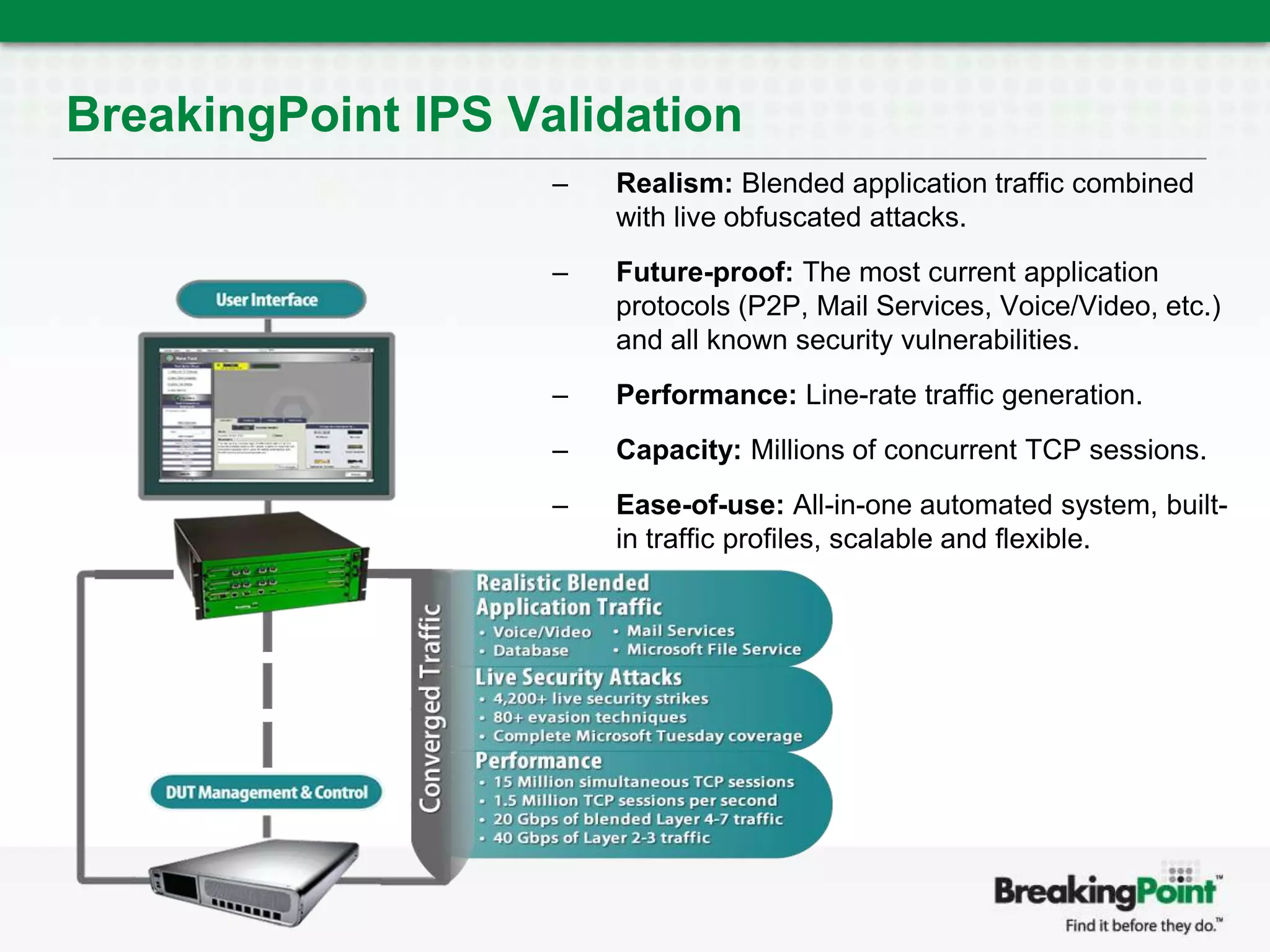
The document discusses the importance of validating intrusion prevention systems (IPS) for resilience under difficult network conditions, emphasizing the need for realistic testing against various traffic loads and current vulnerabilities. It outlines a methodology for testing IPS effectiveness, including simulating maximum session loads and a range of attack scenarios. The use of advanced testing tools like BreakingPoint is recommended for ensuring comprehensive security evaluation and performance validation.