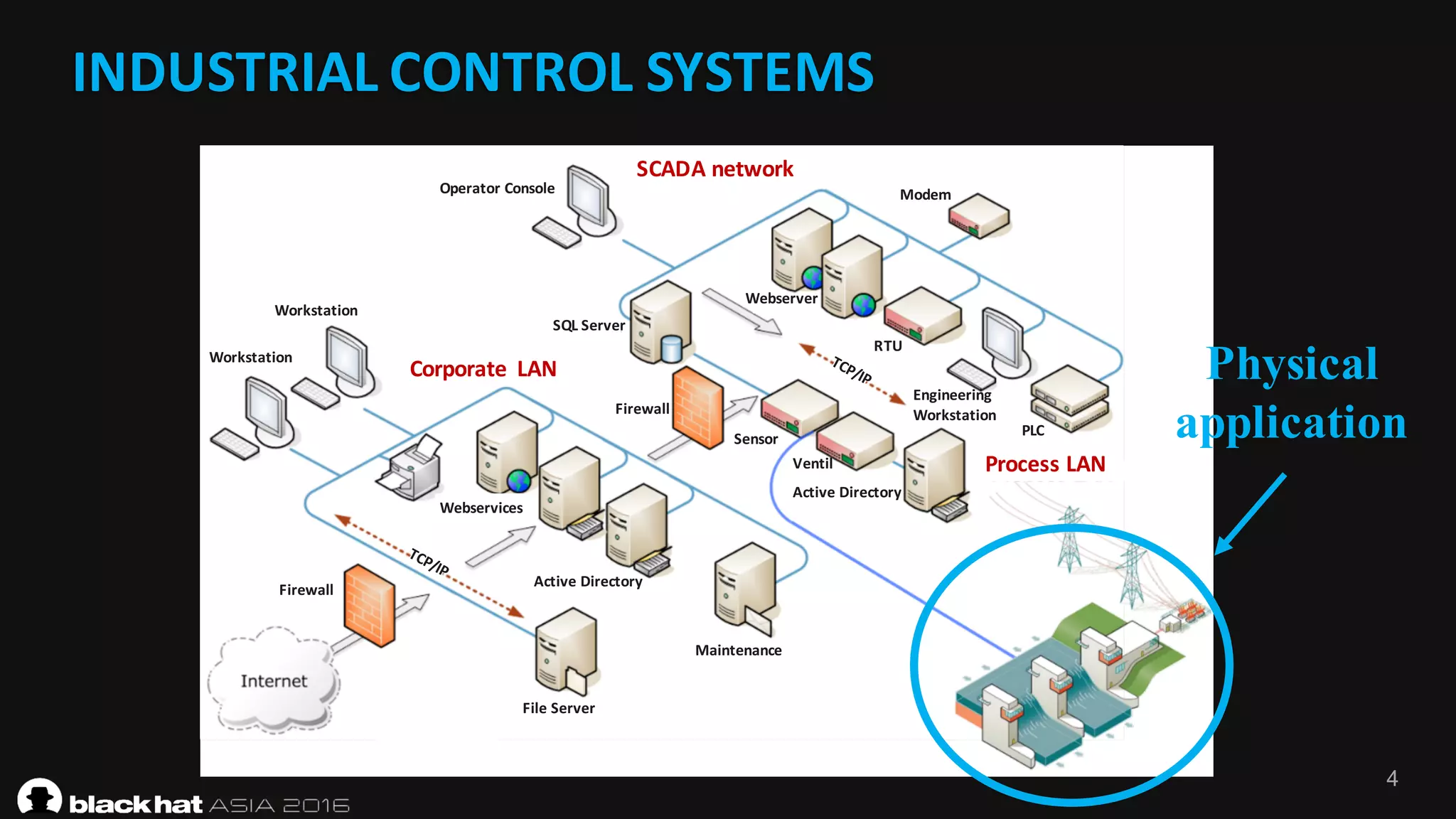
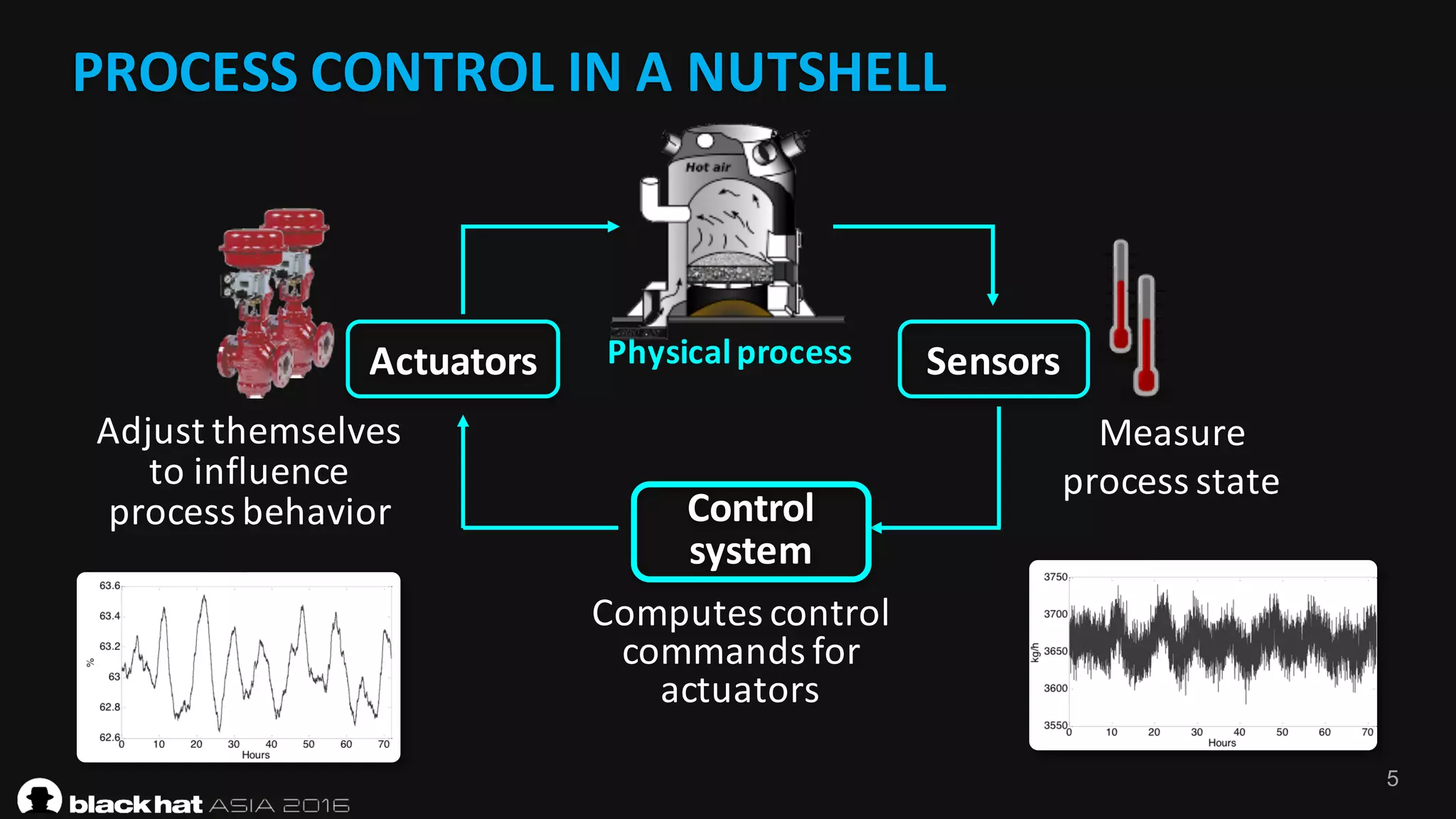
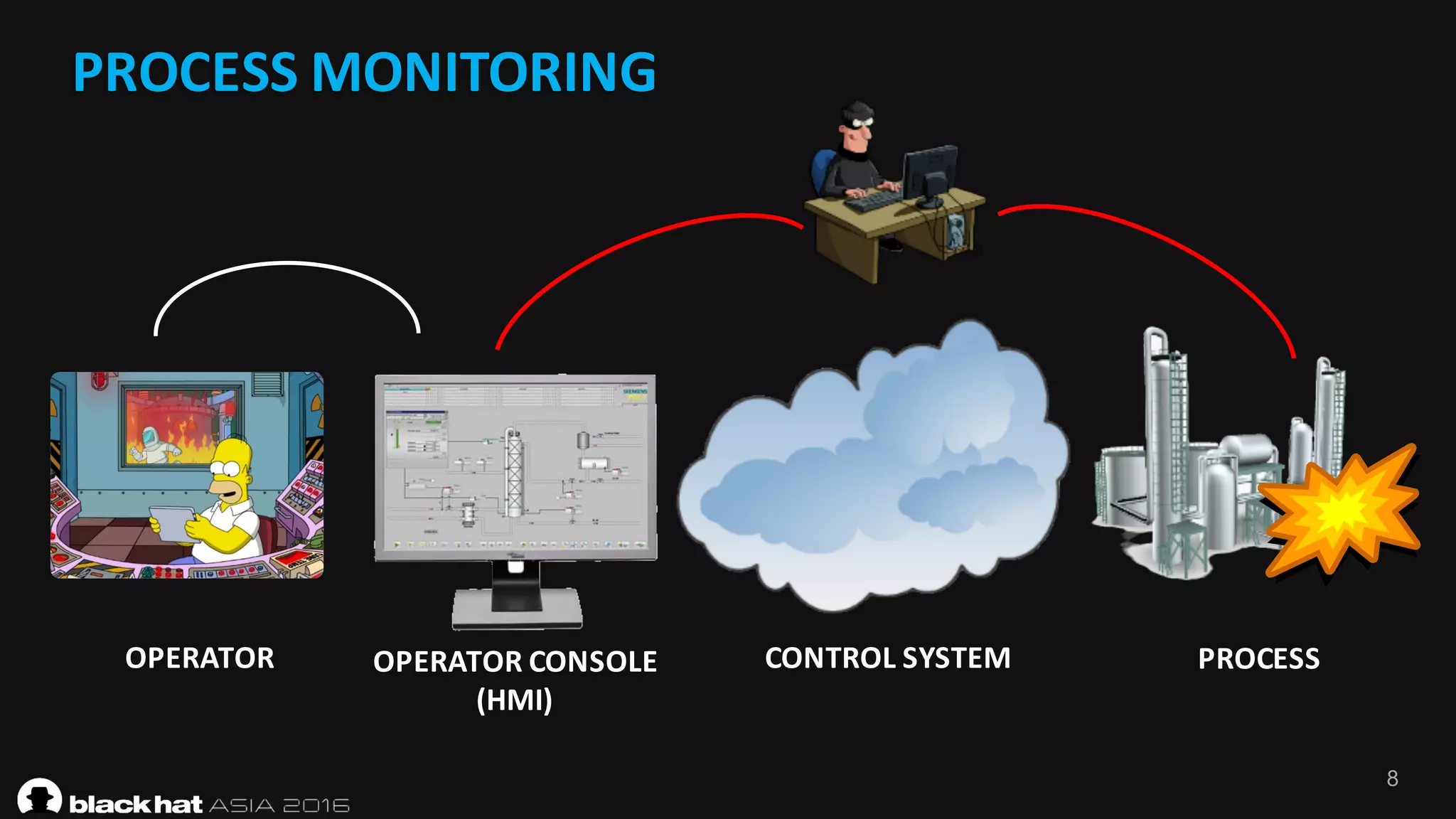
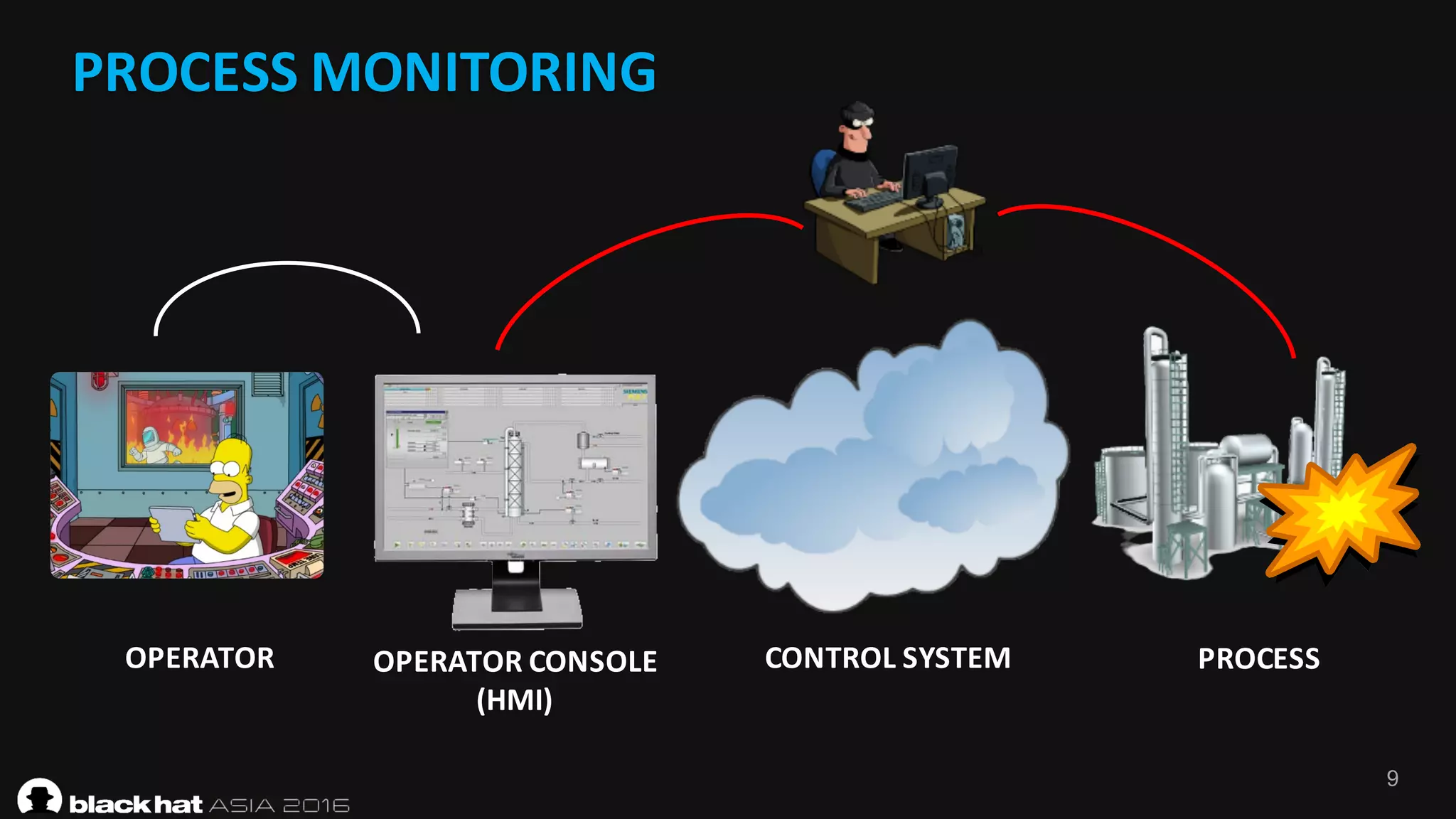
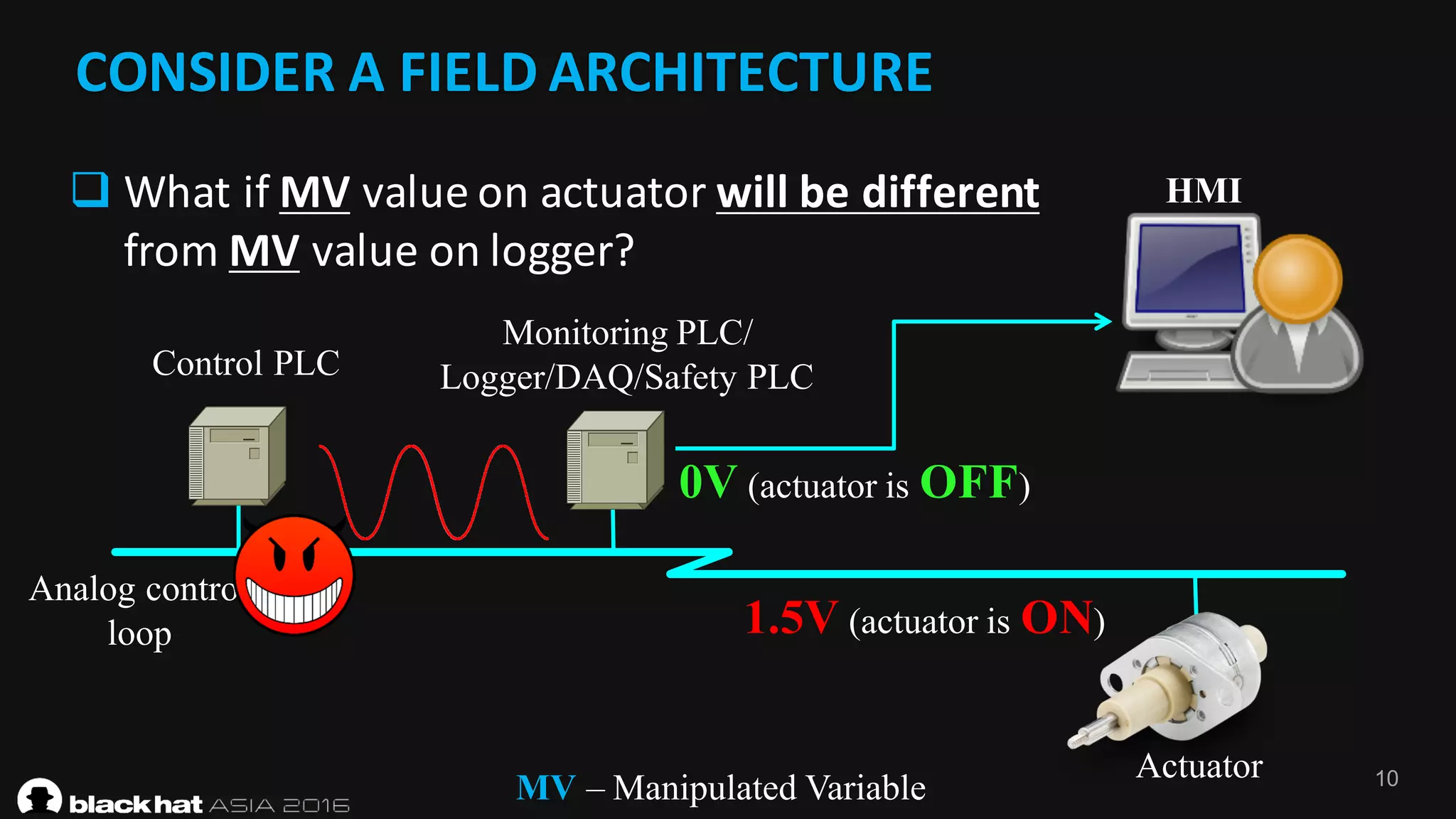
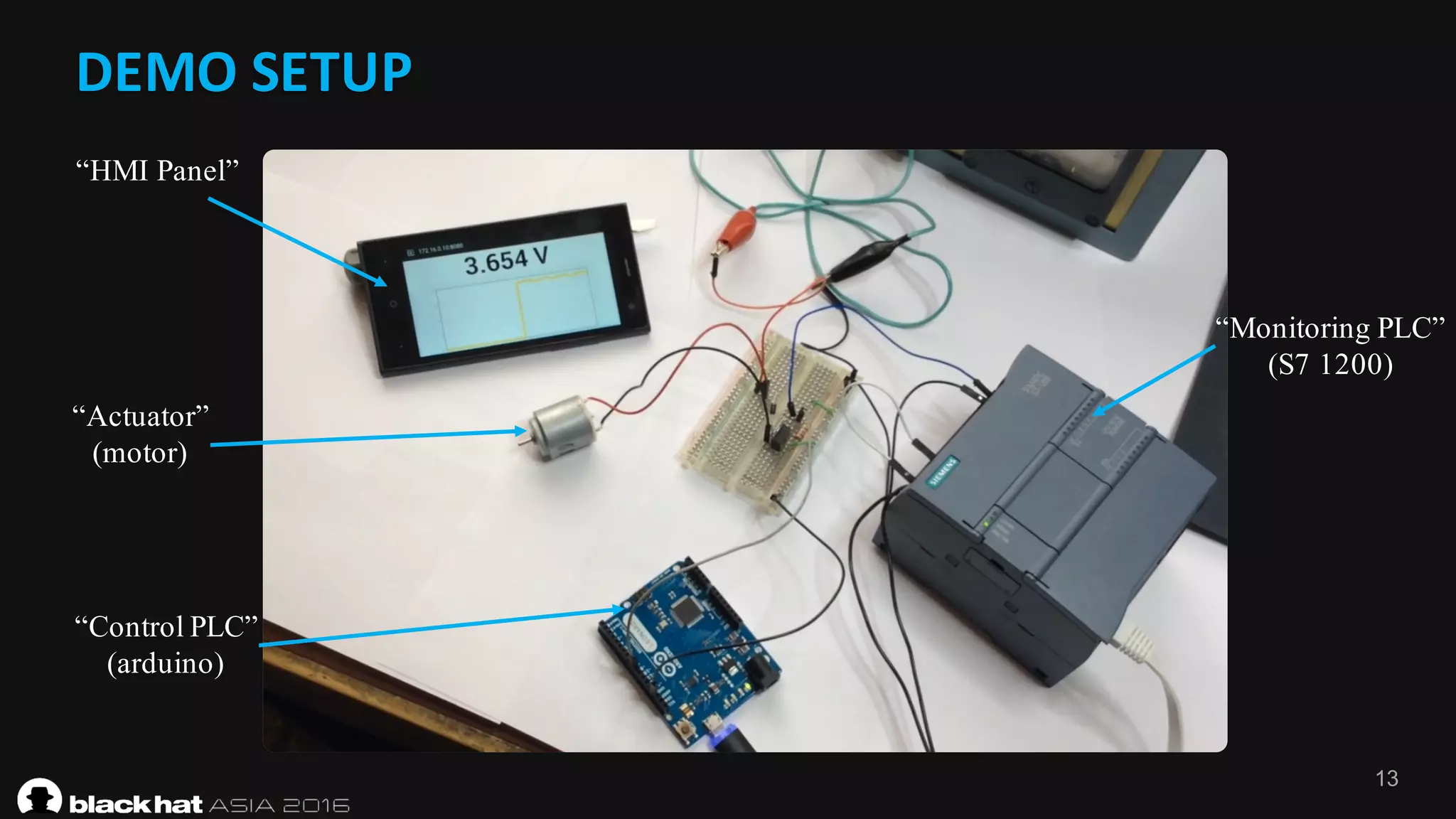
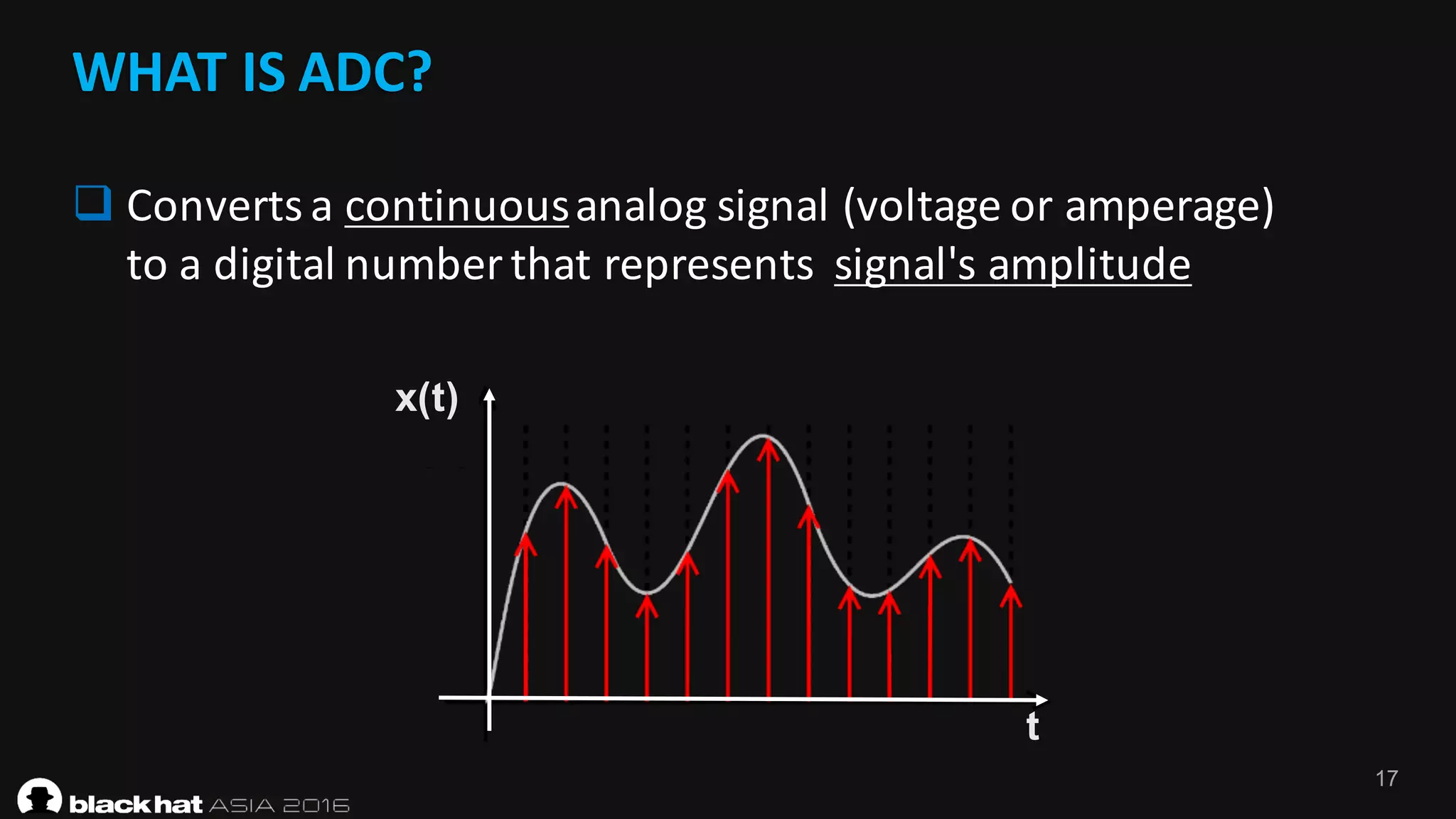
