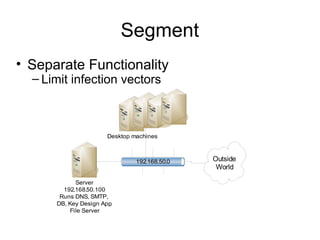
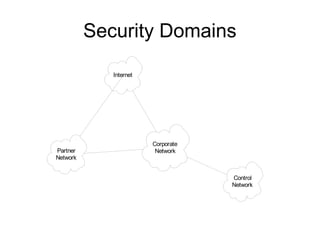
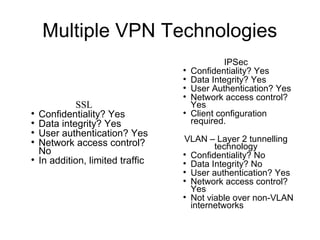
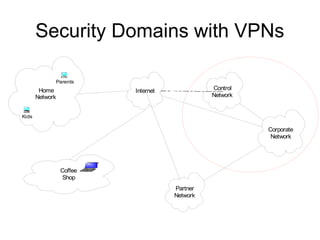
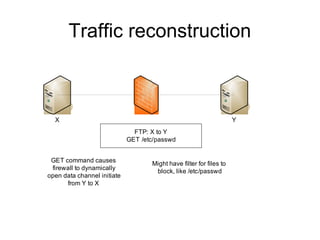
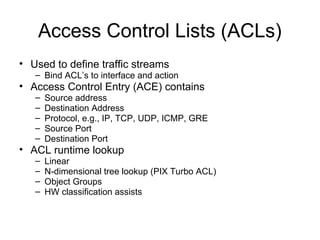
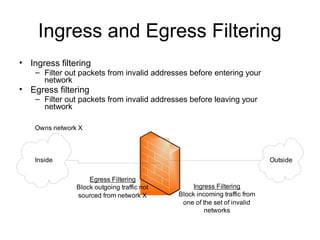
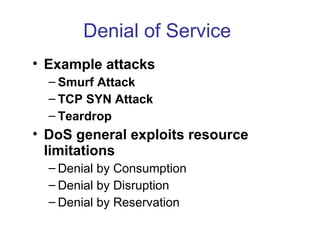
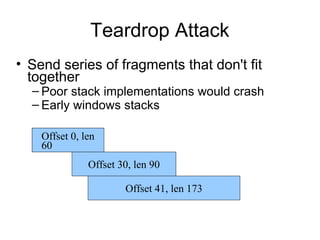
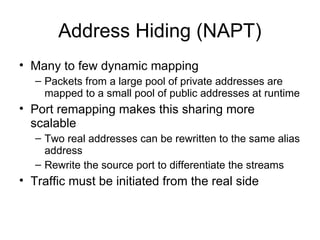
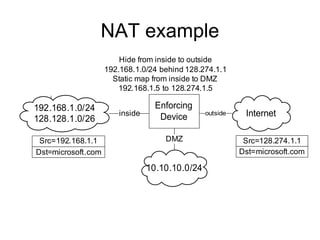
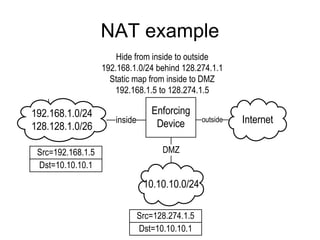
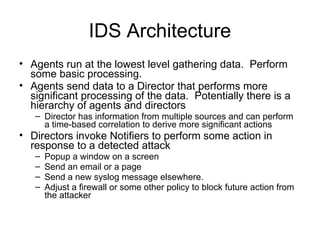
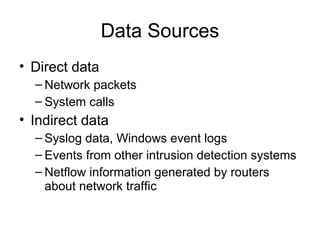
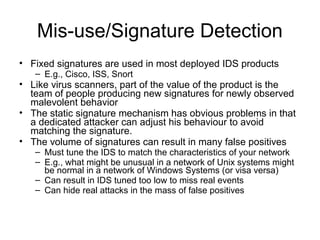
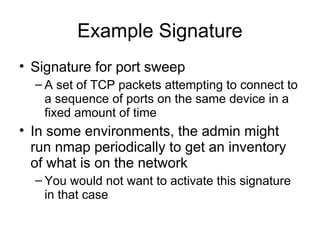
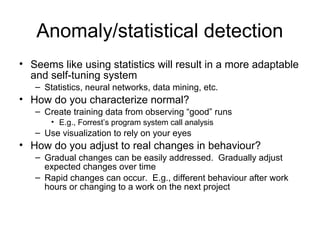
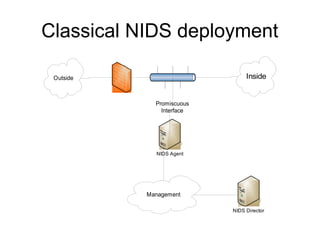
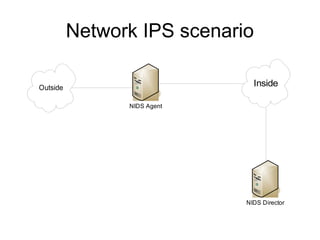
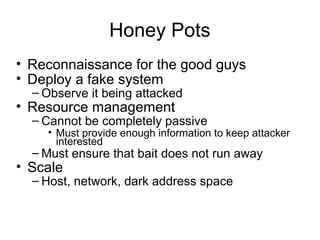
The document provides an overview of network security architecture, focusing on firewalls, intrusion detection systems (IDS), and virtual private networks (VPNs). It discusses different firewall technologies, their functionalities, and the concept of security domains, along with the types of attacks such as denial of service. Additionally, it covers intrusion detection mechanisms, including signature and anomaly-based detection techniques, and concludes with the importance of layered security measures to protect corporate networks.