The document provides an overview of network security essentials, including:
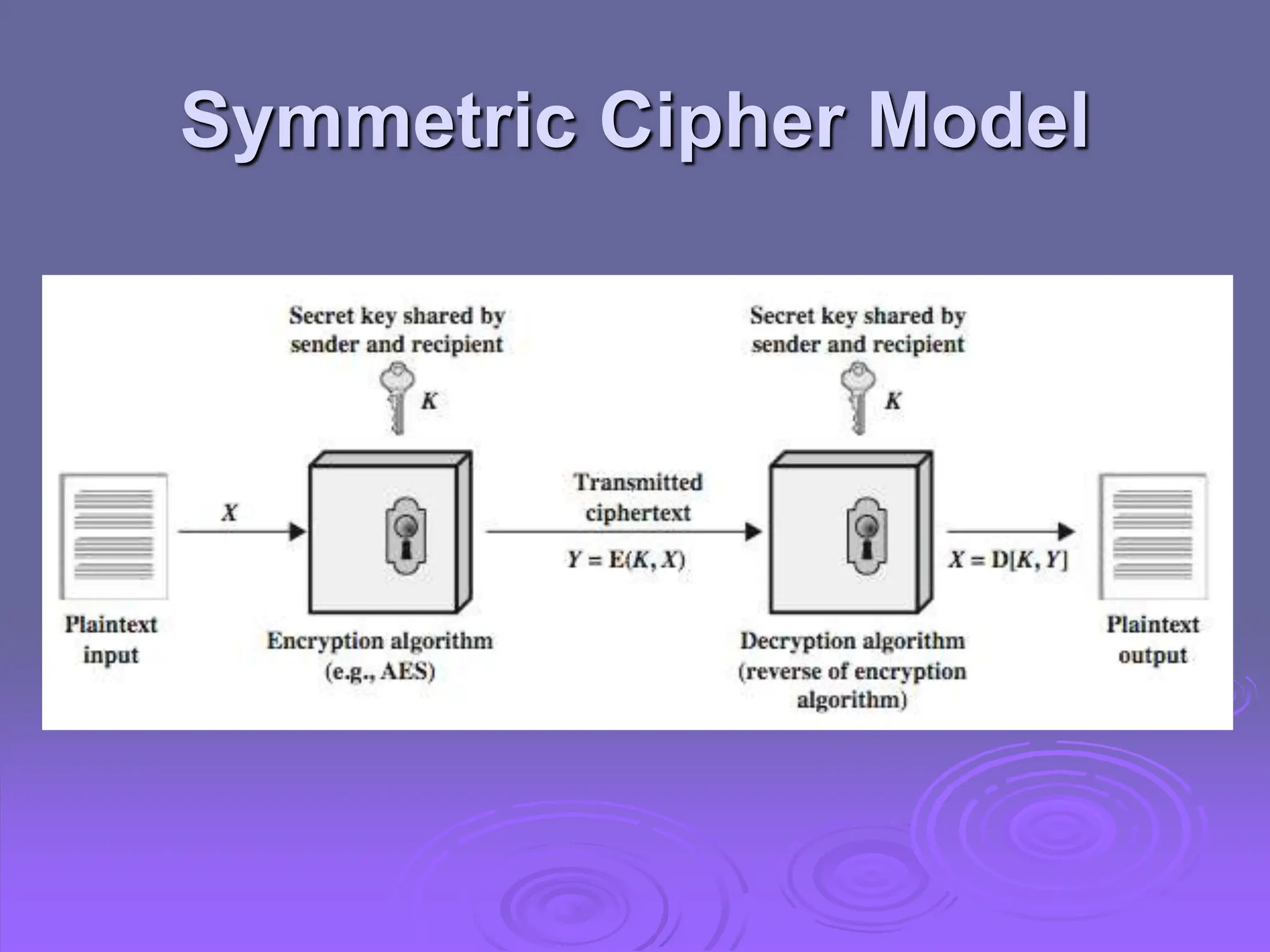
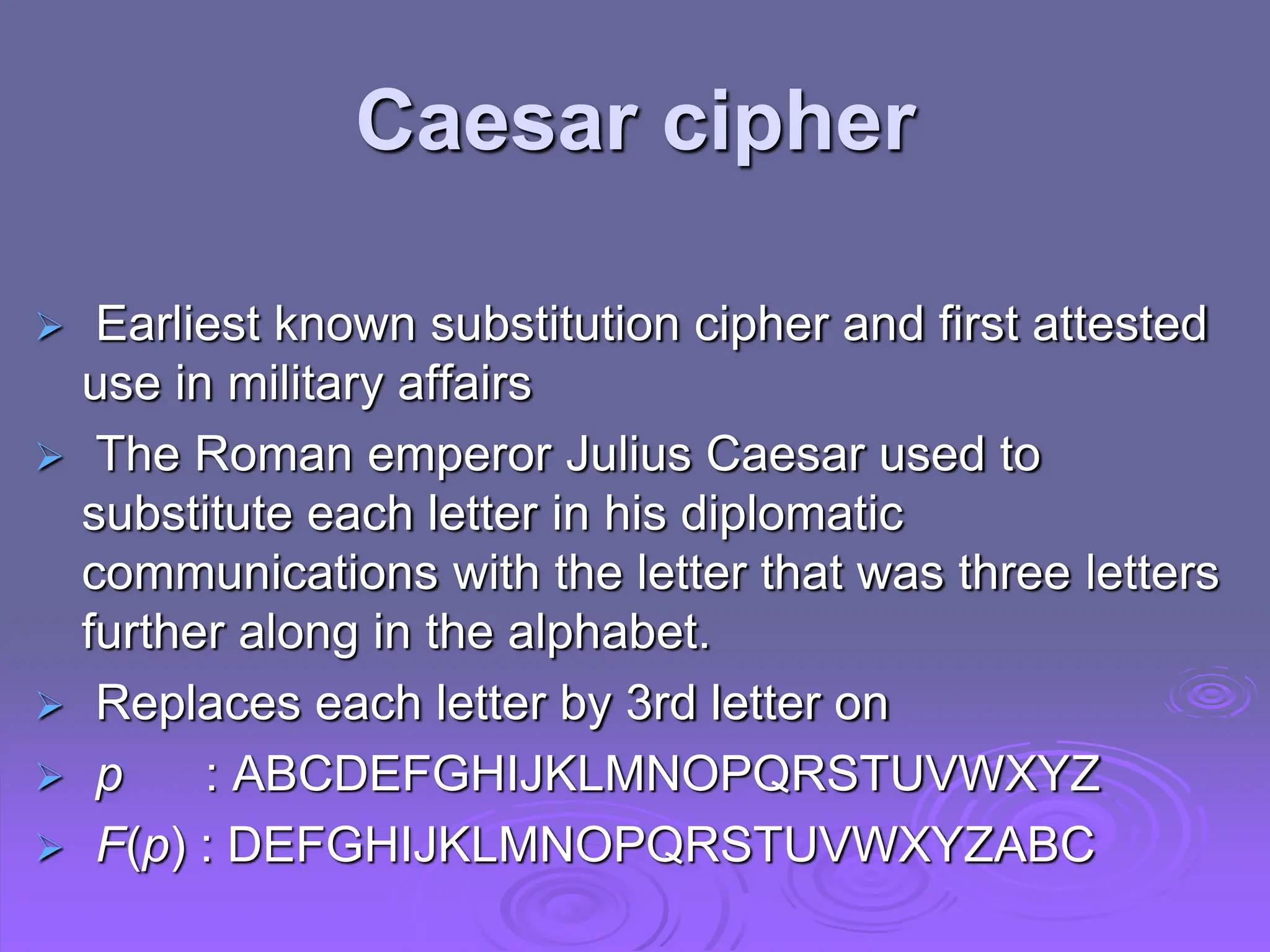
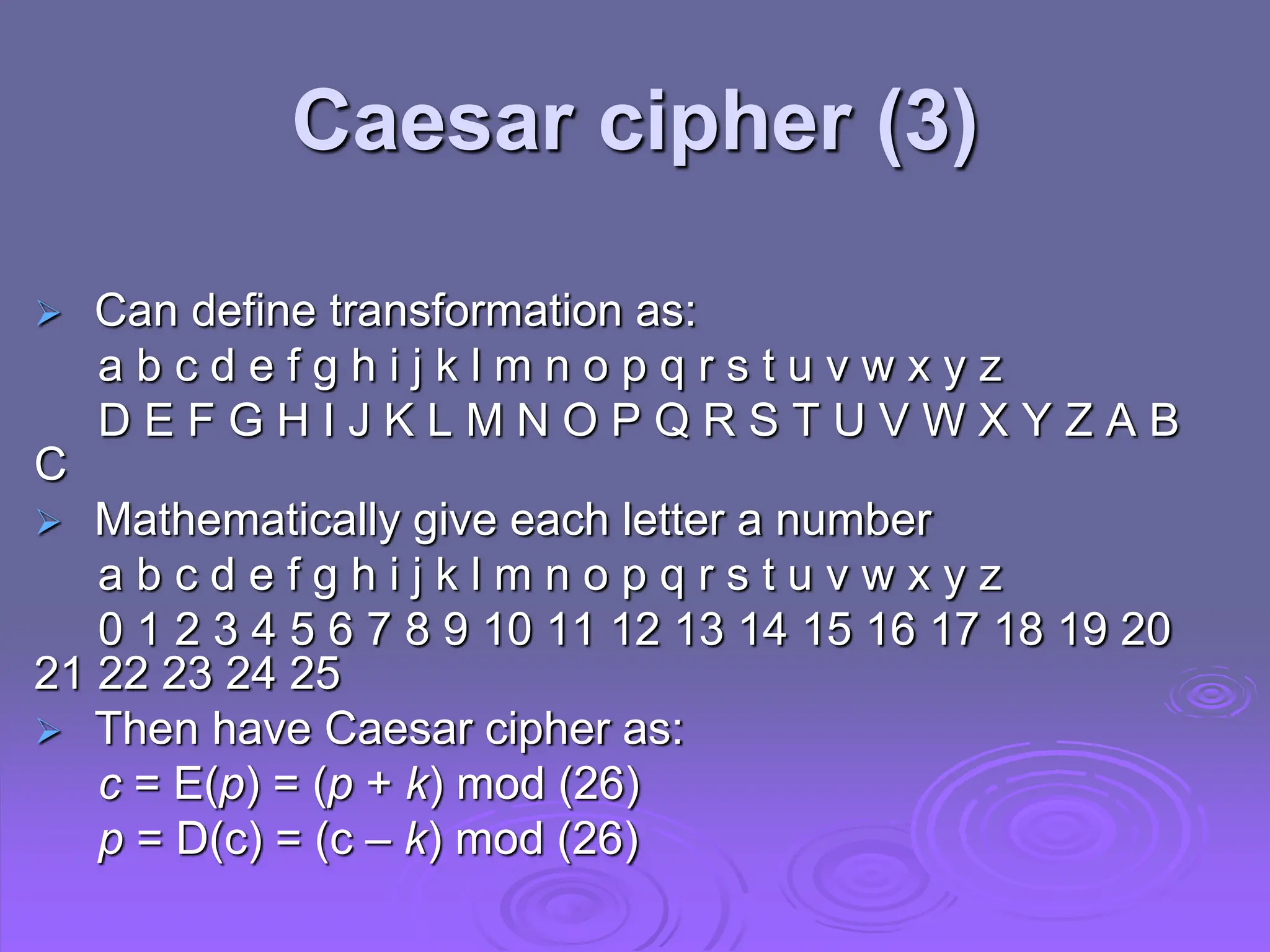
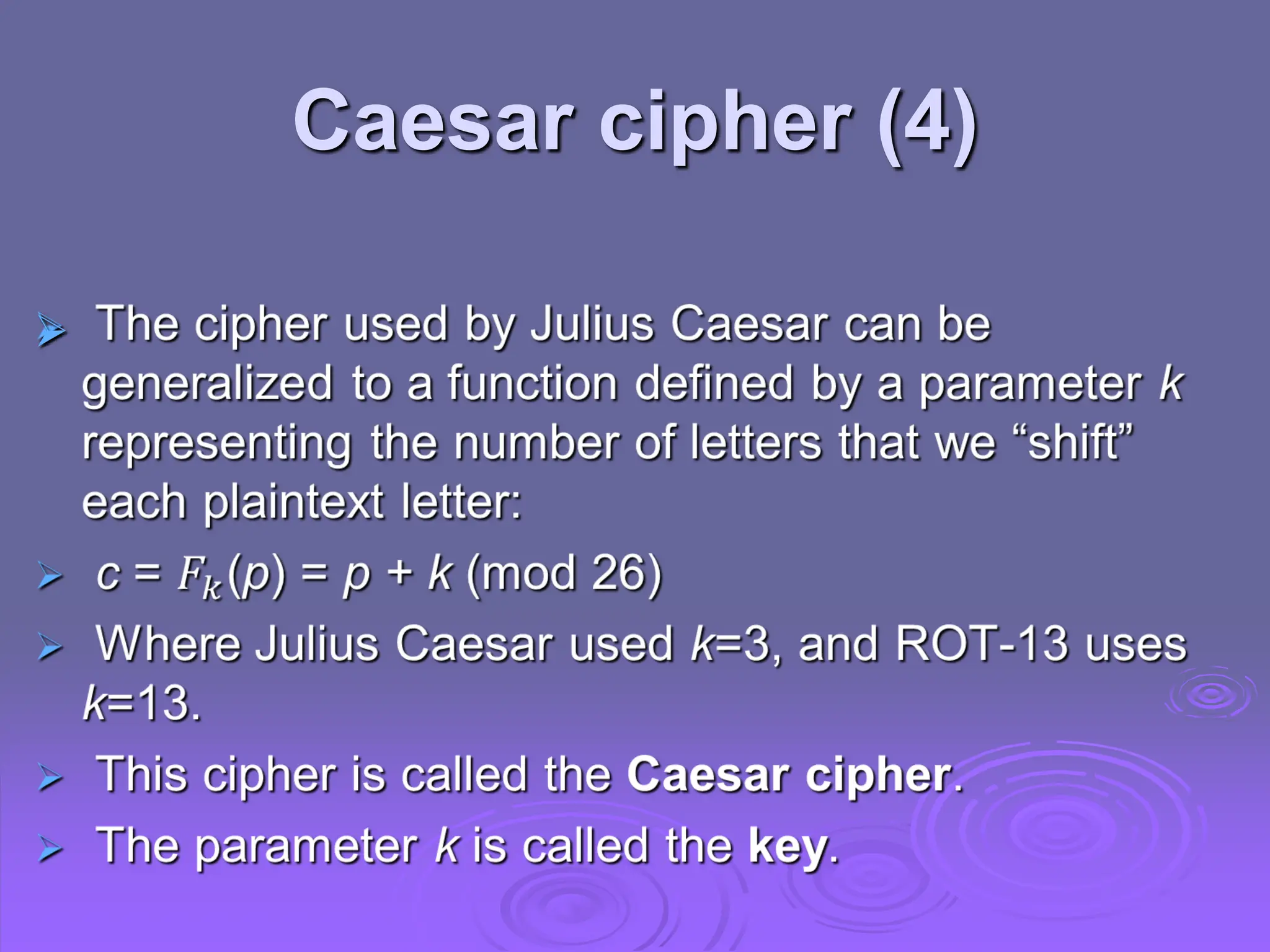
1. Symmetric encryption uses a shared secret key between sender