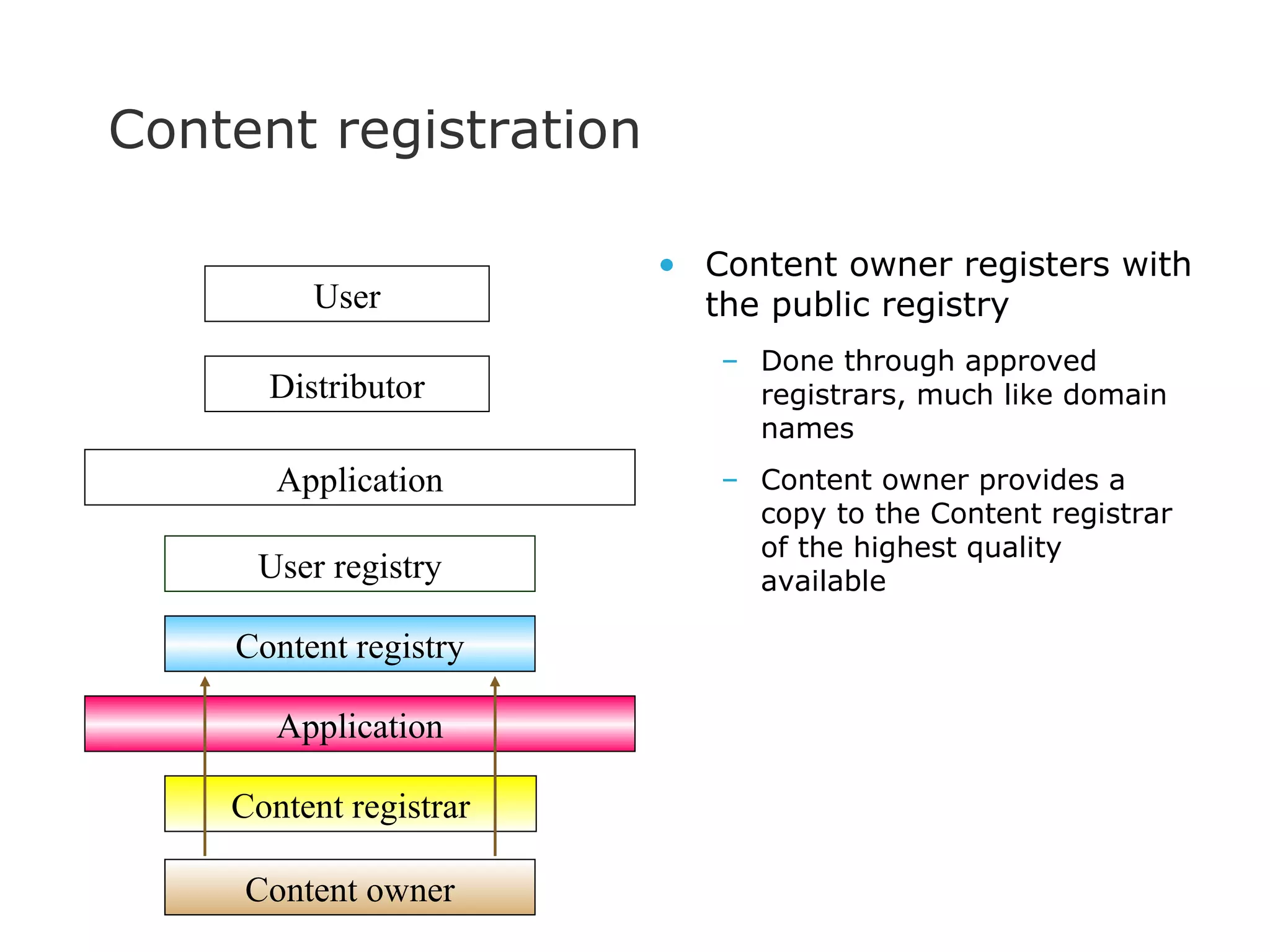
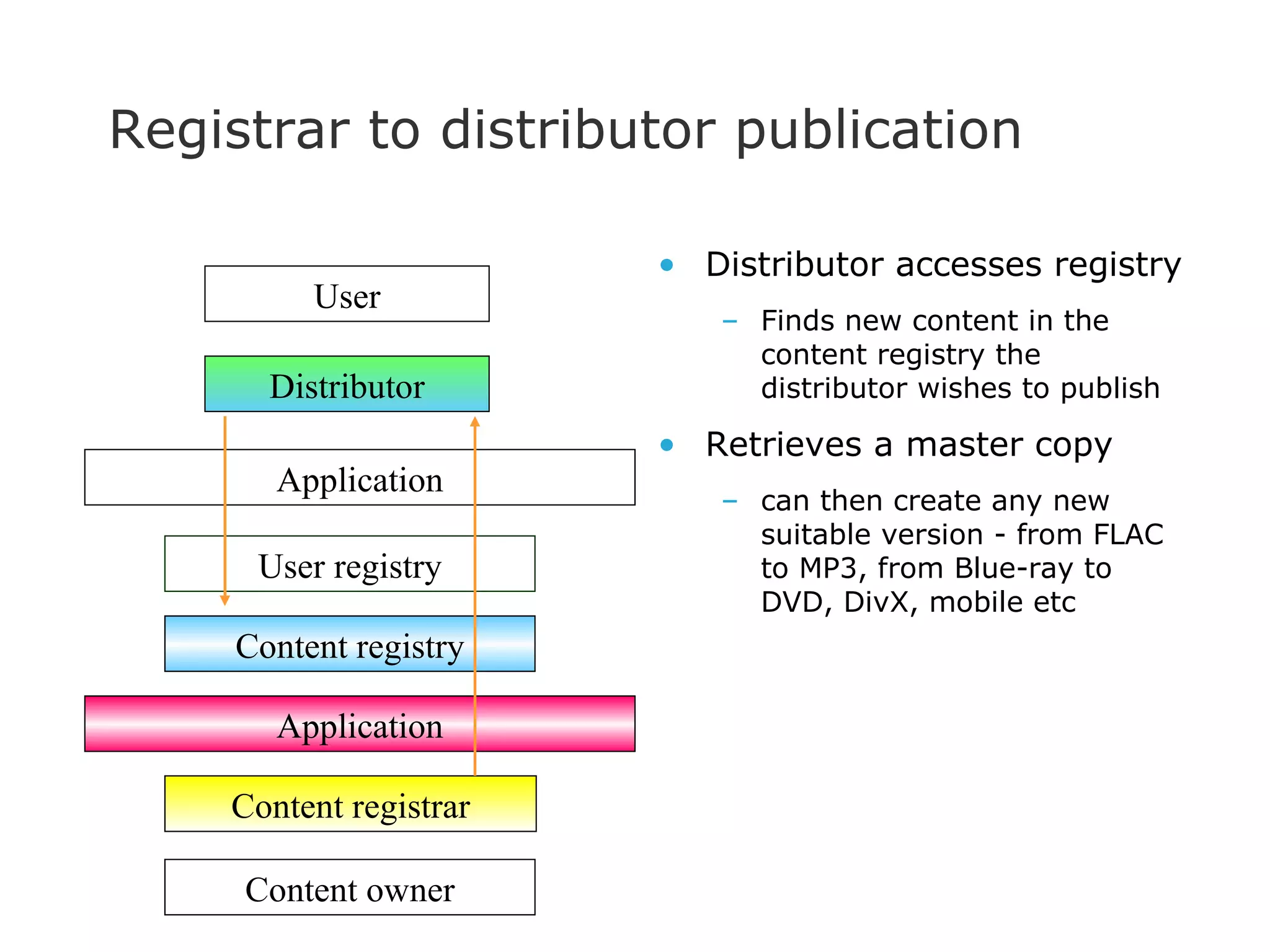
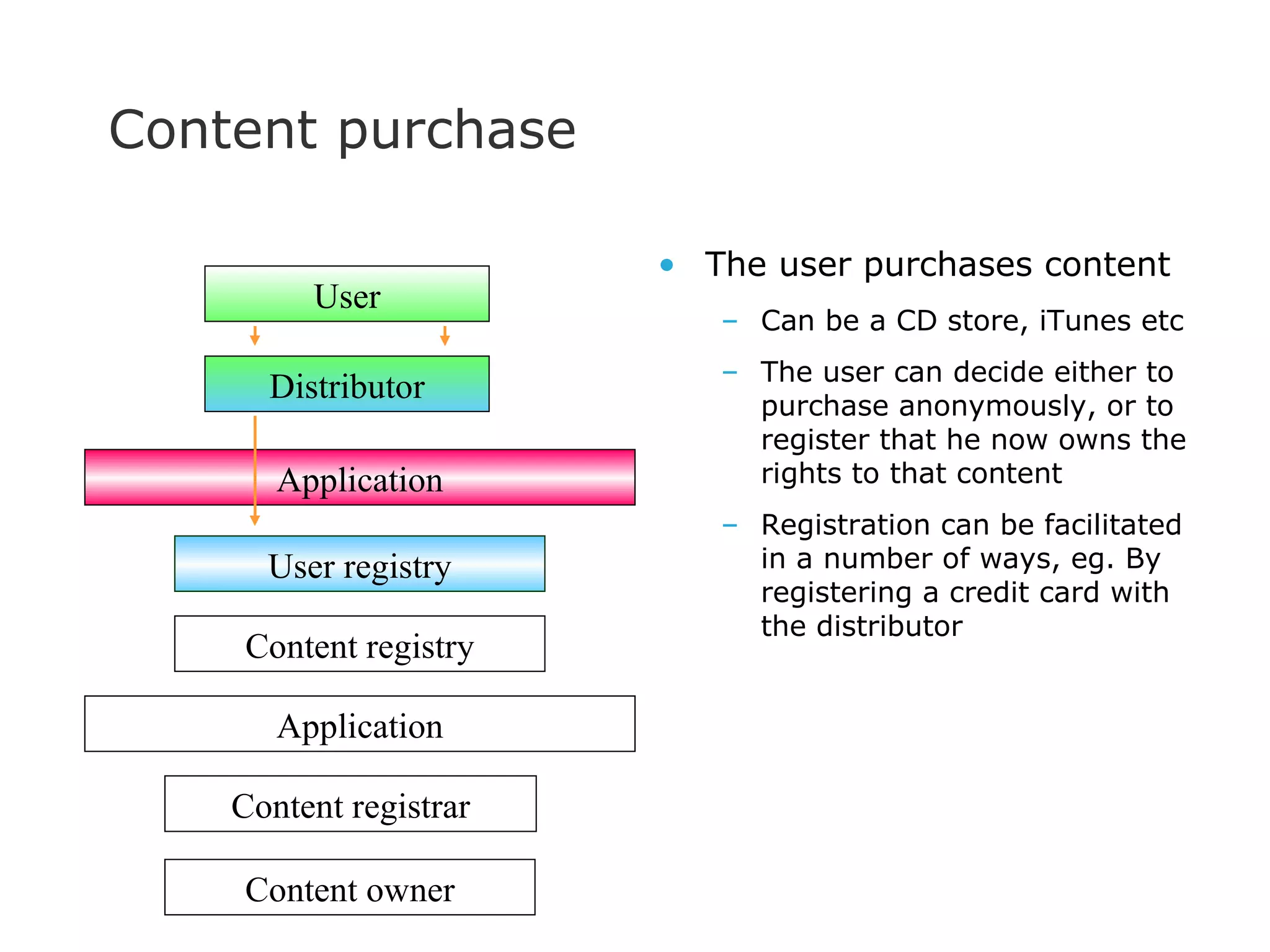
