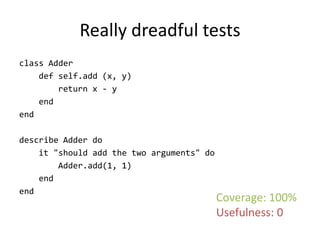
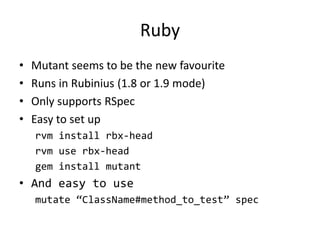
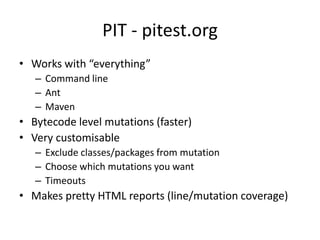
The document discusses mutation testing as a method to evaluate the effectiveness of software tests, emphasizing that code coverage alone can be misleading. It illustrates how mutation testing works by showing how altering code can reveal ineffective tests, highlighting potential pitfalls such as equivalent mutants that do not fail any tests despite being flawed. The document concludes by mentioning specific mutation testing tools for Ruby and Java, and notes the ongoing challenges in accurately identifying equivalent mutations in code.




![How bad is it?
• Good paper assessing the problem [SZ10]
• Took 7 widely used, “large” projects
• Found:
– 15 mins to assess one mutation
– 45% uncaught mutations are equivalent
– Better tested project -> worse signal-to-noise ratio](https://image.slidesharecdn.com/2012-07-03mutationtesting-rubyedition-120704090431-phpapp01/85/Mutation-Testing-Ruby-Edition-22-320.jpg)
![Can we detect the equivalents?
• Not in the general case [BA82]
• Some specific cases can be detected
– Using compiler optimisation techniques [BS79]
– Using mathematical constraints [DO91]
– Line coverage changes [SZ10]
• All heuristic algorithms – not seen any
claiming to kill all equivalent mutants](https://image.slidesharecdn.com/2012-07-03mutationtesting-rubyedition-120704090431-phpapp01/85/Mutation-Testing-Ruby-Edition-23-320.jpg)

![References
• [BA82] - T. A. Budd and D. Angluin. Two notions of correctness and
their relation to testing. Acta Informatica, 18(1):31-45, November
1982.
• [BS79] - D. Baldwin and F. Sayward. Heuristics for determining
equivalence of program mutations. Research report 276,
Department of Computer Science, Yale University, 1979.
• [DO91] - R. A. DeMillo and A. J. O
utt. Constraint-based automatic test data generation. IEEE
Transactions on Software Engineering, 17(9):900-910, September
1991.
• [SZ10] - D. Schuler and A. Zeller. (Un-)Covering Equivalent Mutants.
Third International Conference on Software Testing, Verification and
Validation (ICST), pages 45-54. April 2010.](https://image.slidesharecdn.com/2012-07-03mutationtesting-rubyedition-120704090431-phpapp01/85/Mutation-Testing-Ruby-Edition-32-320.jpg)
![Also interesting
• [AHH04] – K. Adamopoulos, M. Harman and R. M. Hierons. How to
Overcome the Equivalent Mutant Problem and Achieve Tailored
Selective Mutation Using Co-evolution. Genetic and Evolutionary
Computation -- GECCO 2004, pages 1338-1349. 2004.](https://image.slidesharecdn.com/2012-07-03mutationtesting-rubyedition-120704090431-phpapp01/85/Mutation-Testing-Ruby-Edition-33-320.jpg)