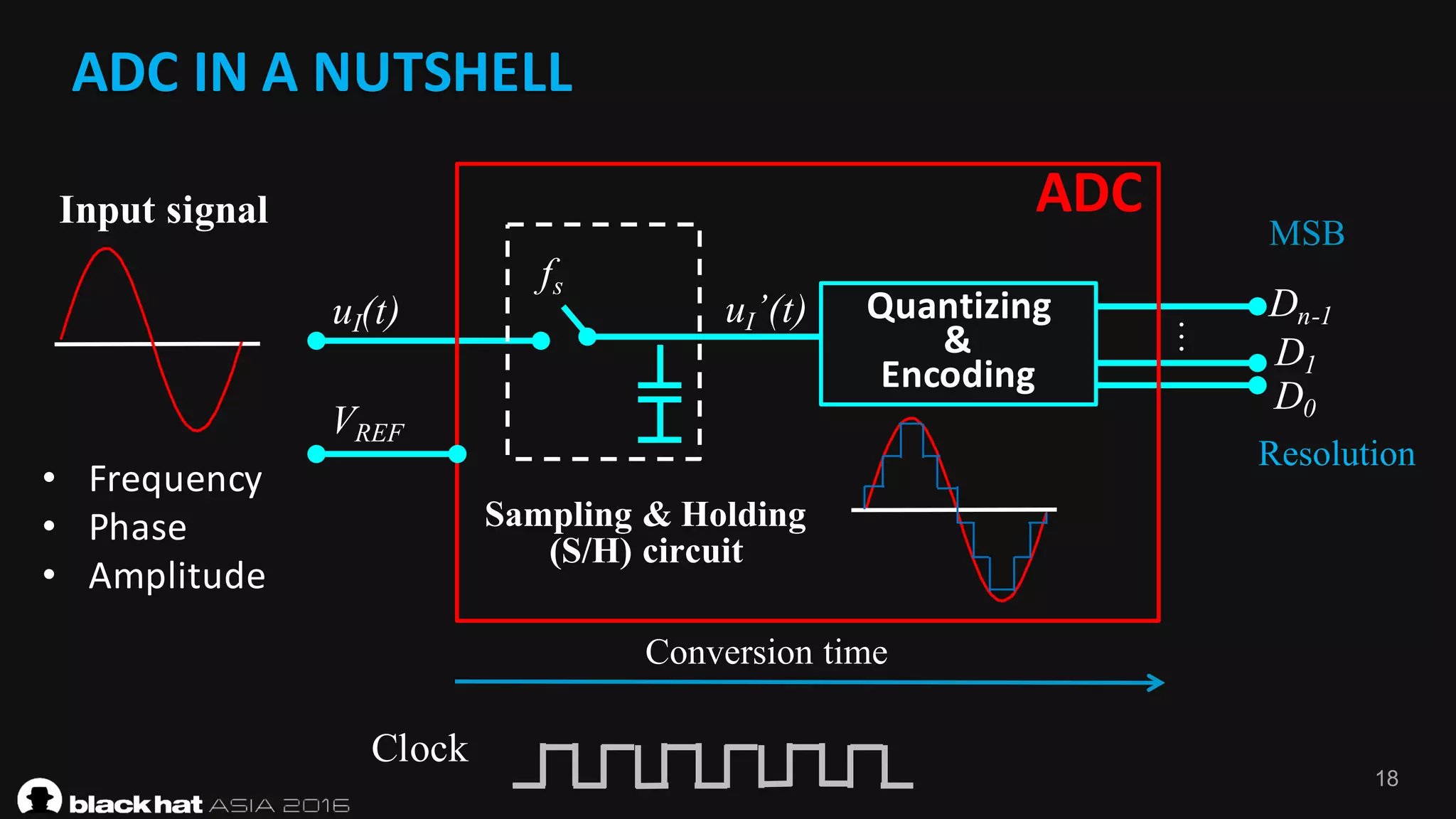
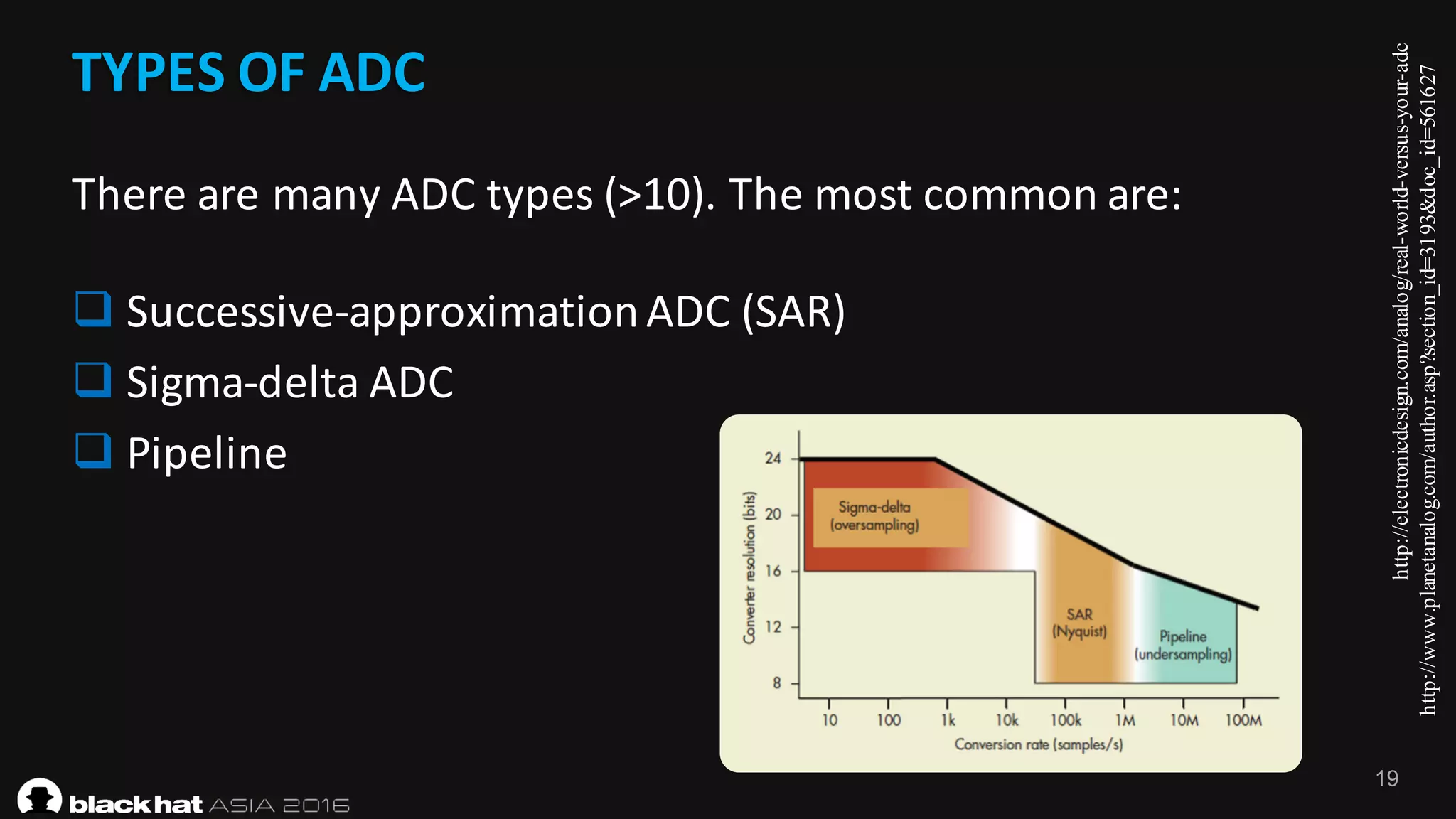
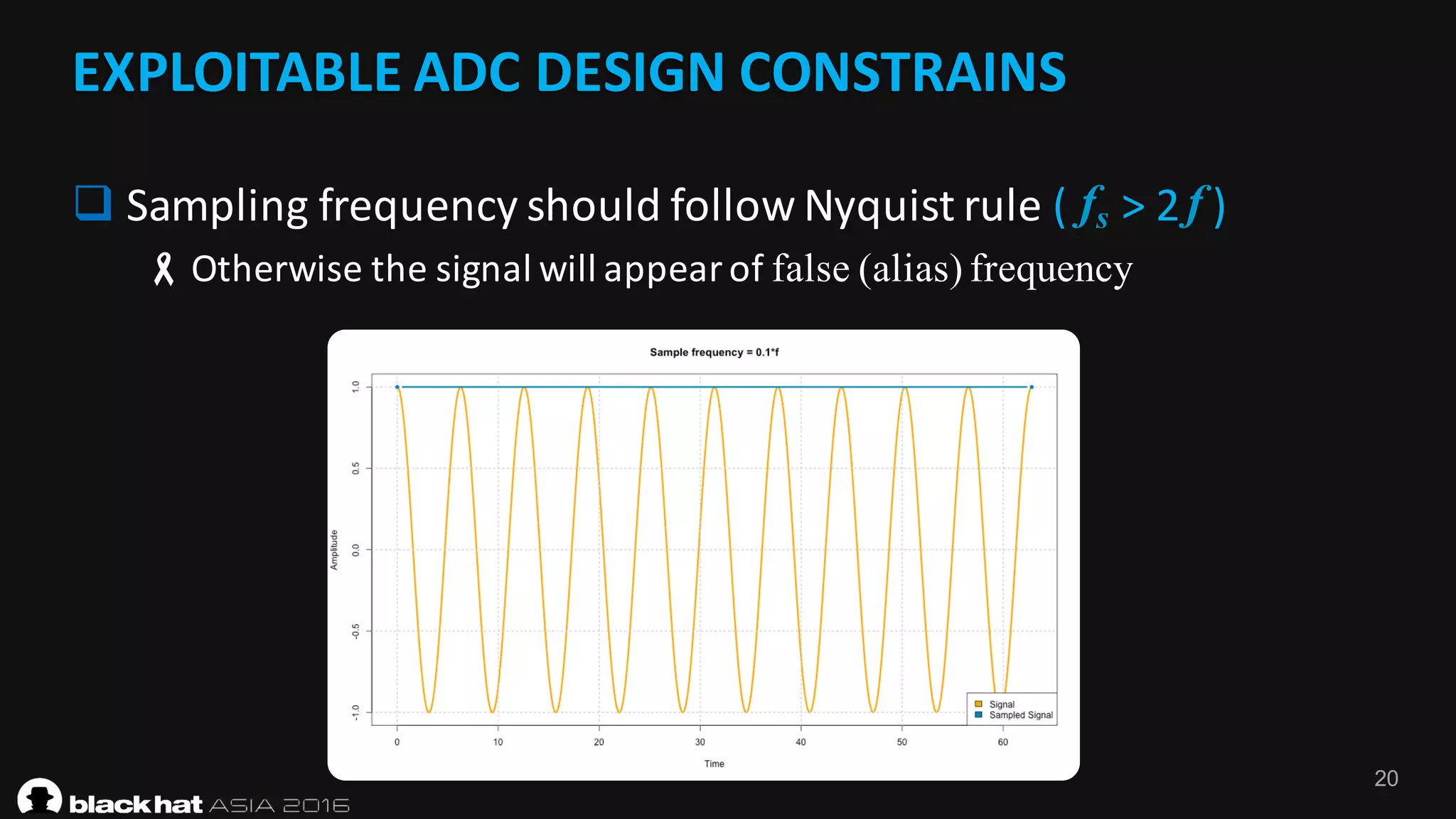
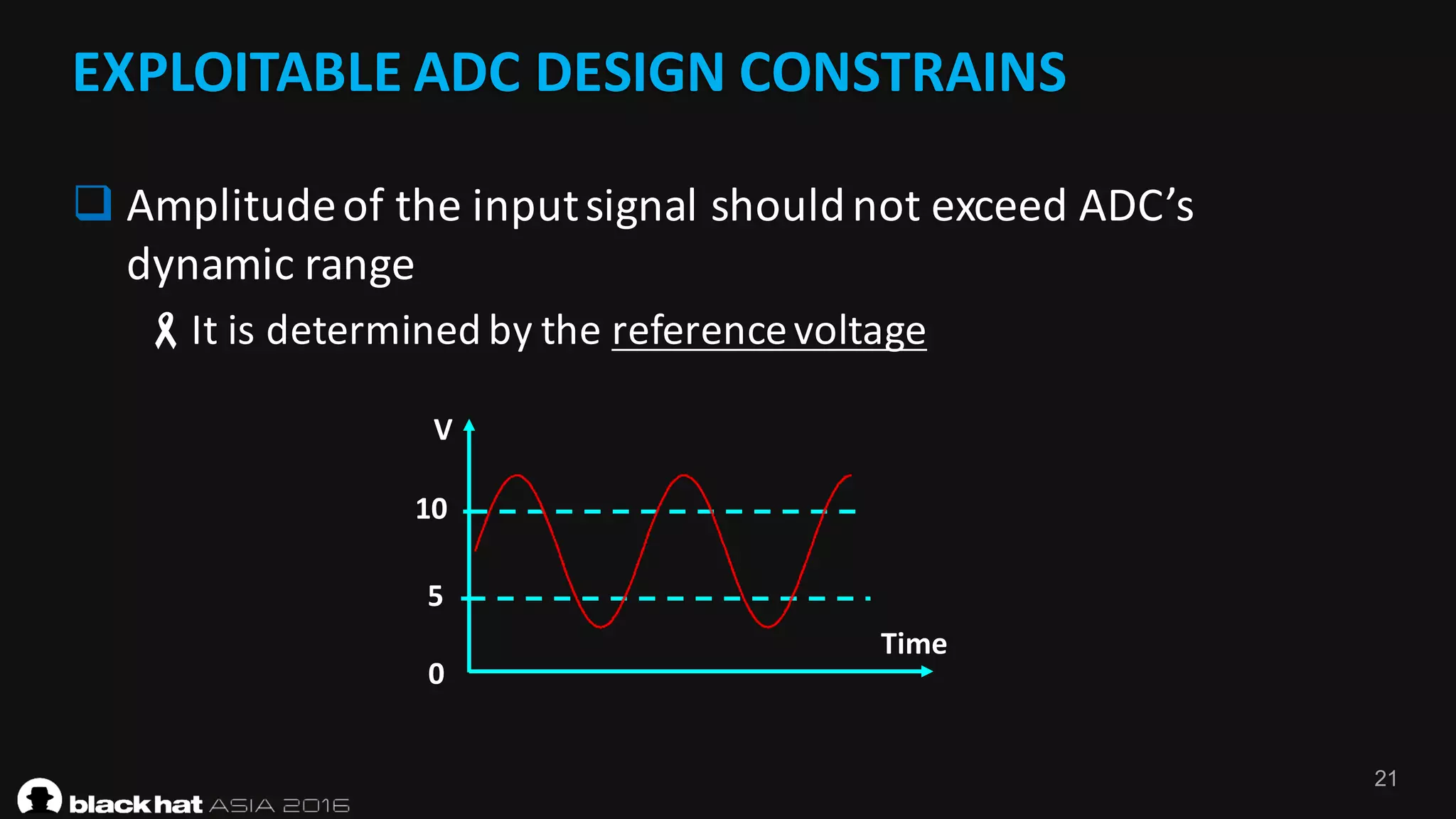
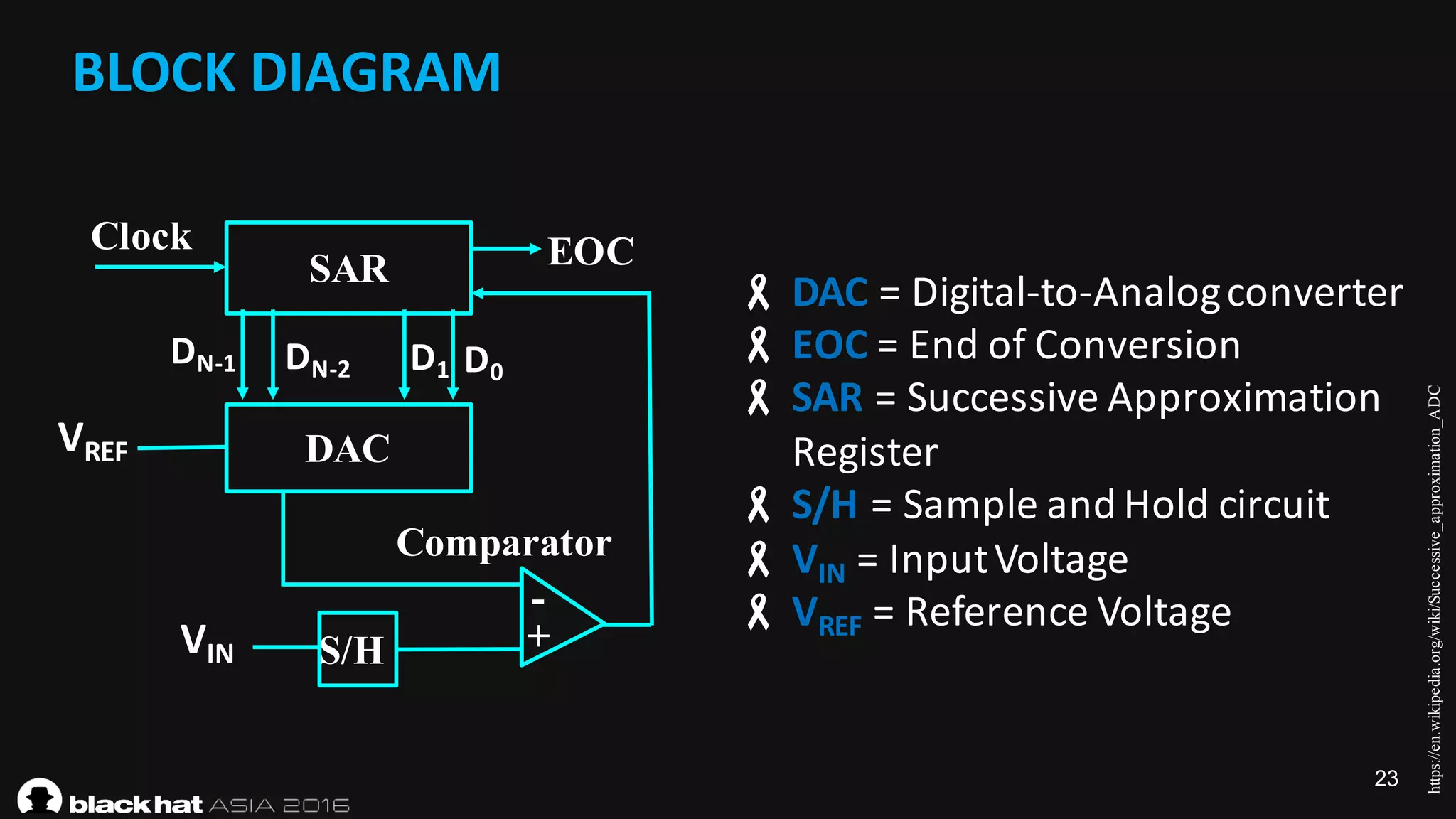
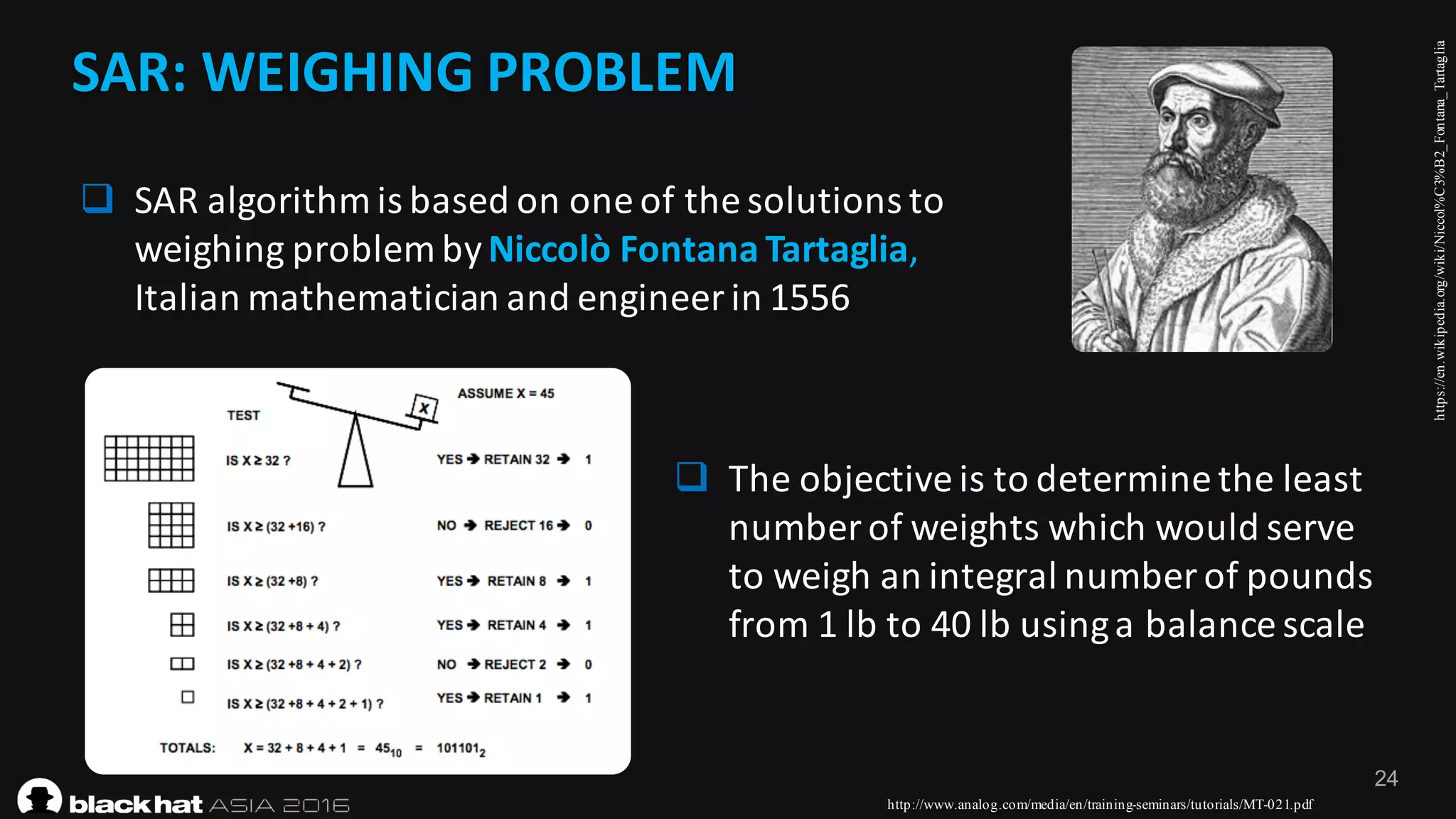
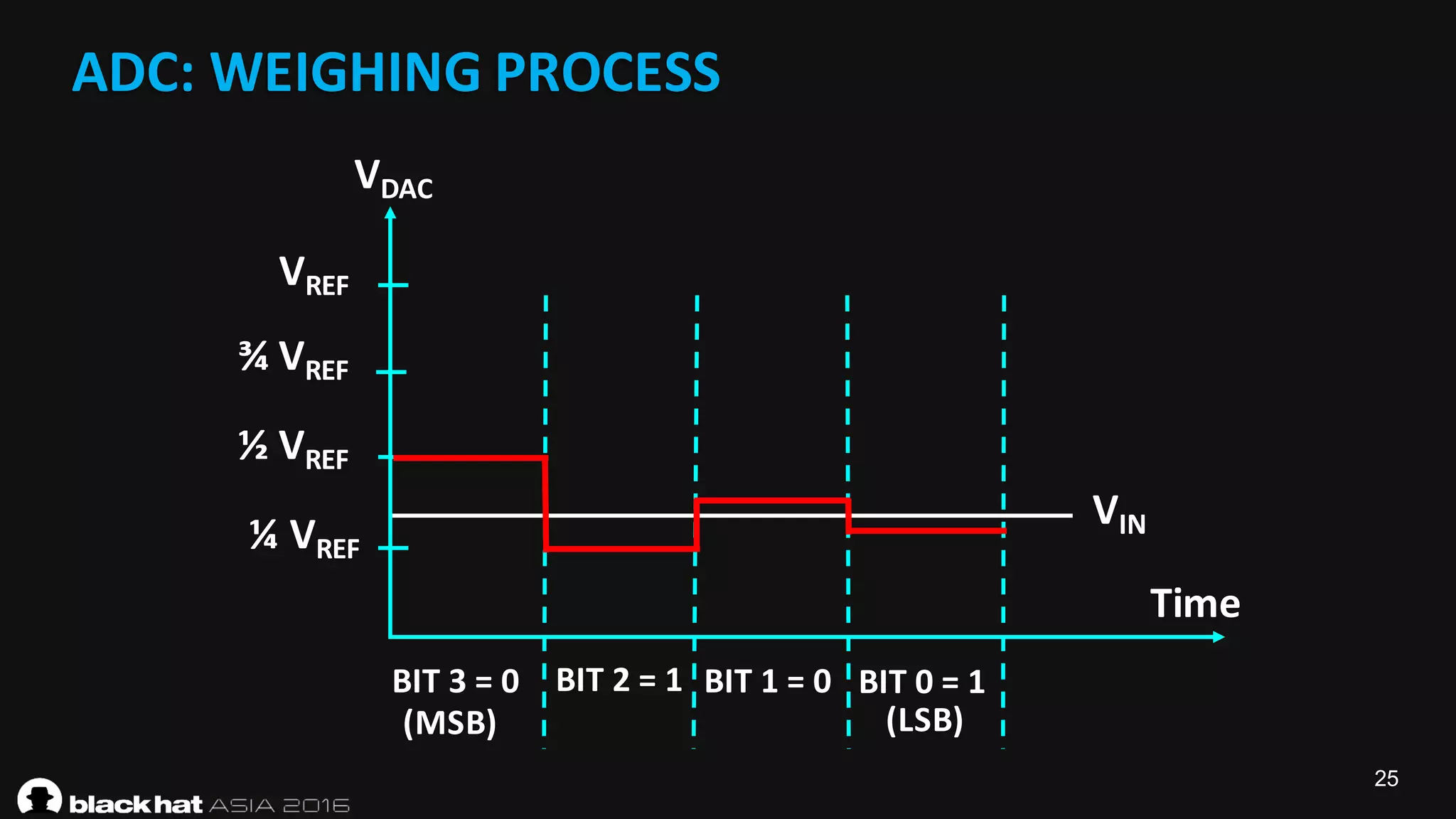
