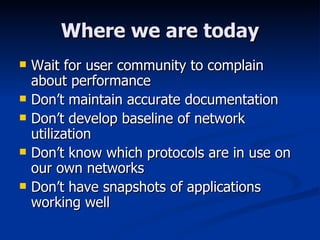
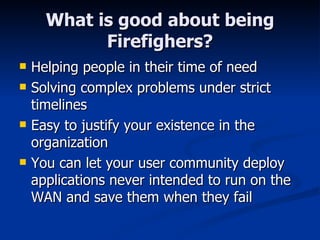
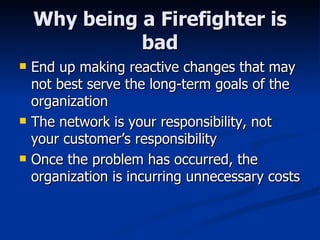
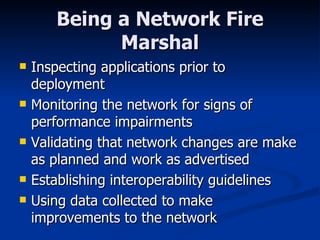
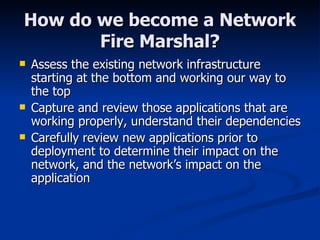
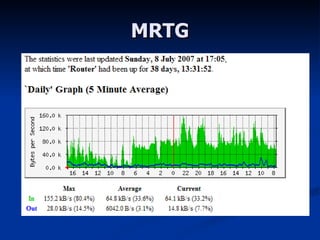
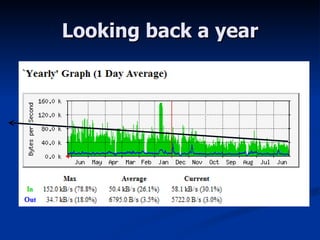
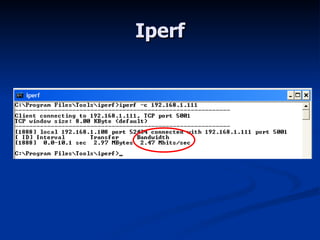
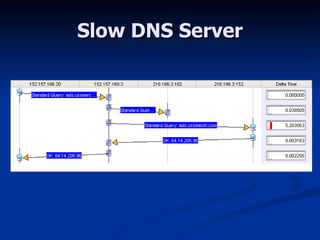
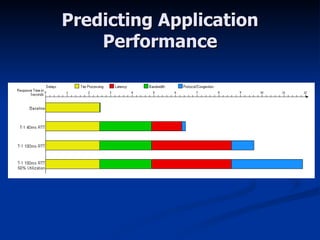
The document discusses shifting network monitoring from a reactive "firefighting" approach to a proactive "fire prevention" model. It recommends assessing the existing network infrastructure starting from the physical layer up, capturing how applications currently work, and carefully reviewing new applications before deployment to determine their network impact and vice versa. Key aspects include monitoring network utilization, errors and server response times, understanding application dependencies, and using tools to test applications prior to rollout. The goal is to establish baselines and catch issues early to minimize unnecessary costs from unplanned outages.