and receiver to encrypt and decrypt messages. Common symmetric algorithms include the Shift Cipher and Caesar Cipher.
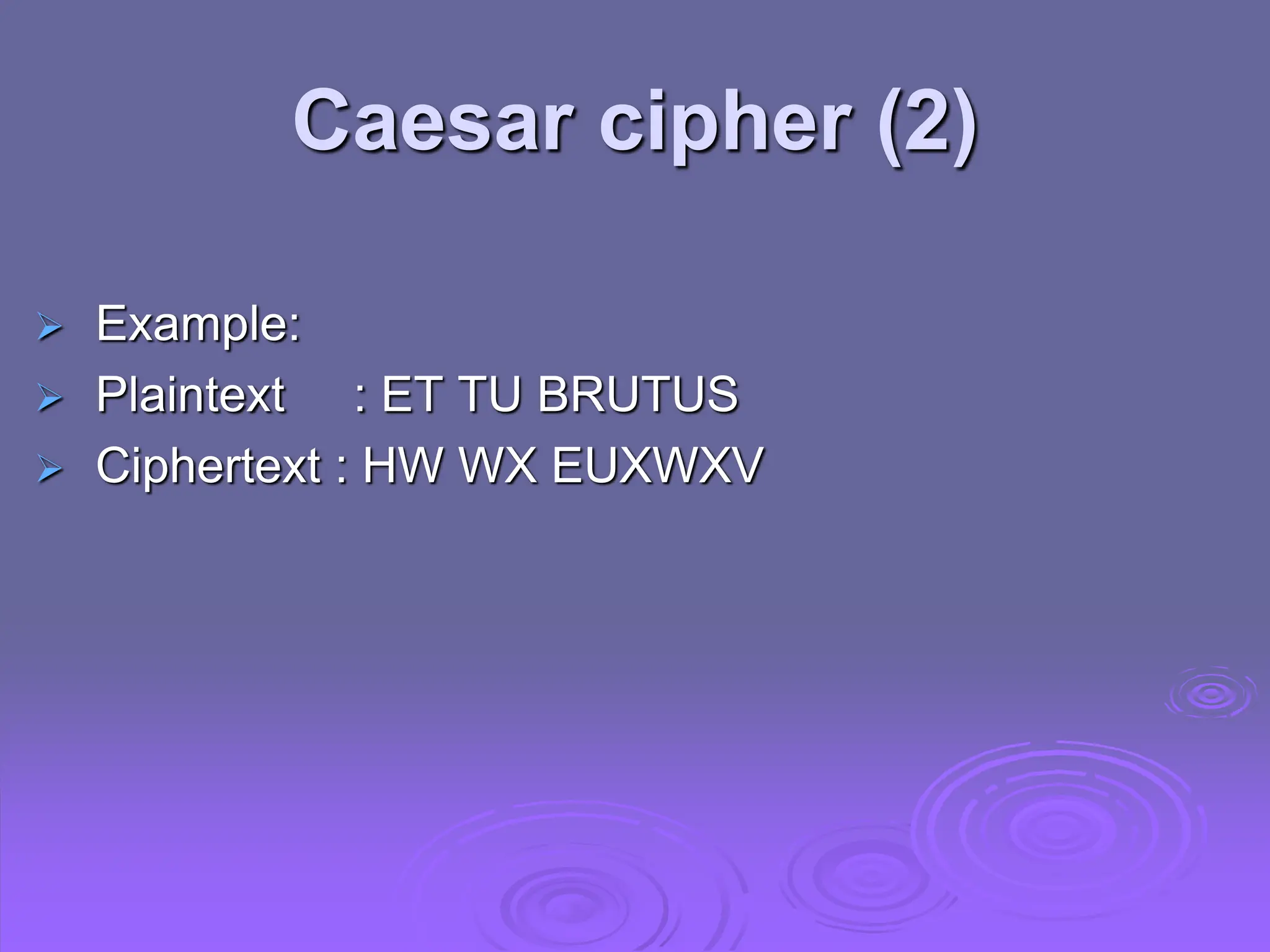
2. The Caesar Cipher replaces each letter with the letter three positions further down the alphabet, encrypting "ET TU BRUTUS" to "HW WX EUXWXV".
