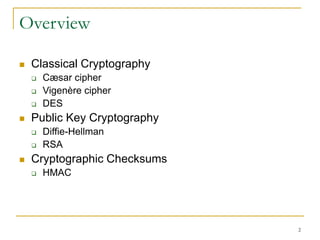
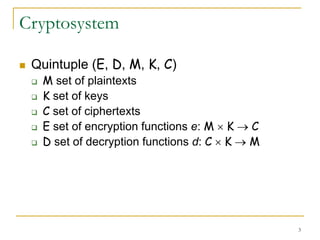
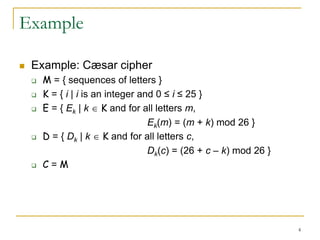
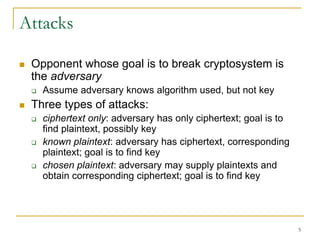
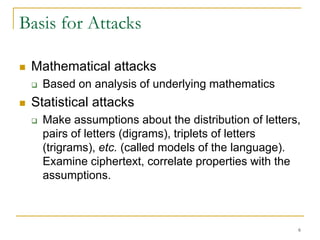
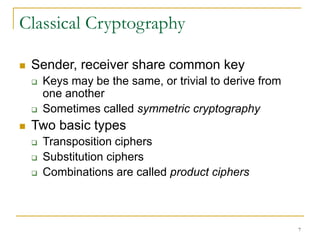
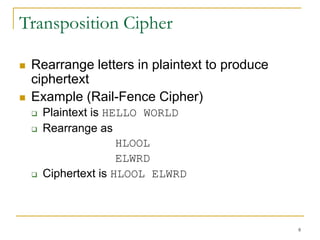
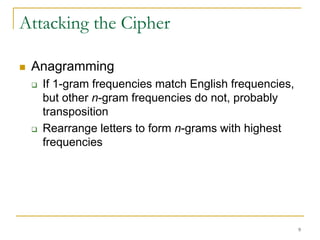
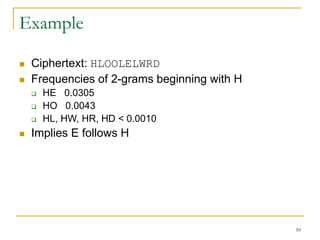
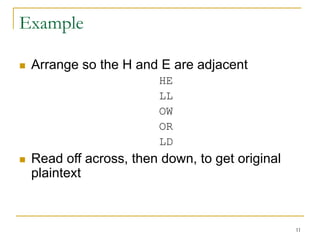
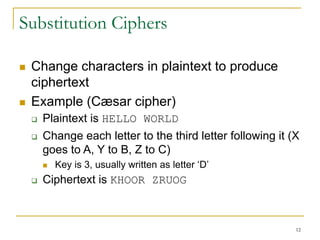
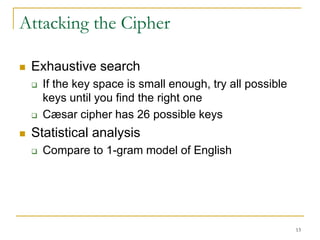
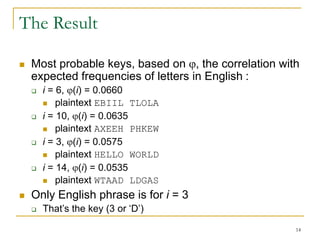
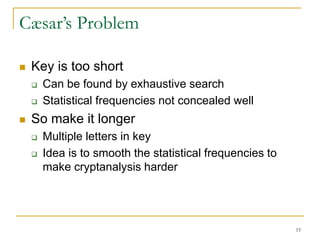
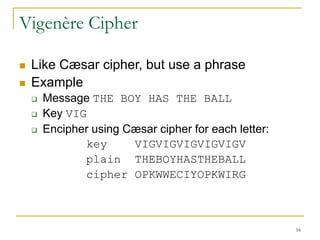
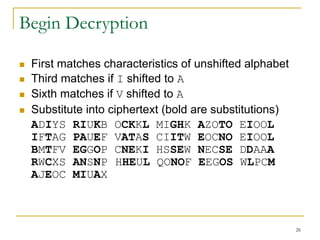
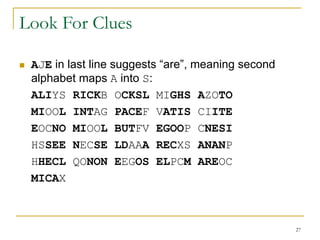
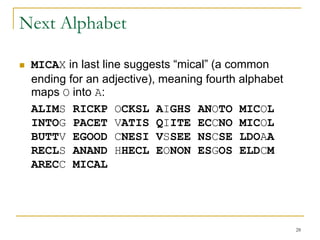
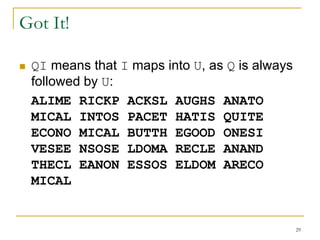
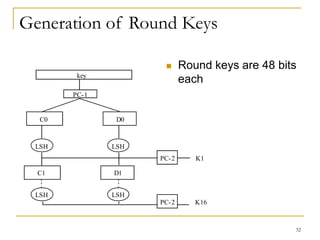
