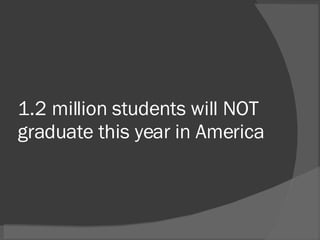
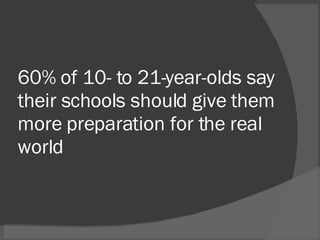
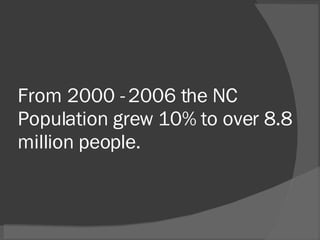
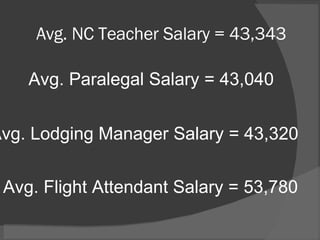
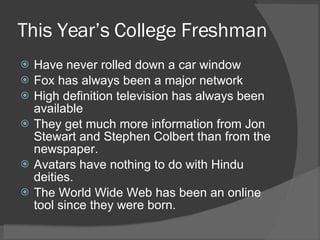
The North Carolina State Board of Education aims to ensure that all public school students graduate equipped for the 21st century. Internet usage among teenagers has seen significant growth, with over 1 billion online users globally, and a notable rise in social networking and content creation among youth. Additionally, there is a call for schools to better prepare students for real-world challenges, evidenced by statistics on college enrollment, employment prospects, and the increasing prevalence of technology in education.