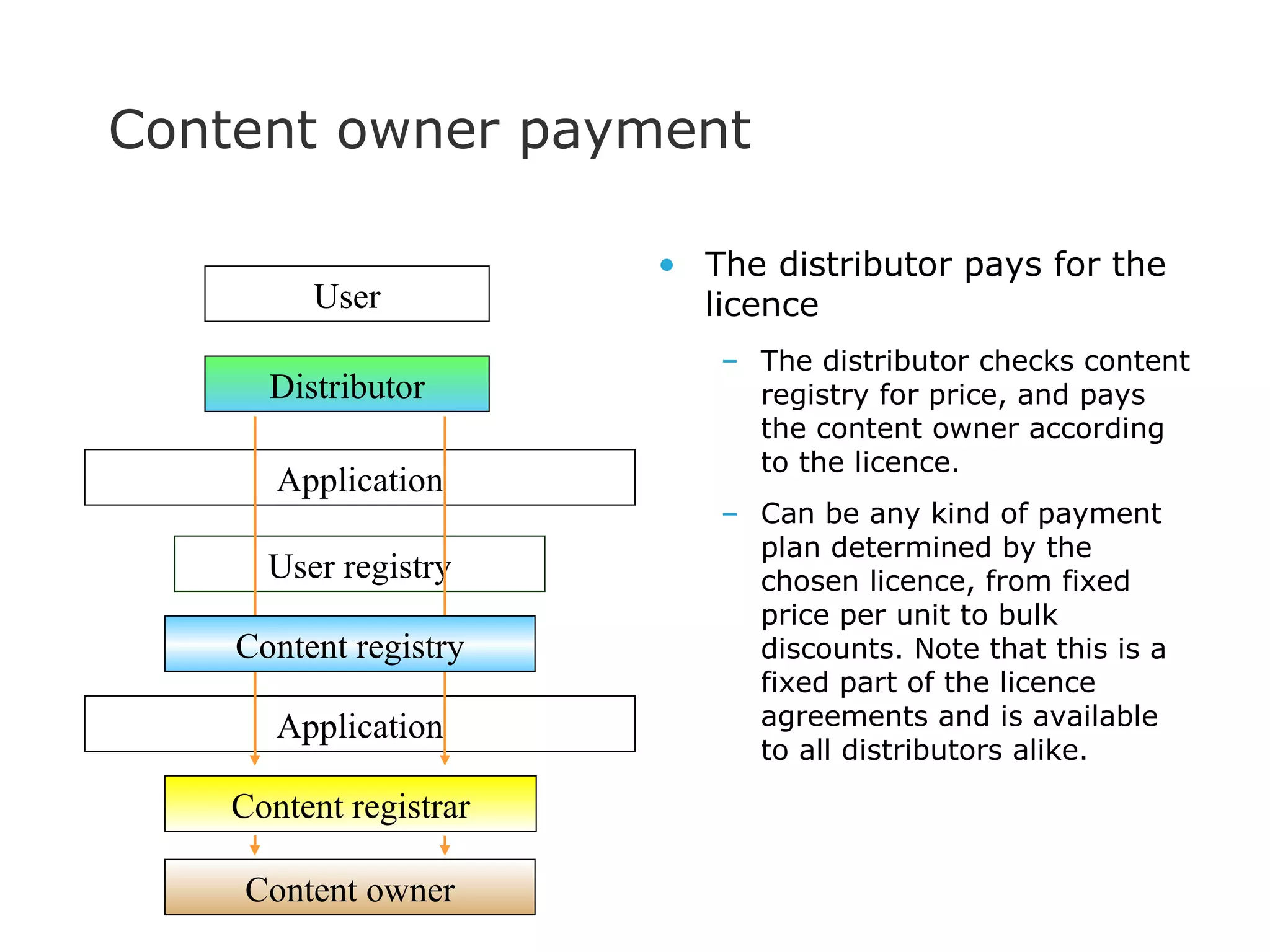
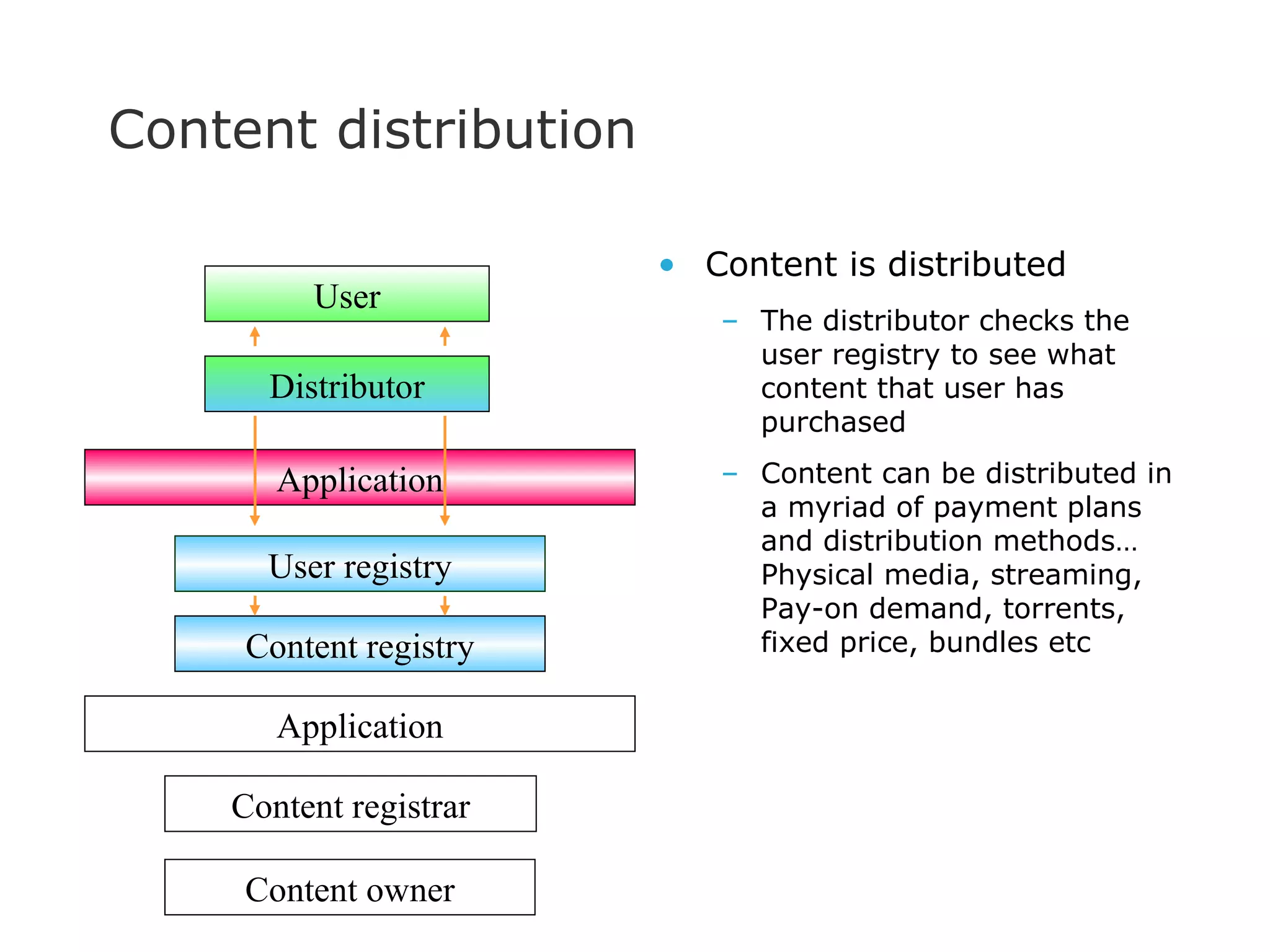
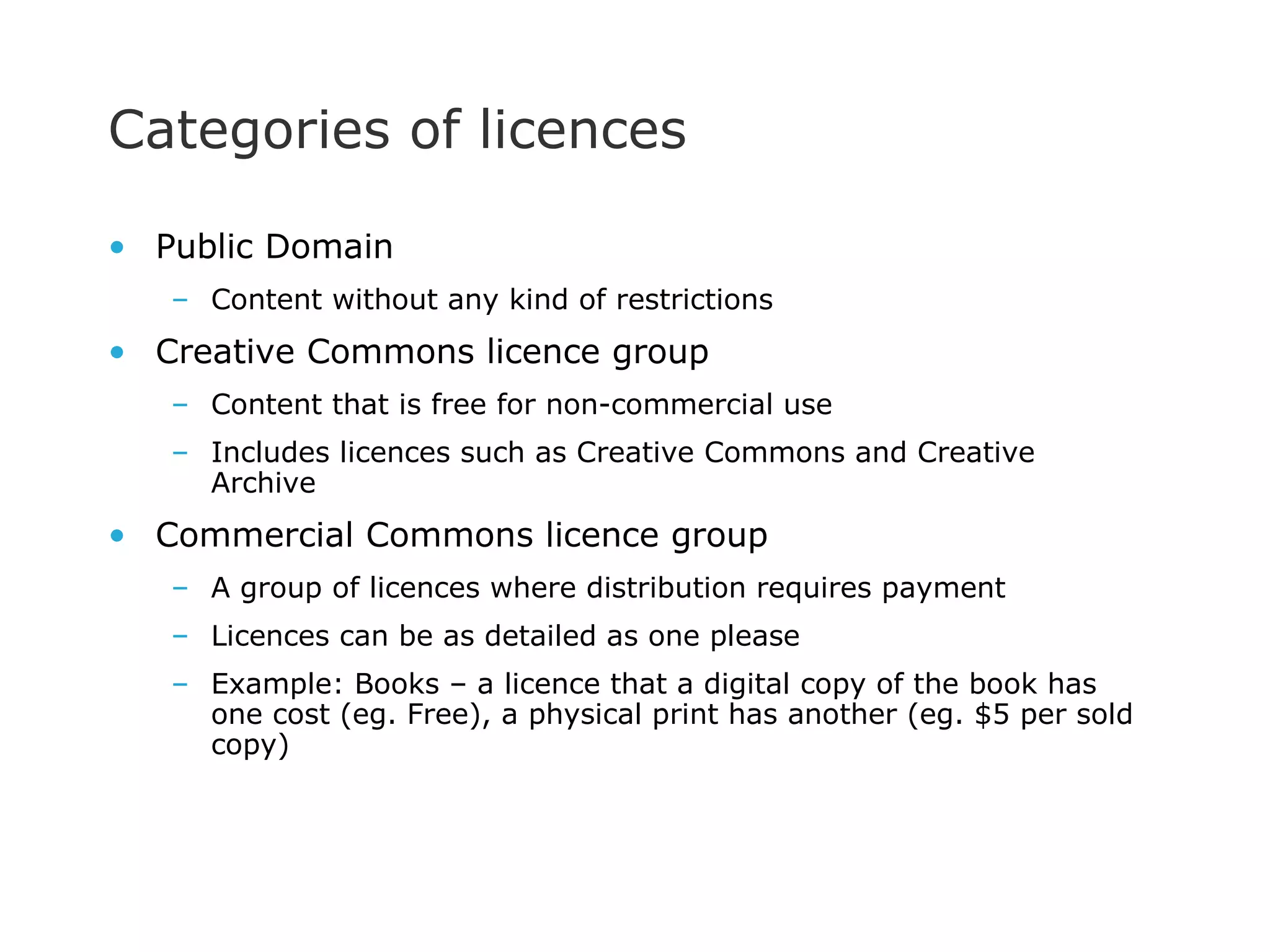
The document discusses the shortcomings of current copyright law, emphasizing that its original purpose—to stimulate culture, creativity, and innovation—is often undermined by commercial practices. It argues for a new model that differentiates between media as a commodity and as a form of expression, promoting free access and non-exclusive content distribution. Additionally, it proposes the establishment of an independent public registry for content to address the needs of creators and consumers while facilitating a more equitable and competitive environment.