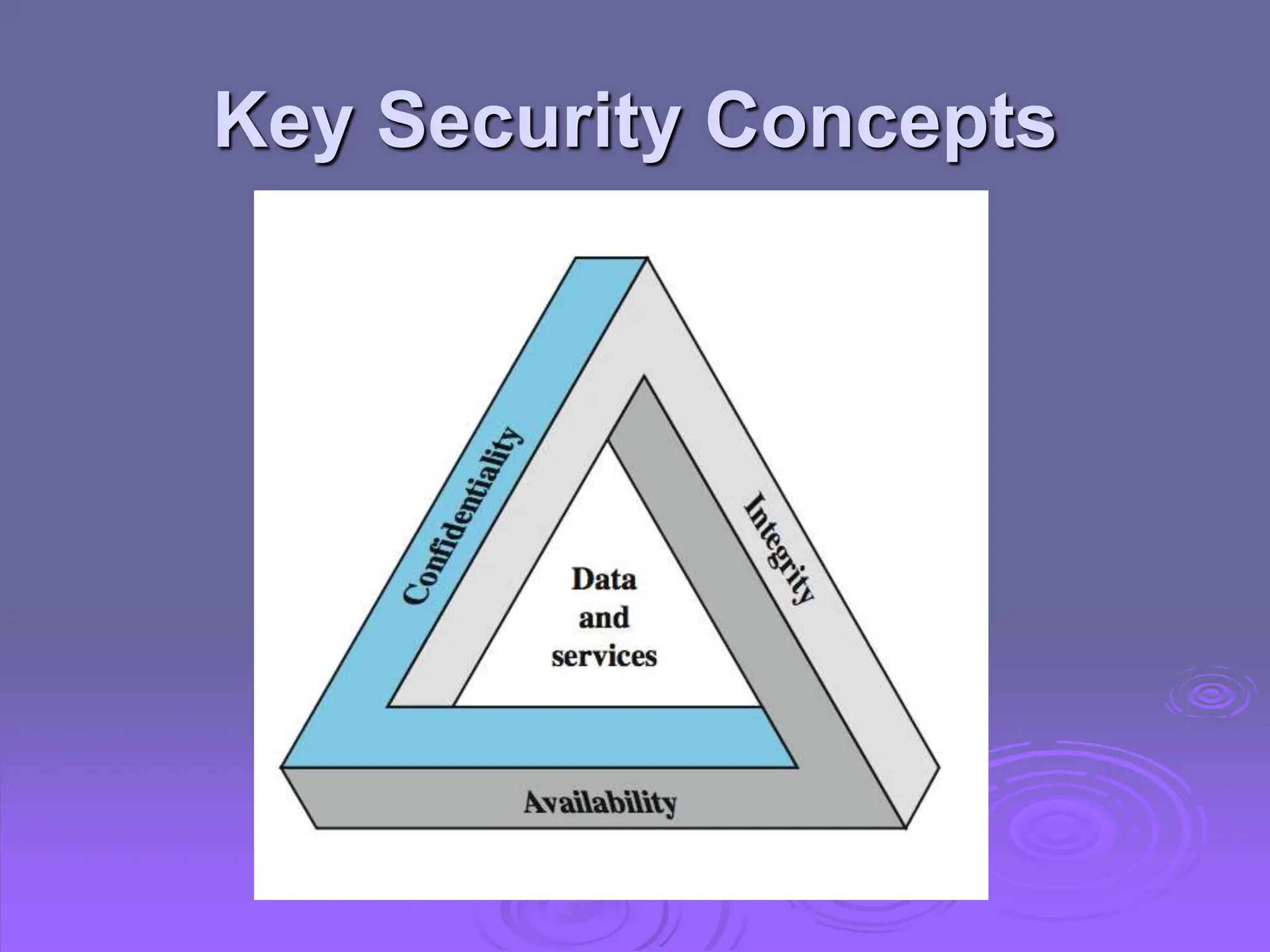
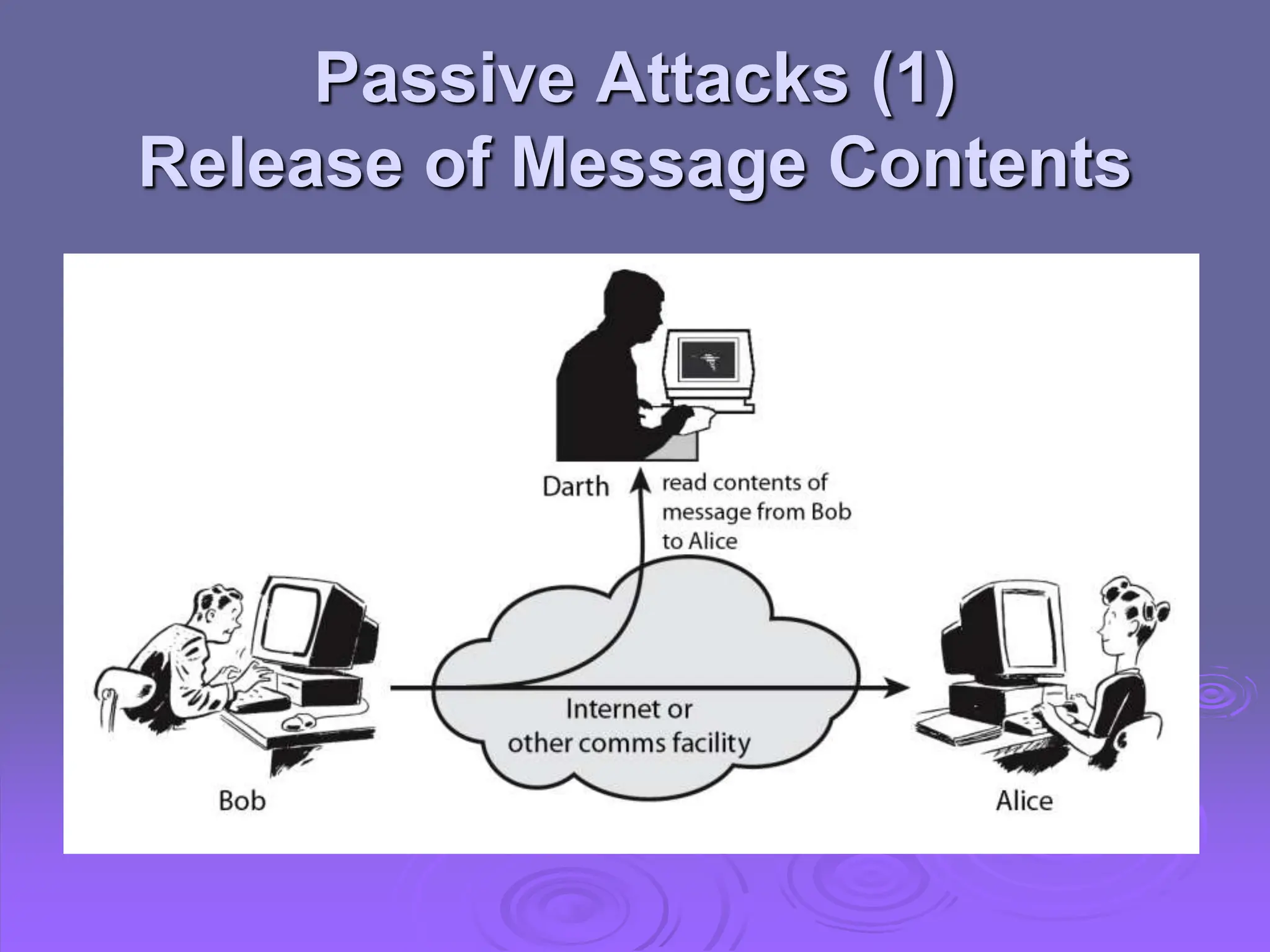
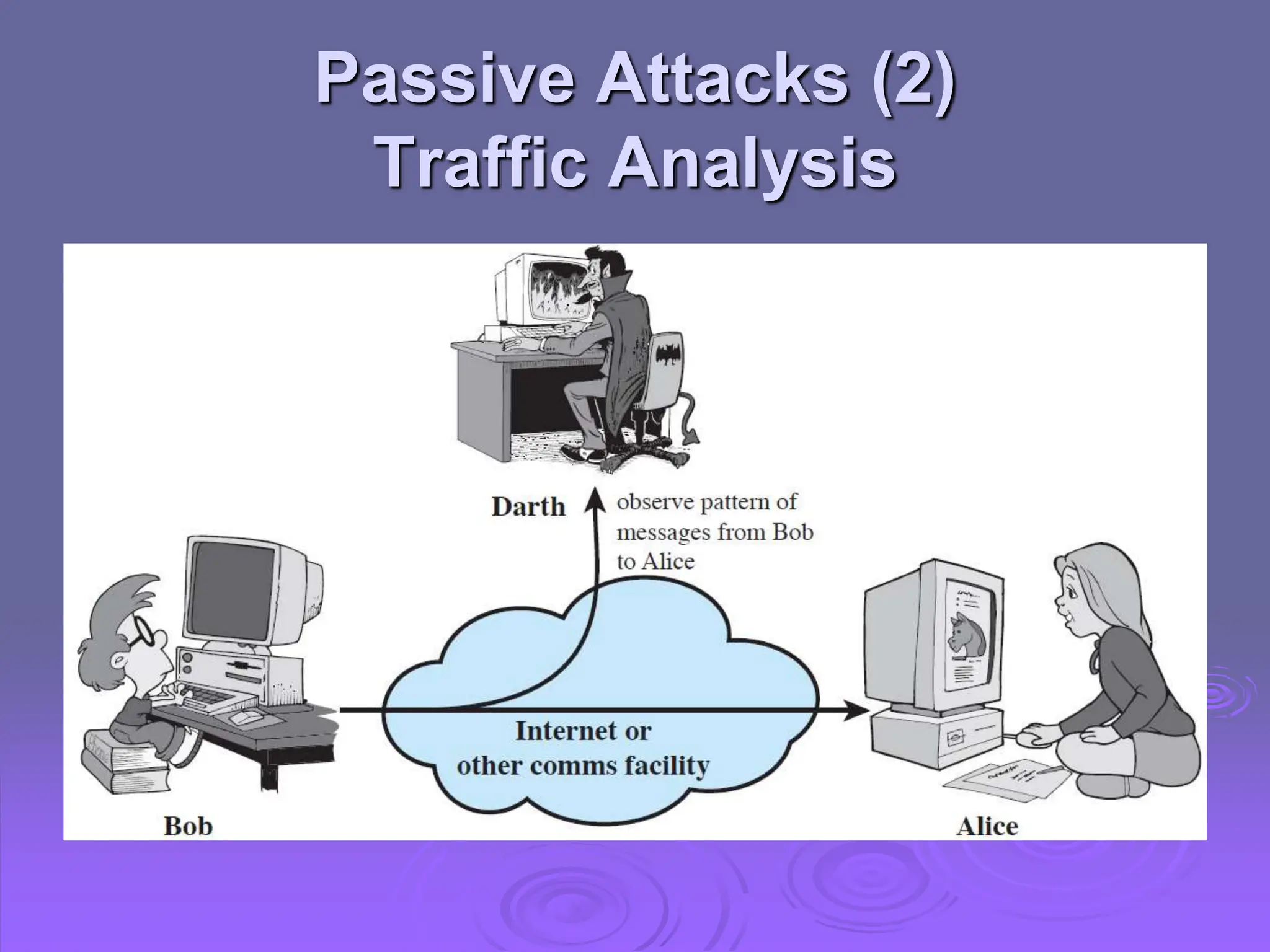
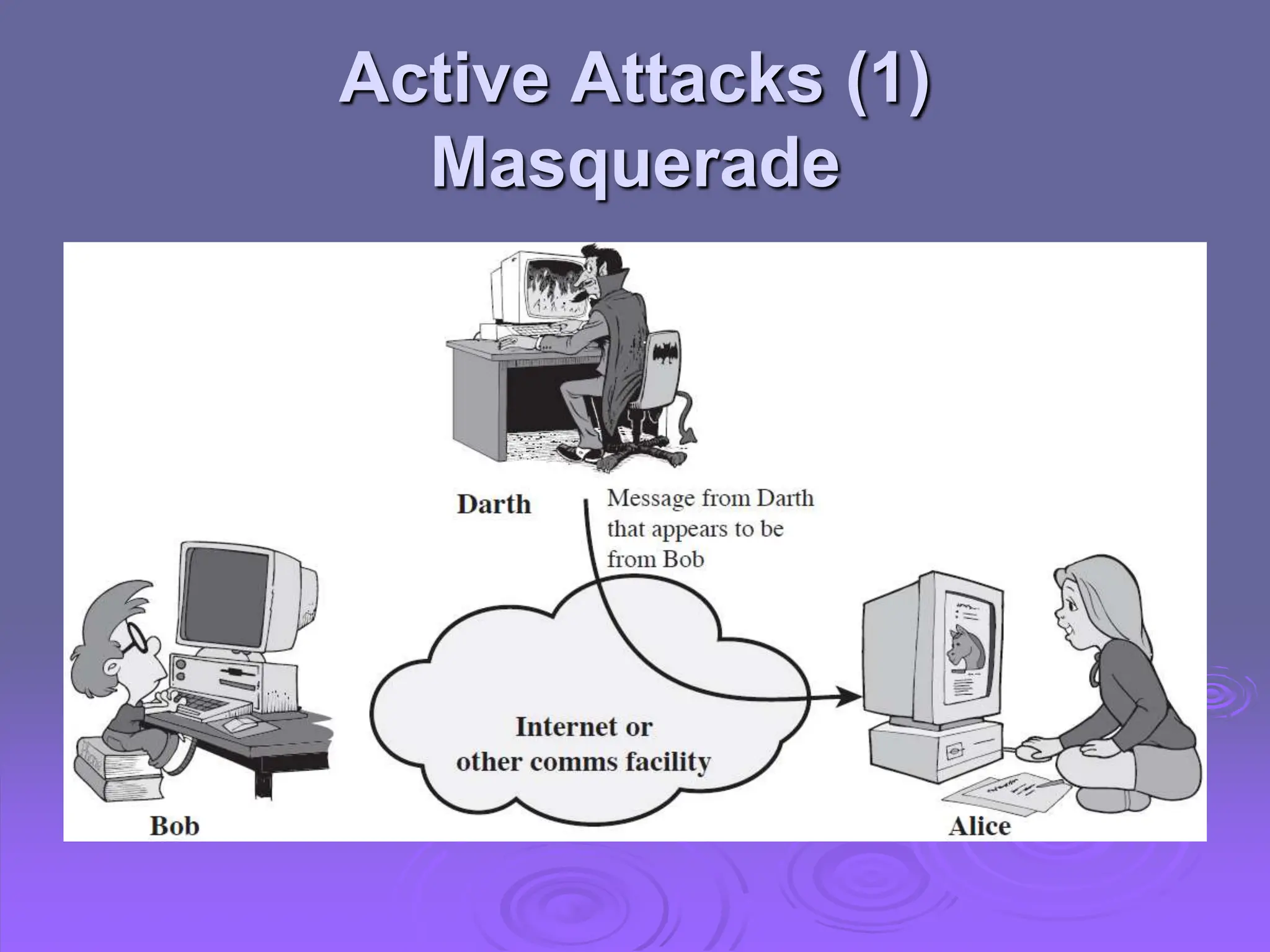
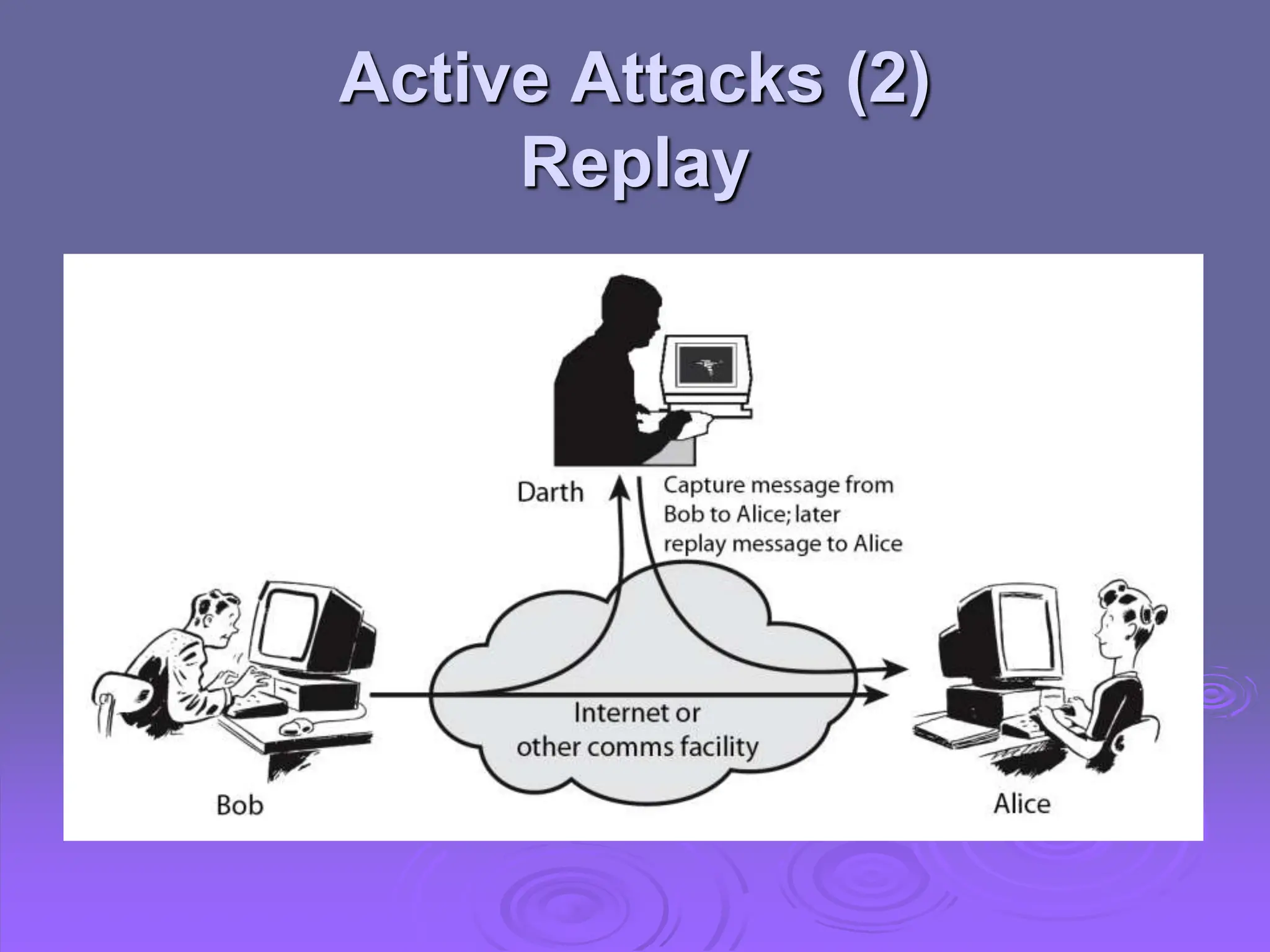