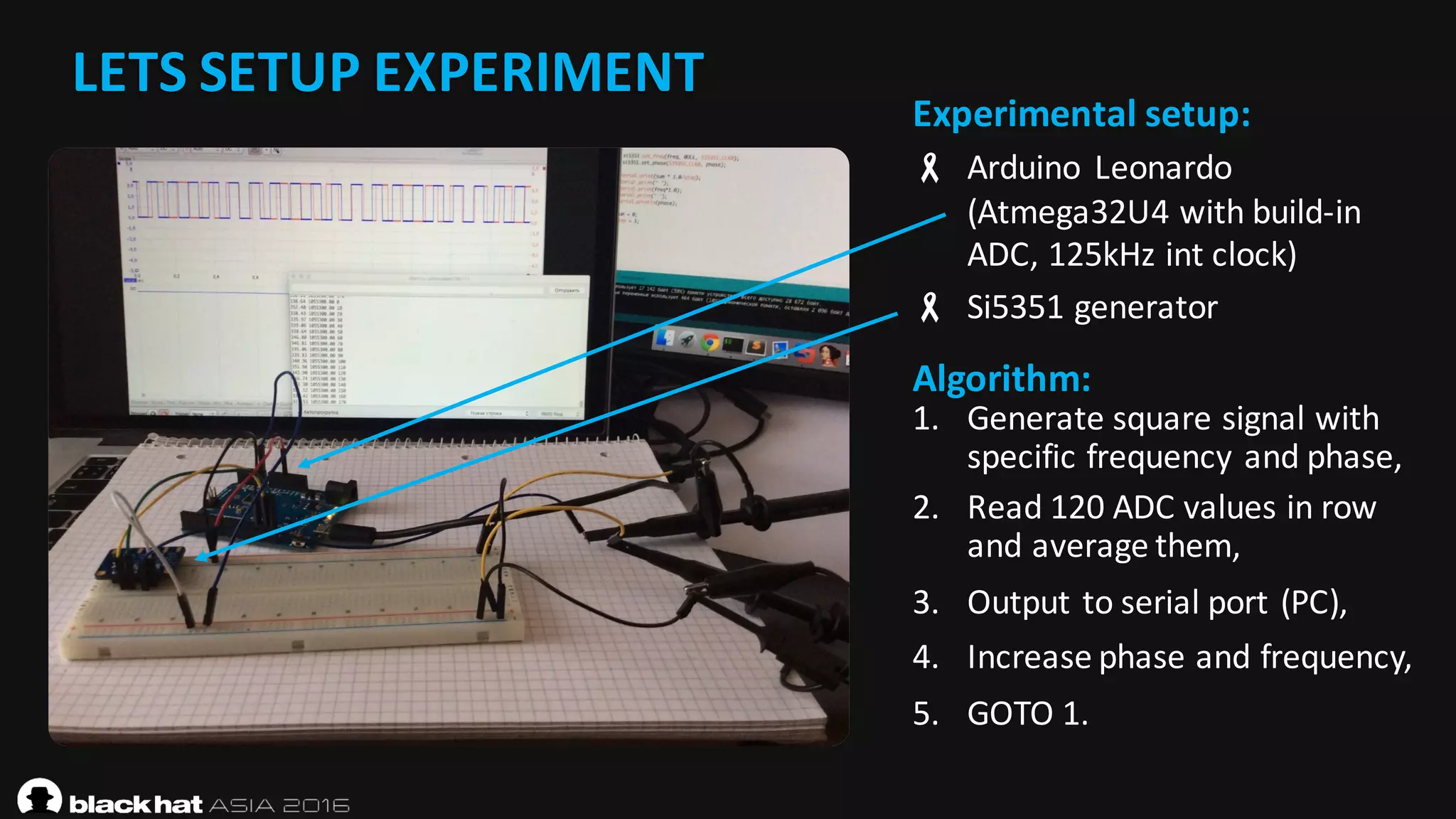
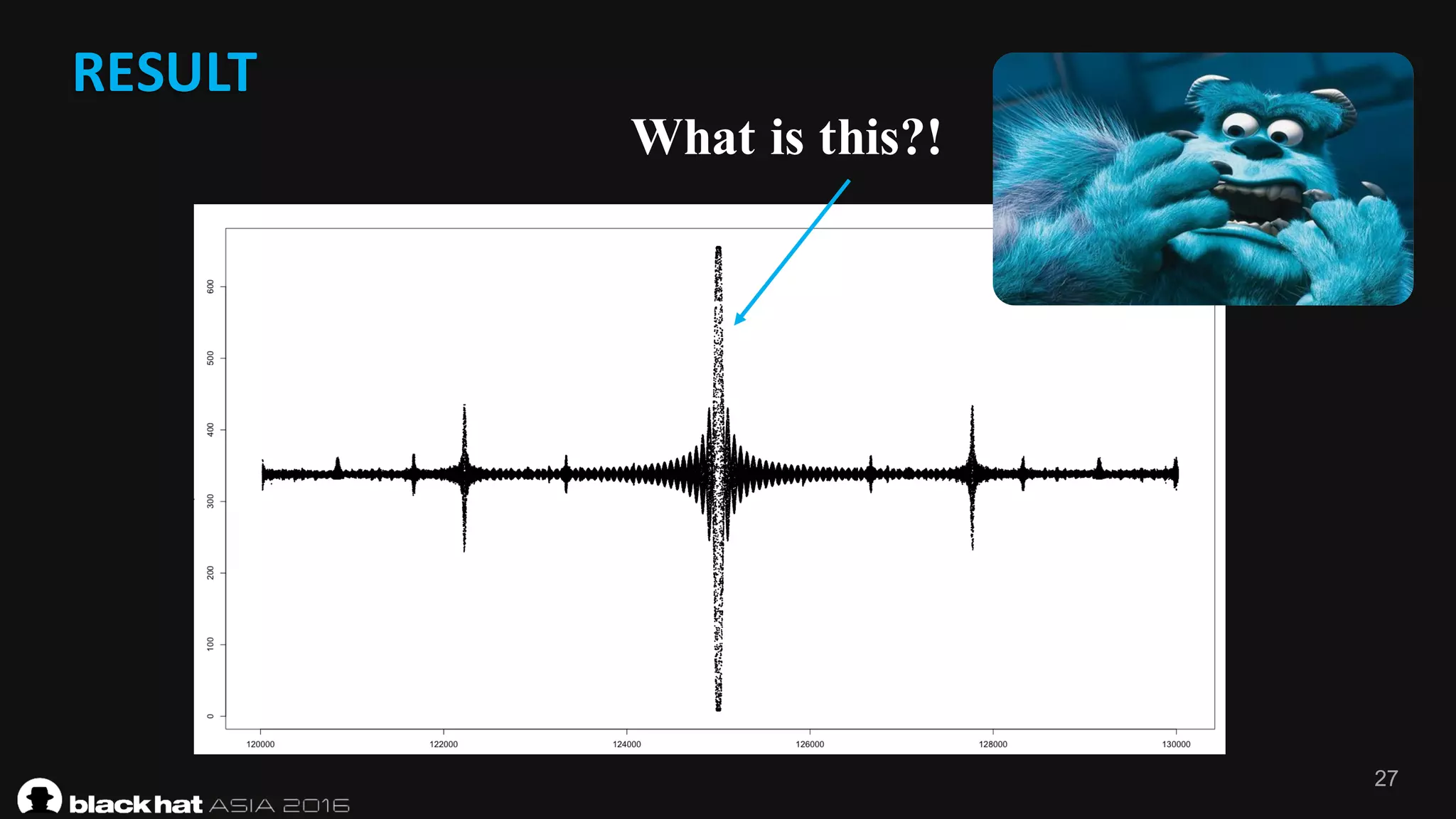
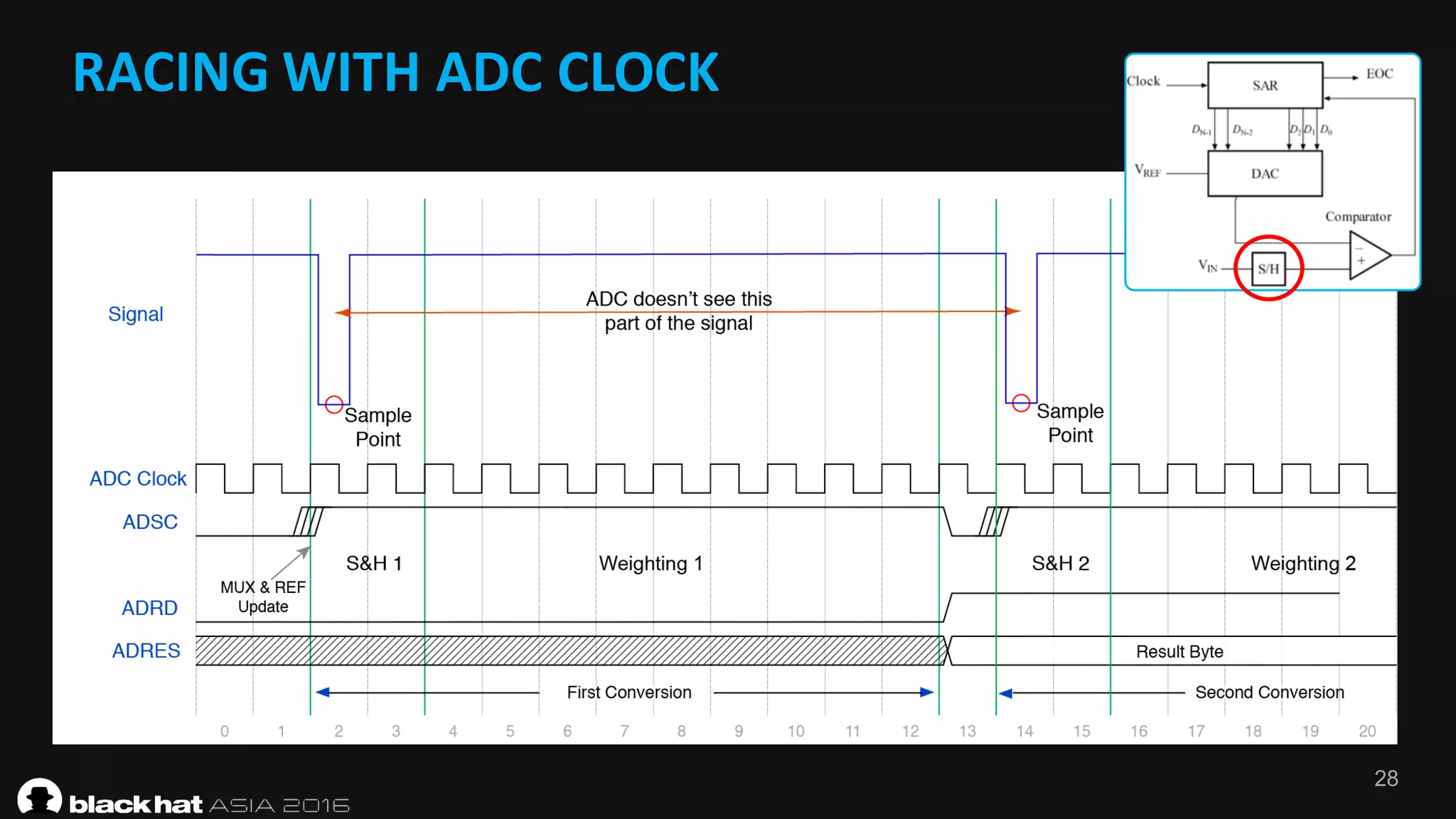
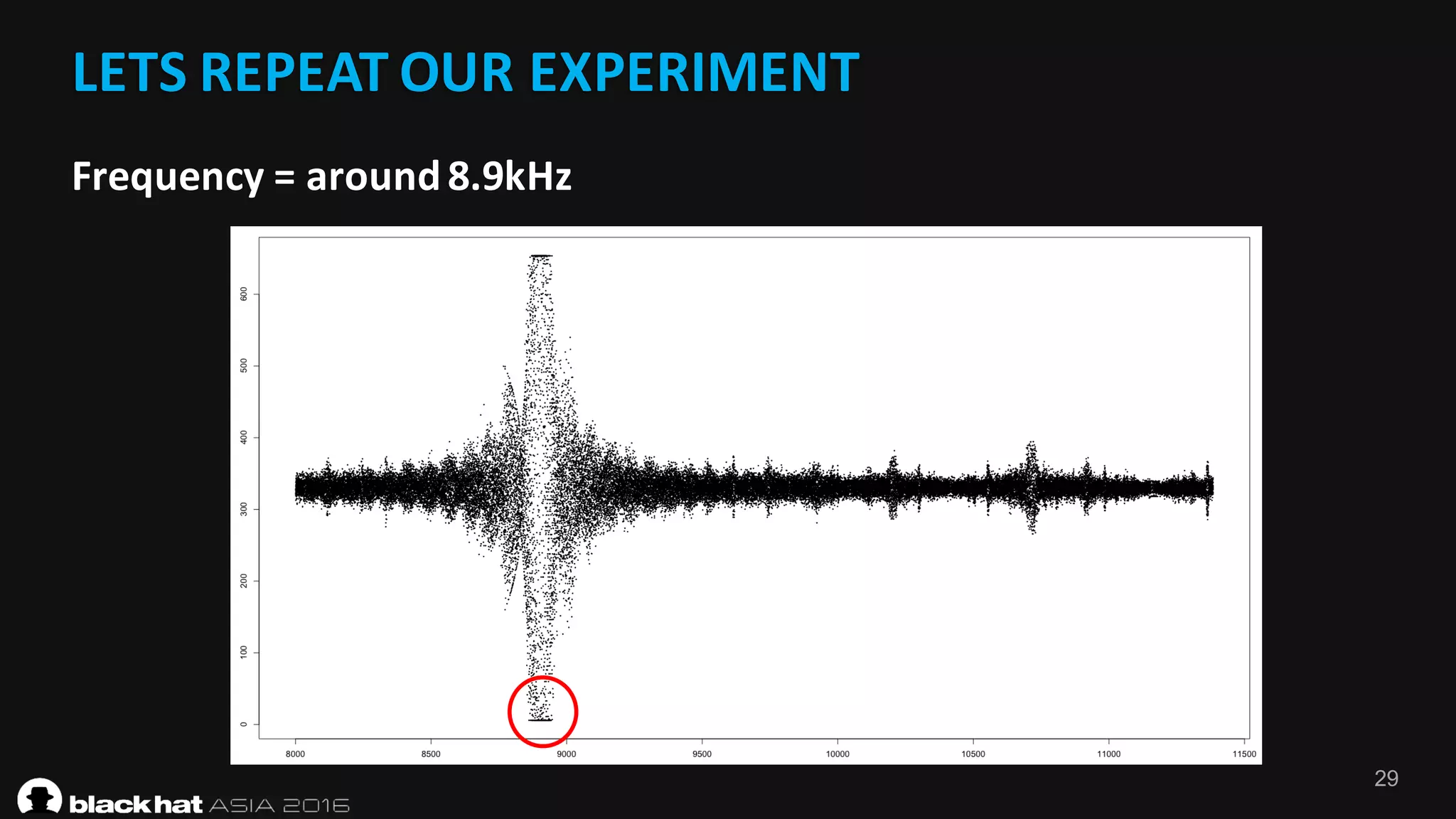
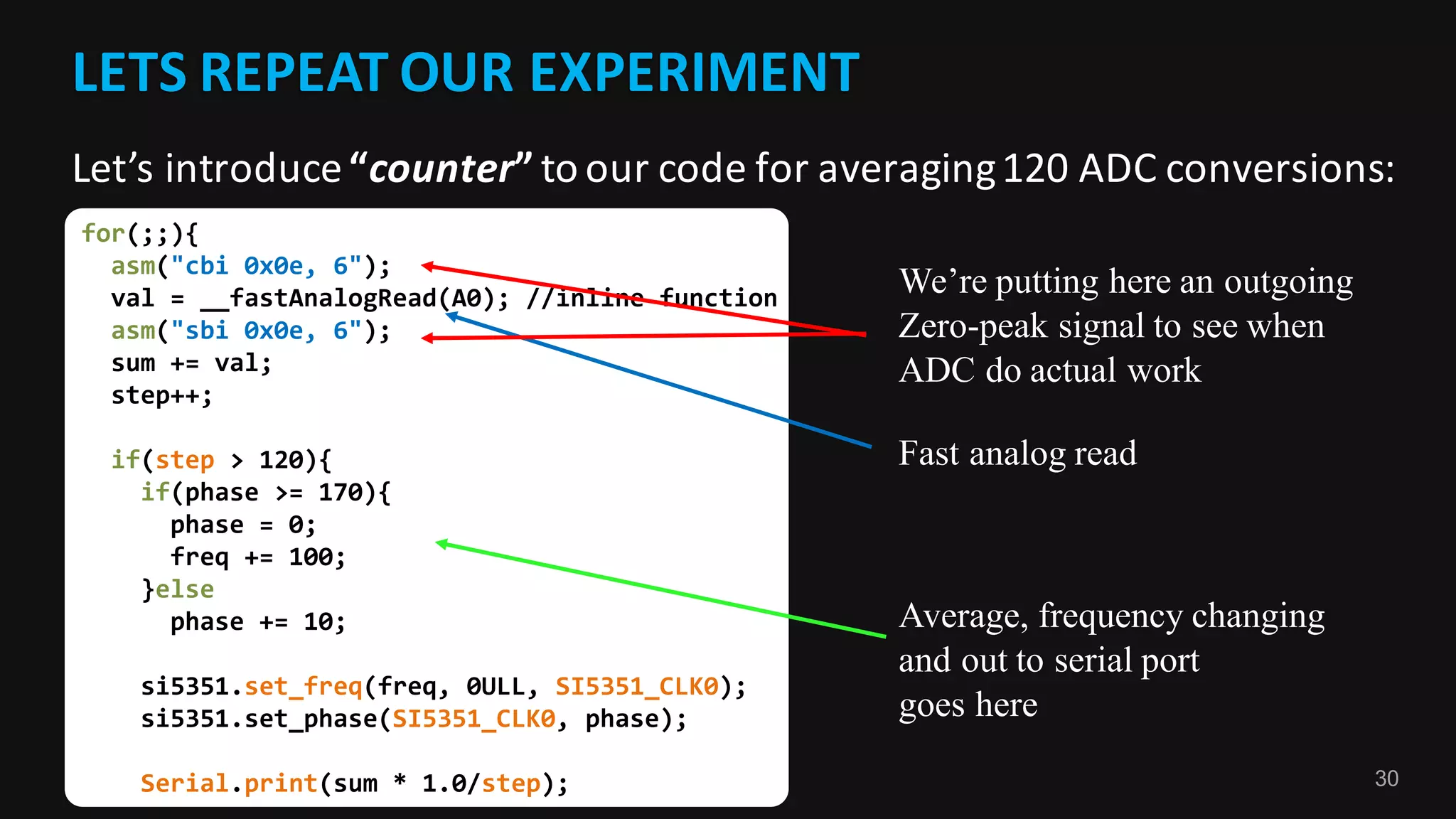
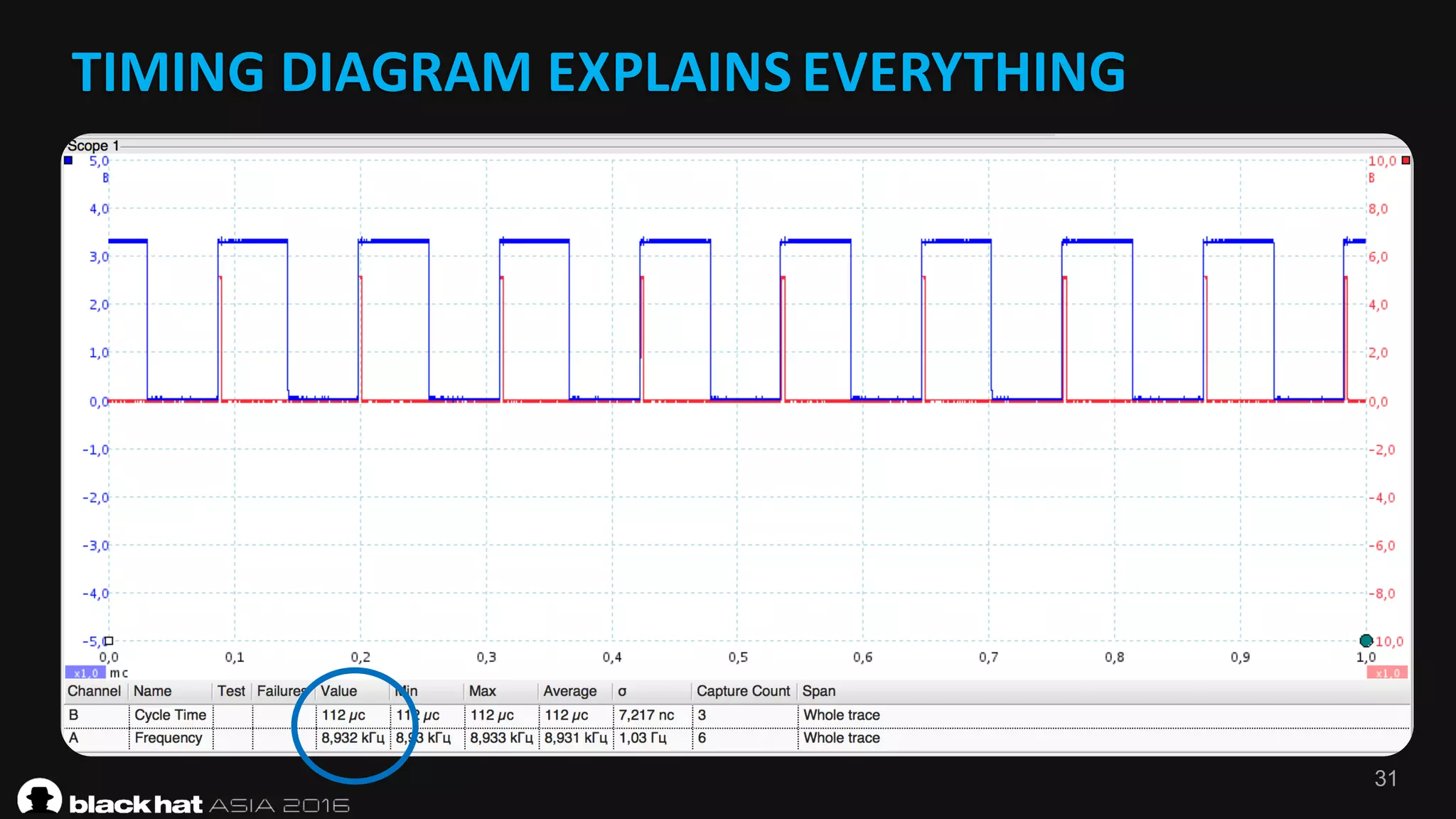
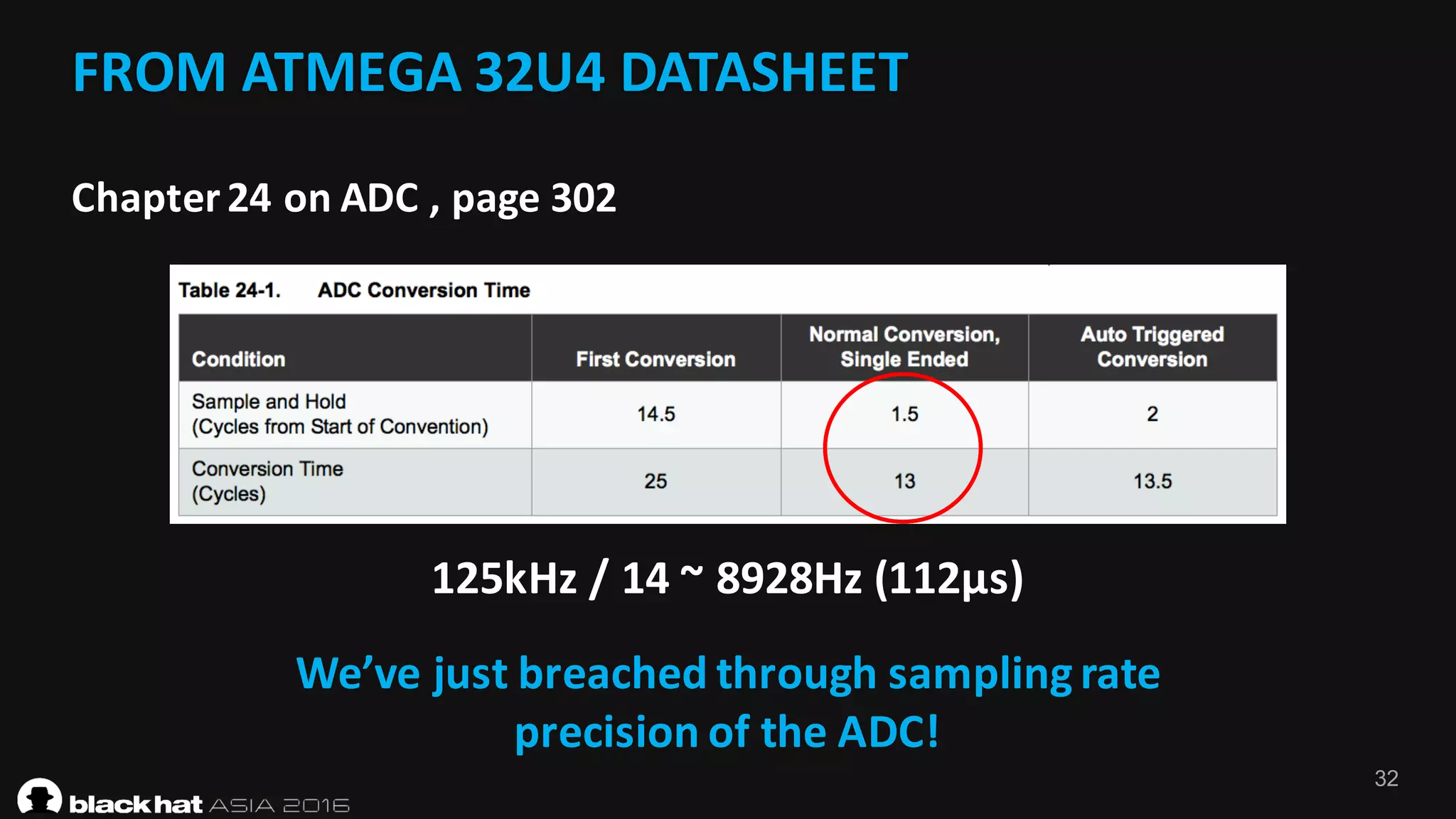
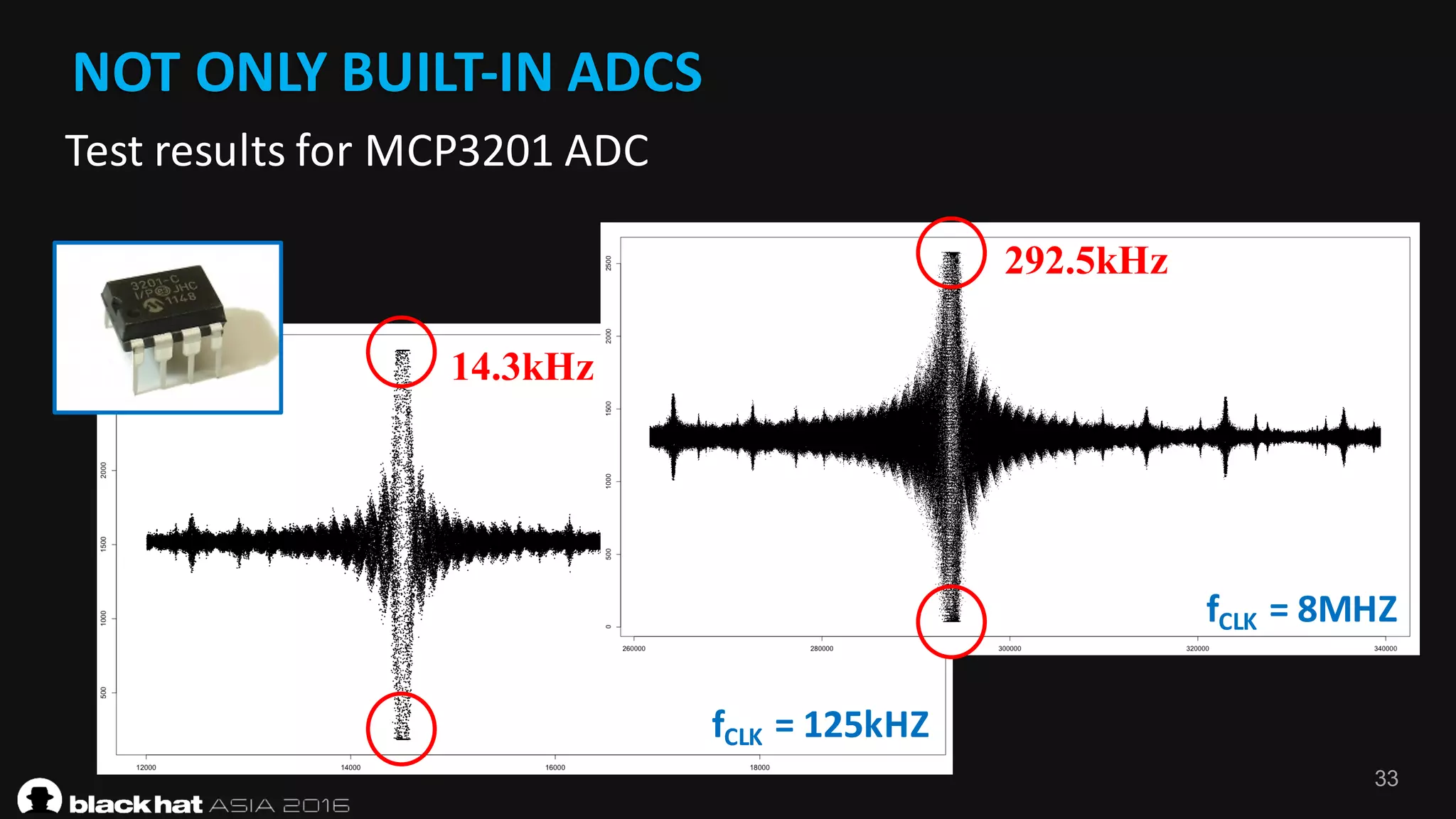
