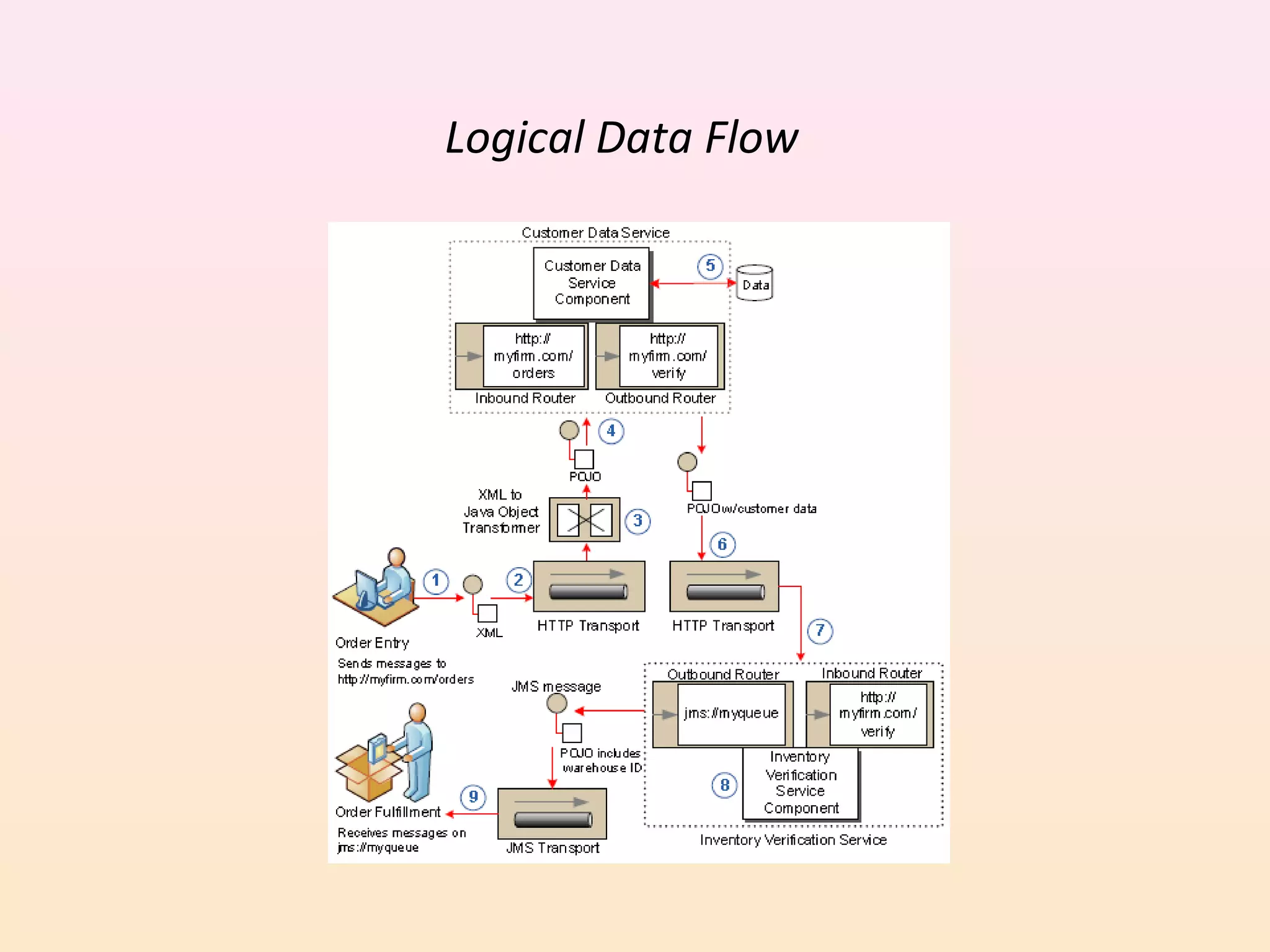
Mule is a lightweight Java-based messaging framework that allows for integration of applications regardless of technology. It uses an enterprise service bus architecture to route messages between applications, handling interactions transparently across platforms and protocols. Mule represents application functionality as reusable services that process data through components, routers, and transports while transformers convert data as needed. It provides tools for building integrated systems without vendor lock-in.