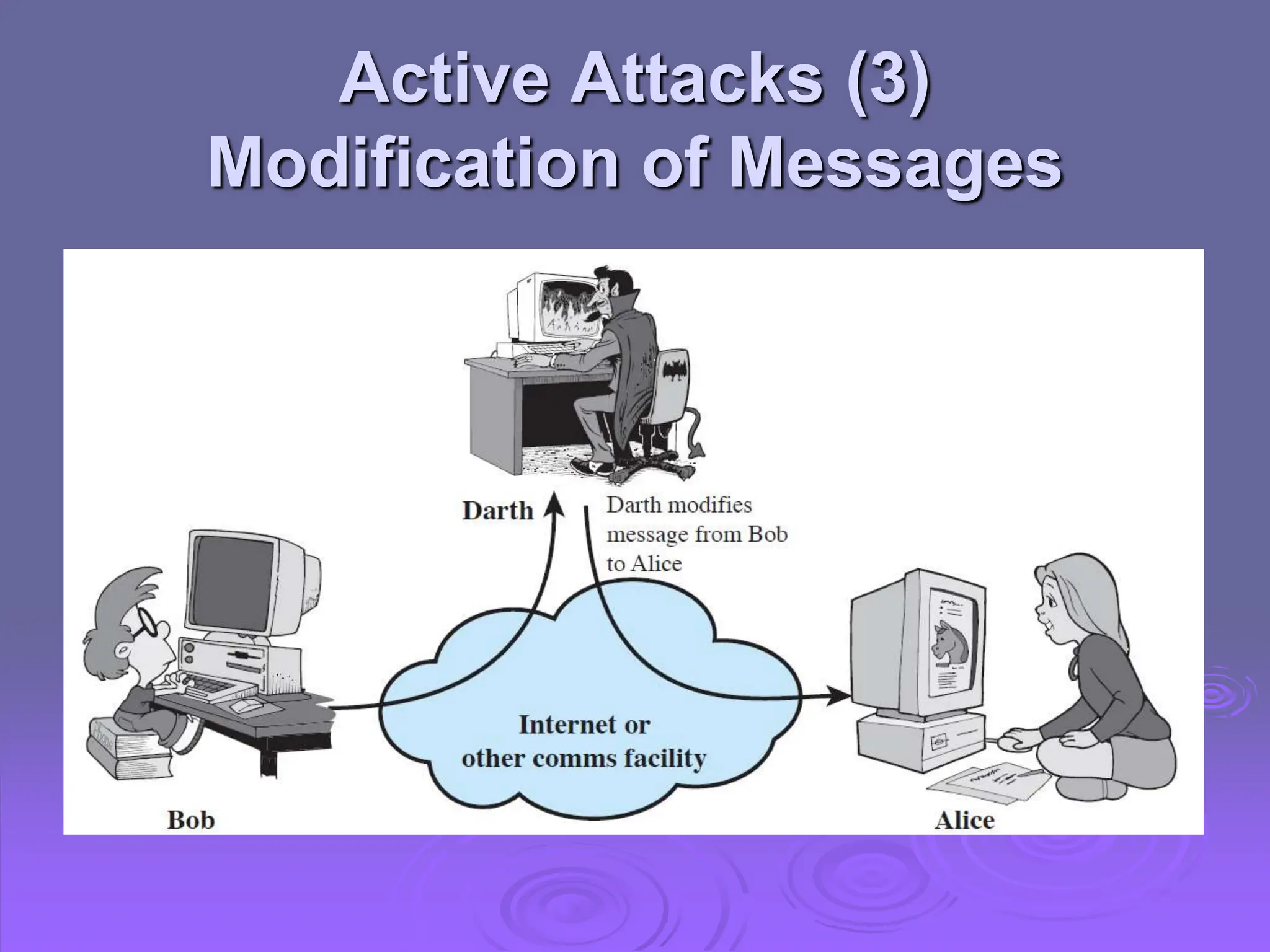
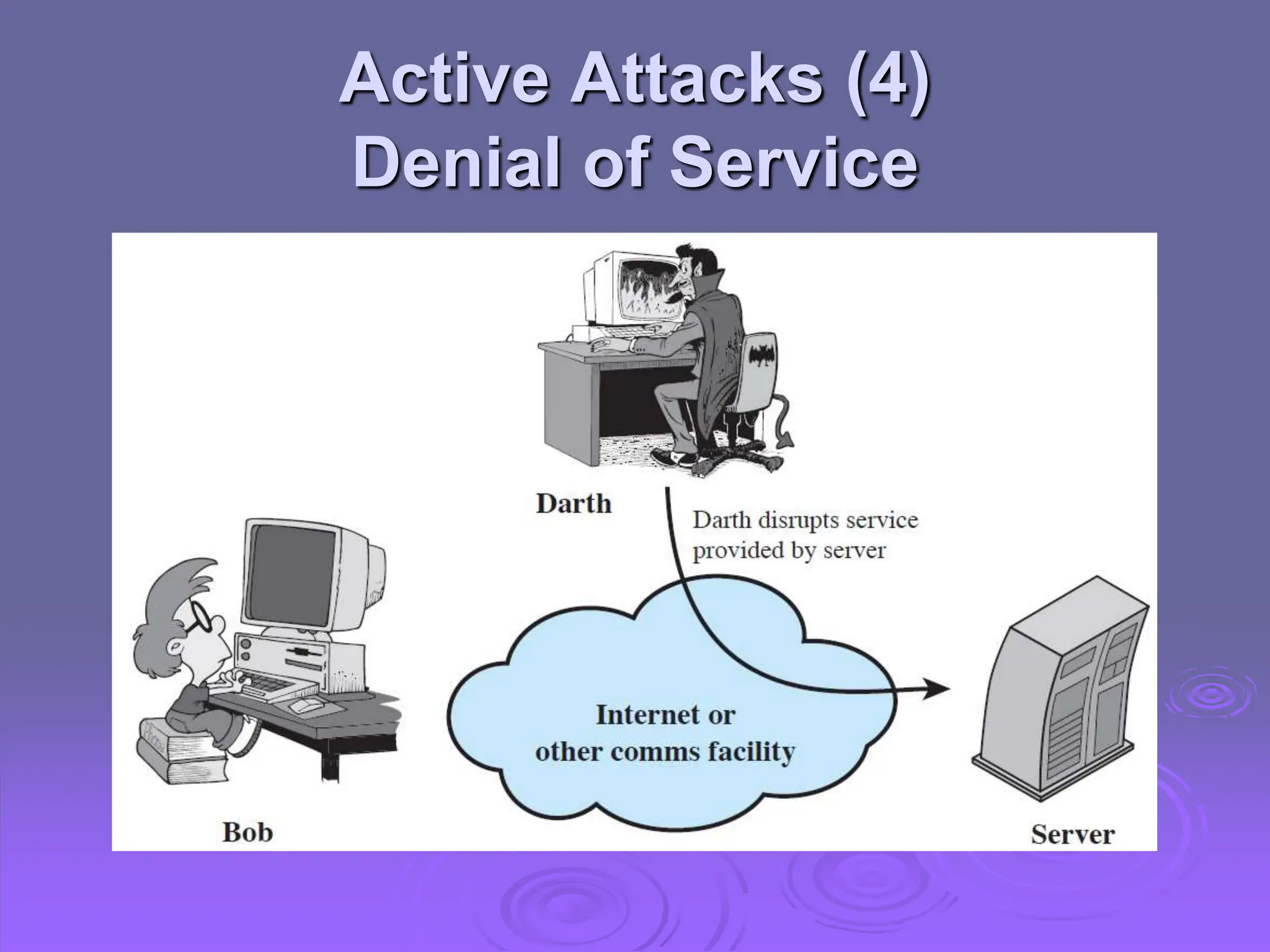
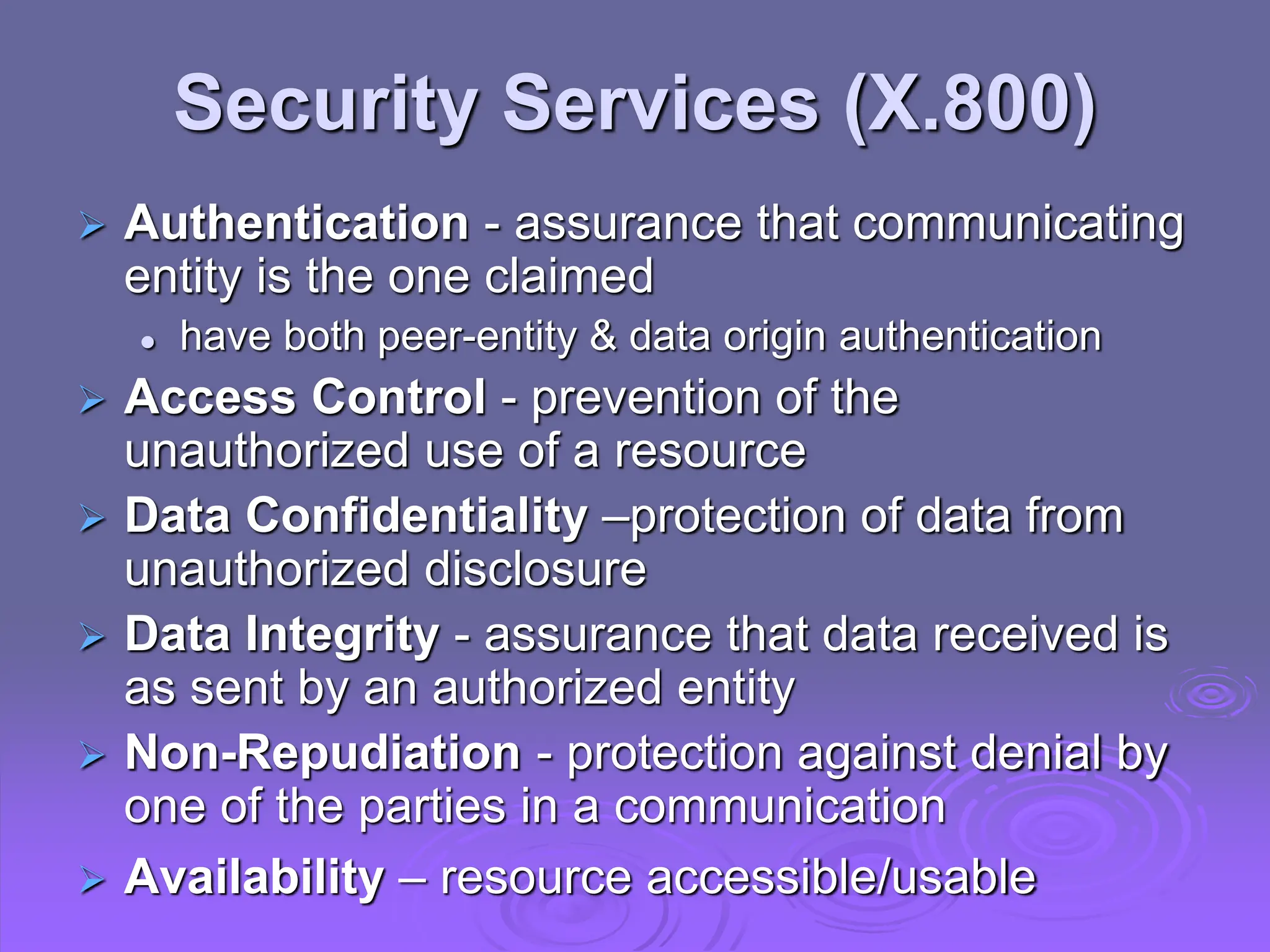
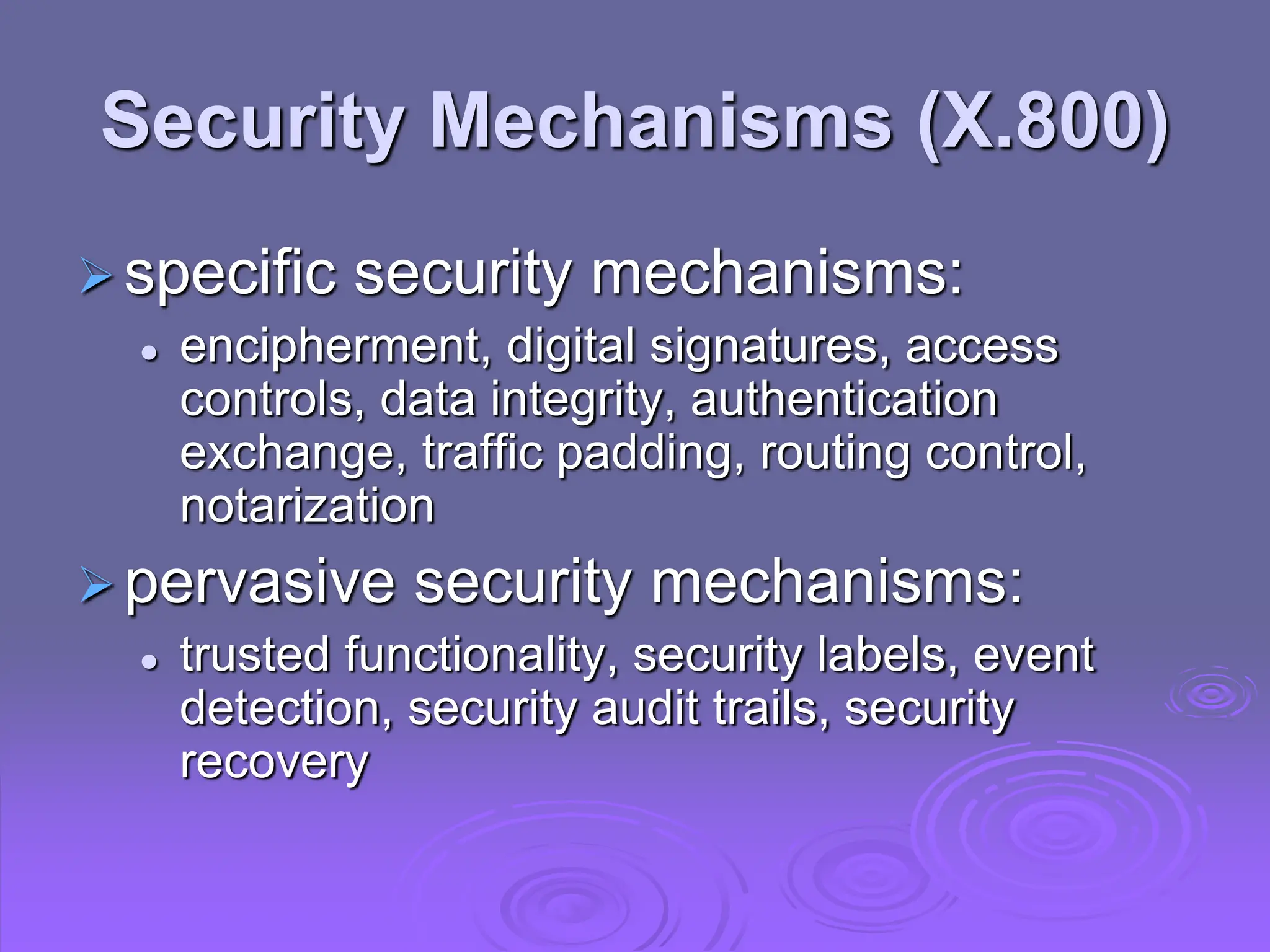
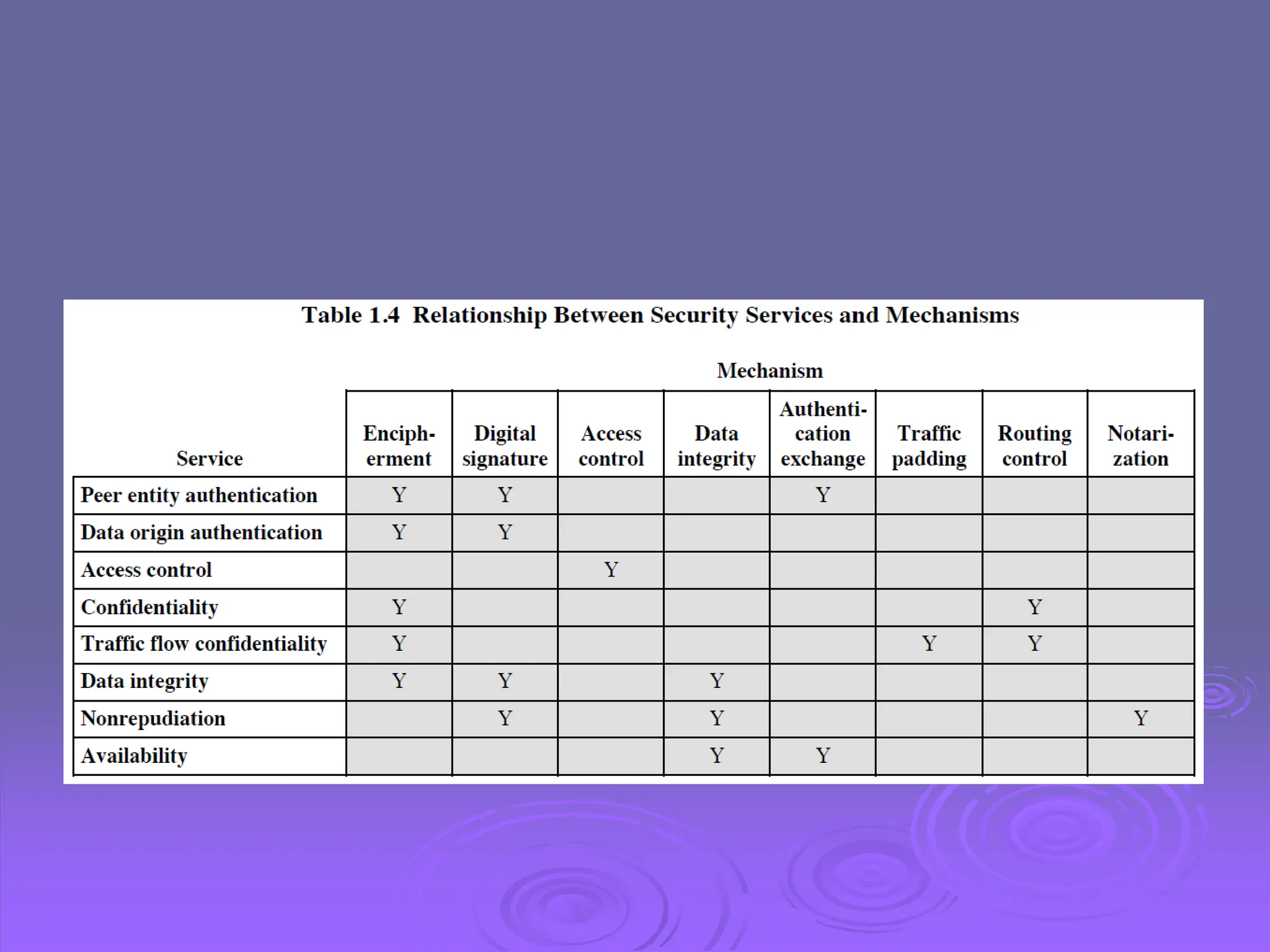