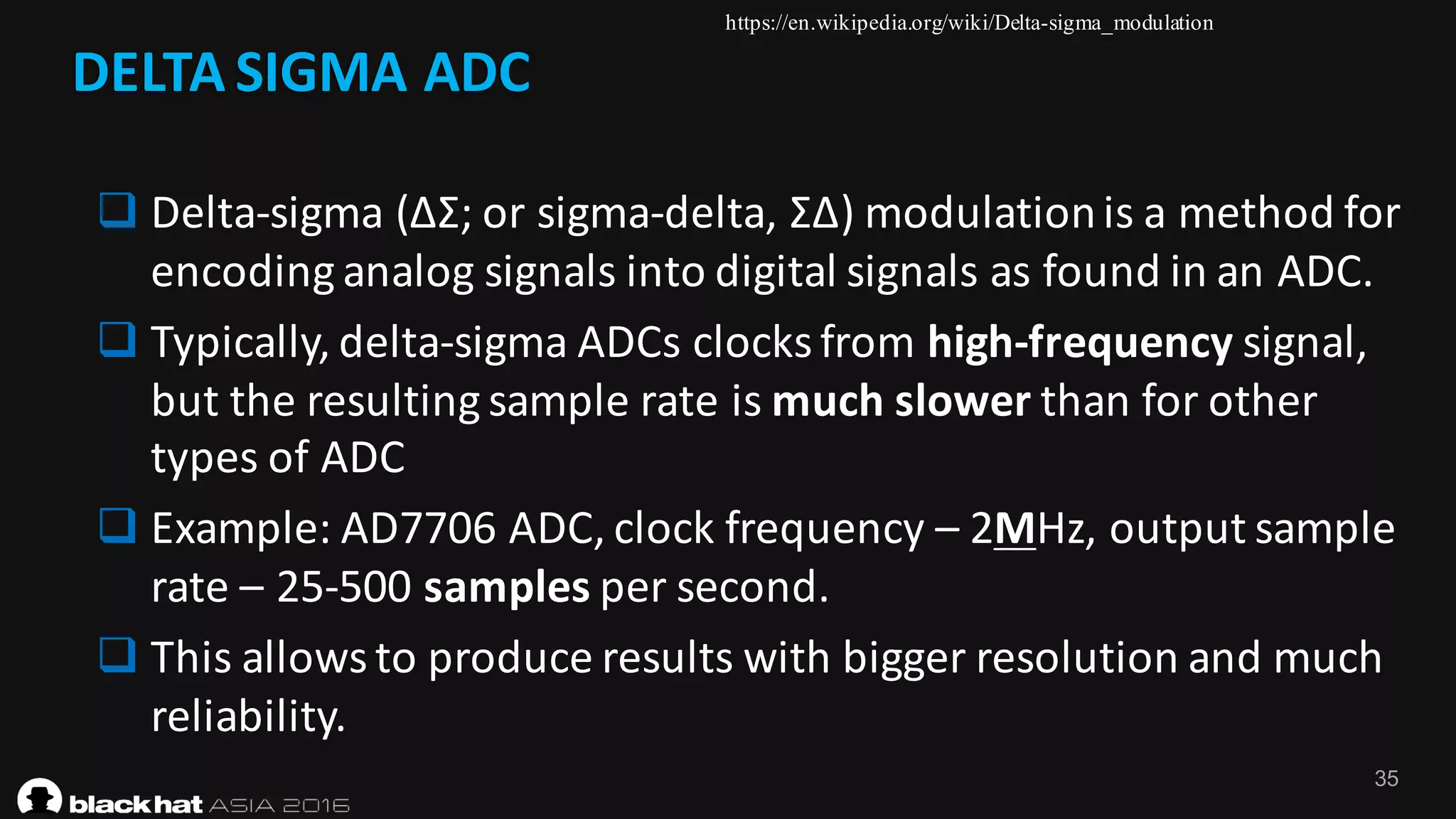
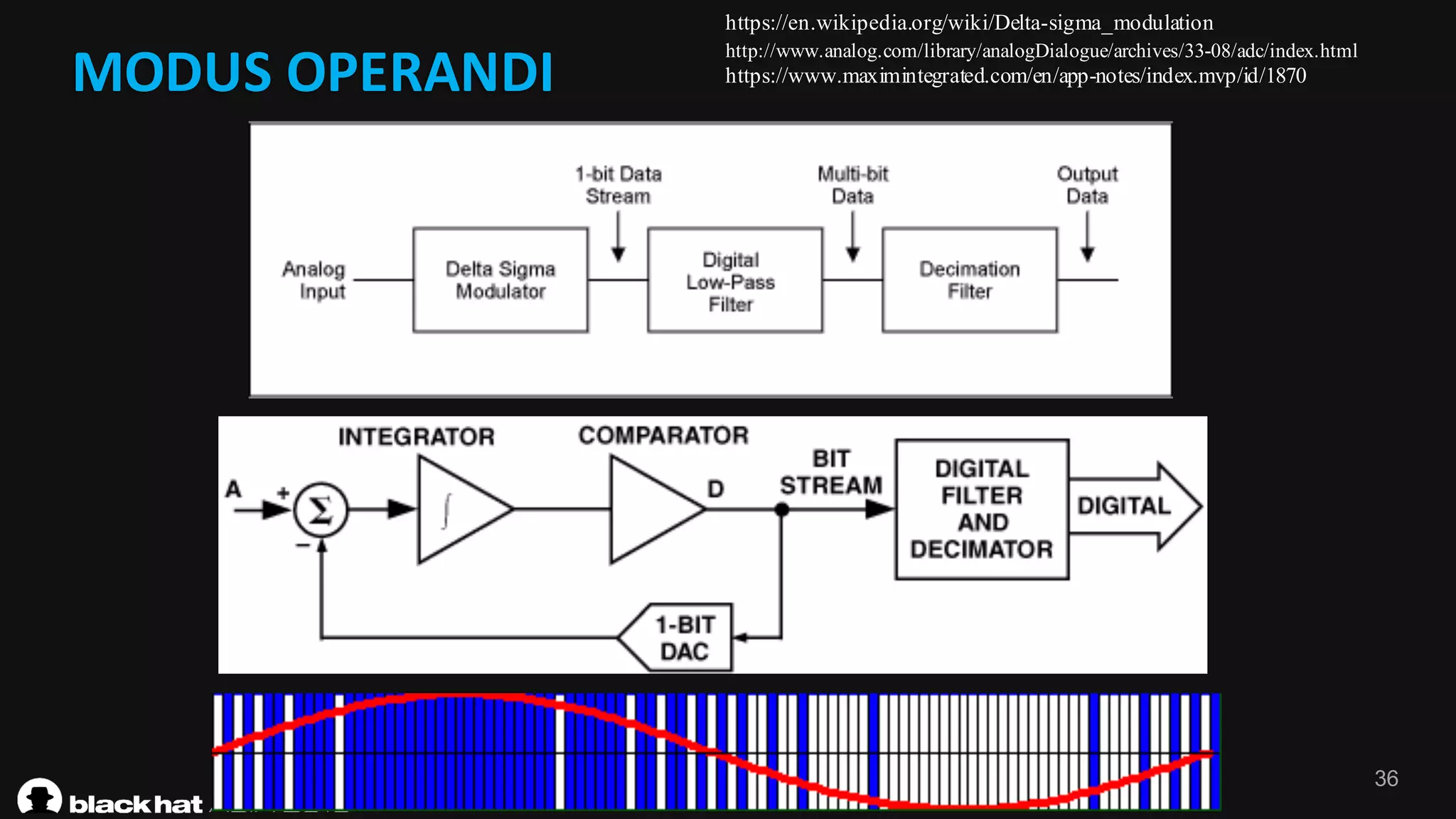
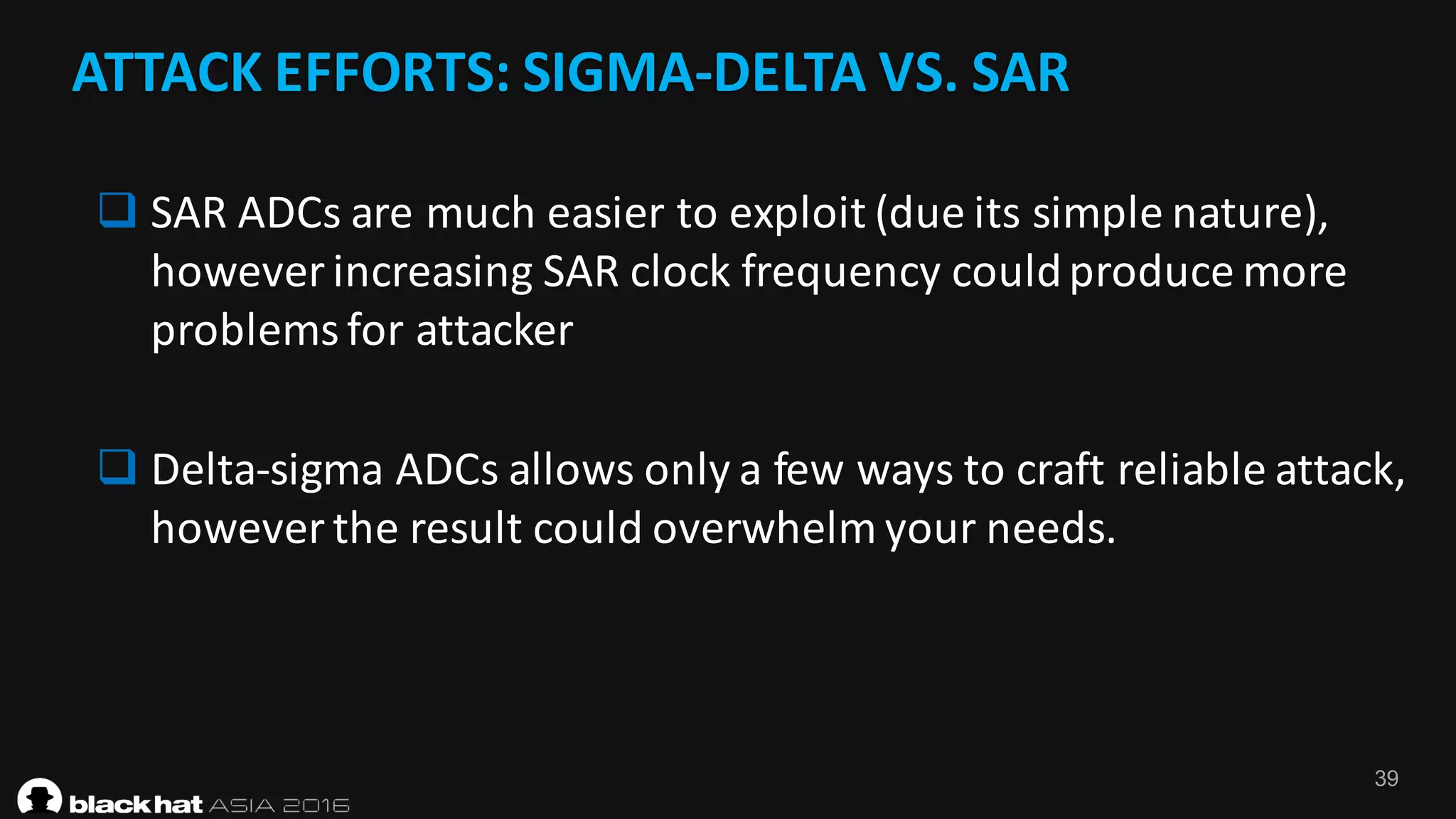
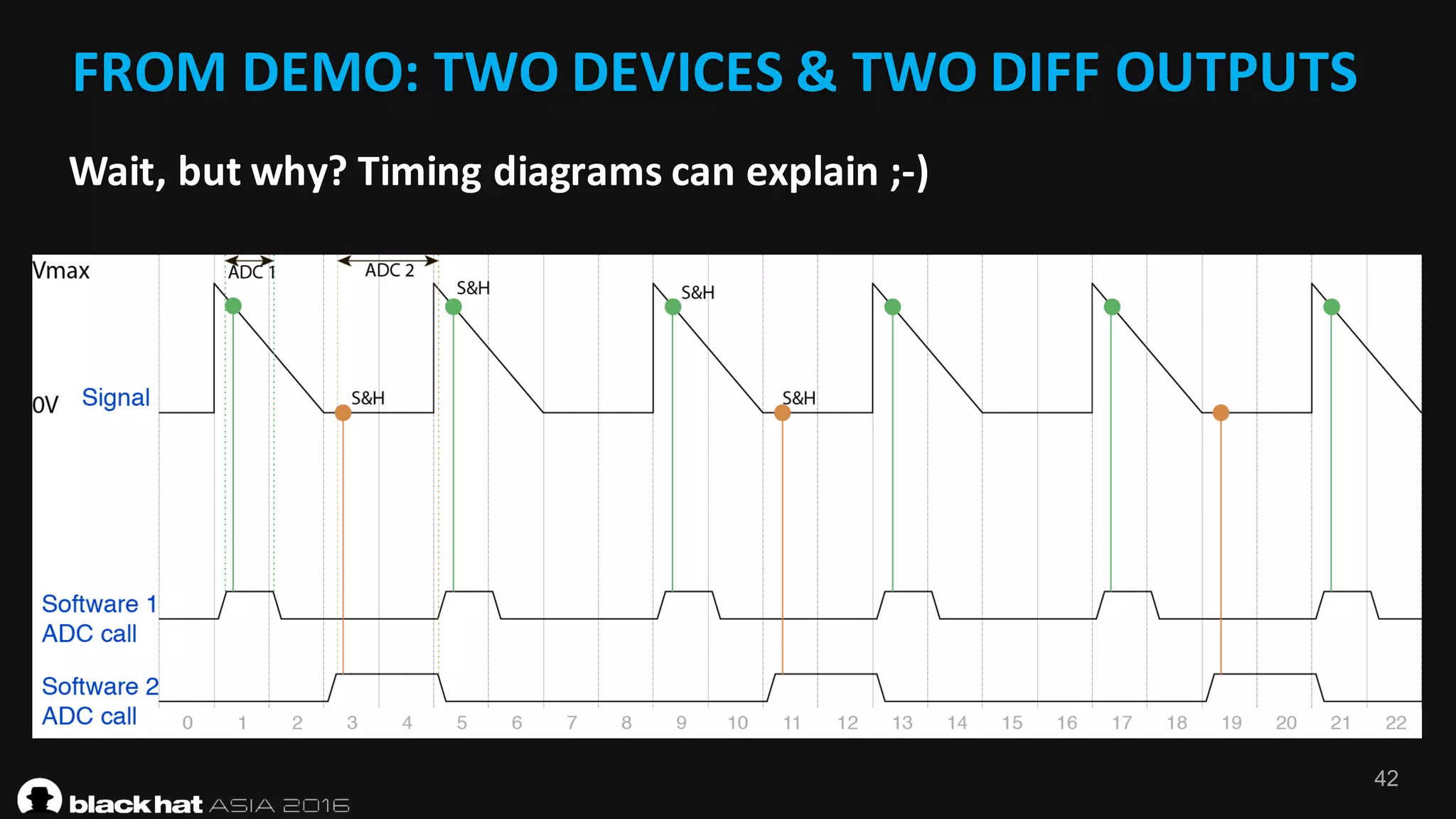
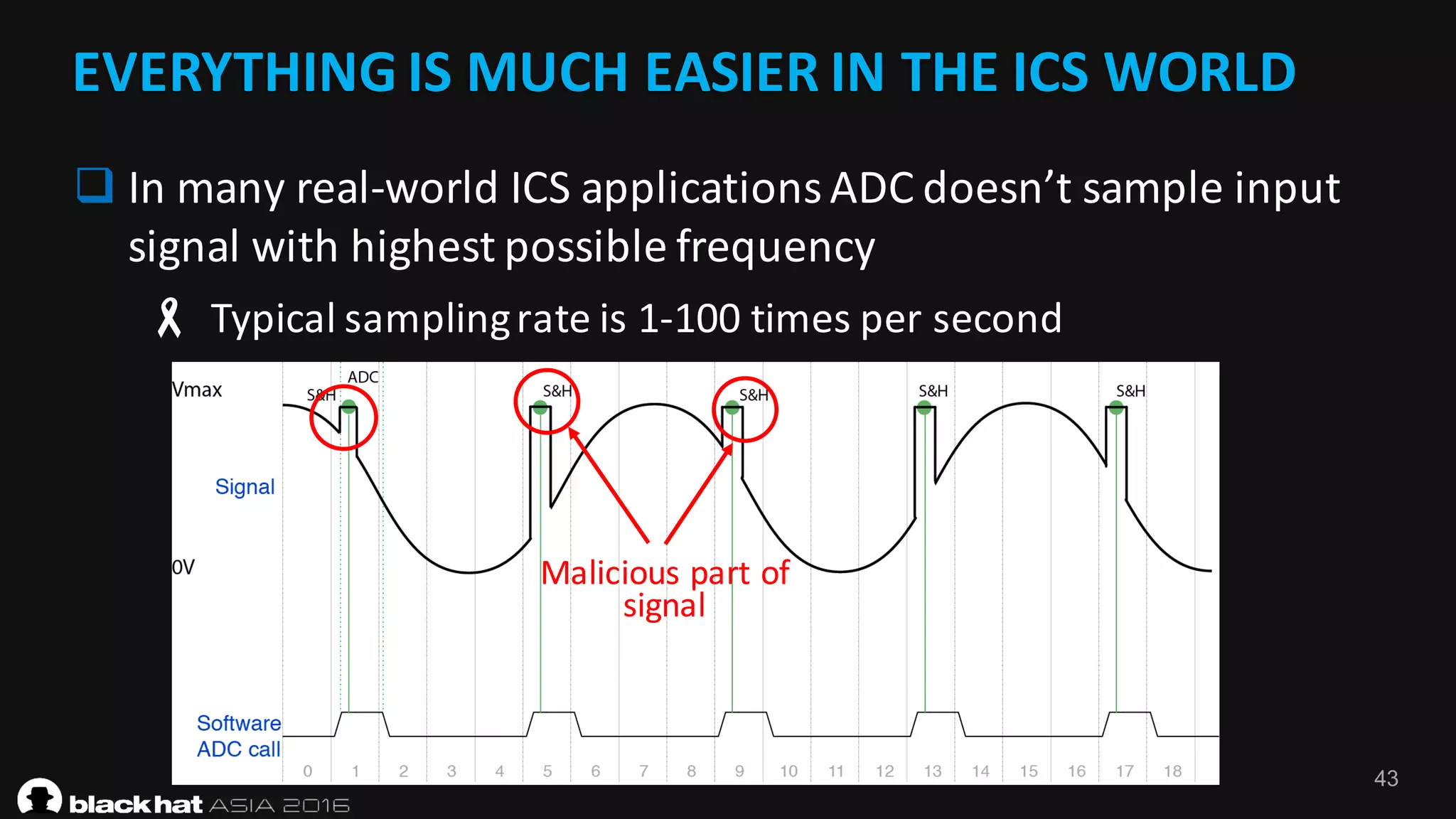
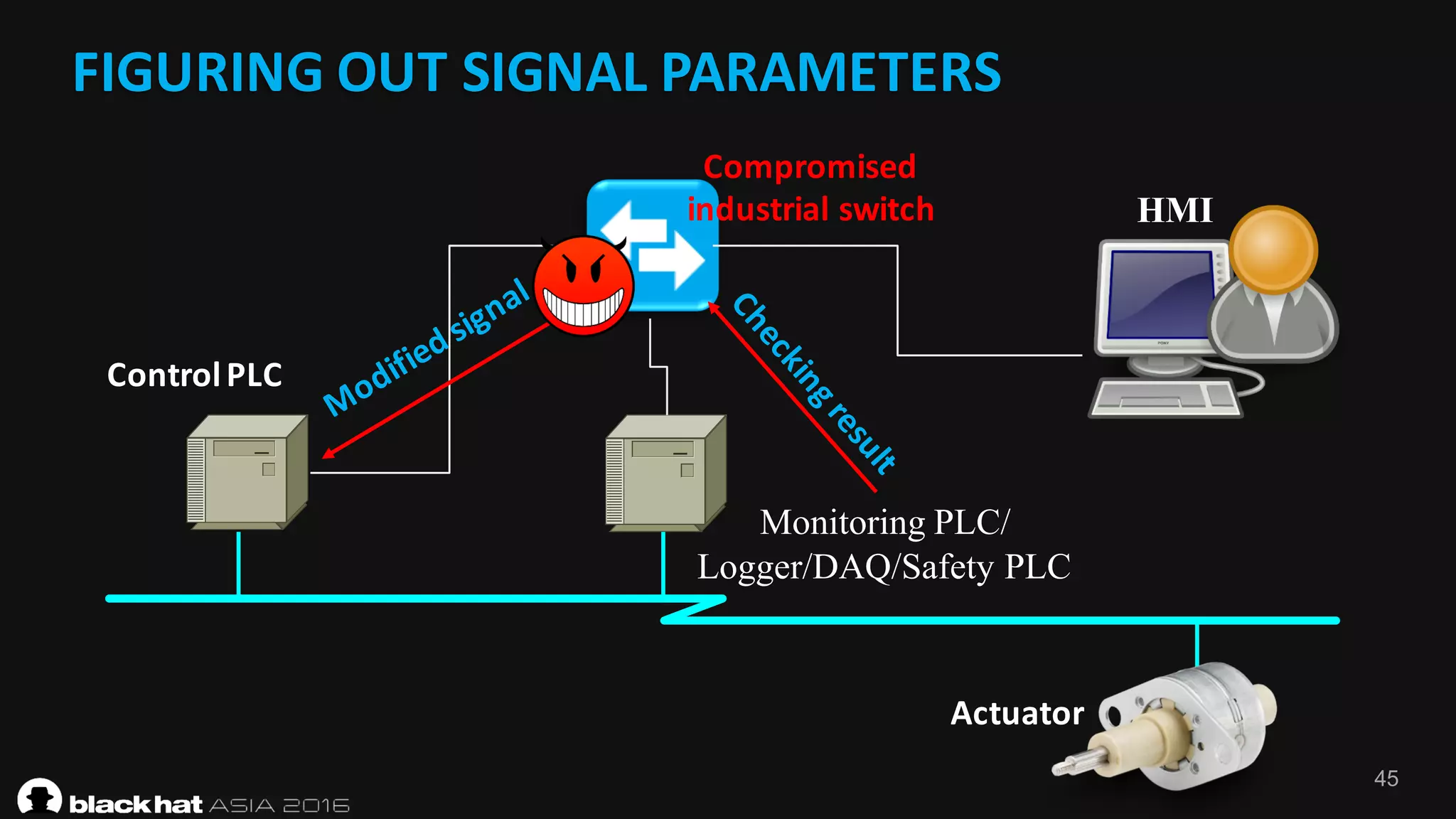
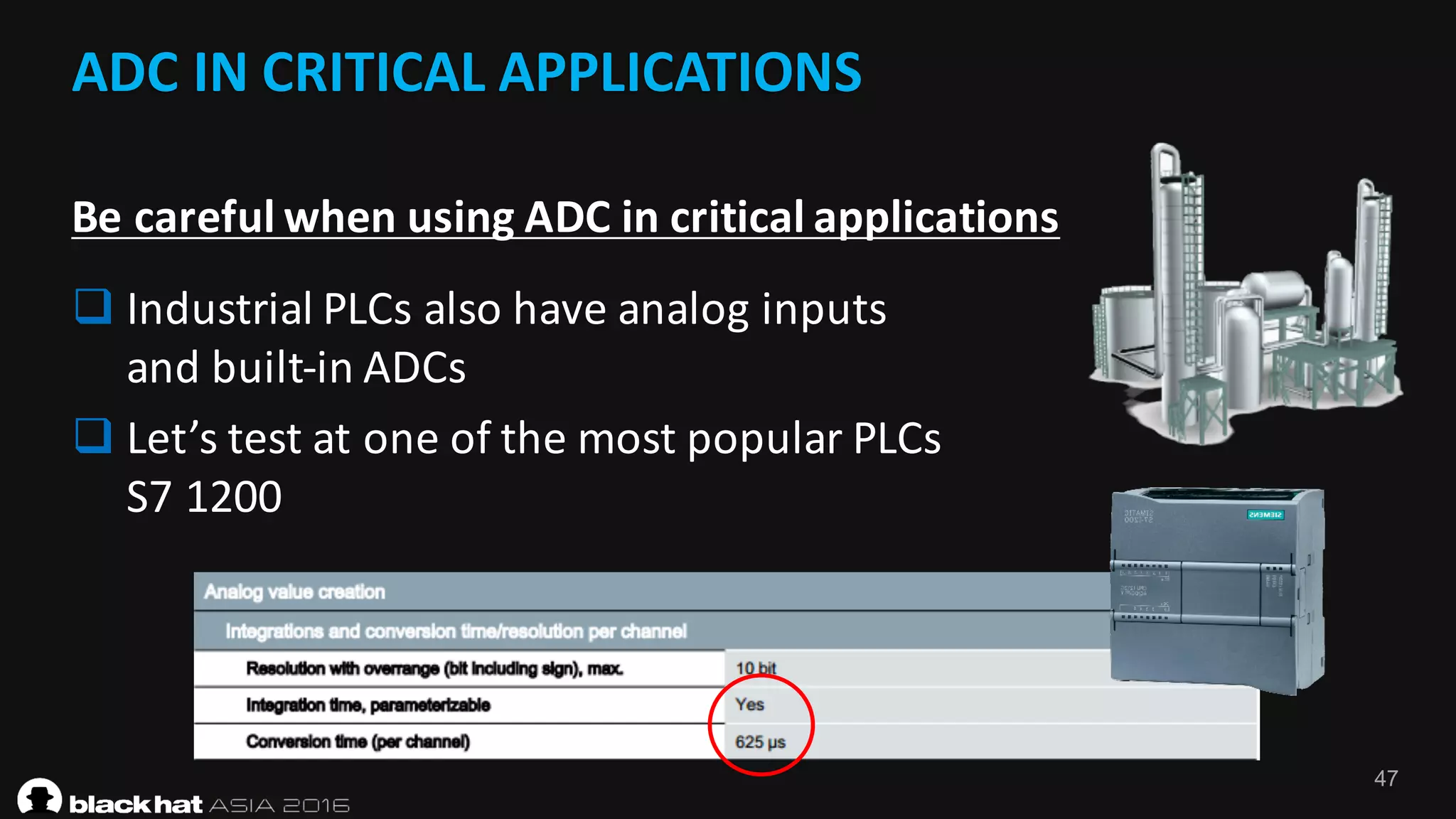
