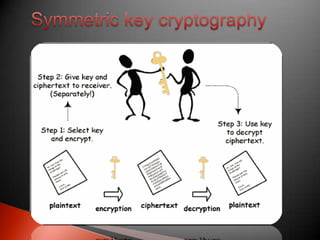
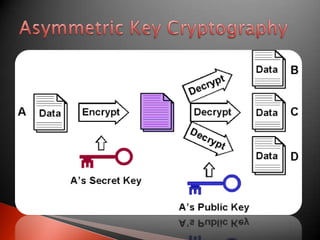
The document discusses the importance of securing information in the digital age. It states that information is a valuable asset that needs to be kept confidential from unauthorized access, protected from unauthorized changes, and available when needed. It then defines some key concepts in information security including confidentiality, authentication, integrity, and access/availability. The document goes on to discuss network security and some common threats. It lists components used for network security like antivirus software, firewalls, and intrusion detection systems. Finally, it briefly covers encryption techniques including symmetric key algorithms and asymmetric/public-private key algorithms.