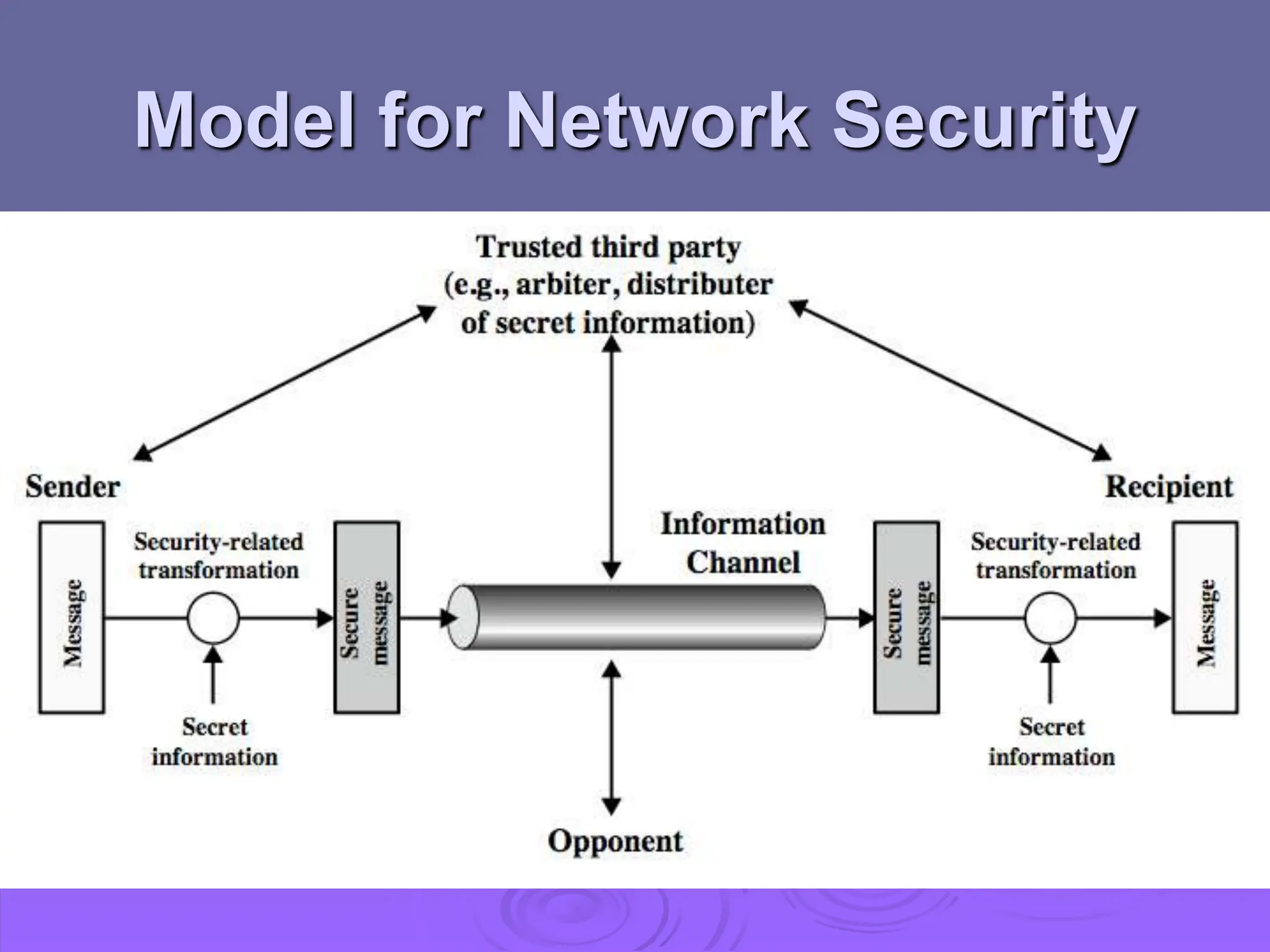
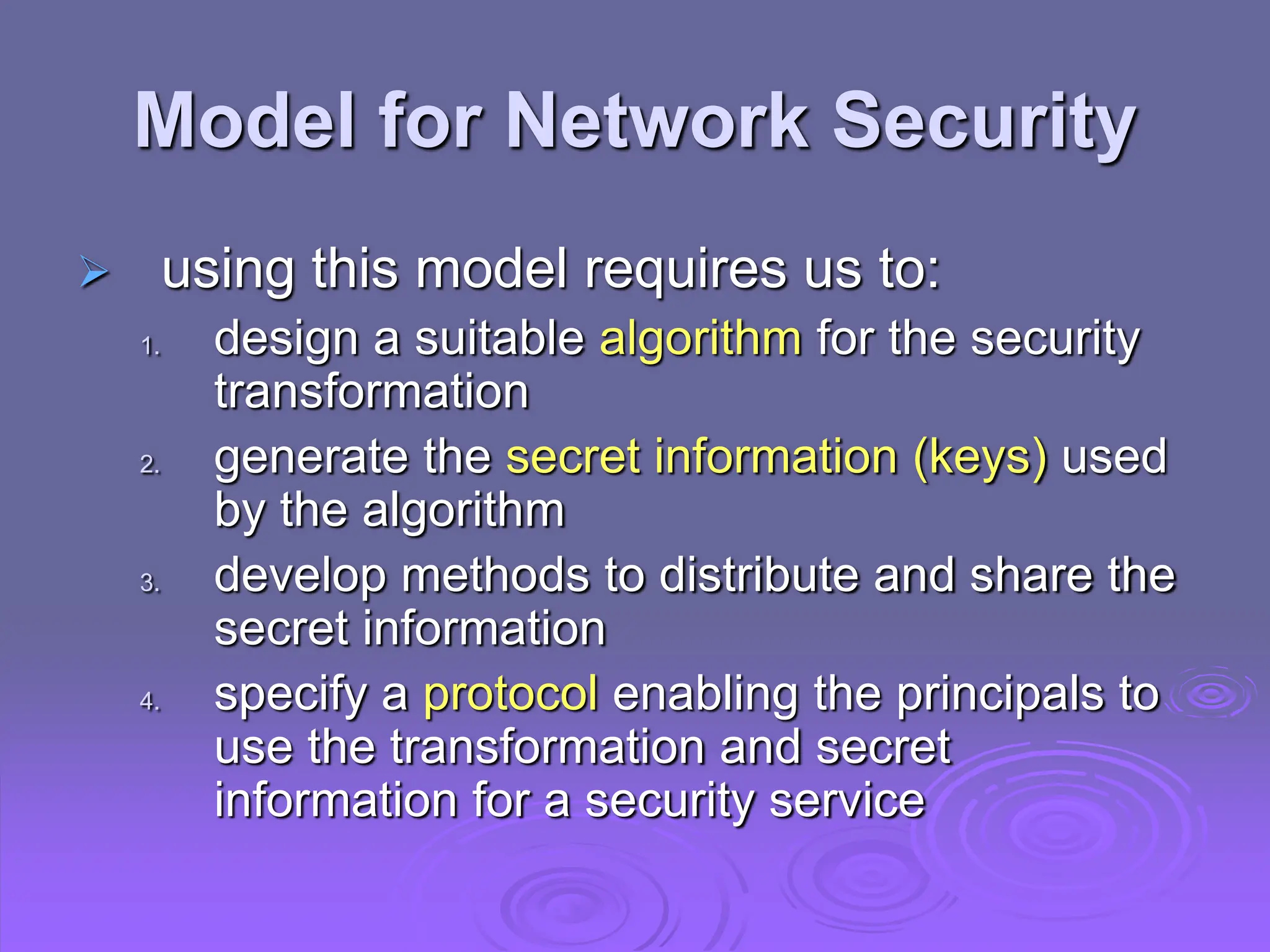
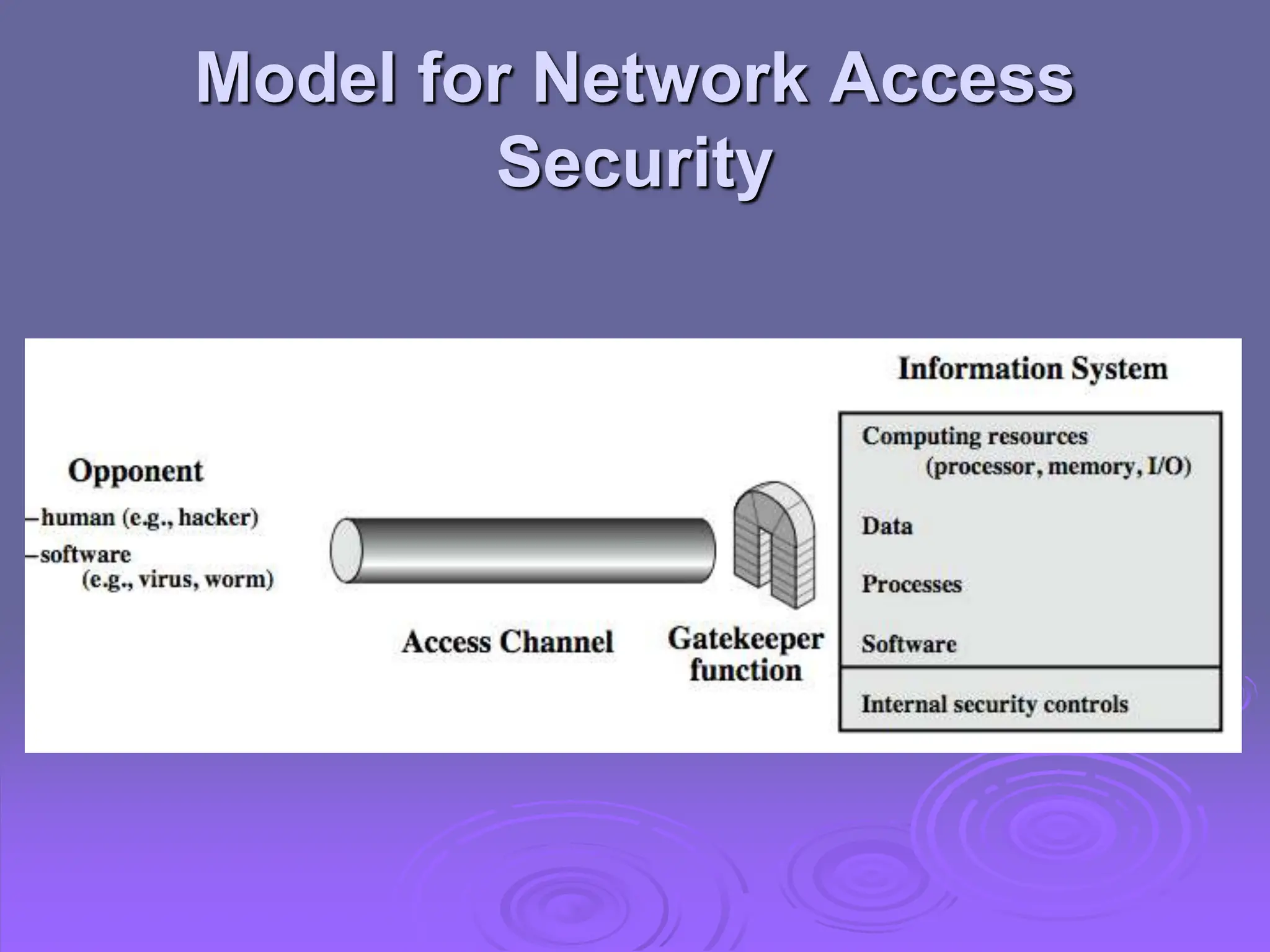
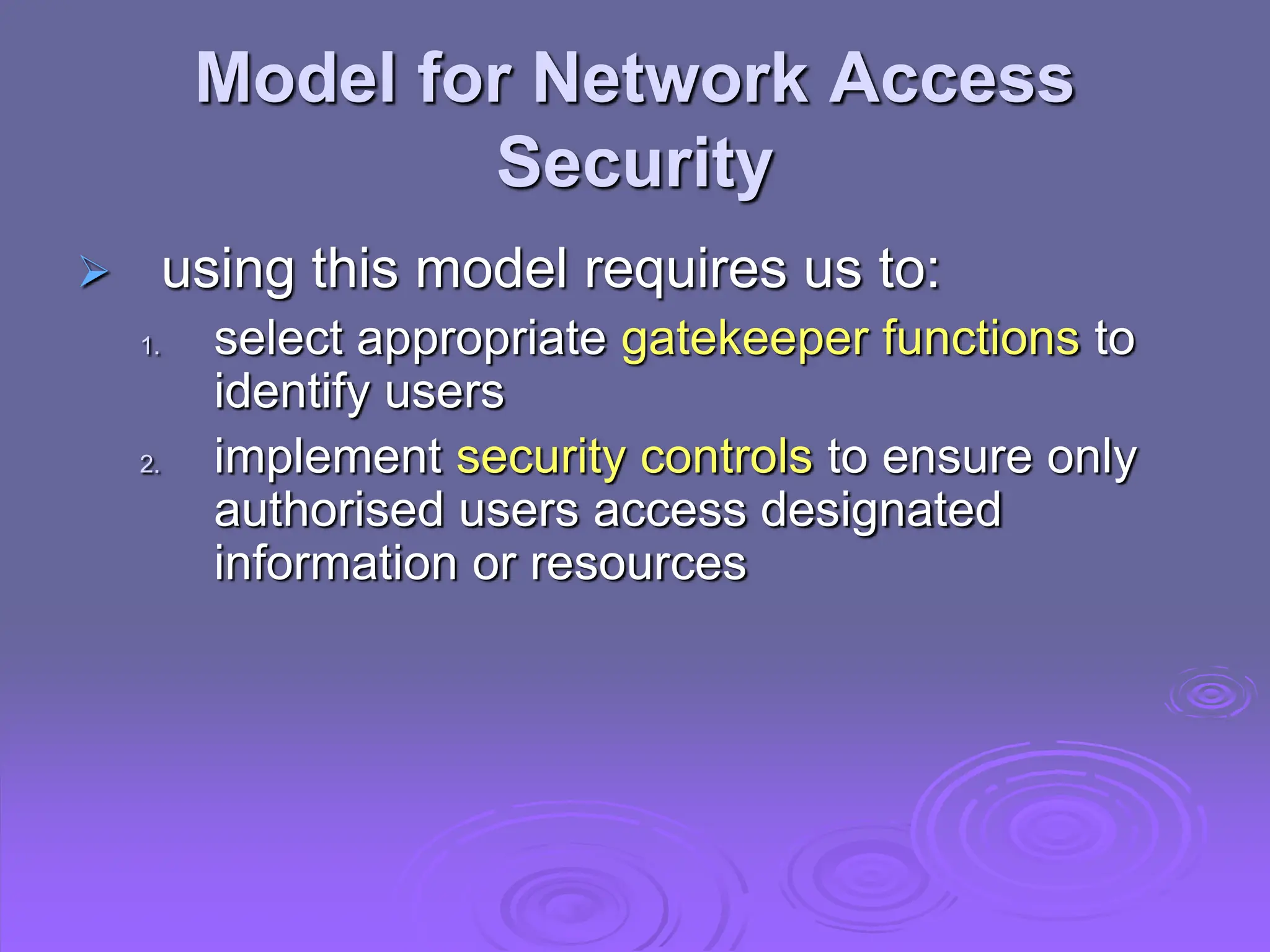
3. Network security concepts like confidentiality, integrity, and availability are discussed alongside security attacks, services, and mechanisms defined in the X.800 standard. Models for providing network and access security are also introduced.
![Computer Security
The protection afforded to an automated
information system in order to attain the
applicable objectives of preserving the
integrity, availability and confidentiality of
information system resources (includes
hardware, software, firmware,
information/data, and telecommunications)
[NIST 1995]](https://image.slidesharecdn.com/lecture-0102-1-240320040843-8cd35a79/75/Network-security-in-computer-network-for-BS-4-2048.jpg)