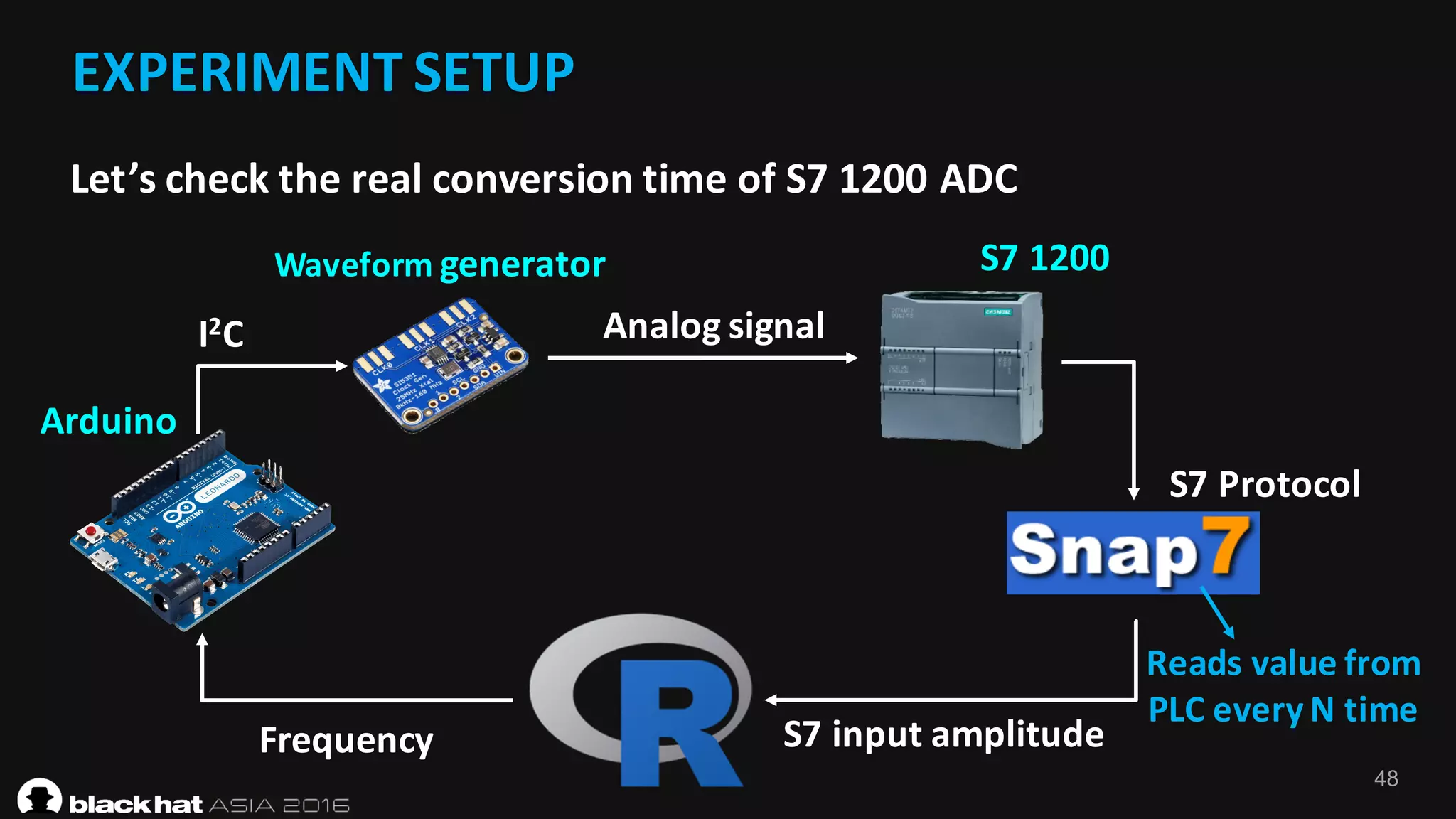
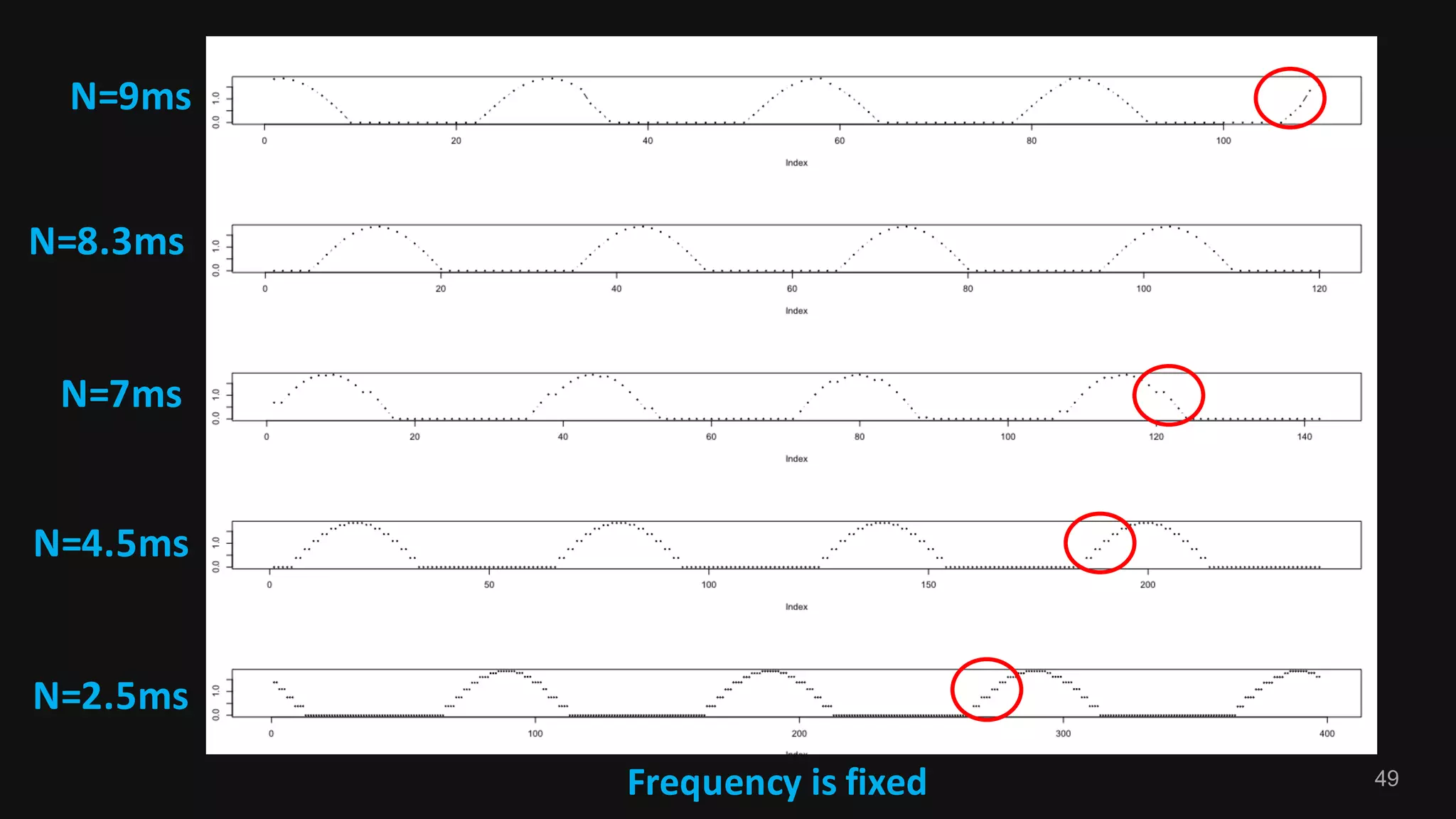
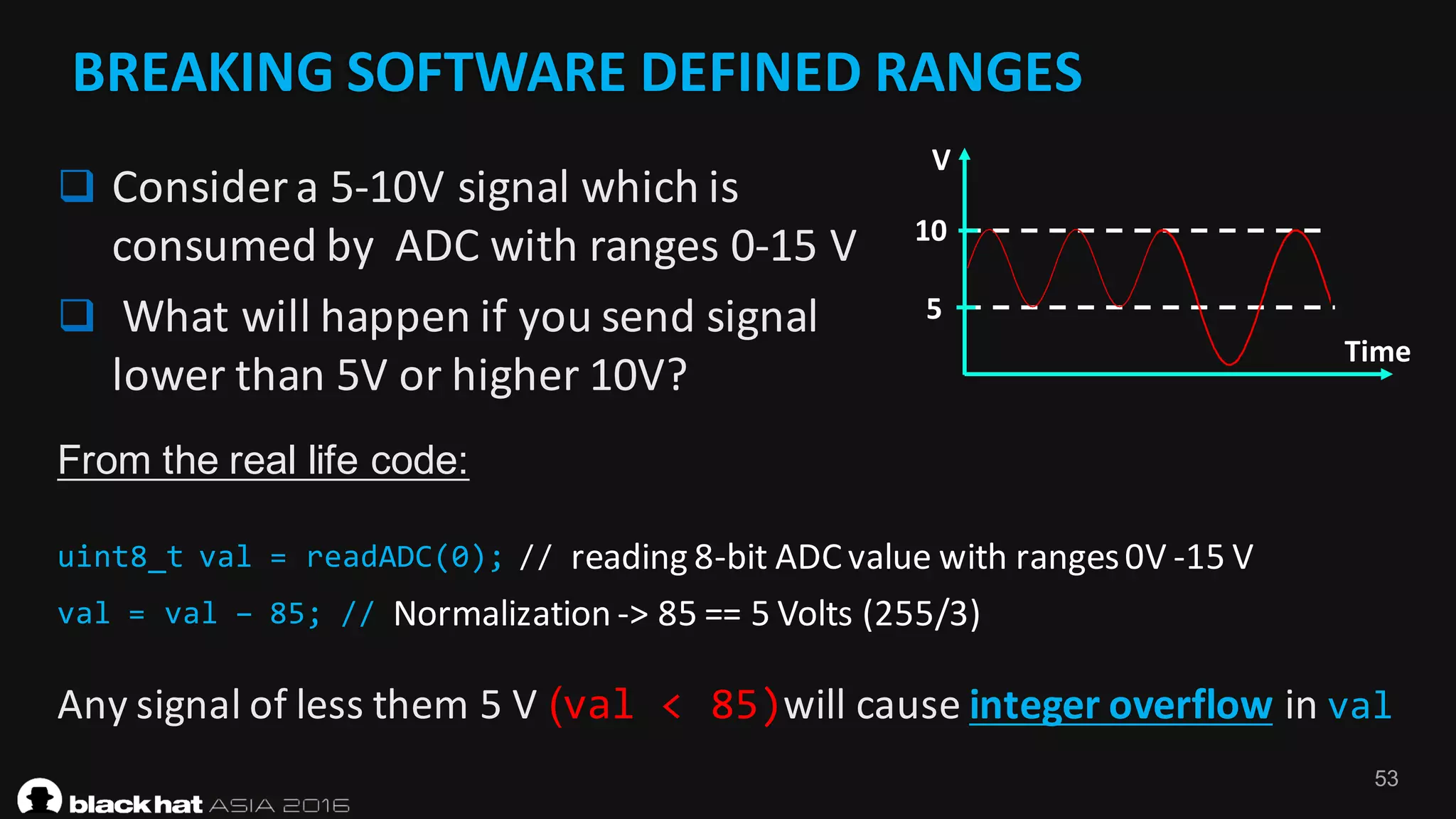
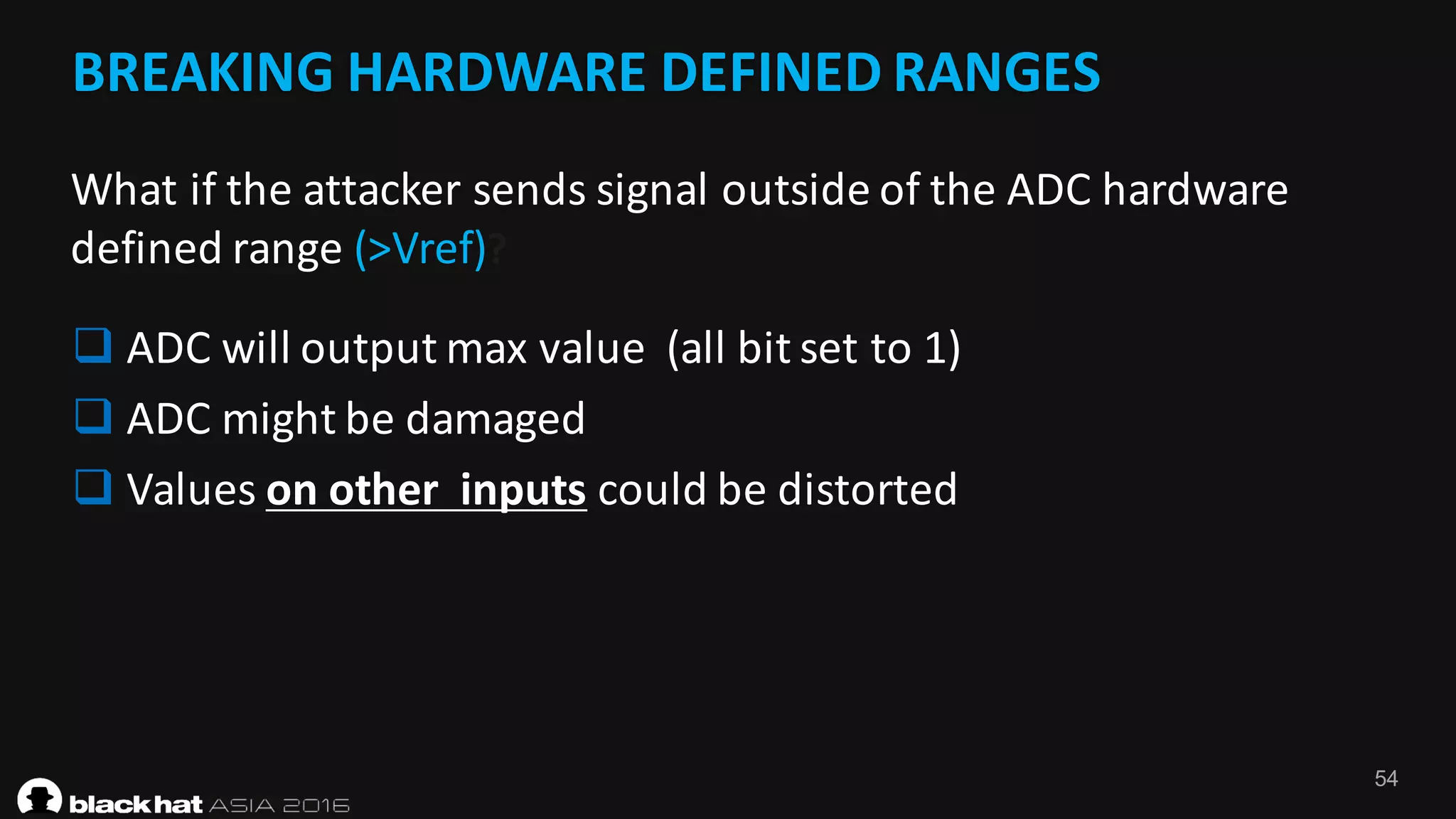
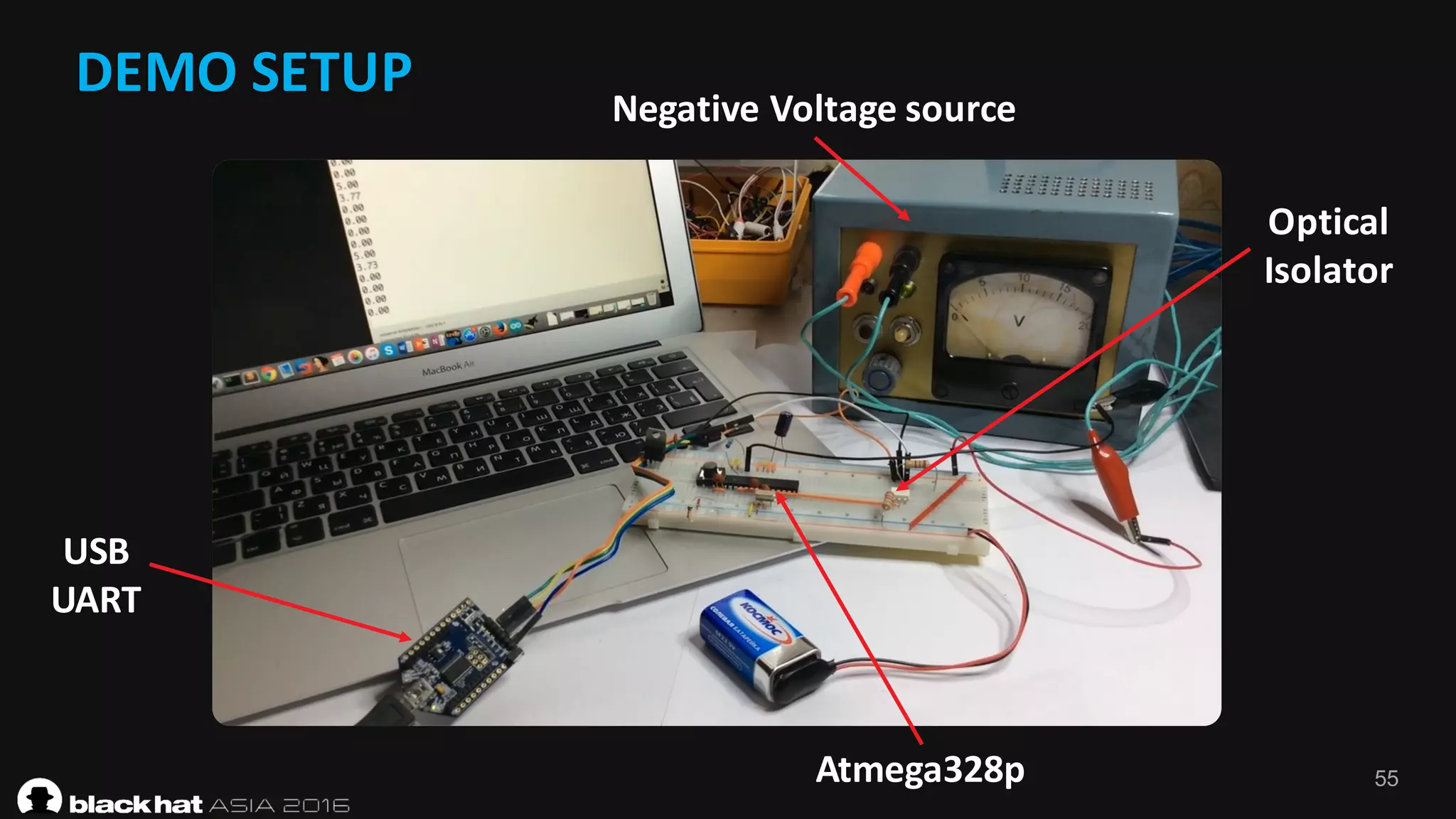
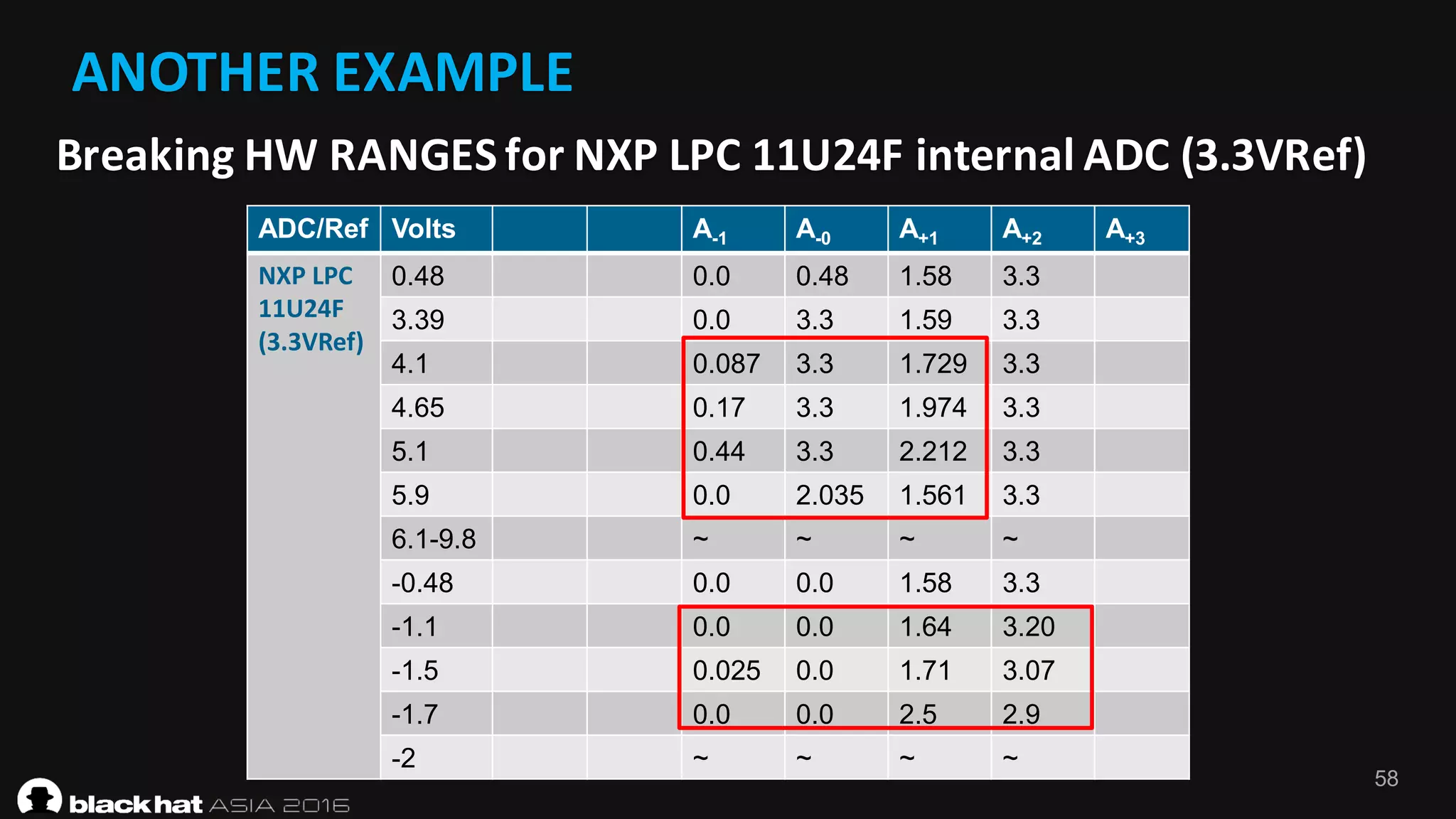
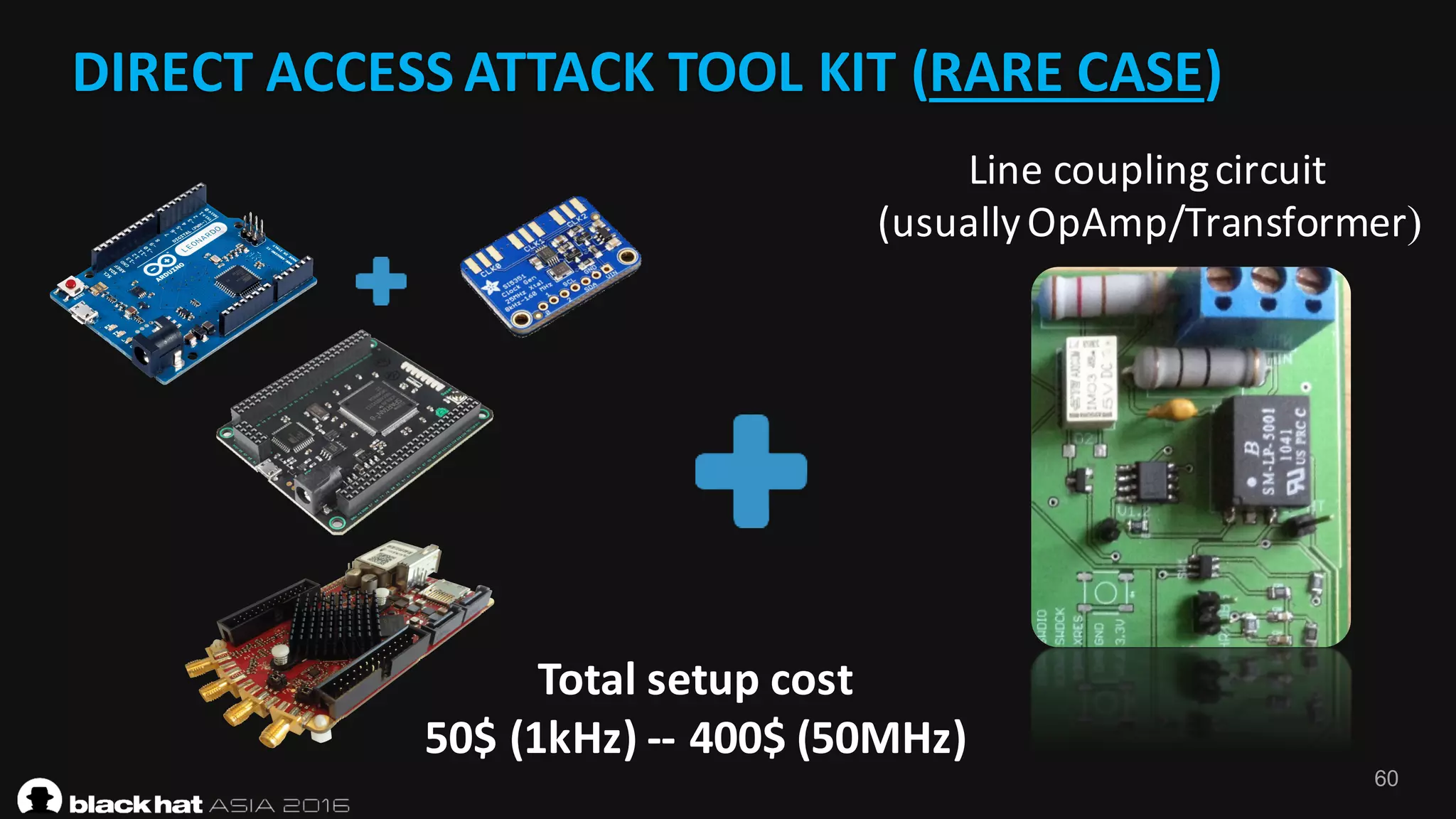
