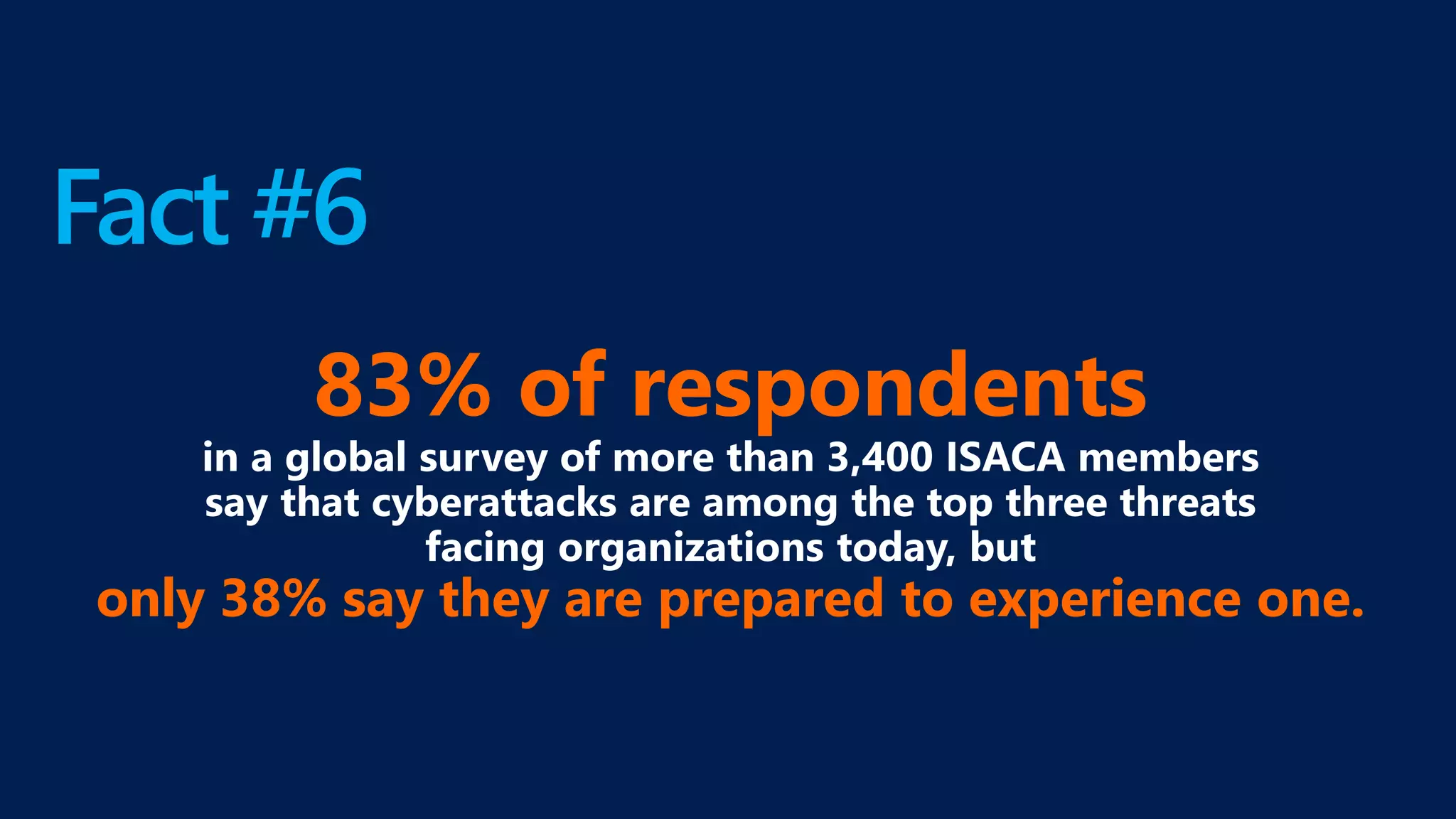
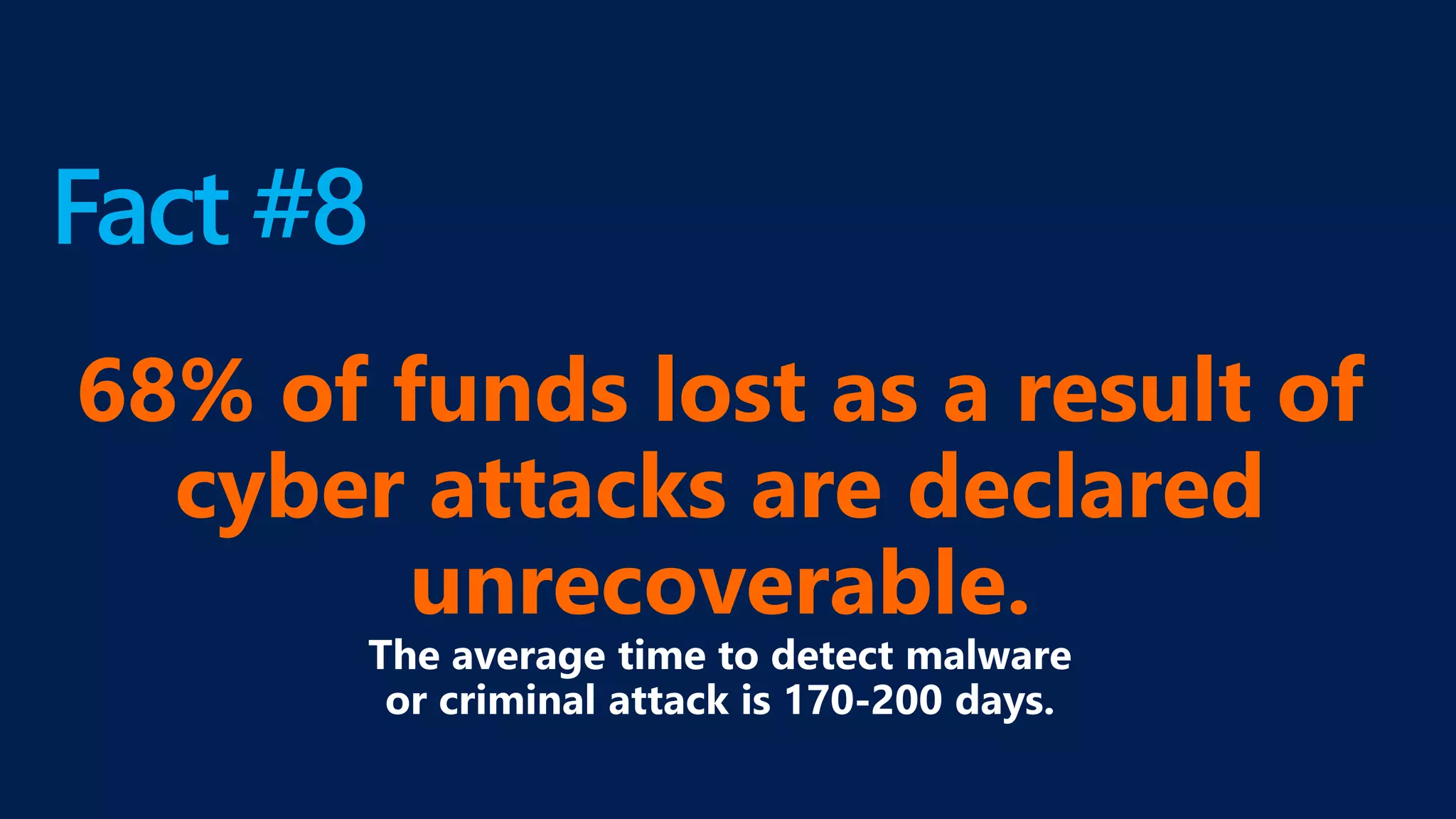
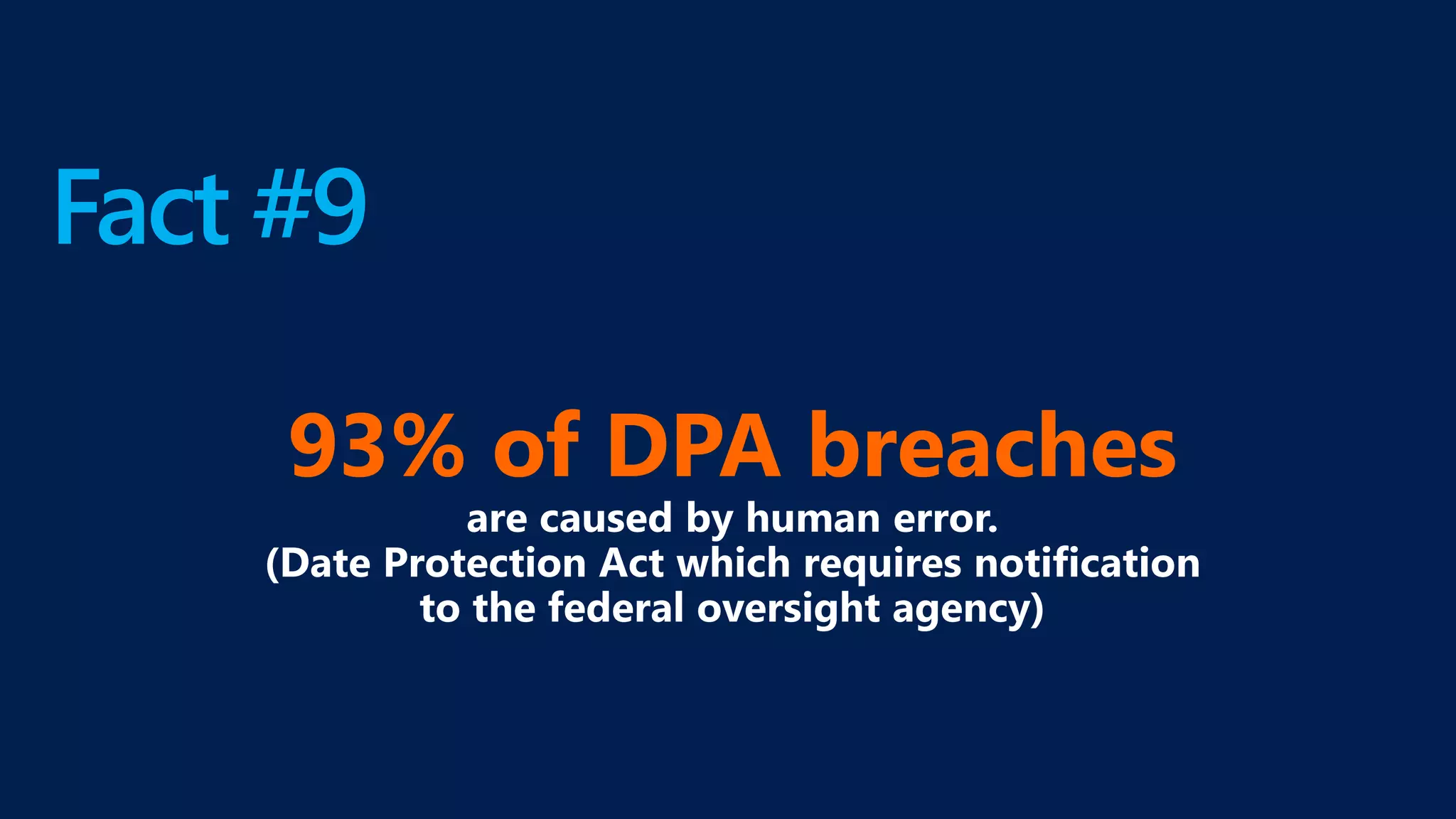
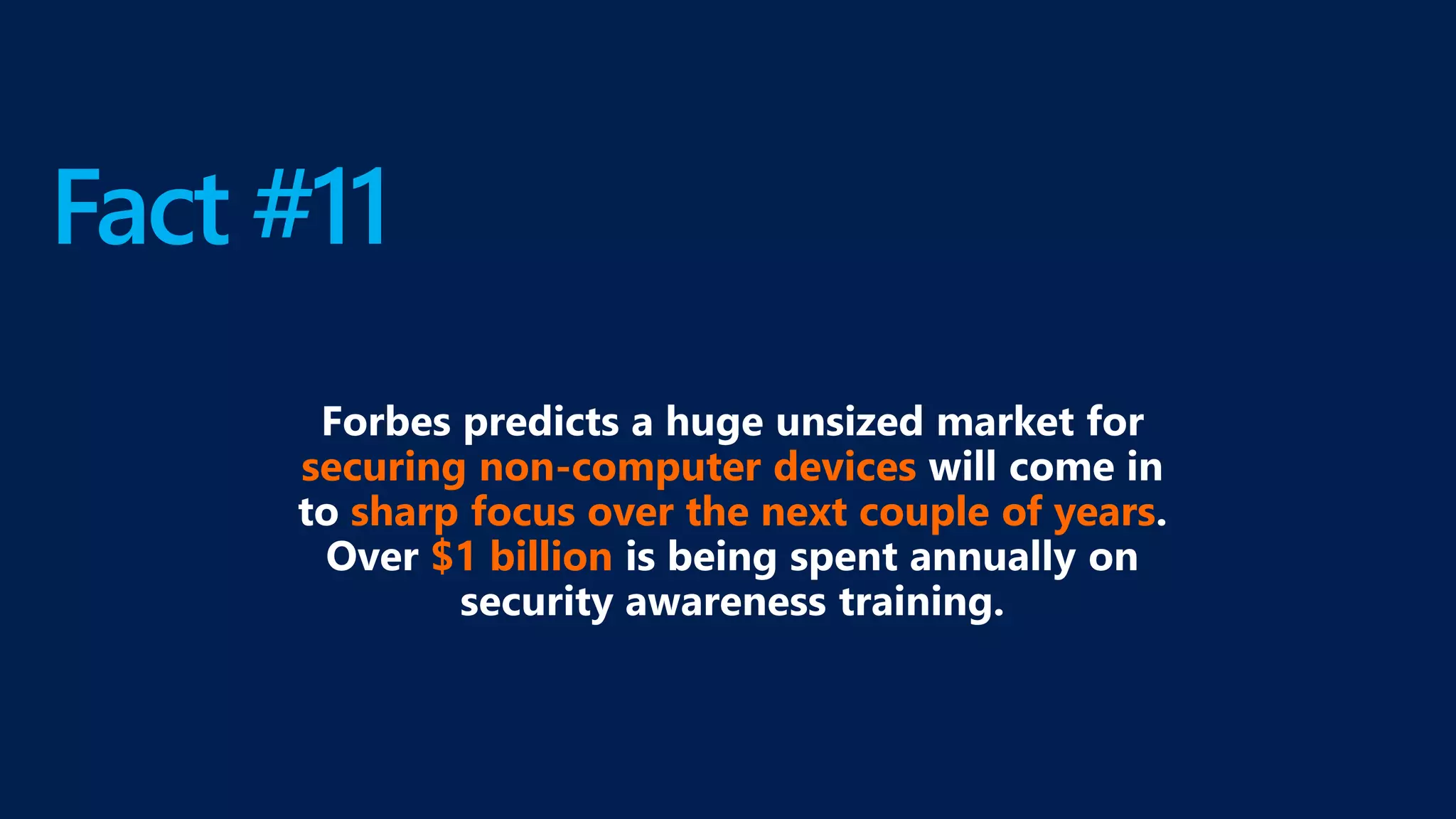
Denis Wilson is a seasoned technology strategist with over 20 years of experience in network systems for small businesses, certified by Microsoft in cloud computing. The document outlines his expertise and offers free resources, including a strategic network security assessment and a trial of Microsoft Office 365. It also highlights alarming cybersecurity statistics, emphasizing the financial impact of cyber attacks and the necessity for businesses to adopt intentional IT strategies.