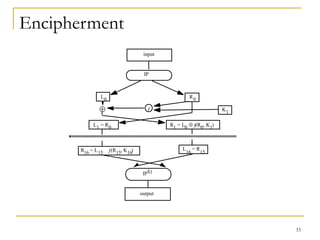
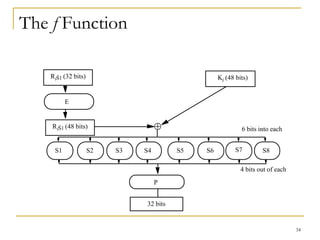
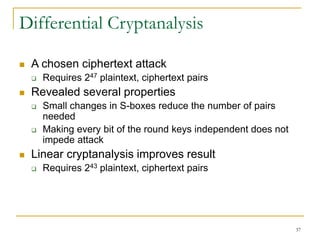
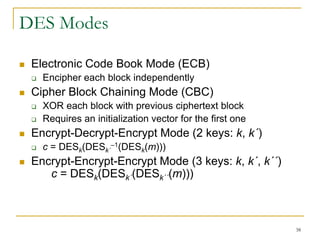
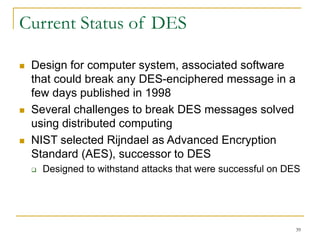
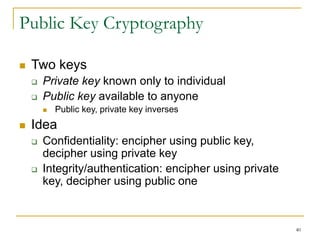
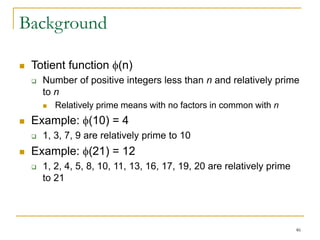
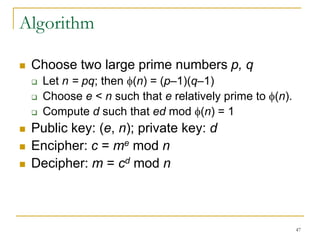
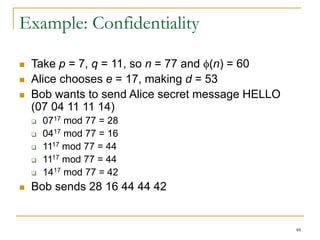
This document provides an overview of cryptography topics including classical cryptography techniques like the Caesar cipher and Vigenere cipher, as well as modern techniques like the Data Encryption Standard (DES) and public key cryptography. It discusses cryptanalysis methods for attacking ciphers like frequency analysis and discusses properties of DES that made it vulnerable to attacks. The document also introduces the idea of public key cryptography and one-time pads.