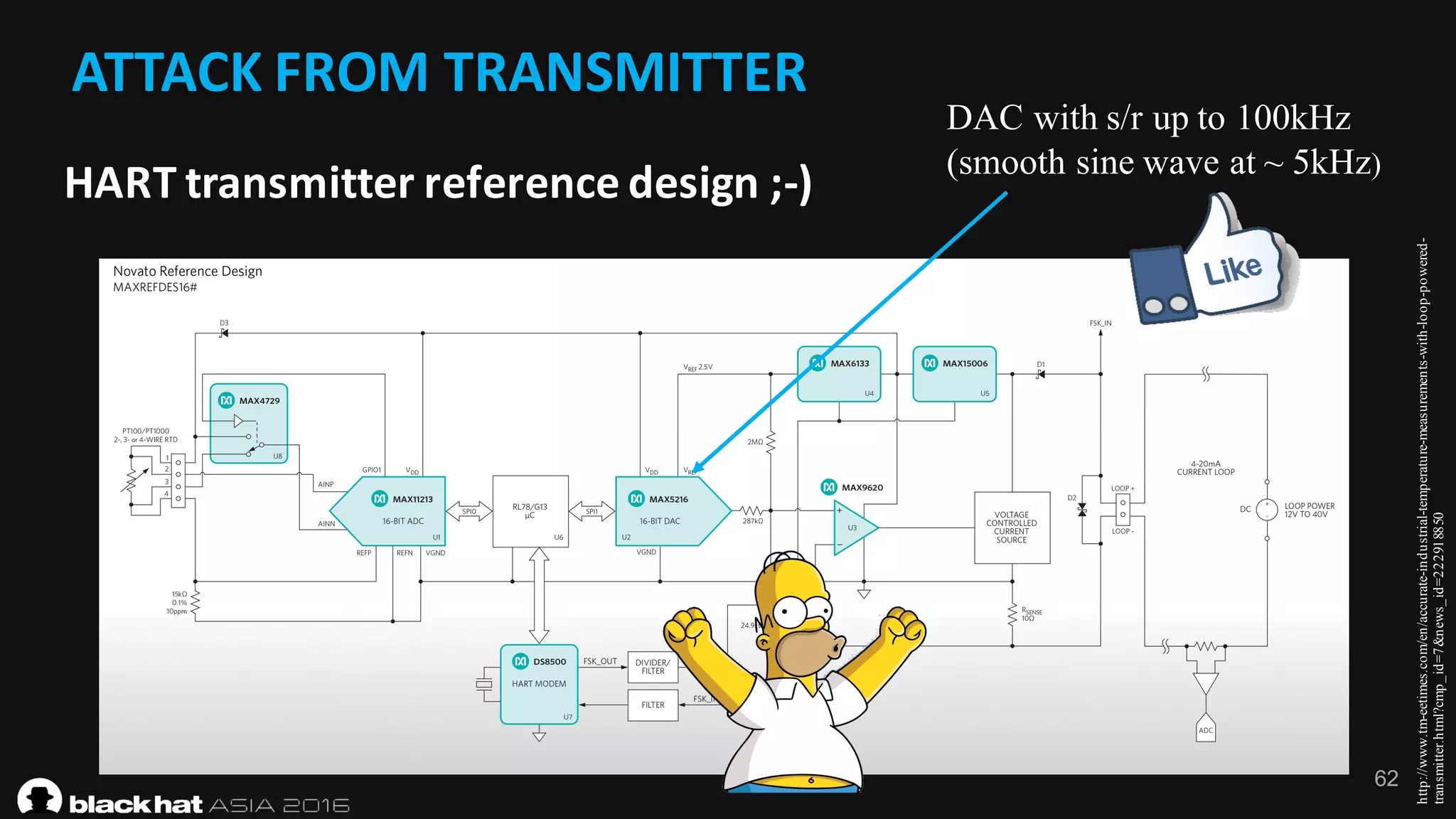
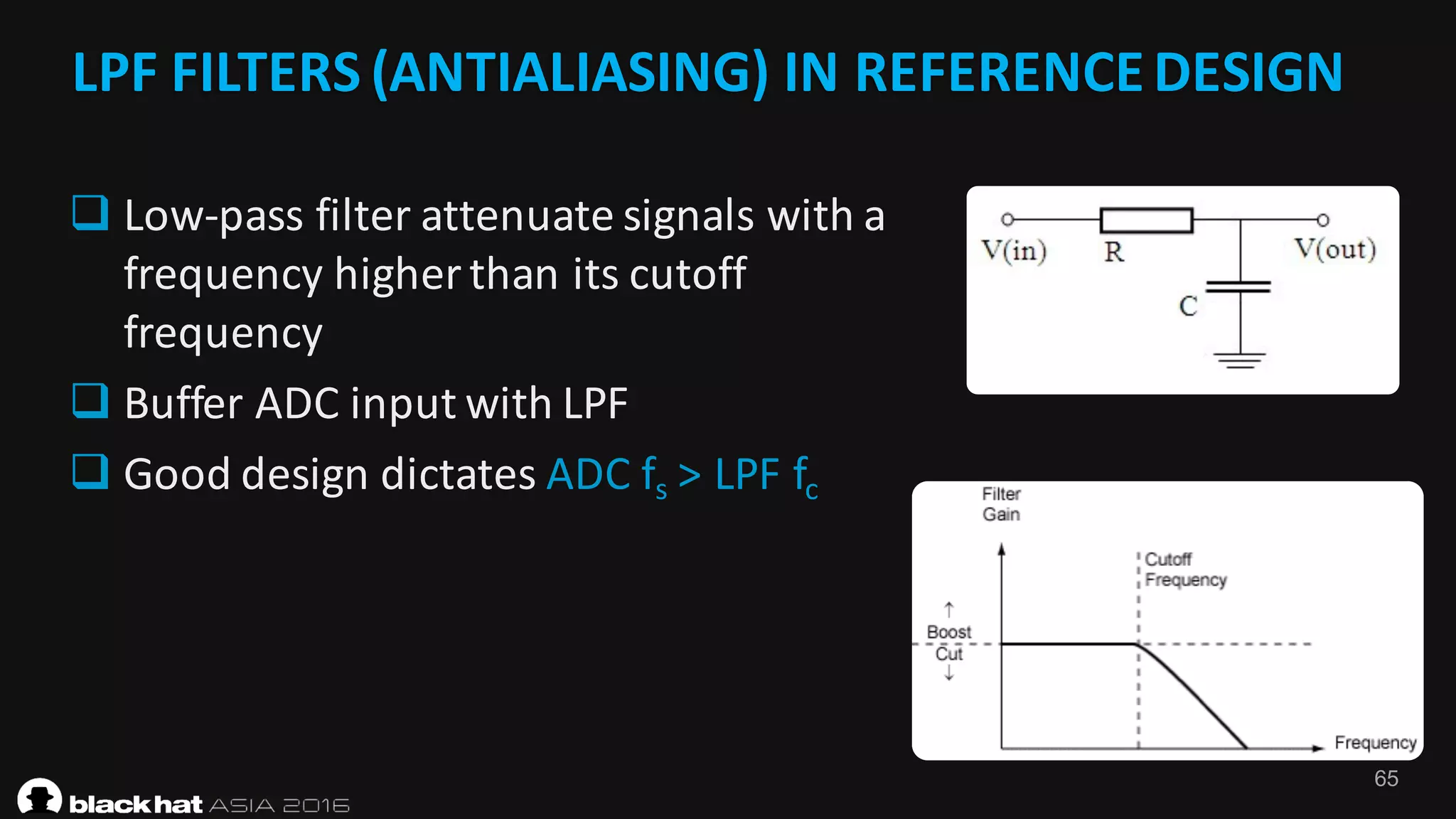
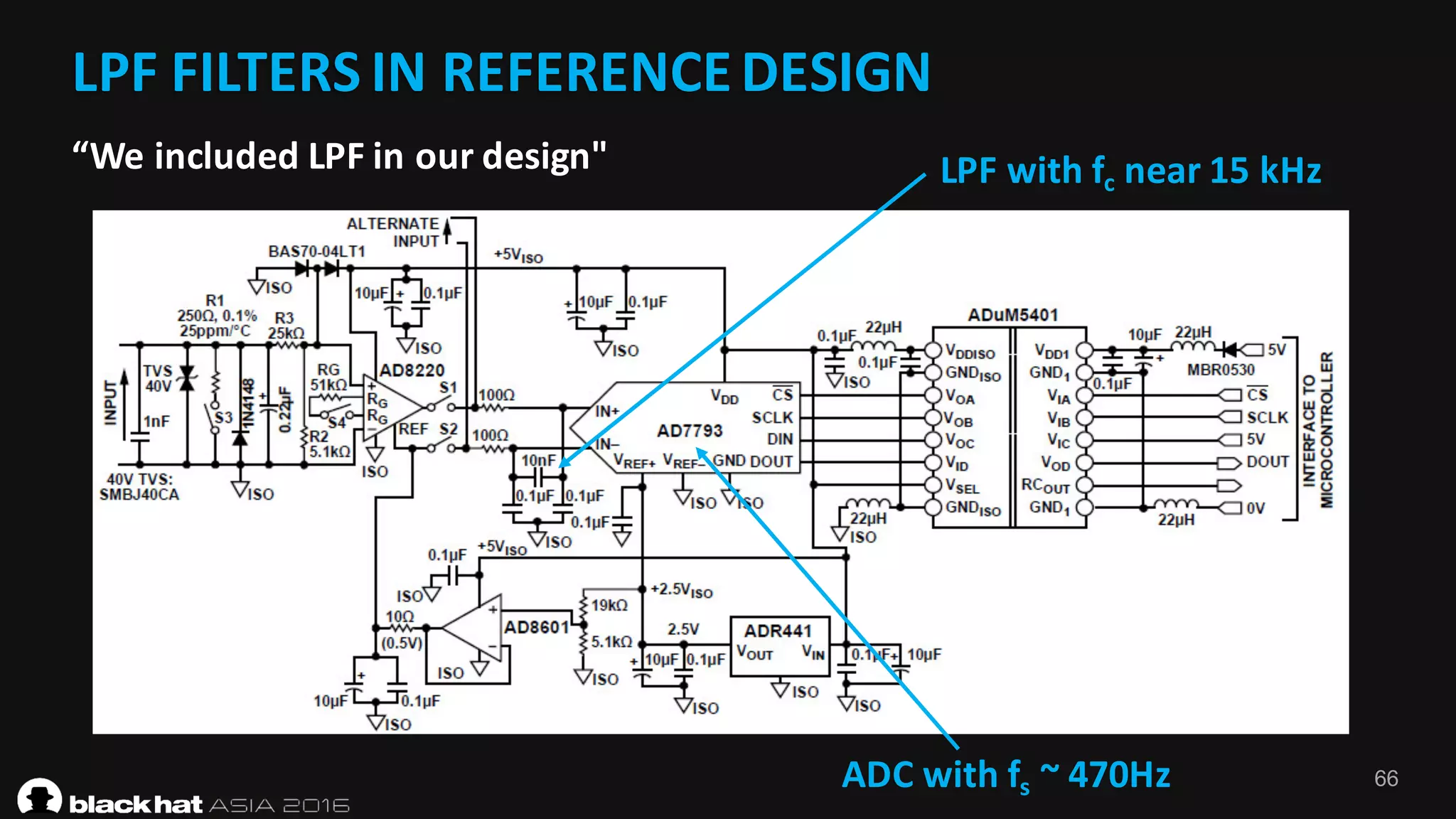
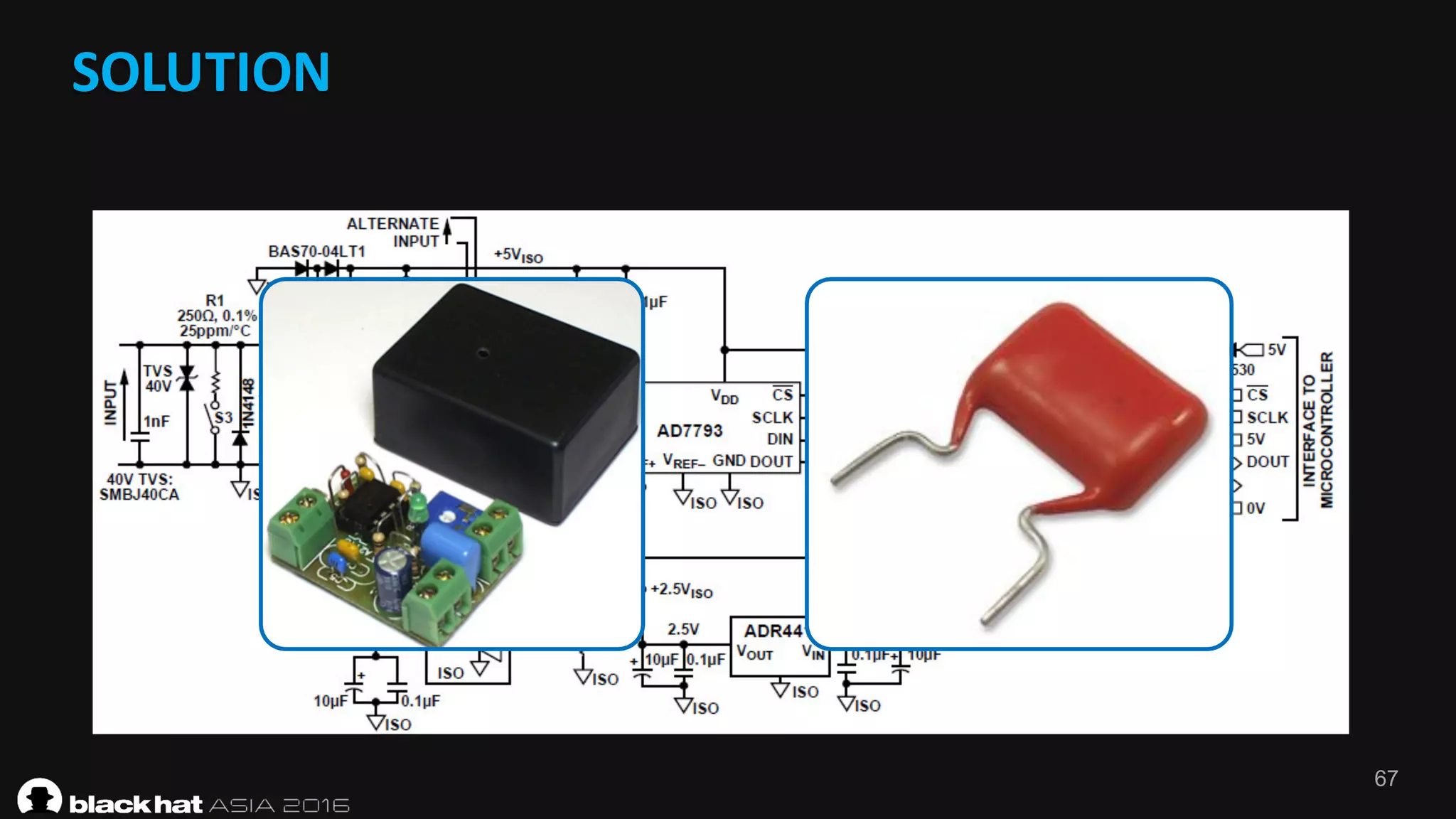
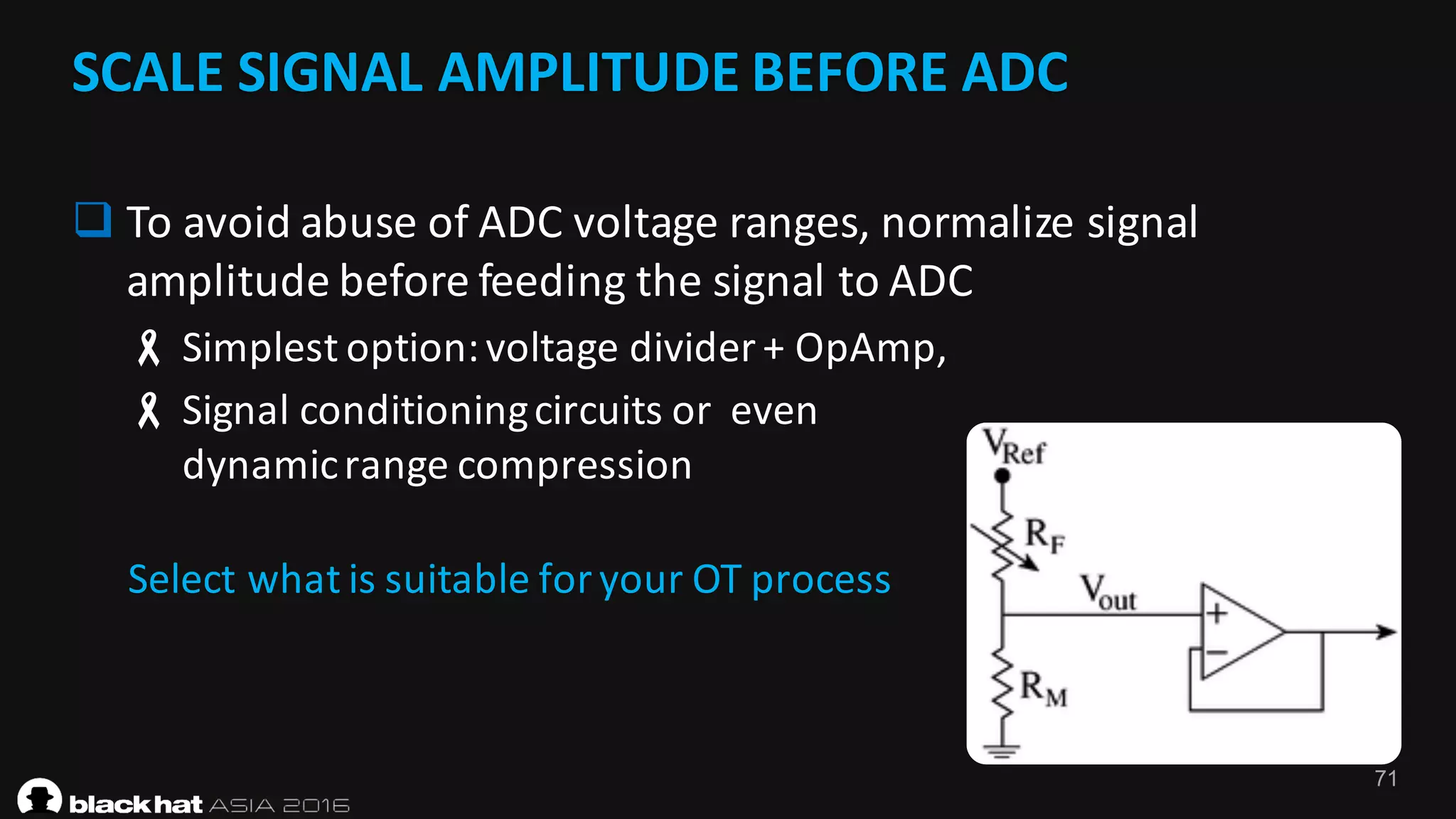
The document discusses attacking industrial control systems by exploiting vulnerabilities in analog-to-digital converters (ADCs). It describes how generating signals at specific frequencies and amplitudes can cause ADCs to output incorrect digital values, potentially compromising sensor monitoring systems. Several proof-of-concept attacks are demonstrated, including generating signals that race the ADC clock, exceed the valid amplitude range, or produce different readings from multiple ADCs measuring the same signal. The document warns that many industrial systems have vulnerabilities in their analog interfacing that could allow remote manipulation if exploited.